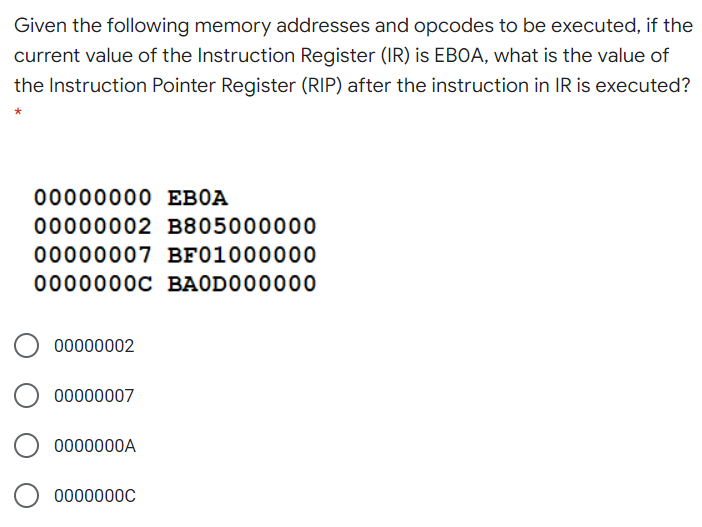
Given the following memory addresses and opcodes to be executed, if the current value of the Instruction Register (IR) is EBOA, what is the value of the Instruction Pointer Register (RIP) after the instruction in IR is executed? 00000000 EBOA 00000002 B805000000 00000007 BF01000000 0000000C BAODO00000
Q: Assume you receive an alert from your company's mail server notifying you that the password for your…
A: Introduction: Phishing is a type of malware that involves the theft of credentials.
Q: Why is it critical for a programme to terminate an open file once it has finished utilising it? Give…
A: Introduction: To close an open file, follow these steps:
Q: Choose your own example of an organization that relies on information technology, and then argue…
A: The most prominent enterprise security issue an organization that relies on information technology…
Q: Enter file name **purchasesl.csv +-- --- ------+ | Customer ID | Product Name | Price | Quantity |…
A: Here is the code according to the question requested.
Q: What distinguishes software engineering from other engineering disciplines and what makes it an…
A: Introduction: Software engineering, like software architecture, is a metaphor for the real thing.…
Q: Describe dynamic testing.
A: Explanation Mostly the dynamic testing is accomplished by those who know the codes and development…
Q: Convert the following code into assembly language program. if ((x x)) { AX = AX + BX; AX=AX 1;
A: To convert the given C code to assembly language, we use the g++ compiler. We can use the "-S"…
Q: What do you consider to be the most pressing issue in software engineering?
A: Introduction: In a standard software development project, interpersonal conflicts between the…
Q: What precisely is an Interrupt? Explain why no hardware disruptions are expected by discussing the…
A: Hardware failures are predicted by describing the many forms of hardware failures: An external…
Q: Q4.Draw the dependency diagram for the DESPATCH_LIST table above. Identify all dependencies…
A: I have provided the dependency diagram for the DESTPATCH_LIST of the given table.
Q: Which one statement out of following four statements about Merge sort and Quick sort is tr Both…
A: Sorry for that as the bartleby guidelines we can solve only one question for you if you want to…
Q: In which of the following machine learning algorithm, the desired output consists of one or more…
A: Answer: Unsupervised learning is the training of a machine utilizing information that is neither…
Q: Consider the set S of all binary strings of length 8. S = {(x1,..., xs) : a; E {0, 1}}
A: Solution:- Total binary strings of length 8 = 28 = 256 Number of 8-bit strings have exactly one zero…
Q: For each of the algorithms below, draw the spanning tree and find the sequence of visited nodes…
A: Handwritten solution of the given question is:
Q: For the SSH protocol, Client generates a random session key which is encrypted and sent to server.…
A: Given statement is False because •The client and server both contribute toward establishing thier…
Q: Ve feel like small digits are often under-appreciated, nost especially those of a 3-digit integer.…
A: let us see the code:- Hope this will help you
Q: Example 2: Using shift and arithmetic instructions, write the MIPS instructions to multiply $10 by…
A: Below is the answer to above query. I hoe this will be helpful for you..
Q: What role does Microsoft Excel play in data management in small businesses? Make use of examples to…
A: institution: Data management entails obtaining, confirming, securing, and storing data so that it…
Q: What are your thoughts on data hiding, encapsulation, and binding? Elaborate.
A: Introduction: The concepts of data hiding and encapsulation are both significant in object-oriented…
Q: POP3 allows users to retrieve email from a remote server. Does this mean that any POP3 client…
A: POP3 stands for Post Office Protocol (Post Office Protocol) POP3 is an outdated protocol that was…
Q: For the following sequence in the order shown, build an AVL tree: 1, 9, 2, 8, 3, 7, 4, 5, 6. Show…
A: Introduction: Here we are required to build an AVL tree for values 1,9,2,8,3,7,4,5,6, also we are…
Q: which operators would make the following statement FALSE? 11 2 Matlab
A: Solution:- FOLLOWING Operators would make the following Matlab statement FALSE:- < , <= , ==…
Q: Write a comparison of CPU Scheduling Algorithms?
A: Scheduling techniques for CPUs Because of the requirement to alter and test operating system kernel…
Q: Idicatng II Chey ng as waIks, tranS and palns, Che grapII below, Classily eaci UI tne b. v2V3 V4V5…
A: In Walk, Vertices or Edges both can repeat. In Trail Vertex can Repeat, But NOT the edges. In…
Q: What is cryptographic hash function?
A: Establishment: Hash Function for Cryptography (CFH)CFH is a hashing method used in contemporary…
Q: With examples, explain the distinctions between is-a relationship and has-a relationship.
A: There are two ways to reuse codes in object-oriented programming either by the implementation of an…
Q: Please complete both question. Thank yo in advance! Q2. What is the main role of the client stub…
A: INTRODUCTION: Here we need to tell the role of the client stub and server in stub in RPCs and…
Q: What kind of programming constraints would we face if we didn't have control structures in place?
A: Introduction: A programming language's key decision-making feature is control structures; without…
Q: Computer science Linux Which system file contains the list of user accounts?
A: Introduction: LINUX is a kernel or working framework that is distributed under an open-source…
Q: Wireless networks encounter a variety of challenges as a consequence of their inherent…
A: The answer is
Q: What are the two main traits that distinguish proxy servers from NAT?
A: Proxy server: It is a server which acting as an intermediary between internal and external…
Q: How will customers enter and exit a web-based retail business designed by you?
A: Given: We've attached an example of a class diagram depicting an online shopping domain model. The…
Q: Distinguish between disaster recovery and business continuity planning.
A: Introduction: Business Continuity and Disaster Recovery are Important.Business continuity describes…
Q: address=(port, host) is the tuple format needed for the address. Question 4 options: True…
A: The problem is based on the basics of socket programming in networking.
Q: ecovery process
A: Disaster recovery: The disasters, for example, fire, floor, psychological oppressor assault, and…
Q: 7. Answer the following: • What subnet is 192.168.111.129 on? A junior network administrator is…
A: The Answer is
Q: Evaluate: 20 %3 6.666 What will/be displayed/ by the following code? x457t4 y+2 coutee *wend None of…
A: Explanation: Here %(modulo operator) gives the result of a remainder when we perform division of two…
Q: What exactly is a Java Virtual Machine?
A: Java: It is an object-oriented programming language with a high level of abstraction and as few…
Q: h 8 as the value of the Codebit. How will
A: A host generates a TCP segment with 8 as the value of the Codebit Below the TCP software in this…
Q: 2. Prove that if x and y are real numbers, then max(x, y) + min(x, y) = x + y. [Hint: Use a proof by…
A: Given x and y are real numbers. To Prove : max(x, y) + min(x, y) = x + y
Q: Is Open Source Software a Good Option?
A: Introduction: When open-source software is properly evaluated, implemented, and maintained, it can…
Q: Computer science Why is automation necessary for contemporary societies
A: Introduction: Increased automation can assist handle issues including wage growth, ageing…
Q: Subtract the given number system. Show your complete and detailed solution. 4. 11111002 – 11112 5.…
A: In Step 2, I have provided detailed solution---------------
Q: (n+ 3)! Write down the first five terms of the sequence an 2n2 + 5n + 8 a1 = a2 = a3 : %3D a4 = %3D…
A:
Q: A multilayer neural network uses gradient descent to search for a global minimum in the loss space.…
A: Answer - A multilayer neural network uses gradient descent to search for a global minimum in the…
Q: Discuss the role of multimedia and virtual reality in teaching computer science
A: Introduction: Multimedia includes everything we see and hear in the form of text, photographs,…
Q: Describe how software quality is seen by various software researchers. How would you describe the…
A: Software engineering is a massive subject of study. The prior art of research is how researchers…
Q: Write a C++ program that reads a maximum of 100 integers from the keyboard,stores them in a long…
A: program: #include <bits/stdc++.h> using namespace std; // Driver codeint main(){ int…
Q: explain switching, routers, hubs, and access points
A: Introduction: SWITCHES: Switches are the devices in computer networks that connect several types of…
Q: Suppose that we have t = 5 treatments and we can only have blocks of size three. .(a) Find the…
A: Number of treatments = 5 Number of blocks = 3
Step by step
Solved in 2 steps

- Compute the physical address for the specified operand in each of the following instructions from previousproblem. The register contents and variables are as follows : (CS) = 0A0016, (DS) = 0B0016, (SI) =010016, (DI) = 020016 and (BX) = 030016.a) Destination operand of the instruction in (c)b) Source operand of the instruction in (d)c) Destination operand of the instruction in (e)d) Destination operand of the instruction in (f)e) Destination operand of the instruction in (g)In a computer instruction format, the instruction length is 16 bits, and the size of an address field is 4 Is it possible to have: 15 instructions with 3 addresses, 14 instructions with 2 addresses, 31 instructions with one address, and 16 instructions with zero addresses, using this format? Justify your answer.1. T/F - if (B)=006000 (PC)=003600 (X)=000090, for the machine instruction 0x032026, the target address is 003000.2. T/F – PC register stores the return address for subroutine jump.3. T/F – S register contains a variety of information such as condition code.4. T/F – INPUT WORD 1034 – This means Operating system should reserve 1034 bytes in memory5. T/F - In a two pass assembler, adding literals to literal table and address resolution of local symbol are done using first pass and second pass respectively.
- Given following code: 00 9000 01 1150 02 1251 03 5300 04 6420 05 7541 06 8414 07 D20A 08 2523 09 0000 0A 3331 0B B200 0C D20A 0D 2523 0E 0000 50 000A 51 0005 52 0000 Explain what each instruction does in the program, stored in the memory locatons 00 through 0E. When the program stops, what are values in registers R0, R1, R2, R3, R4, R5, and in memory location 52? What does the program do?Assume that the state of the 8088’s registers and memory just prior to the executionof each instruction in problem 15 is as follows: * in photos*What result is produced in the destination operand by executing instructions (a)through (k)? *only h through k* (h) MUL DX(i) IMUL BYTE PTR [BX+SI](j) DIV BYTE PTR [SI]+0030H(k) IDIV BYTE PTR [BX][SI]+0030HWhat are the values of ECX, EBP, and ESP registers after executing the following instruction? push ECX Before ECX: 0xBABE EBP: 0x0012FF24 ESP: 0x0012FF24 After ECX: EBP: ESP:
- Assume that the state of the 8088’s registers and memory just prior to the executionof each instruction in problem 15 is as follows: * in photos*What result is produced in the destination operand by executing instructions (a)through (k)? *only b,c,e,g* b) ADC SI, AX(c) INC BYTE PTR [0100H] (e) SBB DL, [0200H] (g) NEG BYTE PTR [DI]+0010HIf R0 = 0x20008000, after STMDA r0!, {r3, r9, r7, r1, r2} instruction is executed, register r7 will be stored in memory starting from which memory base address. A. R0 = 0x20007ff0 B. R0=0x20007fec C. R0 = 0x20007fff D. R0= 0x20007ff4 E. R0 = 0x20007ffefWill upvote! Find the memory address of the next instruction executed by the microprocessor, when operated in the real mode, for the following CS:IP and 80286 register combinations: a. DS=2F2E & DX=9D64 b. CS=9F7A & IP=AB27 c. ES=DE21 & DI=D75F d. SS=FF5C & BP=92B8 e. DS=DC67 & CX=2FE8
- 333: E8B3 8B3: 0A12 A12: 2153 Since the contents of the relevant addresses are 333 in the basic computer given above, the initial value of the PC is 333; When fetching and executing an indirectly addressing ISZ instruction, write the contents of the following registers in hexadecimal (hex) format for the T5 time. AR ........... DR......... IR ........... PC ........... SC ...........Question 30 Assume that EBX and ECX have the following values EBX: FF FF FF 75 ECX: 00 00 01 A2 After the execution of the instruction INC EBX, ECX The Value in EBX is _________ Group of answer choices FFFFFF76 FFFFFF75 000001A2 none of them Question 31 The Hexadecimal Representation for each of the following Binary number 11101111 Group of answer choices 239 EF FE none of them Question 32 Assume that EBX and ECX have the following values EBX: FF FF FF 75 ECX: 00 00 01 A2 After the execution of the instruction MOV EBX, ECX The Value in EBX is _________ Group of answer choices 00000117 FFFFFF75 000001A2 none of themQuestion 13 Assume that EBX and ECX have the following values EBX: FF FF FF 75 ECX: 00 00 01 A2 After the execution of the instruction ADD EBX, ECX The Value in EBX is _________ Group of answer choices 000001A2 00000117 00000117 none of them Question 14 The MOV instruction changes the flags Group of answer choices True False Question 15 The Binary Representation for each of the following Hexadecimal number 7C Group of answer choices 1111000 11110100 1111100 none of them

