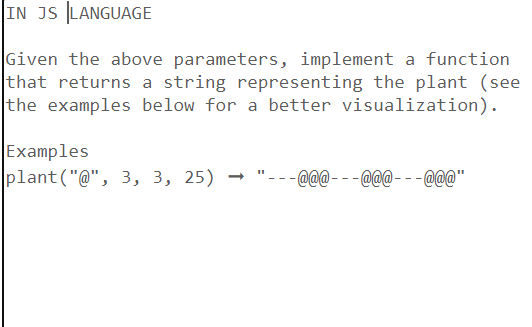
Given the above parameters, implement a function that returns a string representing the plant (see the examples below for a better visualization). Examples plant("@", 3, 3, 25) → "@@@@@@---@@@"
Q: What distinguishes the ARM and Core i3 architectures most significantly? ARM:
A:
Q: What is Linux used for, and how does it function on mobile devices?
A: Introduction: Android is a without doubt one of the most popular Linux-based technologies of all…
Q: Code a JavaScript function as per following specifications: The function is to accept two…
A: function randomIntFromInterval(min, max) { // min and max included return…
Q: Describe three situations where a real-time operating system may be beneficial.
A: An operating system is the program that, after being initially loaded into the computer by a boot…
Q: How much memory is required to store a single letter of the alphabet or a single tiny number?
A: Memory: Memory is the storage space where the data to be processed are stored. Memory is divided…
Q: List the similarities and differences between smartphones, PDAs, and portable media players and…
A: A smartphone is a cell phone with an operating system and more sophisticated networking and…
Q: What are the advantages of using CUDA and graphics processing units (GPUs) for computing?
A: CUDA has a number of benefits over conventional general-purpose graphics processor (GPGPU) machines…
Q: Find a computer application that you have never used before. Attempt to learn to use it using only…
A:
Q: Investigate new developments in wireless networking and the typical cost of wireless LAN…
A: Given: Trends in wireless networking and installation costsWireless local area network topologies…
Q: What function does a service that enables virtual study groups for students play in the current…
A: The spread of COVID-19 has led to the closure of educational institutions all over the world. This…
Q: When a web client tries to access protected resources on a web server, show how native auth
A: The following are the security methods it employs: Extended-release Security Context now creates…
Q: When someone mentions a 4G or 5G phone network, what does it mean?
A: Answer:
Q: The tiers, cost-benefit analysis, and performance of client/server architecture should be explained
A: Introduction Client/Server Architecture is generally refers to systems that divide processing…
Q: What is the memory hierarchy concept? Why did the writers first choose to turn it into a pyramid?
A: Any digital computer must have a memory unit since it is required for storing programs and data.
Q: What advantages do client-server architectures offer over peer-to-peer systems?
A: This question comes from Networking which is a paper of computer science. Let's discuss it in the…
Q: It is better to have a computer with logical divisions and subsystems than one without.
A: Subsystems and logical divisions combined on one machine
Q: What is Linux used for, and how does it function on mobile devices?
A: Introduction: Android is undeniably one of the most popular Linux-based technologies of all time,…
Q: What are the two strongest arguments in favor of layered protocols?
A: Layered protocols are the network protocols which contains many layers. The examples of layers in…
Q: Instead of letting a server register itself with a daemon as in DCE, we could also choose to always…
A: If the port of the server ever changes then it will be difficult to access the endpoint (port). So…
Q: What function does a service that enables virtual study groups for students play in the current…
A: A service that enables virtual study groups for students can help to keep students on track with…
Q: What would an IoT-based illness mean in terms of the law, society, and ethics?
A: We can also think of the development of IoT illnesses as the development of analog‐like devices that…
Q: An example of an output device would be a dot-matrix printer.
A: Output devices are a piece of computer hardware that takes data from a computer in machine readable…
Q: Describe the programming language used to create software for parallel computing.
A: Please find the detailed answer in the following steps.
Q: Your father made the decision to start a software development company and made a start-up investment…
A: The following are the many kinds of network topology: Topology of StarsTopology of BusesTopology of…
Q: Is it feasible to establish a network of computers? What different parts of the network make up the…
A: A computer network is a setup that joins two or more computers together to share and transport data.…
Q: What is em in HTML and what is em in CSS? Provide examples.
A: <em> is Emphasis element It marks text that has stress emphasis. The <em> element can be…
Q: Examine the following and describe each part in detail along with their effects and functionalities.
A: The answer is as below:
Q: If we use straight RGB value coding with 10 bits per primary color, how many colors are there for…
A: Answer:
Q: Identify and explain the Internet of Things reference model (IoT). Use the four connection levels of…
A: Introduction: The IoT Information Model is meta-model that outlines the organisation of major…
Q: c# write program that Calculate a sum of diagonal numbers in array square matrix
A: // Online C# Editor for free// Write, Edit and Run your C# code using C# Online Compiler using…
Q: What would an IoT-based illness mean in terms of the law, society, and ethics?
A: Dependency Injection: Addresses issues such as how an application or class may be independent of how…
Q: protocol called RTP (Real-time Transport Protocol) enables real-time data transmission and…
A: The Real-time Transport Protocol (RTP) is a network standard for transferring audio or video data…
Q: What are the differences between parallel/distributed databases and centralized databases in terms…
A: Definition: A distributed database is a word used to refer to a collection of data that is kept…
Q: Make a spreadsheet to show how to use the Goal Seek function in Microsoft Excel.
A: Make a spreadsheet to show how to use the Goal Seek function in Microsoft Excel.
Q: Briefly describe the following advanced database systems and applications: object-relational…
A: Your answer is given below. Introduction :- The NoSQL/newSQL databases are the focus of advanced…
Q: Consider a distributed system with two sites, A and B. Can site A distinguish among the following? B…
A:
Q: Print "userNum1 is negative." if userNum1 is less than 0. End with newline. Assign userNum2 with 1…
A: The correct JAVA code is given below with code and output screenshots
Q: Describe why, given a heap data structure, the trickle down algorithm takes more operations than the…
A: A heap is a binary tree with the qualities listed below: It is always exhaustive. This indicates…
Q: The stages of the life cycle of a computer system should be explained and shown with examples.
A: Cycle of a computer machine: The Central Processing Unit performs a simple function known as a…
Q: Writing in Python In this part, you'll write the code that implements the flood fill algorithm,…
A: the answer is:-
Q: Is there a limit on what may be done online? What does the physical boundary of a virtual domain…
A: There are certain limits on online work for example :while doing online shopping, one cannot touch…
Q: Which hardware configurations are necessary to guarantee the effectiveness of virtual memory…
A: Given: What hardware approaches are required to ensure the efficiency of virtual memory systems? Do…
Q: Name the top five essential parts of a computer system.
A: The parts of a computer system are the most important components to understand, as they are the…
Q: Think about the following example: A manager responded to your effort to explain the idea of…
A: WEIGHTED EVALUATION MODEL CONCEPT: While describing the notion of the weighted evaluation model to…
Q: Java Script Create a function that takes an array of integers as an argument and returns the same…
A: Algorithm - Take input from user. Now use the below logic - while(arr.length>0){…
Q: What does it mean for extensions, plug-ins, and add-ons to pose a security risk?
A: Extensions, plug-ins, and add-ons can give attackers a way to execute code on a victim's machine.…
Q: Name and briefly explain four factors that contribute to the rise in computer-related errors.
A: The answer is as below:
Q: When creating a thorough information security plan for your management information system (MIS), how…
A: Explanation (1) Viruses: Let's begin with the kind of security danger that is the most common and…
Q: Your company is getting ready to add VoIP to its network. The business is concerned about how…
A: Quality of service (QoS) is the use of the mechanisms or the technologies which work on the network…
Q: Is batch processing a practical substitute today? If so, why is that or why not?
A: Batch processing is not a practical substitute today because it is not as efficient as real-time…
Step by step
Solved in 4 steps with 1 images

- Please do this in JAVA PROGRAMMING. Given: List L of pairs of charactersString SOutput: TRUE if S is a valid string, FALSE otherwise. A string is considered valid if each character in the string can be paired with another character in the string, where the pair belongs to the input list L. Furthermore, two pairs cannot cross each other. In other words, a pair most completely enclose another, or be completely separate. Design and implement an efficient dynamic programming solution to this problem. Examples: Input L: (a b) (b c) (c d) (a a) Input S: aaba Output: True (pairs shown color-coded: aaba, "aa" fully encloses "ab") Input L: (a b) (b c) (c d) (a a) Input S: abcaad Output: True (pairs shown color-coded: abcaad, "ab" is separate from the other pairs) Input L: (a b) (b c) (c d) (a a) Input S: acbd Output: False (acbd is not valid because the pairs cross each other.) Input L: (a b) (b c) (c d) (a a) Input S: aaac Output: FalsePlease implement in Java implement a keyed bag in which the items to be stored are strings (perhaps people’s names) and the keys are numbers (perhaps Social Security or other identification numbers). So, the in- sertion method has this specification: public void insert(String entry, int key);// Precondition: size( ) < CAPACITY, and the // bag does not yet contain any item// with the given key.// Postcondition: A new copy of entry has// been added to the bag, with the given key. When the programmer wants to remove or retrieve an item from a keyed bag, the key of the item must be specified rather than the item itself. The keyed bag should also have a boolean method that can be used to determine whether the bag has an item with a specified key. In a keyed bag, the pro- grammer using the class specifies a particular key when an item is inserted. Here’s an implementation idea: A keyed bag can have two private arrays, one that holds the string data and one that holds the corresponding…Design a Java class named LinearEquation for a 2-by-2 system of linear equations:ax + by = e x=(ed-bf)/(ad-bc)cx + dy = f y=(af-ec)/(ad-bc) The class contains:• Private double data fields a, b, c, d, e, and f.• A constructor with the arguments for a, b, c, d, e, and f.• Six getter methods for a, b, c, d, e, and f.• Methods getX() and getY() that return the solution for the equation.• A method named isSolvable() that returns true if ad - bc is not 0. The method isSolvable() willbe called in the main, if it returns true display the calculated values for x and y by calling getX()and getY(). If the call to isSolvable() returns false, display a message that “the equation has nosolution”. Write a Java program that prompts the user to enter a, b, c, d, e, and f and displays the result. After the valuesfor a through f are entered, create a LinearEquation object. Check to seeIf ad - bc is 0, report that “The equation has no solution”, otherwise print out the values for x and y.
- Please write Lisp code for the following problem. Consider the list:((name (number1 nation)) (MusicPurchasedNorway) (Pressfreedom Norway) (NobelLiterWinners France)(MovieTixHighPrices Switzerland))write a function to access the MovieTixHighPricesvalue using carand cdr.2 (Your function should work on any property list with this set of properties in this order.)Java Programming: Make sure to have parsing statements for parseFor(), parseWhile(), parseIf(), parseFunctionCalls(), and implements the ranges as well. There must be no error at all & make sure to show the output. Attached is information circled as to what the exact function parser.java must have. Below is parser.java: Parser.java public class Parse { public static StatementNode parseFor() throws Exception { // Implementation of parsing for statements } public static StatementNode parseWhile() throws Exception { // Implementation of parsing while statements } public static StatementNode parseIf() throws Exception { // Implementation of parsing if statements } public static FunctionCallNode parseFunctionCall() throws Exception { // Implementation of parsing function calls } public static VariableNode parseVariable() throws Exception { // Implementation of parsing variable declarations }}In Java, a class can only inherit from one other ------- . A class can, however, extend many ----------.
- ITERATORS IN JAVA Re-write this program using Java Iterators but without changing the meaning and consequently producing the same output. class TwoDArray { public static void main(String args[]) { int i, j, k = 0, twoD[][] = new int[4][5]; for(i = 0; i < 4; i++) for (j = 0; j < 5; j++) twoD[i][j] = k++; for(i = 0; i < 4; i++) { for(j = 0; j < 5; j++) System.out.print(twoD[i][j] + " "); System.out.println(); } } }JAVA A Matryoshka, or Russian nesting doll is either solid or hollow. If it is hollow, it contains another doll (which can also be hollow or solid). Given the supplied Doll class, implement a recursive method named show that returns a String representing the chain for dolls, for example Natasha contains Tanya contains Peter public class Doll{ private String name; private Doll dollInside; /** * Constructs a hollow doll with the doll it contains. */ public Doll(String theName, Doll theDoll) { name = theName; dollInside = theDoll; } /** * Constucts a solid doll. */ public Doll(String theName) { name = theName; dollInside = null; } public boolean isSolid() { return dollInside == null; } public String getName() { return name; } public Doll getDollInside() { return dollInside; }} public class DollViewer{ public static String show(Doll d) { /* code goes here */ } public static void main (String [] args) { Doll dolls1 =…JAVA public interface Interf1 { public void repeat(String s1); } Implement the above interface using lambda to accept hello world and print ten times and implement the above interface using inner class to accept hello world and print ten times
- Java Programming: Below is my parser with the different nodes.java. There are errors in the parser. Please fix those errors and attached is the image of the output the parser must produce. Parser.java import java.util.List; public class Parser { private final List<Token> tokens; private int current = 0; public Parser(List<Token> tokens) { this.tokens = tokens; } private Token matchAndRemove(TokenType type) { if (isAtEnd()) return null; Token token = tokens.get(current); if (token.getType() == type) { current++; return token; } return null; } private void expectEndsOfLine() { while (matchAndRemove(TokenType.END_OF_LINE) != null); if (current >= tokens.size()) { throw new SyntaxErrorException("Unexpected end of input"); } } private Token peek(int n) { if (current + n >= tokens.size()) { return null; } return tokens.get(current + n); }…Create a program in Java that implements Polymorphism and asks the users input to compute the wages of regular and contractual employeesProgram this on C++ Overload the constructor with one string parameter in such a way that the DNAsequence will not be NULL, it will be the sequence passed in the function. The functionwill only create the DNA sequence if it is containing the bases A,T,C,G and gaps ‘-‘.If it is not so, the function will print the error message that due to invalid bases, DNAsequence cannot be created.

