Give asymptotically tight upper and lower bounds for T (n) in each of the following algorithmic recurrences. Justify your answers. A. T(n) = T(7n/10) + n B. T(n) = 16T(n/4) + nº C. T(n) = 2T(n/4) + √√n
Give asymptotically tight upper and lower bounds for T (n) in each of the following algorithmic recurrences. Justify your answers. A. T(n) = T(7n/10) + n B. T(n) = 16T(n/4) + nº C. T(n) = 2T(n/4) + √√n
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter5: Control Structures Ii (repetition)
Section: Chapter Questions
Problem 7PE
Related questions
Question
can you help explain the question on the attached?
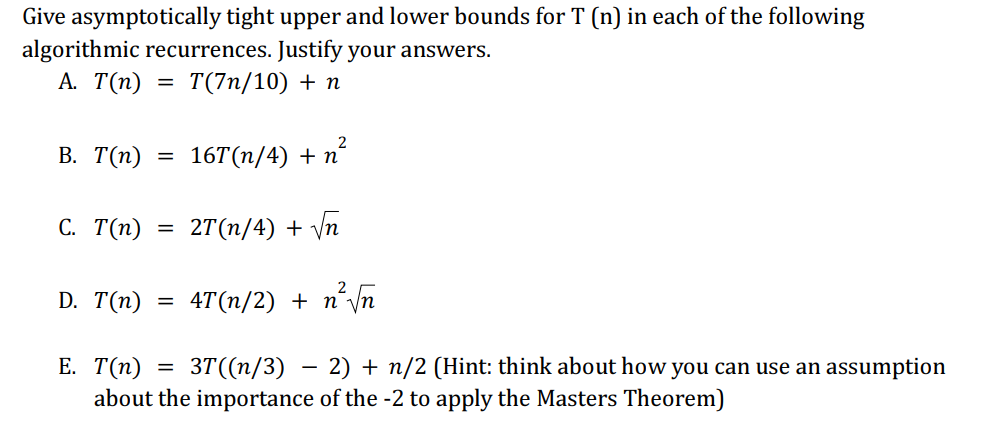
Transcribed Image Text:Give asymptotically tight upper and lower bounds for T (n) in each of the following
algorithmic recurrences. Justify your answers.
A. T(n)
= T(7n/10) + n
B. T(n)
C. T(n)
D. T(n)
=
=
=
2
16T(n/4) + n
2T(n/4) + √n
2
4T(n/2) + n²√√n
E. T(n)
= 3T((n/3) − 2) + n/2 (Hint: think about how you can use an assumption
about the importance of the -2 to apply the Masters Theorem)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning