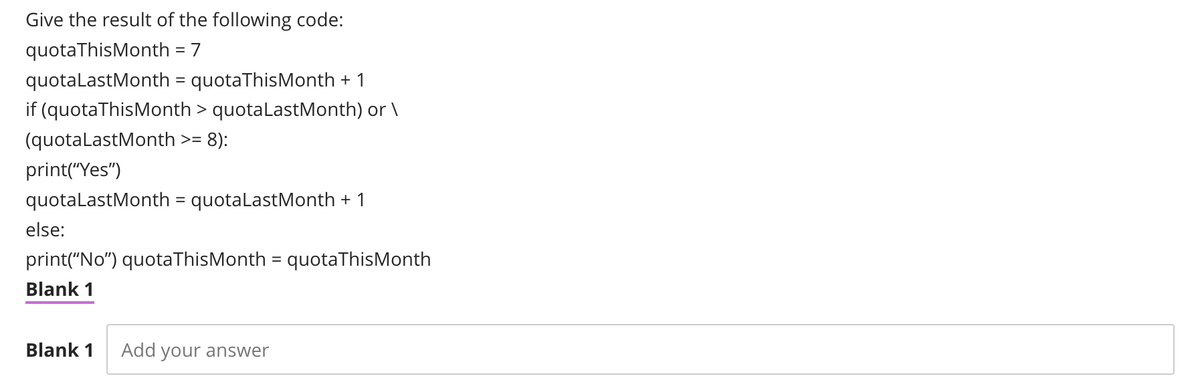
Give the result of the following code:
Q: Despite being offered a promotion to a project management job, you believe you'd be better suited to…
A: Project management : Your company rank affects your hands-oneness. As you climb, you become more…
Q: Given what we know about the Denial of Service assault on iPremier, what are the realistic next…
A: Denial of Service (DoS) assaults are on the rise, posing severe threats to cyber security in a…
Q: secure data
A: Given :- In the above given question, a statement is mention in the above given question Need to…
Q: How would you construct a 512Gbyte memory if an 8Gbyte memory chip were available?'
A: Memory: Memory is organized into structures using memory cells as the fundamental building block.The…
Q: How Can Businesses Use Cloud Services Securely?
A: - We need to talk about the use of cloud by businesses securely.
Q: In this part, we'll examine the pros and cons of a LoT versus M2M method by using a health band as…
A: The Internet of Things (IoT) is a term that refers to the network of devices that connectThe…
Q: Carry out some research on the Internet to learn about the developing trends in wireless networking…
A: Answer to the given question: Developing trends in wireless networking: Mobile edge computing…
Q: The advantages and uses of Convolutional Neural Networks should be discussed in detail.
A: In image recognition and processing, an artificial neural network known as a convolutional neural…
Q: When there are two stations visible at the same time or when one station is hidden, wireless…
A: Networking is the process of one devices are interacting with the other devices in order to share…
Q: What are some of your go-to networking strategies for workers that work remotely or wirelessly?
A: Introduction: A wireless network allows devices to stay connected to the network while remaining…
Q: There are advantages and disadvantages of using wireless networking. Because of the potential for…
A: Any computer network which is not linked by any type of cables or wires is termed as wireless…
Q: Why aren't simple file systems utilised for data processing Computer science nowadays
A: Introduction: There are various disadvantages of using file systems. That is why we now prefer DBMS…
Q: Write a program to reverse the strings stored in the following array of pointers to strings: char…
A: The complete C program is given below with code and output screenshots Two ways are given: First…
Q: List the top 10 benefits of using Artificial Neural Networks in Palestine.
A: Introduction: Artificial Neural Networks (ANNs) are a type of artificial neural network that is…
Q: Computer science education may benefit from the use of multimedia and virtual reality.
A: Introduction: Everything we see and hear in the form of text, photos, audio, video, and other…
Q: Explain the many types of data-hiding methods that provide unique challenges to law enforcement…
A: A law enforcement agency (LEA) is an organisation that enforces the law. This might refer to a…
Q: What protocol, SSL or TLS, encrypts communications between a browser and a web server?
A: Introduction: TLS and SSL are used in the HTTPS protocol.
Q: What kinds of effects do the technologies of the Internet have on the operations of a company?…
A: Business example: BOOKKEEPING: We may select accounting, marketing, manufacturing, retailing, etc.…
Q: What are the three conditions for a network to be considered successful and effective? Would it be…
A: An efficient level of performance is characterized by the ability to complete a task with the least…
Q: Using a single device to connect networks that use several protocols What does the Gateway think…
A: Intro The Gateway is a device that allows users to connect networks using several protocols with a…
Q: Why is it so difficult for businesses to migrate their operations to a platform that is hosted in…
A: Operating System: The operating system and hardware of a server physically located in a data center…
Q: What is the syntax for reading a comma separated value (CSV) file? A pd.read_csv('filename.csv") B…
A: 1. What is the syntax for reading a comma separated value csv file? B. pd.read_csv("filename")…
Q: Explain briefly, using a proof, how this computer's addressable space is determined in this…
A: The range of visible addresses the application that provides the user or the operating system…
Q: "Explain a facility's use of a physical firewall." If you require physical security measures, why…
A: The above question is answered in step 2 :-
Q: How exactly will the Internet of Things (IoT) change the way we go about our everyday lives? To back…
A: Introduction: The Internet of Things (IoT) is a networked, internet-connected collection of devices…
Q: What kind of impact does the use of a waiting line system that only has one server and one phase…
A: Given Question: What effects does using a waiting line system with just one server and one phase…
Q: Explain the importance of periodic wireless audits and the processes that should be taken as part of…
A: Introduction: Wireless auditing is a procedure of verification that is carried out by a security…
Q: Identify the five most critical parts of a computer system.
A: Five PC parts: Each of the five primary computer components has a specific role. Processor (CPU) RAM…
Q: Identify and briefly explain some of the big data problems and challenges.
A: Introduction: The term "big data" refers to the massive amounts of data, both organised and…
Q: What is a feature of static members?
A: INTRODUCTION: We need to answer the characteristic of static members.
Q: C programming for the following formation of a user defined function. Given structs #define…
A: It is defined as a general-purpose, procedural, imperative computer programming language. It has…
Q: When it comes to overseeing software development projects, there are a few key distinctions.
A: Management: Management is the display and coordination of an organization's resources and processes…
Q: What kind of technology may be used to estimate the distance between a cable's damage and the damage…
A: Introduction: While excavating equipment is frequently to blame for cable damage, hand held tools…
Q: Create a list of all of the different types of DNS records. Each one has to have a thorough analysis…
A: The solution to the given question is: Can I use hostname aliases on my company website and mail…
Q: Why is a repair manual so crucial while disassembling a notebook?
A: Introduction: Why is a repair manual so crucial while disassembling a notebook?
Q: how many distinct meanings may be derived from the data in total? How can a network prove that it is…
A: Data is set of information. There are two types of data Qualitative and Quantitative data.
Q: Detailed explanations were provided at the time. When and how will you communicate this to them?…
A: In this question we have to understand that when and how there is delay in the data sent over the…
Q: Discuss the concept competitive intelligence.
A: Competitive intelligence: competitive intelligence is an important activity within corporations,…
Q: What are computer drivers used for?
A: Introduction: The driver, also known as the device driver, creates a file that instructs the piece…
Q: Question 3 What is the output of the following code? print (lambda word, echo: word . echo ("Hey',…
A: Find the answer with reason given as below : As per company guidelines we are supposed to answer…
Q: What is the DHCP protocol's technique for detecting and correcting network errors?
A: DHCP is an application layer protocol that enables you to: Sub netmask Router Address DNS Address…
Q: Wireless apps are the best place to apply error corrections. Which of the following best describes…
A: Adjustments for errors Error correction works well with wireless applications or networks and is…
Q: 2. Write the suitable snip code using for statement to display data after user key-in as in Figure…
A: Since no programming language is mentioned, I am using c language. Code: #include<stdio.h>int…
Q: 1. Design a synchronous counter using SR Flip Flops where the binary equivalent states are changing…
A:
Q: When it comes to healthcare data breaches, what are the best procedures to follow?
A: Data breaches expose confidential, sensitive, or protected information to an unauthorized party. In…
Q: What type of evidence divides information into two distinct categories?
A: Introduction: Proof is just a technique of asserting that we know this notion is true. To…
Q: hat are the effects of multithreading on the utilisation of the central processing unit (CPU) in the…
A: Introduction: Multi-threading is a sort of parallelization in which work is divided into numerous…
Q: Smart cards are necessary for authentication in what situations, although magnetic stripe cards are…
A: Card ReaderA smart card, commonly known as an ICC (integrated circuit card), is a plastic card. A…
Q: Find all about several forms of wireless LAN.
A: Wireless LAN: In a constrained space like a house, school, computer lab, campus, or office building,…
Q: Which problems are best suited to supervised, unsupervised, or reinforcement learning? Justify your…
A: Introduction: supervised learning difficulties may be broken down into subgroups like regression and…
Step by step
Solved in 2 steps

- Write a function called daysOver that takes three arguments: a dictionary, a location (such as ‘Sydney’, ‘Adelaide’,etc) and a temperature and returns the number of days that were over the given temperature for the given location. For example, if we call the function using the line: total = daysOver(dictionaryData, ‘Adelaide’, 40) total will hold the number of days that Adelaide had a temperature greater than 40 celsius in the data. As a test, there were 54 days over 40 celsius in the data. Check that total is 54 for the example when you run your code. Use the daysOver function to print the number of days over 35 celsius for each of the following cities: 'Adelaide','Perth','Melbourne','Canberra','Sydney','Brisbane','Darwin' Which of the Australian cities has the most number of days over 35 celsius?What are the values of i and j after the following code hasbeen executed and i and j are both set to 15 before the codeis executed?i = ++j;j = i++;In c++, please. Thank you! Given a main() that reads user IDs (until -1), complete the BubbleSort() functions to sort the IDs in ascending order using the Bubblesort algorithm, and output the sorted IDs one per line. You may assume there will be no more than 100 user IDs. Ex. If the input is: kaylasimms julia myron1994 kaylajones -1 the output is: julia kaylajones kaylasimms myron1994 The following code is given: #include <string>#include <iostream> using namespace std; // TODO: Write the Bubblesort algorithm that sorts the array of string, with k elementsvoid Bubblesort(string userIDs [ ], int k) { } int main() { string userIDList[100]; string userID; cin >> userID; while (userID != "-1") { //put userID in the array cin >> userID; } // Initial call to quicksort Bubblesort(userIDList, /* ?? */ ); //make this output only the userIDs that were entered, not garbage for (int i = 0; i < 100; ++i) { cout <<…
- the code CREATE FUNCTION Calculate_Monthly_Payment( @mortage_amount BIGINT , @apr DECIMAL(18, 6) , @years INT)RETURNS DECIMAL(18, 6)ASBEGIN /* A = P (i + i (1+i) −1 n ) where: A = Monthly Payment Amount P = Principle (Initial) Mortgage Amount i = APR / 12 = Monthly Interest Rate n = years * 12 = Total Number of Payments */ -- Calculate monthly interest rate DECLARE @i DECIMAL(18, 6) SET @i = @apr / 12 DECLARE @n INTEGER SET @n = @years * 12 RETURN (@mortage_amount *@i * POWER(1+@i,@n)) / (POWER(1+@i, @n) - 1) END isn't working it shows that ERROR: syntax error at or near "@" LINE 3: @mortage_amount BIGINT ^ SQL state: 42601 Character: 48The area of an arbitrary triangle can be computed using the formulaarea = √(s(s–a)(s–b)(s–c))where the square root is applied to the entire product (Links to an external site.) and where a, b, and c are the lengths of the sides, and s is thesemiperimeter of the triangle given (Links to an external site.) by the formula:s = (a + b + c)/2 Write a void function named (Links to an external site.) triangle that computes the area and perimeter(as well as the semiperimeter which will be used to compute the area)of a triangle based (Links to an external site.) on the length ofthe sides. The function should use five parameters (Links to an external site.)—three value (Links to an external site.)parameters (Links to an external site.) that provide the lengths of the edges and two referenceparameters (Links to an external site.) that store (Links to an external site.) the computed area and perimeter respectively. Make yourfunction robust. Note that not all combinations of a, b, and cproduce a…Write a function called sumSeries that computes the following summation:?(?) =1/2 +2/3+....+i/(i+1)Write a test program that uses sumSeries to display the following table:i m(i)1 0.50002 1.1667…19 16.402320 17.3546
- Please enumerate all of the situations when invoking inline functions will not get the expected results.Consider the following function: def squareArea(sideLength) : return sideLength ** 2 What is the value of squareArea(3)? _____ a.2 b.3 c.6 d.9A teacher is compiling data and needs to find the number of B grades. A B grade is any score greater than 79 and less than 90. If the data is listed in B1 through B210, which function would count the grades correctly? a. =COUNTIFS(B1:B210,>79,B1:B210,<90) b. =COUNTIF(B1:B210,">79") c. =COUNTIFS(B1:B210,">79",B1:B210,"<90") d. =COUNTIFS(B1:B210,">79","<90")
- Teacher has prepared the result of a class containing n number of students. He wants to give the award to 3 toppers of the class. Display the Result for 3 toppers as reflected as percentage form in floating type data. Note- include class in code and write the code in C++. Please do this question . Please include class in this codeQuestion 3: Write a function that computes the ratio of vowels vs. consonants (????????????????����������������) in a given sentence. The ratio should be given as a floating-point number rounded off to two decimal places. When writing your function, be sure to appropriately cater for the following punctuation marks: apostrophes (') quotations (") full stops (.) commas (,) exclamations (!) question marks (?) colons (:) semicolons (;) Arguments: sentence (string) →→ sentence required to compute the ratio. Return: ratio (float) →→ a ratio that describes the number of vowels to consonants: vowels/consonants. ?HINT? Remember to cater for the white spaces that appear in your sentence. Expected outputs vowel_consonant_ratio("This is a random sentence!")==0.62 vowel_consonant_ratio("Thomas! Where have you been?")==0.83What will be the output of the following code snippet? #include <stdio.h> union example { long price: int quantity; float tax; }: int main() { union example val; val.price = 15; printf("%d", (int)sizeof(val)); val.quantity = 6; val.tax = 0.12; return 0; (a) 8 (b) 16 (c) 14 (d) 4











