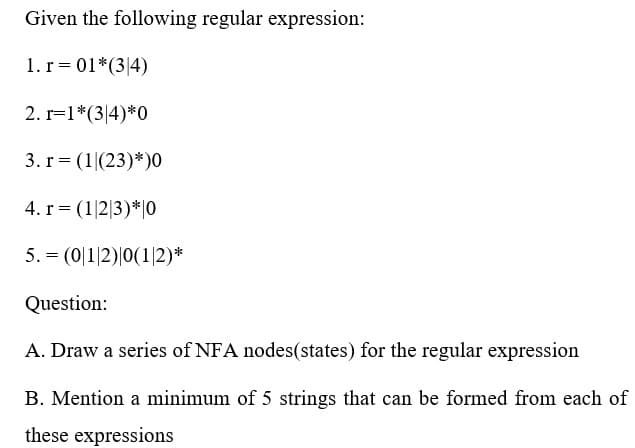
Given the following regular expression: 1. r = 01*(34) 2. r=1*(34)*0 3. r= (1|(23)* )0 4. r = (1|2|3) * 0 5. = (0|1|2)|0(1/2)* Question: A. Draw a series of NFA nodes(states) for the regular expression B. Mention a minimum of 5 strings that can be formed from each of these expressions
Q: Give two instances of the issue between readers and authors. Please provide a response to the…
A: Reading and writing problems encountered by real people.
Q: How would you design a stack which, in addition to push and pop, also has a function min which…
A: As the programming language is not mentioned here, we are using JAVA The JAVA code is given below…
Q: o if your computer doesn't recognise your fingerprint and hence access is
A: How can you fix Windows fingerprints not working?Whatever the cause of your fingerprint reader /…
Q: There are several issues that arise from wireless networks because of their intrinsic…
A: Among the concerns of wireless network users are: network connection issuesBecause of technological…
Q: Please provide an example and a definition of the operating environment.
A: Operating Environment: An operating environment is the location where a programme may be executed…
Q: The vast majority of home equipment can now interact wirelessly thanks to recent technological…
A: Wireless information: Wireless communication technology transmits information using electromagnetic…
Q: Is utilising a peer-to-peer networking system beneficial or detrimental?
A:
Q: 1. Draw a picture illustrating the contents of memory, given the following data declarations: You…
A: The Memory Layout looks like Byte by Byte Address Data 0x1000 4a 0x1001 61…
Q: cal system in w on an array of s of the array is 2 by the merge s
A:
Q: What are the three degrees of data abstraction that are available?
A: The Answer start from step-2.
Q: What are the four most important facets of software development, in terms of importance? Four…
A: Given: What are the four most significant facets of software development?To increase overall program…
Q: How can a computer accomplish multitasking in a single machine scenario? Explanation utilising a…
A: Multitasking is the execution of numerous tasks (also known as processes) simultaneously over a…
Q: QUESTION 1 Given below NFA a) Convert the NFAs to DFAs b) Describe the regular expression NFA 1 Q5 E…
A: 1) NFA to DFA convert
Q: Which of the statements below is false about c#? A.The Program execution starts at the Main method…
A: Introduction: C# is a general-purpose, modern and object-oriented programming language pronounced as…
Q: The majority of today's appliances can communicate wirelessly, thanks to recent breakthroughs in…
A: Introduction: Technology has revolutionized our world and daily lives. Additionally, technology for…
Q: What do you think is the most important part of the software development process? Don't just state…
A: Given: In your opinion, which of the several stages that are often included in the process of…
Q: What is the X window system? Explain its architecture. What is xFree86?
A: A network-based graphical window system, sometimes known as X, is the X Window System. Client-server…
Q: Do subsystems of huge computer processes and programmes make sense when broken into smaller…
A: Virtual memory segmentation: Every process is divided into several segments, not all of which are…
Q: Which architectural pattern is best for applications where data is produced by one component and…
A: Which architectural pattern is best for applications where data is produced by one component and…
Q: create a simple C# language payroll program that has Encapsulation and inheritance.
A: In this problem, we need to design the c# code and show examples around Encapsulation and…
Q: Which of the following if remove in the c# program will not affect the execution even if it not…
A: The given question are multiple choice selected question.
Q: In what cases does it make sense to split down large-scale computer processes and programmes into…
A: The Answer is in step2
Q: A certain grade of steel is graded according to the following conditions: (i) Hardness must be…
A: Let in the following code, h = Hardness of steel cc = Carbon content ts = Tensile strength…
Q: 1. Consider the following instruction: Instruction: AND Rd, Rs. Rt Interpretation: Reg[Rd]= Reg[Rs]…
A: a) ALU Operation is AND,BSrc will look to register,OpSel will tell ALU to perform AND. MemW is…
Q: What are optimization problems? How is greedy algorithm or dynamic problem play a role in solving an…
A: Finding the ideal answer from among all viable possibilities is known as the optimization issue.…
Q: Exactly why does a systems analyst need translation skills? What kinds of organisations may be…
A: Given: Non-technical people rely on systems analysts to translate complex concepts into plain…
Q: Question 1: answer by true or false - The level of Ordinal data can characterized with a fixed zero…
A: 1. Data that may be meaningfully ordered by order of magnitude are said to be at the ordinal level.…
Q: How operating systems implement processes remains a mystery to us.
A: implementing processes in operating systems Processes are implemented by operating systems: Process…
Q: How can you tell whether the use of the cloud creates a security risk? Can we keep them safe?
A: The use of cloud resources to load, store, and process data in cloud spaces are known as cloud…
Q: In the search method of a circular list, care must be taken to store the pointer (or reference) of…
A: The question is to comment on the given statement: In the search method of a circular list, care…
Q: What exactly is meant by the term "nearest neighbour" (NN)?
A: Introduction: NEAREST NEIGHBOR TERM: Nearest neighbor heuristic is a algorithm which is used the…
Q: What kinds of worries do people often have in relation to incidents involving cybercrime
A: Concerns around cybercrime cases need to be addressed. Cybercrimes have developed fast in our period…
Q: Wireless networks provide a number of technological difficulties because of their design. Using your…
A: The following are the ramifications for users and technology: There is an issue with integration:-…
Q: Problem 2: Write a Java program to perform the following: Present the user with a menu of selections…
A: The JAVA code is given below with code and output screenshots switch statement is used in the code
Q: In terms of cyber security, how has technology changed human behaviour?
A: Against the onslaught of cyberattacks, systems, networks, programmers, devices, and data are guarded…
Q: In software development, what are the four most significant attributes that may be subdivided?…
A: The process of generating, building, deploying, and supporting software is called "software…
Q: reads data from a file and writes data to the file.... Use a list to store the data read from the…
A: the program is an given below :
Q: what are the two main functions of the network layer (choose two)? a. Routing b. Addressing c.…
A: Let's first take a brief view of the network layer in the OSI model Network layer is at the number…
Q: The causes of cyberbullying, as well as its effects on society and ways to stop it, are all talked…
A: According to Section 500 of the Indian Penal Code, which addresses defamation, forgery of the…
Q: How many host are required for each route n this daigram? Fa0 PC-PT Fa0/1 PC_IPOH1 Fa0/3 Fa0/0.…
A: It is defined as a physical or virtual internet working device that is designed to receive, analyze,…
Q: What can a Designer's bounding box tell you about an object's properties
A: Introduction : A Bounding box is an imaginary rectangle that serves as a point of reference…
Q: The task is to use structures and arrays, make a list of 30 students and store their information in…
A: Note: As no language is specified, the below code is in python language. Start. Read the inputs.…
Q: Write a program to reverse a string.
A:
Q: What can we learn about making suggestions and drawing conclusions from the world of cyber crime?
A: Given: In terms of providing suggestions and drawing conclusions, what are the lessons that may be…
Q: What is the relevance of kernel mode for operating systems?
A: Kernel Mode is a mode of operation that employs the kernel. The executed code has full and…
Q: It is advantageous to utilise asymmetric encryption methods, such as those used in public-key…
A: Public-key cryptography: Public-key cryptography is another name for this kind of encryption. This…
Q: ite a technical report about the 2-tier (collapsed) rarchical design model. Create a design to…
A: SUMMARY Two-Tier Collapsed Core Design The three-tier hierarchical design maximizes depiction,…
Q: What is the difference between a data attribute and a data item in the data hierarchy? What is an…
A: Introduction: Hierarchy is a method of structuring an organization that involves multiple levels of…
Q: 12.1 15 16 17 The following figure shows plots for three functions up to input size of 6. Is this…
A:
Q: What is the execution of the following code? What is the execution of the following code? A=3 B=5.2…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Solve the subparts A,B with full step and no reject thank u
Step by step
Solved in 2 steps with 5 images

- Write a MapReduce program that uses pairs approach and outputs the relative frequency of word pairs. - Given “(a, b)” and word pair “(b, a)”, they are considered as different word pairs, - Do not output count the pair of same words, e.g., “(a, a)”, - The words are considered co-occurred if they are in the same line and the number of words between themGiven the head of a singly linked list of integers, write the function to arrange the elements such thatall the even numbers are placed after all the odd numbers. The relative order of the odd and eventerms should remain unchanged.Input Format:Elements of linked listOutput Format:Resultant linked listSample Input 1:1 4 5 2Sample Output 1:1 5 4 2Sample Input 2:1 11 3 6 8 0 9Sample Output 2:1 11 3 9 6 8 0 in javaIn C language, implement the following two functions that allow breaking a string into non-empty tokens using a given delimiter. For example, For a string "abc-EFG-hi", and a delimiter '-': the list of tokens is ["abc", "EFG", "hi"] For a string "abc-EFG---hi-", and a delimiter '-': the list of tokens is ["abc", "EFG", "hi"] For a string "abc", and a delimiter ' ': the list of tokens is ["abc"] For a string "++abc++", and a delimiter '+': the list of tokens is ["abc"] That is, we break the string using the given delimiter, and the tokens are only the non-empty substrings. 1. The function count_tokens gets a string str, and a char delim, and returns the number of tokens in the string separated by delim. int count_tokens(const char* str, char delim); For example count_tokens("abc-EFG--", '-') needs to return 2. count_tokens("++a+b+c", '+') needs to return 3. count_tokens("***", '*') needs to return 0. 2. The function get_tokens gets a string str, and a char delim, and returns the…
- Write a program that animates quadratic probing,as shown in Figure . You can change the initial size of the hash-table in theprogram. Assume the load-factor threshold to be 0.8.Let Σ = {a, b, c}, let L1 be the set of all the strings over Σ which have the same number ofa’s, b’s and c’s, and let L2 the set of strings of Σ where all the a’s precede all the b’s andall the b’s precede all the c’s. What is:(a) L1 ∩ L2?(b) L1 ∪ L2?(c) L1?(d) L2?(e) L1 ⊕ L2?Implement the following function in C programming language that get a string, and compute an array of non-empty tokens of the string containing only lower-case letters. For example: ● For a string "abc EFaG hi", the list of tokens with only lower-case letters is ["abc", "hi"]. ● For a string "ab 12 ef hi ", the list of such tokens is ["ab","ef","hi"]. ● For a string "abc 12EFG hi ", the list of such tokens is ["ab","hi"]. ● For a string " abc ", the list of such tokens is ["abc"]. ● For a string "+*abc!! B" the list of such tokens is empty.That is, we break the string using the spaces as delimiters (ascii value 32), and look only at the tokens with lower-case letters only . The function get_tokens gets a string str, and returns the array with the tokens containing only lower-case letters in the correct order. The length of the array should be the number of tokens, computed in count_tokens. char** get_tokens(const char* str); For example:● get_tokens("abcEFaG…
- Develop a brute-force algorithm that finds the longest common sequential elements of two given lists with the Java programming language. For example, the following two lists are given: S1 = [B,C,D,A,A,C,D] S2 = [A,C,D,B,A,C] Common lists are: [B,C], [C,D,A,C], [D,A,C], [A,A,C], [A,C], [C,D], … Note that although both lists have a common [C,D,A,C] (sub)list, both list items are skipped and the left-to-right order is intact. Apply the brute force algorithm. Explain Time Complexity?You are given a string X of length n and another string Y of length m ≤n. Say,the indexes p1, p2, p3, p4 and q1, q2, q3, q4 form two sub-sequences, i.e., 0 ≤ p1 < p2 < p3 < p4 < nand 0 ≤q1 < q2 < q3 < q4 < n; then, they are non-overlapping if p4 < q1.The task is to count the maximum number of non-overlapping sub-sequences of X that are thesame as Y . Thus, if X = GAXTYAWBGTAUGBTABGRGTAXB and Y = GTAB, then the answer is3 as shown by the red fonts. We cannot select the underlined GTAB as it overlaps with a red GTAB(i.e., among overlapping sub-sequences, you can select only one of them).Describe an O(m + n) time algorithm to obtain the count. Write a pseudo-code.Implement the following two functions that allow breaking a string into non-empty tokens using a given delimiter in c language . For example, ● For a string “abc-EFG-hi”, and a delimiter ‘-’ : the list of tokens is [“abc”, “EFG”, “hi”] ● For a string “abc-EFG---hi-”, and a delimiter ‘-’ : the list of tokens is [“abc”, “EFG”, “hi”] ● For a string “abc”, and a delimiter ‘ ’ : the list of tokens is [“abc”] ● For a string “++abc++”, and a delimiter ‘+’ : the list of tokens is [“abc”] That is, we break the string using the given delimiter, and the tokens are only the non-empty substrings. The function count_tokens gets a string str, and a char delim, and returns the number of tokens in the string separated by delim. int count_tokens(const char* str, char delim); For example● count_tokens("abc-EFG--",'-')needstoreturn2. ● count_tokens("++a+b+c",'+')needstoreturn3.● count_tokens("***",'*')needstoreturn0.The function get_tokens gets a string str, and a char delim, and returns the…
- Implement the following two functions that allow breaking a string into non-empty tokens using a given delimiter in c language . For example, ● For a string “abc-EFG-hi”, and a delimiter ‘-’ : the list of tokens is [“abc”, “EFG”, “hi”] ● For a string “abc-EFG---hi-”, and a delimiter ‘-’ : the list of tokens is [“abc”, “EFG”, “hi”] ● For a string “abc”, and a delimiter ‘ ’ : the list of tokens is [“abc”] ● For a string “++abc++”, and a delimiter ‘+’ : the list of tokens is [“abc”] That is, we break the string using the given delimiter, and the tokens are only the non-empty substrings.Suppose you are given two circularly linked lists, L and M. Develop javaapplication for telling if L and M store the same sequence of elements (butperhaps with different starting points).Write programs with these input and output Given positive integers m and n, find the number of ontofunctions from a set with m elements to a set with n elements.

