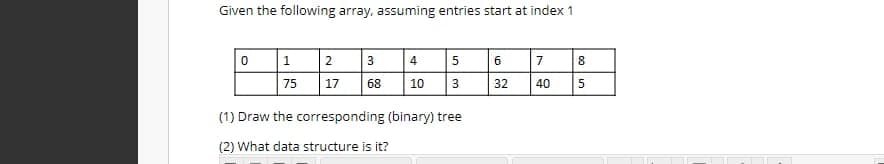
Given the following array, assuming entries start at index 1 0 1 75 2 17 3 68 4 10 5 3 (1) Draw the corresponding (binary) tree (2) What data structure is it? 6 32 7 40 8 5 00
Q: What impact has the internet had on the development of different kinds of systems?
A: Corporate businesses, industries, and organisations have all been significantly altered by the…
Q: b. Start with the seed xo = 67, and generate 5 pseudo-random numbers using the formula Xn 17 Xn-1…
A:
Q: IN JS PROGRAMMING T Given a word, create an object that stores the indexes of each letter in an…
A: Input - String Output - Map of laters with position In this problem, we need to design the code…
Q: Calculate the total time required to transfer a 1.5-MB file in the following cases, assuming an RTT…
A:
Q: Specify how the CSMA/CD protocol works in detail.
A: Carrier-sense multiple access with collision detection, or CSMA/CD, is the term used to explain how…
Q: Files and folders on a computer's hard drive may be created, viewed, and managed with the help of…
A: The part of the operating system that controls files and directories is called the file system. our…
Q: When designing a compiler, what factors should be prioritized to provide a high-quality, reliable…
A: Optimizing compilers are pieces of computer software that seek to eliminate or enhance certain…
Q: I was wondering if you could elaborate on the Class C IP address
A: The correct answer for the above question is given in the following steps.
Q: In what sense is a computer "programmed?" Which criteria are most important when deciding on a…
A: A computer program consists of code that is executed on a computer to perform particular tasks. This…
Q: Is it conceivable for the data breach to have a major impact on cloud security? Why should I be…
A: It certainly has an effect.Due to a data leak, an unauthorised individual has access to sensitive,…
Q: What must be done for the computer to check the CD-ROM for the boot files necessary to start up the…
A: Booting is the process in which a computer's hardware checks to see whether all of its features are…
Q: Do Windows machines have any potential entry points for investigators?
A: Laptop forensics gathers volatile and nonvolatile data.Permanent dataRAM-stored dataContrary to…
Q: What exactly are cloud-based data storage and backup services? Is there a place online where I can…
A: A cloud computing provider who manages and runs data storage as a service provides cloud storage,…
Q: Question 10 Given a list containing 32 elements, indicate whether a linear or a binary search would…
A:
Q: Consider an environment in which there is a one-to-one mapping between user-level threads and…
A:
Q: Specifically, how does the LDAP protocol function inside a PKI, and what is LDAP?
A: Lightweight Directory Access Protocol (LDAP) is an abbreviation for Lightweight Directory Access…
Q: When it comes to storing data, what are the main pros and cons of using the cloud?
A: INTRODUCTION: The key benefits and drawbacks of cloud-based data storage are highlighted in this…
Q: In this challenge you should repeat a specific given char x times. Create a function that takes a…
A: I give the code in Javascript along with output and code screenshot
Q: How do the most vital parts of Phases of Compiler operate, and what are they? Each step of this…
A: Fig - Phase of Compilers Phases of compiler are:- Lexical Analyzer Syntax Analyzer Semantic…
Q: Describe what will happen for the following scenario when Wait/Die is adopted. What will happen when…
A:
Q: 1. Find Fourier series Coefficients for x(t) = cos(2t + 7) 2. Find Fourier series complex…
A:
Q: What impact has the internet had on the development of different kinds of systems?
A: The Internet is a huge organization that interfaces PCs everywhere. Through the Internet,…
Q: code in C
A: Introduction C programming language is a type of language that is basically to learn as a simple…
Q: What are the most challenging challenges to handle in light of this massive data expansion?
A: Data expansion is basically the technique of duplicating every perception in the information by an…
Q: please code in python the question is in the image
A: Coded using Python 3.
Q: Write and verify an HDL behavioral model of a D flip-flop having asynchronous reset.
A: Introduction to Verilog Verilog is a HARDWARE DESCRIPTION LANGUAGE (HDL) that is used to describe a…
Q: What are the many different factors that must be considered while building a compiler that can…
A: Steps to find the answer:Guidelines collectionCompiler developers get instruction set ideas. Authors…
Q: When I asked the last question on Bruce wayne problem, the answer seems too few subnets needed for…
A: Bruce wayne problem : A subnet, or subnetwork, is a segmented piece of a larger network. More…
Q: Define the Line Matching and Word Selection in SetAssociative Caches ?
A: Lets see the solution.
Q: If you could define MFA and describe how it operates, that would be great. Just how safe are your…
A: Introduction: Describe the multifactor authentication technique and the phrase's meaning. What…
Q: It is unclear how quantum computing will affect code.
A: Introduction: Quantum computing looks to open up new avenues for dealing with very complex…
Q: Which steps in developing most heavily to guarantee Explain. a compiler must be prioritized a…
A: Compiler optimization: An optimizing compiler is a piece of computer software that attempts to…
Q: Specifically, what are some best practices for managing firewalls? Explain.
A: Firewall: We can describe firewall as a system which is designed to prevent unwanted users to access…
Q: wing tables support the database of a shopping store. The schema contains four tables i.e. Customer,…
A: let us see the answer Since you have asked multiple questions we will answer 2 of them if you want…
Q: A certain CS professor gives 5-point quizzes that are graded on the scale5-A, 4-B, 3-C, 2-D, 1-F,…
A: Lets see the solution.
Q: What exactly are cloud-based data storage and backup services? Is there a place online where I can…
A: Cloud-based data storage: A cloud computing provider who manages and runs data storage as a service…
Q: One possible form of network infiltration is for malicious traffic to be redirected from one VLAN to…
A: statement: The connection is unavailable because the desktop is unable to find the server's hardware…
Q: The prevalence of cybercrimes is increasing globally. Identify and explain five techniques which…
A: Secure your hardwareWith so much attention given to acquiring the newest and most sophisticated…
Q: Why should one use Java's Collection Framework, and what benefits does it provide?
A: Framework for collecting data: The implementation of generally reusable collection data structures…
Q: governance, along with the Make a list of the top five areas or fields of internet internet-related…
A: The solution for the above given question is given below:
Q: Tell me about an online authentication attack that makes use of cookies.
A: What Are Cookies? Cookies are text files that include small pieces of data such as a login and…
Q: A successor to ASCII that includes characters from (nearly) all writtenlanguages isa) TELLI b)…
A: ASCII stands for American Standard Code for Information Interchange, it is a character encoding…
Q: How do you get the computer to look in the CD-ROM drive for the operating system files first?
A: Introduction When a computer is turned on, the operating system is launched during the booting…
Q: A multiprocessor with eight processors has 20 attached tape drives. There is a large number of jobs…
A:
Q: how to take use of cloud computing's benefits
A: The benefits of cloud computing can be used in the following ways given in the below step:
Q: Explain Full form of SATA hard disk?
A:
Q: Does it make sense to restrict the lifetime of a session key? If so, give an example how that could…
A: In order to guarantee the security of a communications session between a user and another computer…
Q: C has a construction called a union, in which a field of a record (called a struct in C) can hold…
A:
Q: 7. A multiple-choice test contains 10 questions. There are four possible answers for each question.…
A:
Q: Detail the primary Java interfaces used by the collections framework.
A: Collections in Java are frameworks that provide an architecture for storing and manipulating sets of…
Step by step
Solved in 2 steps with 2 images

- Given the following text file (tree.txt), load the data into a binary search tree representation in Python Implement a method to calculate the height of the tree from the root (iterative or recursive) The image attached to this question should be rendered as the file "tree.txt"Consider the following array representation of a complete binary tree in python. A B C D E F G H I J K L M N O Perform following operations on the tree. Find left child and right child of each parent in the tree Find sibling of each node in the tree Find parent of each node in the treeDraw a binary search tree for the following data elements: 13, 15, 59, 9, 42, 44, 100, 10, 5.
- 24( If the binary tree is represented by the array as below, then find the parent of node 46. a. 26 b. 96 c. 45 d. 21(a) Create and draw a binary search tree using the following data entered as a sequence set: 80 70 -4 99 34 50 -9 13 69 3. (b) Insert 21 into the tree created in step (a). Draw the updated tree.Please answer the following, #5. Write clearly please. Create a height-balanced binary search tree from the following sorted array. 1 5 9 11 12 13 15 18 19
- Develop a pseudo-code algorithm for a level-order traversal of a binary tree. Create an array-based implementation (write a program) of a binary tree using the computational strategy. Include the following methods: a. Remove a node from the binary tree. b. Insert a node into the binary tree. c. Remove the minimum (smallest) element from the treeDraw a binary search tree (BST) whose elements are inserted in the following order: 50 72 96 94 102 26 12 11 9 2 10Create a Binary Search Tree Class with the following four Operations using a single C++ program: Operations: 1. Insert(int n) : Add a node the tree with value n. Its O(lgn) 2. Find(int n) : Find a node the tree with value n. Its O(lgn) 3. Delete (int n) : Delete a node the tree with value n. Its O(lgn) 4. Display(): Prints the entire tree in increasing order. O(n).
- 1. Construct a binary tree for the numbers 3,4,5,6,7,8,9. Then for each number input taken at runtime, show the number of iterations required to reach that node from root node containing the target number. (10) 2. Construct a binary tree with the following keys as strings a. Desktop, CSU, Spring2022, CIS260, CIS 265, Vacation, Hackathon Your first task is to put this data in an array of string and search for a folder name. Let us say that the folder name is “Hackathon”. Using the array subscript, how many iterations does it take to find the folder? (10) Next, convert this array into a Binary tree and arrange in alphabetical order, and try to find the same folder. List the number of Iterations.(10) Bonus: Now replace the folder names with file contents. So you need a File class where there is a filename variable and file content variable, both should be strings. So the node would have file object instead of just names. So you have an array of File class objects, so the binary tree will…Create an array version of a binary search tree based on an array implementation of a binary tree using the simulated link approach. Each array element must maintain a reference to the data element that was placed there, as well as the array positions of the left and right children. You must also preserve a record of accessible array places where items have been erased so that those slots may be reused.Input.txt contains 1 2 3 5 8 13 21 34 55 89 Binary node.java contains import test.BinaryNode; // BinaryNode class; stores a node in a tree. // // CONSTRUCTION: with (a) no parameters, or (b) an Object, // or (c) an Object, left child, and right child. // // *******************PUBLIC OPERATIONS********************** // int size( ) --> Return size of subtree at node // int height( ) --> Return height of subtree at node // void printPostOrder( ) --> Print a postorder tree traversal // void printInOrder( ) --> Print an inorder tree traversal // void printPreOrder( ) --> Print a preorder tree traversal // BinaryNode duplicate( )--> Return a duplicate tree /** * Binary node class with recursive routines to * compute size and height. */ class BinaryNode { public BinaryNode( ) { this( 0, null, null ); } public BinaryNode( int theElement, BinaryNode lt, BinaryNode rt ) { element = theElement; left = lt; right = rt; } /** * Return the size of the binary tree rooted at t. */…

