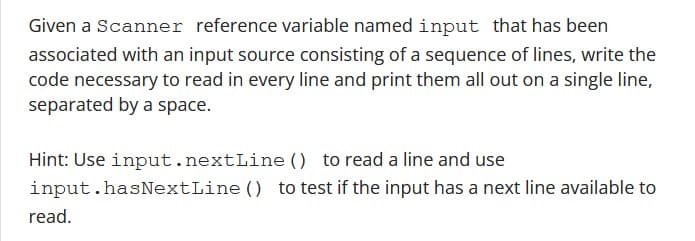
Given a Scanner reference variable named input that has been associated with an input source consisting of a sequence of lines, write the code necessary to read in every line and print them all out on a single line, separated by a space. Hint: Use input.nextLine() to read a line and use input.hasNextLine () to test if the input has a next line available to read.
Q: How would you combine your DFDs?
A: Data Flow Diagrams (DFDs) are valuable tools for visualizing and understanding the flow of data…
Q: PointSource used IBM Rational Test Workbench to find and fix a number of software bugs before…
A: IBM Rational examination Workbench is an integrated taxing solution that ropes a choice of testing…
Q: During the course of the semester, we came up with methods and the SDLC. What is the Software…
A: Software Development alludes to the most common way of designing, making, testing, and keeping up…
Q: What are the potential security vulnerabilities and mitigation strategies associated with…
A: The Internet of Things (IoT) refers to a network of interconnected physical devices, vehicles,…
Q: Give an outline of the most important parts of electronic payment methods that make online and…
A: Electronic payment methods have revolutionized the way we conduct transactions, making online and…
Q: Why do wireless networks degrade faster than cable ones?
A: Wireless networks have become an integral part of our modern society, providing us with the…
Q: Give examples of how these three measures might improve transport layer security.
A: One of the key ways to perk up transport layer safety is by ornamental encryption standards.…
Q: What kind of attention is needed? Why should a company make sure that the right safety precautions…
A: A company should pay close attention to safety precautions during normal business operations to…
Q: Local and international agents assist Mobile IP hosts.
A: Mobile IP is a communication protocol exploited to allow mobile device users to move from one…
Q: Which key on the computer is the same as the Left Menu key?
A: The contribution that is often referred to as the "Left Menu" key is additional often than not…
Q: Tell us about three ways that technology can be used to help secure the transport layer.
A: In the realm of computer networks, securing the transport layer is crucial to protect sensitive data…
Q: Operating System: Please In your own words, and clearly. A) How would you explain the concept of…
A: The critical section problem is a problem in computer science that arises when multiple processes…
Q: Who should decide where the information security job should be in the organization's hierarchy? Why?
A: The position of the information security job within an organization's hierarchy is an important…
Q: How are vertical and horizontal partitioning complementary?
A: Complementary relationship between vertical and horizontal partitioning in the context of data…
Q: Give three technical restrictions supporting transport layer security.
A: According to the information given:-We have to define three technical restrictions supporting…
Q: How would you combine your DFDs?
A: combining DFDs involves integrating multiple diagrams to provide a comprehensive representation of a…
Q: ompare and contrast the financial performance of organizations that uphold high ethical standards to…
A: In today's globalized and interconnected business environment, ethical standards play a crucial role…
Q: Before the data hack, why did Target not have a CISO?
A: 1) CISO stands for Chief Information Security Officer. A CISO is a senior executive responsible for…
Q: Write a call for ideas for an order system for the KFC mobile app.
A: KFC, a popular fast-food chain, is looking to enhance its mobile app by introducing a new and…
Q: Fairly limit what students can do. Include rules about using the internet at school, on breaks, with…
A: In educational institutions, it is essential to establish reasonable limitations on student…
Q: What does OLAP do? OLAP stands for online analysis processing.
A: A computing category known as "Online Analytical Processing" (OLAP) program allows users to analyze…
Q: Why are new systems costly and risky?
A: The happening and implementation of inexperienced systems can occur a costly undertaking anticipated…
Q: Compliant/Noncompliant Solutions The following code segment was provided in Secure Coding Guidelines…
A: The code segment reads data from a file without taking into consideration potential security…
Q: Before releasing the FIMC app, PointSource utilised IBM's rational test workbench to find and fix…
A: IBM Rational Test Workbench is a powerful technology that aids in the construction and testing of…
Q: Consider the example below that shows both the payload and the two-dimensional parity bits (shown in…
A: Digital communication: Digital communication is the process of transmitting digital data over a…
Q: Compare wireless, twisted-pair, coaxial, and fiber-optic connections.
A: In modern networking, various types of connections are used to transmit data and establish…
Q: What does a distributed lock service have to do with big data and the cloud?
A: A Distributed Lock Service is an essential component in distributed systems, which helps realize…
Q: How should a DBA maintain a DBMS after selection
A: DBA stands for Database Administrator. A DBA is a professional responsible for managing and…
Q: dictionary and six DBLC steps: what's the connection?
A: in the following section we will learn about Data dictionary and six DBLC steps: what's the…
Q: Information security personnel may have prevented the Target breach.
A: The Target breach, which occurred in 2013, was a significant cyber attack that resulted in the theft…
Q: Give more information about the technical tasks that the DBA's technical function usually takes care…
A: A Database Administrator (DBA) plays a crucial role in managing and maintaining databases within an…
Q: business intelligence (BI) and BI tools (BI tools).
A: Business intelligence (BI) is a technology-supported method that analysis data bonus provide…
Q: Why do wired networks lose speed more quickly than wireless ones?
A: A Database management system (DBMS) driver is a crucial component in managing And utilizing…
Q: "What are the key considerations and trade-offs in selecting a programming language for developing…
A: According to the information given:-We have to define the key considerations and trade-offs in…
Q: How would a regular brick-and-mortar business leverage FBA with Amazon's information systems?
A: Amazon's FBA service provide businesses the occasion to store their foodstuffs in Amazon's…
Q: How do processes on different hosts recognise each other?
A: In the realm of computer science, a procedure may stand for an tremendous instance of a Computer…
Q: What methods are used now after decades of technical advancements?
A: The saying "appliance education" (ML) and "fake aptitude" (AI) are both contraction designed for the…
Q: ests to be addressed are 82,170,43,140,24,16,189. And the Read/Write arm is at 48, and it is also…
A: In disk scheduling, the aim is to manage the order of disk I/O operations to improve overall system…
Q: Discuss the significance of ASCII codes in computer systems.
A: ASCII (American Standard Code for Information Interchange) codes are a widely used character…
Q: How do you connect endpoint and infrastructure devices in a LAN? Which cable would link the two…
A: Setting up a Local Area Network (LAN) involves interconnecting various devices such as computers,…
Q: How do you organise data entering data?
A: The process of organizing data when entering it into a system is crucial for efficient data…
Q: If you could customise a dashboard for your organisation, what data would you include?
A: When customizing a dashboard for an organization, the choice of data to include would depend on the…
Q: How can staggered reduce rotational latency using the disc metaphor?
A: What is rotational latency using the disc metaphor: Rotational latency, in the disc metaphor, is the…
Q: PointSource fixed many software issues before starting the FIMC app using IBM's logical test…
A: IBM's Logical Test Workbench (LTW) is a comprehensive testing and analysis tool that provides…
Q: How would a regular brick-and-mortar business leverage FBA with Amazon's information systems?
A: According to the information given:-We haev to define a regular brick-and-mortar business leverage…
Q: Laws provide information security requirements, whereas ethics provide ethical principles. Privacy…
A: In the digital age, the protection of information and privacy has become a crucial concern. To…
Q: Is it possible to start a business in Malaysia right now?
A: Starting a business can be an exciting and potentially rewarding venture, but it is important to…
Q: How do the home agent and the foreign agent work together to handle Mobile IP hosts?
A: According to the information given:-We have to define the home agent and the foreign agent working…
Q: The invisible web: how big?
A: As we navigate the expansive realm of the internet, it's easy to assume that search engines have…
Q: If you could create your own company screen, what information would you put on it?
A: Key information that could be included on a company screen, which serves as a digital display to…
Java code
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images

- I need help fixing this code so that it can print outputs described in the image below: import java.util.Scanner; public class LabProgram { public static void main(String[] args) { Scanner scnr = new Scanner(System.in); int currentPrice; int lastMonthsPrice; double mortgage; currentPrice = scnr.nextInt(); lastMonthsPrice = scnr.nextInt(); mortgage = (currentPrice * 0.051) / 12; System.out.println("This house is $" + currentPrice + ". The change is -100000 since last month."); System.out.println("The estimated monthly mortgage is $" + mortgage + "."); }}Using modulus operator (%), Create a java program that will convert an input time(integer in seconds) to its equivalent in Hours, Minutes, and seconds Using BufferedReader to get input from the user, and System.out to output theresultI have a difficult task that i have been given, the problem is that I just simply cant seem to manage to first print a binary number so if you give me six my code doesnt seem to print the number in binary. but also i need to print it in reverse and my code just doesnt seem to work with that. heres my code import java.util.Scanner; public class LabProgram { public static void main(String[] args) { int x; int output; int i; Scanner input = new Scanner(System.in); x = input.nextInt(); output = x; for ( i = 0; i <= x; i = ++i){ output = x / 2; System.out.println(output); } } } // and bellow this are my instructions . what am i doing wrong what am i missing? ive googled sites and erased portions of code, put in eithers. ive switched back and forth from a for loop to a while loop for awhile now Write a program that takes in a positive integer as input, and…
- Create a JAVA program to input integer greater than zero (0) and not more than four digitinteger using 'JOptionPane Method' and display how many digit/s inputted by theuser.If your sample inputs are not within the range or out of range, the message outputwill be “You entered an invalid input”. See attached image for the sample output.Create a Java program to input integer greater than zero (0) and not more than four digitinteger using JOptionPane method and display how many digit/s inputted by theuser. If your sample inputs are not within the range or out of range, the message outputwill be “You entered an invalid input”. See Attached image for the sample output.I need help with this java problem so it can output like this in the image attached: import java.io.FileInputStream;import java.io.FileOutputStream;import java.io.IOException;import java.text.DecimalFormat;import java.util.Scanner; public class LabProgram { public static void main(String[] args) throws IOException { Scanner scnr = new Scanner(System.in); // Initialize variables for calculating exam averages int count = 0; double sumMid1 = 0, sumMid2 = 0, sumFinal = 0; // Initialize FileOutputStream for output FileOutputStream fos = new FileOutputStream("report.txt"); // Prompt for the filename System.out.print("Enter the name of the TSV file: "); String fileName = scnr.nextLine(); FileInputStream fis = null; try { fis = new FileInputStream(fileName); // Read the file and build the content string StringBuilder sb = new StringBuilder(); int ch; while…
- Write a program that displays the classic BINGO game, displays a BINGO card (5x5 square), and tests the bingo card for a winner via 2 users Steps: 1- Ask user 1 to enter 24 numbers between 10-40 no duplicates / check for range and repetition 2- Ask user 2 to enter 24 numbers between 10-40 no duplicates / check for range and repetition 3- Design 2 BINGO cards as you see below 4- Distribute the numbers onto the 2 cards with each user input with 0 in the middle 5- Display the 2 cards in 1 screen as you see below 6- Generate a random number between 10-40 no duplicates / check for range and repetition 7- Compare the random number with the numbers on the 2 cards 8- If the random number matches any number on each card, change the number on the card to 0 9- Check for winning cards 5 numbers in a row or column = 0 5 numbers in a diagonal = 0 all 4 corners of the card = 0 if any of the players won, display who is the winner and exit the program if the 2 players won, display both are the…Write a program which accepts an integer n and checks whether the input number n is in the range from 4 to 17; inclusive. If the integer is not in the given range, then it asks the user to enter the integer again. It then calculates the sum of all integers from n to n3 and prints out the result. Paste your complete code together with a screenshot using the sample input. Sample input: 30 Value is not in range, try again: 6 The sum of integers from 5 to 6^4 = 8000Write a program that coverts a zip code to a bar code. The bar codes use large and small bars. We will use : as a small bar and | as a large bar. Each digit has its own bar pattern. 1 is :::|| 2 is ::|:| 3 is ::||: 4 is :|::| 5 is :|:|: 6 is :||:: 7 is |:::| 8 is |::|: 9 is |:|:: 0 is ||::: The barcode also includes a check digit. The final digit added to the bar code verifies the previous numbers are correct. To Determine the checksum: Add all the digits together Determine what needs to be added to make the total a multiple of 10 The bar code also always starts and ends with a large bar. This is used by the scanner to align the letter. Drexel's Zip Code is 19104 The check digit is 5. The sum of the digits is 1+9+1+0+4 = 15. To make 15 a multiple of 10, we need to add 5. The bar code will be |:::|||:|:::::||||::::|::|:|:|:| The majority of work in this problem is done by digit. It makes sense to store the zip code as a string, not as an integer. Write the function checksum(zip)…
- Write a program that coverts a zip code to a bar code. The bar codes use large and small bars. We will use : as a small bar and | as a large bar. Each digit has its own bar pattern. 1 is :::|| 2 is ::|:| 3 is ::||: 4 is :|::| 5 is :|:|: 6 is :||:: 7 is |:::| 8 is |::|: 9 is |:|:: 0 is ||::: The barcode also includes a check digit. The final digit added to the bar code verifies the previous numbers are correct. To Determine the checksum: Add all the digits together Determine what needs to be added to make the total a multiple of 10 The bar code also always starts and ends with a large bar. This is used by the scanner to align the letter. Drexel's Zip Code is 19104 The check digit is 5. The sum of the digits is 1+9+1+0+4 = 15. To make 15 a multiple of 10, we need to add 5. The bar code will be |:::|||:|:::::||||::::|::|:|:|:| The majority of work in this problem is done by digit. It makes sense to store the zip code as a string, not as an integer. Write the function checksum(zip)…Java Program ASAP Please pay attention to the screenshot for test case 2 and 3 and please make sure you match the result. Modify this program so it passes the test cases in Hypergrade becauses it says 5 out of 7 passed. import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.ArrayList;import java.util.Arrays;import java.util.InputMismatchException;import java.util.Scanner;public class FileSorting { public static void main(String[] args) { Scanner scanner = new Scanner(System.in); while (true) { System.out.println("Please enter the file name or type QUIT to exit:"); String fileName = scanner.nextLine(); if (fileName.equalsIgnoreCase("QUIT")) { break; } try { ArrayList<String> lines = readFile(fileName); if (lines.isEmpty()) { System.out.println("File " + fileName + " is empty."); } else {…Write a program, reading the temperature data from an input file, translating them to another temperature scale by the choice of user (F2C, C2F, K2C, C2K, K2F, F2K) and writing the calculated temperature values in output file. it is input file and output file java code . i am giving you the code you need to implement the code with I/O file import java.util.Scanner; public class Lab15{ public static void main(String[] args) { Scanner Keyboard = new Scanner(System.in); double Frahenhite, Celsius, Kelvin ; int input = 1;while (input==1){for (int i = 1; i<=2; i++) { System.out.println("Choose an option"); System.out.println("FTC - Fahrenheit to Celsius"); System.out.println("CTF - Celsius to Fahrenheit"); System.out.println("FTK - Fahrenheit to Kelvin"); System.out.println("KTF - Kelvin to Fahrenheit"); System.out.println("CTK - Celsius to Kelvin"); System.out.println("KTC - Kelvin to Celsius");…

