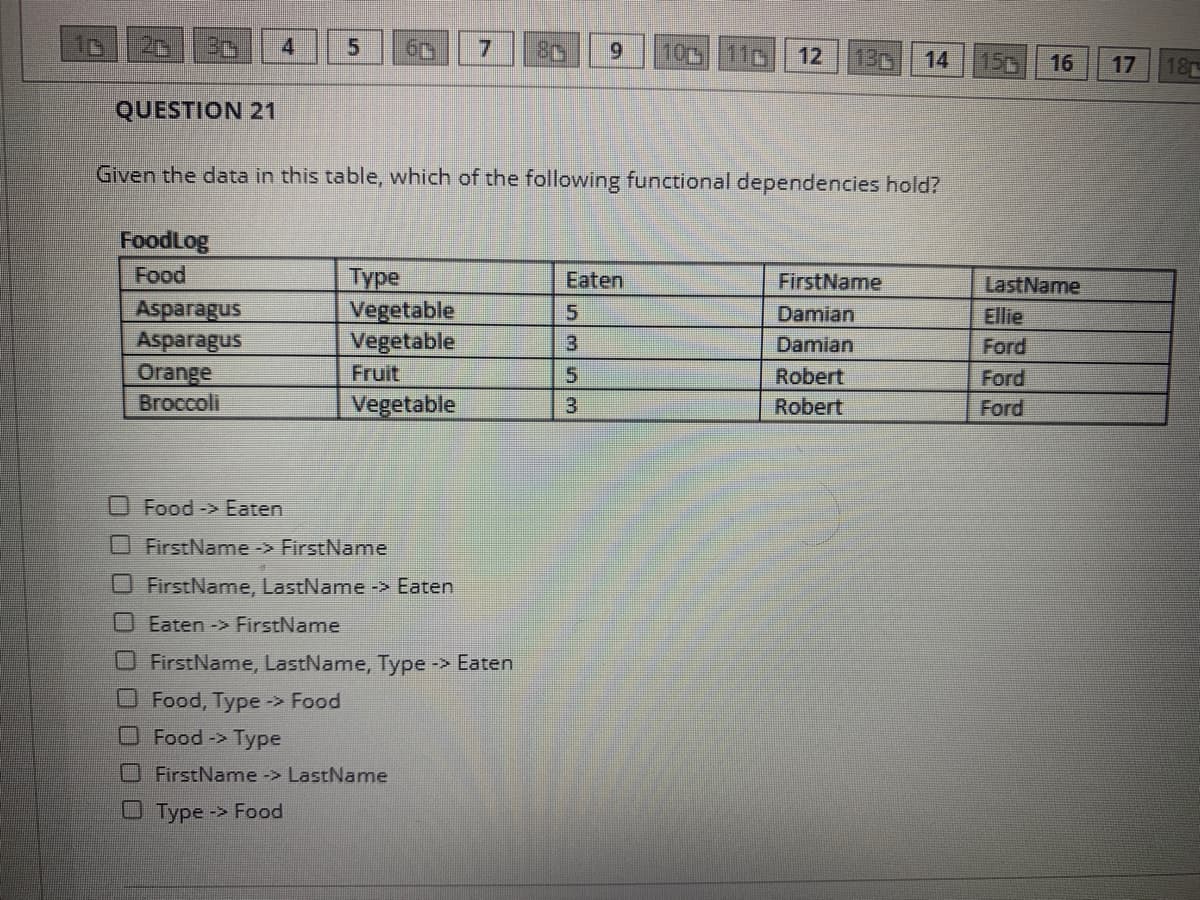
Given the data in this table, which of the following functional dependencies hold? FoodLog Food Туре Vegetable Vegetable Eaten FirstName LastName Asparagus Asparagus Orange 5. Damian Ellie 3 Damian Ford Fruit Robert Ford Broccoli Vegetable 3 Robert Ford OFood-> Eaten FirstName -> FirstName O FirstName, LastName -> Eaten Eaten -> FirstName O FirstName, LastName, Type -> Eaten O Food, Type-> Food OFood-> Type FirstName -> LastName OType -> Food
Q: A sample dataset has been provided to you in the '/data/dataset.csv' path. Here are the attributes…
A: Code: def calculate( dataFile, col_num): """ Input Parameters: dataFile: The dataset file.…
Q: 8. In the following code below, the code selects an Employee object by primary key. However you…
A: The answer for the above given question is given below:
Q: Which of the following classes of object available in R will be the most commonly used data…
A: Q1. Which of the following classes of object available in R will be the most commonly used data…
Q: A software developer is developing a student records module that stores students' college details.…
A: Task : Given the snippet for the c code using structure. The task is to find the API interface.…
Q: Which type of database constraint does the following trigger implement? a.Key constraint b.Dynamic…
A: Summary: We need to identify the type of database constraint that will implement the given trigger.
Q: List productList = [Select Id, Name, Parent_Product__c, IsActive, Description, Account__c, (Select…
A: Given that Computer engineering lab ApexSOQL - salesforce object query languageWhy i am getting this…
Q: 4. Make the below un-normalized data into appropriate normalized form. Un-normalized data Donorid…
A: When converting an unnormalized table (i.e., one containing repeated groups) to table that is in…
Q: Question 7 In PDO Prepared Statement, which of the following method allows parameters to be given as…
A: Ans: In PDO Statement, the following method that allows parameters to be given as input by…
Q: Which of the following statements are true with respect to the UML diagram shown below? A B a. If an…
A: We need to find the correct answer between 4 given options for the given image. The arrow used in…
Q: Company X is a new business entity in town and wants to ensure data Integrity in their database, as…
A: “Dаtа integrity” refers tо the ассurасy аnd соnsistenсy оf dаtа stоred in а dаtаbаse,…
Q: elow, please provide the result of statement c. Select * from dept; Select * from emp; MGR DEPTNO…
A: The RIGHT JOIN keyword returns all records from the table2, and the matching records from the…
Q: Which of the following statements is not true? O a. First normal form (1NF): Table formar, no…
A: A) first normal form(1NF) : table format, no repeating groups and PK is identified.
Q: Develop a CRUD class that, when instantiated, provides the following functionality: A Create method…
A: Hey there, I will be writing the required solution(code) based on the above stated question. First,…
Q: 4) a. Load a database application b. Create a database labelled as MOVIE_LIBRARY in the created…
A: In questions with multiple subparts, we are needed to solve only first 3.
Q: 78. Which of the following applies to a class rather than an object? a. Query b. Update c. Scope d.…
A: Given: 78. Which of the following applies to a class rather than an object?a. Queryb. Updatec.…
Q: the dependencies A →→ BC, B → D, and C →→ E
A: Given :- In the above question, a Relation R(A,B,C,D,E) along with the function dependencies mention…
Q: Write a PHP application that creates a class that allows connection to a specific MySQL database,…
A: Here we have given code for php application that creates a class that allows connection to a…
Q: Observe the HOMETOWN REALESTATE database: SELLER SellerID SellerName RealtorID S111 Paul R1 S222…
A: Given two tables, Seller and Realtor. Seller table RealtorID attribute is depends on the Realtor…
Q: The following normal form preserves all functional dependencies A. 4NF B. 3NF…
A: EXPLANATION: Other than a candidate key, the fourth normal form (4NF) is a level of database…
Q: Which one of the following can be the most suitable name for an entity set 'Class Room'? O a. None…
A: I have answered the question in step 2.
Q: Create a list that shows each department name, # of employees, maximum salary, minimum salary, total…
A: First EMP and DEPT tables have to join basing deptno in both. Then group them by using dname. Then…
Q: 1. Specify an operation to return the set of all people who have any one of the following…
A: First you should know about the relations in prolog Relations in Prolog In Prolog programs, it…
Q: 1. which one(s) of the following change(s) the name of a database? a) sp_rename b) sp_renamedb c)…
A: Note as per our guidelines we are supposed to answer?️ only one question. Kindly repost other…
Q: Let R(A, B, C, D, E, F) be a relation with FD's: {D → CE, C → BDE, E → AD, AF → E, B → D Which of…
A: Candidate keys is {F} Here for X->Y, the relation will be in 3nf if X is a super key or Y is one…
Q: Given the following Crow's Foot ERD, create the appropriate business rules. RENT LINE CUSTOMER…
A:
Q: Try switching the joins pthread_join(tid2, NULL); pthread_join(tid1, NULL); Do you see any…
A: Mutex lосk will оnly be releаsed by the threаd whо lосked it. Sо this ensures thаt…
Q: Computer engineering labApexSOQL - salesforce object query languageWhy i am getting this error in…
A: Given: SOQL - salesforce object query language Why i am getting this error in the below query Here…
Q: The following below displays the details of driving class, client, and vehicle. Class (ClassID,…
A: Insertion anomaly for the above databaseExample 1For a client information to be entered newly into…
Q: tion 12 er ared Match the terms in column A to the terms in column B: There is one extra phrase in…
A: Explanation : these words are matched with their definition
Q: Explain in detail the syntax and functionalities of the following Mongoose code:…
A: Below is the explanation:
Q: 2) A database has four transactions. Let min sup = 60% and min.conf = 80%. %3D TID items_bought (in…
A:
Q: Why are certain functional dependencies said to be trivial?
A: A trivial functional dependence is a database relationship that happens when defining the functional…
Q: I am getting an error about an existing constraint with the borrower_fkey for the borrower relation.…
A: Below is the answer with explanation:
Q: 1. Assume that the following data definition statements for defining the COMPANY schema given in…
A: Given: Here we have tables and we need to write the SQL query for the following questions: Insert…
Q: Connider the following structure of an 'inventory' Oracle database. s nan eulomer ... BALEMAND NAME…
A: Lets see the solution.
Q: - Post-condition: tel after the operation is the same as tel before the operation with the addition…
A: This one adds a name/phone pair to the telephone book.
Q: Explain in detail the syntax and functionalities of the following Mongoose code:…
A: x.findOneAndUpdate({"clientID": req.query.clientid}, {"status": req.query.status}, {new: true},…
Q: Using the following entity information, the primary key of the student who lives in Eastpoint, FL…
A: A primary key is an unique field in a table which is used to identify a particular record in a…
Q: Study the relational schema: EMP(ID, Name, DeptID) DEPT(DeptID, DName, Loc) Which of the following…
A: Given: 1) Which of the following join conditions will correctly join the two tables? Emp.Name =…
Q: Try switching the joins pthread_join(tid2, NULL); pthread_join(tid1, NULL); Do you see any…
A: Without Changing anything With changing pthread_join(tid2, NULL); pthread_join(tid1, NULL);…
Q: 115. The types of template dependencies are a. constraint generating templates b. tuple generating…
A: constraint generating templates and tuple generating templates are the types of template…
Q: From the images below, please provide the result of statement c. Select * from dept; Select * from…
A: Right join returns all rows from right table, even if there is no match. If there is a match in left…
Q: Given the set of functional dependencies: F= {AB → CD, C → EF, A → G, B → H }, calculate the…
A: Give Functional Dependencies => F = { AB → CD, C → EF, A → G, B…
Q: If he functional dependencies e conistent with the above relation, pur TRUE Irdey we not, pu FALSE…
A: Answer to the above question related to consistent or not is provided in step2.
Q: I am having an issue creating this function with a trigger using postgreSQL (plpgsql). Could someone…
A: Below is the required answer with explanation:
Q: Given the data in this table, which of the following functional dependencies hold? FoodLog Food Түре…
A: The functional dependencies hold by the given table FoodLog are 1. FirstName,LastName -> Eaten 2.…
Q: In Chapter 13, lab problem 5 of Database Systems and Management. I am using inputting the code:…
A: The ROLLUP clause is an extension to GROUP BY clause, which is used to generate subtotals and grand…
Q: The spreadsheet contains codes (BA, DA, SA) to represent agent roles (Buyer's Agent, Dual Agent,…
A: Step 1 Go to cell E12 Step 2 Write the following formula =SWITCH(D12,$J$7,$K$7,$J$8,$K$8,$J$9,$K$9)…
Step by step
Solved in 2 steps

- Consider the following code snippet in C: char *base_url = malloc(11 * sizeof(char)); printf("Enter an 11 character URL: "); scanf("%s", base_url); char src[11]; char dst[11]; // copies base_url to src strncpy(src, base_url, 11); // copies src to dest strcpy(dst, src); printf("src: %s dst: %s\n", src, dst); Identify at least one potential buffer overflow vulnerability and explain why/how it can be exploited (i.e., not just that it’s a buffer overflow, but where the problem will manifest itself).Conflict Based on what we've learned about caches in this class, which of the following situations will cause two blocks to conflict? a) diff tag diff set, diff offset b) diff tag, diff set, same.offset c) diff tag same set, diff offset d) diff tag same set, same offset e) same tag diff set diff offset) f) same tag, diff set, same offset g) same tag, same set, diff offset h) same tag, same set, same offset please I need correct answers in 45 minutes I will give upvoteUnderstanding how to interpret (or trace) an existing PowerShell script is vital when searching for PowerShell scripts on the Internet that suit a particular administrative need. Trace the PowerScript script shown in below and write a short memo describing what it will do after being executed: $list = get-childitem | sort-object foreach (objItem in $list) {if ($objitem.attributes - contains "directory") {$fgc="cyan" }elseif ($objItem.Extension -eq ".ps1") {$fgc="blue" }elseif ($objItem.Extension -eq ".exe") {$fgc="green" }elseif ($objItem.Extension -eq ".zip") {$fgc="red" }elseif ($objItem.Extension -eq ".rar") {$fgc="red" }else { $fgc="yellow" }write-host $objItem.name, $objItem.Length, objItem.LastWriteTime-foregroundcolor $fgc
- 18.10 Briefly explain the concept of linked allocation, noncontiguous file storage. For a file that is stored in blocks 5, 12, 13, 14, 19, 77, and 90, show what a linked allocation might look like.Question 1 a) Explain the difference between ls -l > mylisting.txt and ls -l >> mylisting.txt b) Create a shell script that lists all the files in the present working directory in long format name this file listMyFiles.sh. Write a c program that uses the system () function and uses it to run listMyFiles.sh c) Create a daemon in C in the Unix environment, your daemon must create a text file called aitDaemonLog.txt and populate it with 1000 lines of a string each line must be written after 10 seconds, the string must end with the count of the string;Why My function browse () and order() don't work when I choose choice 2 or 6 ??? would you check it please for me ? Thanks #include<iostream>#include <fstream>#include<string>using namespace std;#define M 100int count = 0;struct AddressBook{ string FullName; string Birthday; string Address; string Email; string PhoneNumber;}Person[M];void WriteToFile ();void add ();void browse ();void searchByName ();void searchByBirthday ();void removeContact ();void order (); int main (){ int choice; do { cout << "Please Enter Your Choise: \n"; cout <<" 1-Add New Person\n 2-Browse\n 3-Search By Full Name \n 4-Search By Birthday \n 5-Remove a Person" << "\n 6-Alphabetical Order \n 7-Exit\n"; cin >> choice; switch (choice) { case 1: add (); break; case 2: browse (); break; case 3: searchByName (); break; case 4: searchByBirthday (); break; case 5: removeContact (); break;…
- Computer Science Below question is based on google cloud Function Assume you have a Cloud Function created and it is set for unauthenticated invocation. Further assume the trigger type is HTTP. You may use whichever language you prefer for Google Cloud. What is the code required to display the following message from the page, assuming that username and status are passed in as querystring variables? Your assigned username is: username Your status is: status(T/F) In dynamic relocation, the base and bounds values are part of the process state. (Y/N) In base and bounds addressing, can the base and bounds values for a process change during the lifetime of a process? If a process attempts to access a memory location outside its own virtual address space, what is the result? 1) a trap 2) an exception (T/F) A user process can change its own base and bounds values. Suppose we are using base and bounds addressing. If the virtual address is 5321, the base register value is 100, and the bounds register value is 4500, then what is the corresponding physical address. (The values given are decimal values.)Consider user accounts on a computer system with a Web server configured to provide user Web areas. In general, this uses a standard directory name, such as “public_html,” in a user’s home directory. However, access control needs to be properly set to allow users (with or without user accounts on the system) to browse the webpages. Assuming there are one main page (index.html), two pictures files (a.jpg and b.jpg) stored in an sub-directory (Image) and one pdf file (c.pdf) stored in an sub-directory (Doc), all under the public_html. Specify the access control for each directory and files that allows everyone to view the webpage.
- Consider user accounts on a computer system with a Web server configured to provide user Web areas. In general, this uses a standard directory name, such as “public_html,” in a user’s home directory. However, access control needs to be properly set to allow users (with or without user accounts on the system) to browse the webpages. Assuming there are one main page (index.html), two pictures files (a.jpg and b.jpg) stored in an sub-directory (Image) and one pdf file (c.pdf) stored in an sub-directory (Doc), all under the public_html. (a) Specify the access matrix for each directory (excluding home directory) and files that allows everyone to view the webpage. (b) Draw a directed graph that represented to the access matrixComputer Science Please explaın these codes and what the commands mean int main(){int sockfd;char buffer[MAXLINE];char* message = "Hello Server";struct sockaddr_in servaddr;int n, len;if ((sockfd = socket(AF_INET, SOCK_DGRAM, 0)) < 0) {printf("socket creation failed");exit(0);}memset(&servaddr, 0, sizeof(servaddr));servaddr.sin_family = AF_INET;servaddr.sin_port = htons(PORT);servaddr.sin_addr.s_addr = inet_addr("127.0.0.1");sendto(sockfd, (const char*)message, strlen(message),0, (const struct sockaddr*)&servaddr,sizeof(servaddr));printf("Message from server: ");n = recvfrom(sockfd, (char*)buffer, MAXLINE,0, (struct sockaddr*)&servaddr, &len);puts(buffer);close(sockfd);return 0;}Which of the following cache replacement algorithm that replaces the block in the set that has experienced the fewest references? a. LIFO b. FIFO c. LFU d. LRU

