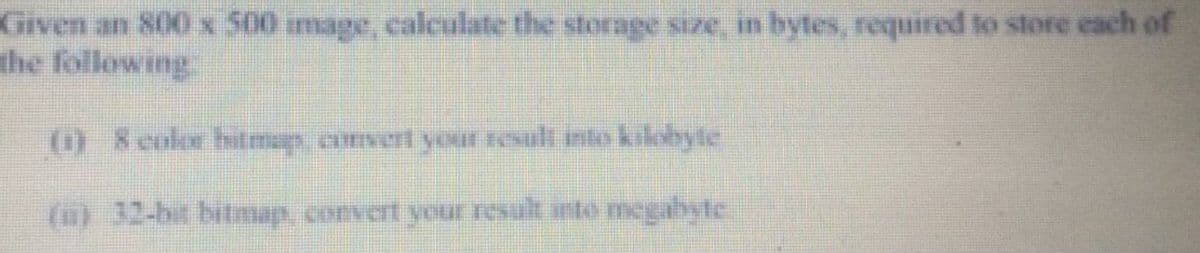
Given an 800 x 500 image, calculate the storage size, in bytes, required to store each of the following () 8 color bhitmap, convert your result into kilobyte (u) 32-bit bitmap, convert your result into megabyte
Q: 18. What are the values of the following Python expressions? 2**(3**2) (2**3)**2 2**3**2 a) 512, 64,...
A: We are given 3 python statements and we are going to find out the output produced by them. I am also...
Q: What exactly does parallel computing imply?
A: EXPLANATION AND ANSWER: Parallel computing: It is a type of computing architecture that uses multipl...
Q: Show that the dual of the max flow problem has always an integer optimal solution.
A: The maximum flow issue can be expressed as follows: Given a network G = (N, A) and two nodes s (sour...
Q: It is necessary to employ critical sections in uniproce
A: Q)It is necessary to employ critical sections in uniprocessor systems in order to preserve shared me...
Q: An organization has issued metal keys to its employees and has recently suffered some after hours em...
A: A keycard is defined as a security token which will grant access through electrically-powered doors....
Q: Is a microoperation the same as a machine instruction in terms of meaning?
A: The Answer is in step2
Q: Explanation of the distinctions between data and address buses, as well as control buses
A: Introduction: The address bus and data bus are distinguished because the address bus is used to tran...
Q: The reason of diskthrashing is not known. What measures can you take to mitigate its consequences?
A: Introduction: A process thrashing is described as a condition in which a process spends most of its ...
Q: What function does this feature play in dispute resolution in the DBMS component?
A: Introduction: Database management systems provide a lot of advantages, but they're also expensive an...
Q: Explain why compilers utilise parsing methods that are only effective on a subset of all grammars in...
A: Introduction: The parser is the compiler step that accepts a token string as input and translates it...
Q: Write a python code to generate the pattern as shown in the figure below:
A: The program is written in Python. Check the program screenshot for the correct indentation. Please c...
Q: Implement the Gauss-Seidel Method. Iterate until the relative approcimate error is less than 0.00001...
A:
Q: Create a JavaScript Arrow function that meets the following requirements: • Authored using arrow e...
A: Algorithm: Start Implement a arrow function named _replaceCharacter that takes a string s as an arg...
Q: nsider a hypothetical hardwired control unit which support four atrol signals S0, Si, s2, s3 and thr...
A: Here in this question we have given a hypothetical hardwired control unit.which support four signal ...
Q: What exactly is ASCII and how did it come to be?
A: Ans: ASCII that is stands for the American Standard Code for Information Interexchange that is a sta...
Q: Following the Learning Analytics Reference Model developed by Chatti et al., what are the many goals...
A: Learning analytics goal.
Q: Computer science What are the drawbacks of working with uncertified software engineers?
A: Who is a software engineer? Software engineering is the study of the development, administration, an...
Q: What is the most widely used programming language for server-side web scripting?
A: PHP is the most popular language for server-side web scripting
Q: So, what exactly is the difference between a static and a dynamic website?
A: Given: Dear student we need to explain about what is exactly difference between a static and a dynam...
Q: What role does Amazon Web Services play in the support of Netfilx as an information management syste...
A: Introduction: AWS's support for Netflix is as follows:Netflix is the world's largest internet televi...
Q: A(n) _________________ is a classification of an element based on its status or use. A) pseudo-clas...
A: The correct answer will be Option(A) Pseudo-class Explanation:- Pseudo-class is used in a classifica...
Q: Discuss the Process Management of Apple iOS version(15) Mobile Operating System
A: iOS (Originally iPhone OS) is a mobile operating system developed and distributed by Apple inc. Orig...
Q: Logic Gates: Discussion on each operations of the gates And thank you
A: Logic Gates: A logic gate is a computer model or a physical electrical device that implements a Boo...
Q: Question 3 In the machine language instruction F358, what are the operands? Fand 35
A: Find the answer with explanation given as below :
Q: the employee table containing five columns - "Id","Name", "Salary","Designation" and "Experience" in...
A: Lets see the solution.
Q: What are the four most typical issues linked with inefficient data administration?
A: Introduction: Data are unprocessed facts and numbers that may be analyzed to provide knowledge and i...
Q: Describe the set architecture's protection and instruction mechanisms.
A: EXPLANATION AND ANSWER: Instructions of set architecture: It is referred to as computer architecture...
Q: Address Hex dump 021BA128 01 02 03 04 05 06 07 08 ASCII 021BA130 09 29 20 69 6E 20 73 74 .) in st 02...
A: The answer is
Q: le: 15, 20, 35, 10 *1/5 Out R
A: in rule: 15, 20, 35, 10 *1/5 Out Rule?
Q: Simplify the equation to a)sum of product b)product of sum F=(x, y, z)=Σ(0,1,4,5,6);d(2,3,7)
A: We are given a Boolean function and we are going to find out its SOP (sum of product) and POS(produc...
Q: What should a data governance scheme include?
A: Introduction: The data governance framework addresses corporate rules and policies, data quality and...
Q: E Give a result to the algorithm Start K-1 Sum-0 Sum-Sum + K No K>10 Ves Print Sum
A:
Q: Convert each of the following decimal values to 8-bit two’s complement binary: i) -3810 ii) 551...
A: Introduction Convert each of the following decimal values to 8-bit two’s complement binary: i) -3...
Q: Define dirty read, nonrepeatable read, and phantom read.
A: Dirty Read A dirty read occurs when one transaction is changing the record, and therefore the other...
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A:
Q: What Ethernet cabling category is most suitable in supporting 10GB/s transfer speeds? O Cat 7 Cat 3 ...
A: Here in this question we have given some ethernet cabling category and we have asked that which is m...
Q: Under the heading "Components of Information Technology," discuss the many components of information...
A: Answer the above questions are as follows:
Q: Write an R program, using the corrgram library, to plot the Average_Daily_Traffic_Counts.csv dataset...
A: 5. answer import matplotlib.pyplot as plt import numpy as np import pandas as pd data = pd.read_c...
Q: What is the Big-O complexity of the following function: f(n^2 + 100n + 15712958) Choose the foll...
A: INTRODUCTION: One of the most basic methods for computer scientists to assess the cost of an algori...
Q: Convert 1110.0112 to decimal.
A:
Q: CRC (Cyclic Redundancy Check) is done at this layer of the OSI model: Session Physical Application O...
A: Cyclic redundancy Checking known as CRC is present at data link layer which is used for detecting th...
Q: What are the steps taken during a security incident response
A: Steps taken during a security incident response are
Q: What exactly is the goal of concurrency control?
A: Purpose of Concurrency Control Concurrency controls prevent data integrity problems, which can aris...
Q: Write a C++ program that will display a menu consisting of 3 brands of soda, 3 kinds of sandwiches, ...
A: 1)Start 2)Display the menu 3)Ask user for input 4)Based on the input calculate total bill and dis...
Q: What is the length of an IPv6 address in terms of bits?
A: Given Length of IPv6 in term of bits.
Q: What exactly are bignums? Which languages are they compatible with?
A: It is a tool that is used to represent the code for the value of the integer which contains a very l...
Q: Use c++ programming language: Write a program that prompts the user to input the amount of money th...
A: Answer : Below are the CPP code with output in step 2
Q: benefits and drawbacks of cosmos db
A: Introduction: The following benefits are associated with the use of the Cosmos database: A multi-mod...
Q: Use the concept split delimited string array for c# code
A: using System; namespace SplitString { class HelloWorld { static void Main(str...
Q: What is the most appropriate selection measure for CART algorithm? Answer Choices: a) Information ga...
A: Correct option. Gini index - Gini index is the most appropriate selection measure for CART algorit...
Step by step
Solved in 3 steps with 2 images

- Given an 800 x 500 image, calculate the storage size, in bytes, required to store each of the following: 8 color bitmap, convert your result into kilobyte and 32-bit bitmap, convert your result into megabyte.Given the 3-bit 4x4 pixels image f(x,y) below, rescale the range of pixel values of f(x,y) so that they can be represented by 2 bits. What is the resulting image?An 8-bit pixel takes up one byte of computer space; one kilobyte is 1024 bytes; one megabyte is 1024 kilobyte. How large is a Landsat Thematic Mapper image in Megabytes knowing that each image includes 7 bands of 6,000 columns x 6,000 rows coded on an 8-bit pixel per band?
- Calculate the storage size of image ( uncompressing ) in Gbyte for each True Color image, Note that the dimensions of image 512 X3 512An image of size (1200×628) pixels, how many KB are required to store this image? 320KB 750.2KB 300 KB 735.9KBThis is a ____ mega pixels picture. Based on the same image file properties screen shown in previous question, the size of the file saved without compression would be ____ MB (Megabytes).
- Given a 512 x 512 image, calculate the number of bytes required for its pixel storage for a) A grey scale image of 256 grey levels. b) A true color image of three bytes per pixelConsider a color image with 6x8 pixels. R, G, and B components are stored with 8 bits. There are 2^n distinct colors in the image and each pixel is stored with n bits in index color format. What is the MAXIMUM value of n that makes index color format more advantageous than RGB color format?Converting an image to grayscale simplifies the algorithm and reduces computational requirements prior to extracting the image features. Assume a given colour digital image has a size of 300 by 400 pixels, and a colour depth of 8 bits per primary colour. Calculate the total bits per pixel (bpp) and the size of this image file in bytes with disregard to the image compression type. Provide a short explanation on the calculation.
- I need help please with a multimedia software system, Please. Got confused and need help, please. Regards 1) Let's consider one 300×240300×240 24-bit color image. Please fill in the number of quantized indexes for this image using these specified quantization methods in the following table:How many bits does it take to store an uncompressed 1,200 X 800 RGB color image? If we found out that the image actually takes only 2.4 Mbits, what is the compression ratio?If the image contains 800 x 600 pixels, with RGB coloring system, how many megabytes are required to store this image as a bitmap inside the computer?

