Given a string, write a method to find the first non-repeating vowel (a, e, i, o, u) in it and return its index. If it doesn't exist, return -1. Assume that all the characters of the String is lowercase. Do not use String class functions other than charAt() and length() You can also try to solve with Map data structure like using a Map variable.
Q: As a result of recent advancements in technology, almost all of today's appliances that are designed…
A: Introduction: By utilising technical advancements, you may streamline your operations, increase…
Q: Have you ever seen someone being harassed or bullied by someone else over the internet? When you…
A: Have you ever seen someone being harassed or bullied by someone else over the internet? When you…
Q: Which one is superior, and why do we still need both packet and circuit switches in the 21st century…
A: Packet and Circuit Switches: The two different switching techniques used to connect numerous…
Q: A name has this scope if it is declared in the function parameter list of a function declaration…
A: In function prototype, we specify name of the function, return type of function, types of…
Q: CYB/405 **Who are the stakeholders although there may be multiple for some** Who are the KEY…
A: Key stakeholders for each plan and practices are given below
Q: How can you aid in preventing internal and external threats?
A: Threat: A threat is nothing but a suspicious or malicious activity they can damage the sensitive…
Q: There are a total of three user processes in an operating system, and each of these processes…
A: In an operating system, there are three user processes, and each of these processes requires two…
Q: market place and may be used to provide network security.
A: Introduction: A “firewall” is designed to protect computers from harmful intrusions. Wireless…
Q: Project 6: You have to create a program in Clanguage in which the user enters the mass mand radius…
A: We need to write a C code for the given scenario.
Q: What is the most significant distinction between holding the copyright to a piece of software and…
A: The legal phrase for stating and demonstrating who owns intellectual property is "copyright" (the…
Q: The availability of flexible multiprocessor systems is one of the most significant advantages that…
A: The usage of many processors in close proximity to one another is supported by multiprocessing…
Q: I was wondering if you could perhaps walk me through the fundamentals of how a cache hierarchy is…
A: The answer of the question is given below
Q: Project 6: You have to create a program in C language in which the user enters the mass m and radius…
A: Moment Of Inertia for a Circular Disc: The tendency of a body to resist change or moment of inertia…
Q: For instance, you might safeguard the network in your house by using personal firewalls and network…
A: In this question we have to discuss about the multiple different kinds of precautions that may be…
Q: What happens to employees not following the security policy? An employee found to have violated this…
A: Introduction to security policy An organization's security policy is a written document that…
Q: Which two kind of wireless technology are used the vast majority of the time
A: Please find the answer below
Q: Could you perhaps elaborate on what you mean by the term "principle of non-repudiation"? Thank you…
A: Introduction An assertion's non-repudiation status gives a confirmation that it can't be refuted in…
Q: you have to create a program in C language in which the user enters the mass M and radius L of a…
A: Algorithm: 1. Read mass, m. 2. Read radius, r. 3. moment_of_inertia = (m * r * r) / 2. 4. Print…
Q: I would be grateful if you could provide a detailed explanation of the reason (or reasons) why my…
A: The answer of the question is given below
Q: You have to create a program in C language in which the user enters the mass m and radius of a…
A: Algorithm: 1. Read mass, m. 2. Read radius, r. 3. moment_of_inertia = (m * r * r) / 2. 4. Print…
Q: If you could perhaps describe the three tenets that serve as the foundation for integrity, it would…
A: The question has been answered in step2
Q: Provide at least three reasons why the spiral model is preferable to the waterfall technique, and…
A: A set of computer activities that are dedicated to create, design, deploy and the support the…
Q: Why is it so important to stop criminal acts from being perpetrated online?
A: Today, data and information are precious in the global economy; thus, cybercrime is rising. Cyber…
Q: • Create a dictionary with at least five key-value pairs. Use strings for either the keys, the…
A: Below I have provided Python Programming. Also I have attached the screenshot of the code and output…
Q: Are you in agreement with the statement that was made by Mukherjee, which argues that an approach to…
A: Human rights : These rights are inherent to all human beings, sex, nationality, ethnicity, and…
Q: You have to create a program in C language in which the user enters the mass m and radius of a…
A: Algorithm: 1. Read mass, m. 2. Read radius, r. 3. moment_of_inertia = (m * r * r) / 2. 4. Print…
Q: Write a program to read the values of the monthly water consumption for two months and display the…
A: Below I have provided C++ Programming. Also, I have attached the screenshot of the code and output…
Q: In what ways would it be feasible to tell whether or not the operating system of a laptop has been…
A: Operating System: An operating system (OS) is the programme that manages all of the other…
Q: Diagrams may be used to illustrate the differences between scalar processors and superscalar…
A: Scalar and superscalar processors are two of the numerous hardware options for computer processors.…
Q: mentioned in the presentation, and how would you explain its functionality to someone who has never…
A: Introduction: Below describe the name of the non-free Linux firewall that was mentioned in the…
Q: Which two sorts of technology can be found in almost all wireless networks used in today's world?
A: Wireless technology These days, wireless technological frameworks have been one of the fundamental…
Q: Please do question d and e. It follows from a, b and c
A: Answer d: ============================================================================ initially we…
Q: In order for a network to perform its functions in the most efficient manner, what are the three…
A: In order for a network to perform its functions in the most efficient manner, we need to find the…
Q: Authentication of messages may take done using a wide number of distinct approaches.
A: Authentication of messages:- Authentication of message is another form of security. It ensures…
Q: What are the key functions that a firewall is responsible for?
A: A Firewall : It is defined as a cybersecurity tool that monitors incoming and outgoing network…
Q: In accordance with whatever provisions of the law is it permissible to make use of a particular…
A: Definition: According to the UM Copyright Guidelines, it's common practise to copy…
Q: There are a few issues with the superscalar processor that need maintenance as soon as it is humanly…
A: Scalar processors and super scale processors are differ in the way of use of illustrative instances.…
Q: Why is it so important for people to have a working knowledge of spreadsheets in the current…
A: A spreadsheet program allows storing the data in the tabular format i.e. in rows and column…
Q: A name fined in file/namespace scope. It can be referenced by name only thin the same translation…
A: In computing the namespace which refers to the set of signs that are usually used to identify and in…
Q: Data that has been saved in memory may be retrieved using one of two unique methods: either…
A: Given: The two approaches for finding data in memory are sequential and direct access. However, most…
Q: Q9 A Python program to find the duplicate element in an array data is shown in Figure Q9, complete…
A: Below I have provided Python Programming. Also, I have attached the screenshot of the code and…
Q: 7. Show that, CFLTM = {(M) | M is a TM and L(M) is a context free language } is undecidable.
A:
Q: You have to create a program in C language in which the user enters the mass m and radius R of a…
A: Algorithm: 1. Read mass, m. 2. Read radius, r. 3. moment_of_inertia = (m * r * r) / 2. 4. Print…
Q: Question Use the LOGISTIC regression option to find a logistic growth model that best fits the data…
A:
Q: ~31. Given the following numbers in array A 18 47 29 30 32 50 40 43 35 24 ... what is the contents…
A: let's see the correct answer of the question
Q: Investigate the ways in which wireless networks are influencing the growth of nations that are still…
A: Given: A type of computer network known as a wireless network links network nodes by use of wireless…
Q: What precisely is the purpose of a firewall system, particularly one that is regarded as being of…
A: Specify the objective of the firewall system. NOTE: Because you have posed many inquiries, we will…
Q: Data that has been saved in memory may be retrieved using one of two unique methods: either…
A: Sequential and direct memory access are two strategies for locating data. However, significant…
Q: using uml make the sequence diagram and the collaboration diagram of the following case: USE CASE…
A: The question has been answered in step2
Q: Suppose a list contains marks earned in the courses CSE110, PHY111, and MAT110 of each student…
A: Here I have defined a custom method named sortDict() that takes a dictionary as an input parameter…
Use Java
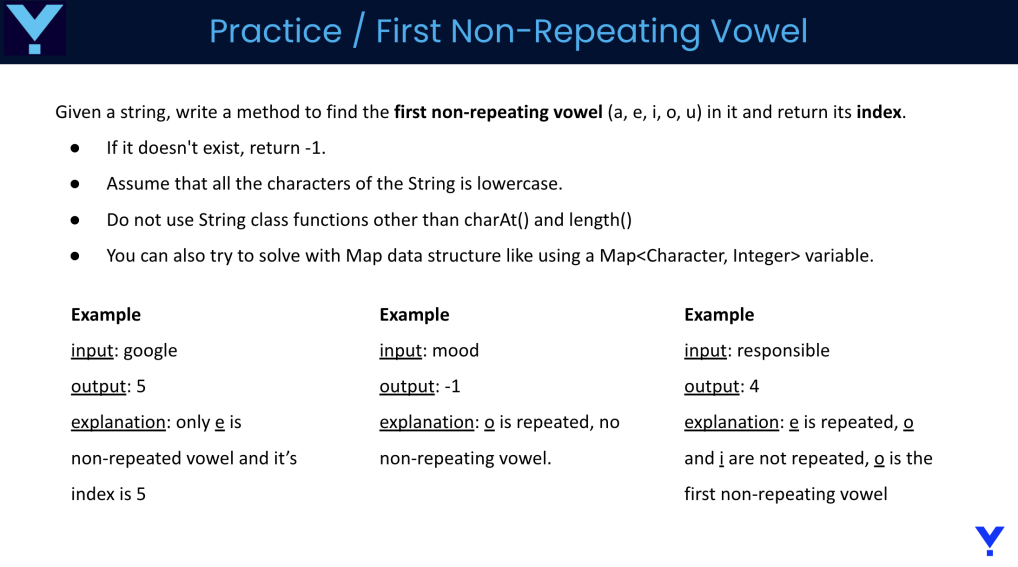
Step by step
Solved in 2 steps with 1 images

- Write the value_equality method.Given the two expressions ? and ?, first compute the set of variables ? that appear in either ? or ?. Then, the idea consists in performing num_sample times the following test for equality: First, produce a variable assignment (a dictionary) mapping each variable in ? to a random value. Choose these random values from the gaussian distribution centered around 0 and with standard deviation 10 (for instance; any continuous distribution with infinite domain would work). You can obtain such numbers using random.gauss(0, 10). Then, compute the values of ? and ? with respect to that variable evaluation. If the values are closer than a specified tolerance tolerance, you consider ? and ? equal (for that variable valuation). Otherwise, you can stop and return that ? and ? are different. If you can repeat the process num_sample times, and ? and ? are considered equal every time, then you declare them equal. WRITE CODE IN PYTHONImplement a function called tautology? that takes as input a fully parenthesized formula and returns true if it is a tautology and false otherwise. As was the case in the previous lab, the formula will contain at least one set of parentheses for each operator, but may contain more. The best strategy for doing is to use an insight called Quine's method. It is based on the observation that if a formula, such as (p or (not p)), is a tautology, the result of substituting p with true is a tautology and the result of substituting p with false is also a tautology. This implies a computational strategy: to evaluate whether a formula F is a tautology1. Collect all of the propositional variables.2. Substitute every occurrence of the first variable with #t and every occurrence ofthe same variable with #f3. Make two recursive calls to Tautology? “And” the results.4. When all possible substitutions have been made, i.e., the formula contains onlytruth values, evaluate the formula and return the…Implement a function called tautology? that takes as input a fully parenthesized formula and returns true if it is a tautology and false otherwise. As was the case in the previous lab, the formula will contain at least one set of parentheses for each operator, but may contain more. The best strategy for doing is to use an insight called Quine's method. It is based on the observation that if a formula, such as (p or (not p)), is a tautology, the result of substituting p with true is a tautology and the result of substituting p with false is also a tautology. This implies a computational strategy: to evaluate whether a formula F is a tautology 1. Collect all of the propositional variables. 2. Substitute every occurrence of the first variable with #t and every occurrence of the same variable with #f 3. Make two recursive calls to Tautology? “And” the results. 4. When all possible substitutions have been made, i.e., the formula contains only truth values, evaluate the formula and return…
- solve in C please. Implement the following two functions that get a string, and compute an array of non-emptytokens of the string containing only lower-case letters. For example:● For a string "abc EFaG hi", the list of tokens with only lower-case letters is ["abc", "hi"].● For a string "ab 12 ef hi ", the list of such tokens is ["ab","ef","hi"].● For a string "abc 12EFG hi ", the list of such tokens is ["abc","hi"].● For a string " abc ", the list of such tokens is ["abc"].● For a string "+*abc!! B" the list of such tokens is empty.That is, we break the string using the spaces as delimiters (ascii value 32), and look only at thetokens with lower-case letters only .1. The function count_tokens gets a string str, and returns the number ofsuch tokens.int count_tokens(const char* str);For example● count_tokens("abc EFaG hi") needs to return 2.● count_tokens("ab 12 ef hi") needs to return 3.● count_tokens("ab12ef+") needs to return 0.2. The function get_tokens gets a string str, and…Please implement in Java implement a keyed bag in which the items to be stored are strings (perhaps people’s names) and the keys are numbers (perhaps Social Security or other identification numbers). So, the in- sertion method has this specification: public void insert(String entry, int key);// Precondition: size( ) < CAPACITY, and the // bag does not yet contain any item// with the given key.// Postcondition: A new copy of entry has// been added to the bag, with the given key. When the programmer wants to remove or retrieve an item from a keyed bag, the key of the item must be specified rather than the item itself. The keyed bag should also have a boolean method that can be used to determine whether the bag has an item with a specified key. In a keyed bag, the pro- grammer using the class specifies a particular key when an item is inserted. Here’s an implementation idea: A keyed bag can have two private arrays, one that holds the string data and one that holds the corresponding…def reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('ATest string!')'A!gnirts tseT' """ do it on python, and do not use any list, import or split, or append or join.
- def reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('watchNow')'watchwoN' >>> reverse_sentence('hot')'hot' """ do it on python, and do not use any list, import or split, or append or join.def reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('ATest string!')'A!gnirts tseT'""" passdef reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('ATest string!')'A!gnirts tseT' """
- Complete the method below that prints all elements that are in both Set<String> s and Set<String> t. Each matching element should be followed by a space. What can I change to make it work? import java.util.Set;import java.util.Iterator; public class Sets{ public static void printMatches(Set<String> s, Set<String> t) { System.out.print("{ "); while(in.hasNext()){ String next = in.next(); { if((s.contains(next))&& (t.contains(next))){ System.out.print(next+" "); } } System.out.println("}"); }} import java.util.Set;import java.util.TreeSet;import java.util.Arrays; public class SetsTester{ public static void main(String[] args) { Set<String> set1 = new TreeSet<>(Arrays.asList("Bob", "Bill", "Sally")); Set<String> set2 = new TreeSet<>(Arrays.asList("Sam", "Bob", "Frank")); Sets.printMatches(set1, set2);…The map file holds a bunch of rectangles. Some of the rectangles are solid, and you can think of them like crates in a warehouse. They can be enclosed by a non-solid rectangle, and those rectangles are just there to make theintersection testing and such go faster. If a line doesn't cross a non-solid rectangle, then it cannot hit any rectangle inside it. Nice! The format is:Solid(1)/Nonsolid(0) x_min y_min x_max y_max (list of children iff not solid) The list of children are line numbers (the lines start at 0) of solid rectangles inside the non-solid rectangle. Solid rectangles do not have children. All non-solid rectangles must have children. Here's a sample file:0 0 0 100 100 1 21 1.1 1.0 1.2 1.31 10 10 11 110 50 60 70 80 40 55 65 65 75 51 56 66 64 74 The first line (line 0) is a non-solid rectangle with two children (the next two rows, lines 1 and 2). The first rectangle ranges from (0,0) to (100,100). The children of it are both small solid rectangles, the first is only .1 x .3,…Improve the given code below, make sure that the code will require input from the user. Problem: Write a JavaScript function that would accept a string and return the reverse of that string. const reverse = (str) => {const arr = []; //stores character in rev orderconst len = str.length; //finds the length of the stringlet i;for(i = len; i >= 0; i--)arr.push(str[i]); //adds the chars of str to arrreturn arr.join('');} let stringTest, reverseString; //for dummy stringstringTest = "john gabriel";reverseString = reverse(stringTest); console.log("Num3");console.log(`Reverse of the string "${stringTest}" is: "${reverseString}"`);console.log("\n");

