Given the following snippet of kernel code: _private int8 vec = (int8) (-3, -2, -1, 0, 1, 2, 3, 4); vec++; vec.s135 = vec.s357 < 2; What will the final contents of vec be? Select one: a. None of the choices are correct b. (-2, 1, 0, 0, 2, 0, 4, 5) c. (-2,-1, 0, 1, 2, 3, 4, 5) d. (-1,-1,-1, 0, 0, 3, 4, 5) e. (-2,-1, 0, 0, 2, 0, 4, 5) Clear my choice Which of the following statements about parallel patterns is/are TRUE? 1. A geometric decomposition pattern requires data to be modified before computation. 2. A stencil pattern requires access to neighbouring data. 3. A mapping pattern must use associative operators. Select one: a. 1 and 2 b. 2 and 3 c. 1 and 3 d. 1 only e. 2 only Clear my choice Which of the following statements related to heterogeneous computing is/are TRUE? 1. CPUs and GPUs are the only types of processors in heterogeneous computing. 2. Heterogeneous computing can be used to perform parallel computing. 3. The processing capabilities of CPUs and GPUs are different. Select one: a. 1 only b. 2 only c. 1 and 3 d. 1 and 2 e. 2 and 3
Given the following snippet of kernel code: _private int8 vec = (int8) (-3, -2, -1, 0, 1, 2, 3, 4); vec++; vec.s135 = vec.s357 < 2; What will the final contents of vec be? Select one: a. None of the choices are correct b. (-2, 1, 0, 0, 2, 0, 4, 5) c. (-2,-1, 0, 1, 2, 3, 4, 5) d. (-1,-1,-1, 0, 0, 3, 4, 5) e. (-2,-1, 0, 0, 2, 0, 4, 5) Clear my choice Which of the following statements about parallel patterns is/are TRUE? 1. A geometric decomposition pattern requires data to be modified before computation. 2. A stencil pattern requires access to neighbouring data. 3. A mapping pattern must use associative operators. Select one: a. 1 and 2 b. 2 and 3 c. 1 and 3 d. 1 only e. 2 only Clear my choice Which of the following statements related to heterogeneous computing is/are TRUE? 1. CPUs and GPUs are the only types of processors in heterogeneous computing. 2. Heterogeneous computing can be used to perform parallel computing. 3. The processing capabilities of CPUs and GPUs are different. Select one: a. 1 only b. 2 only c. 1 and 3 d. 1 and 2 e. 2 and 3
Chapter14: Security, Troubleshooting, And Performance
Section: Chapter Questions
Problem 7HOP
Related questions
Question
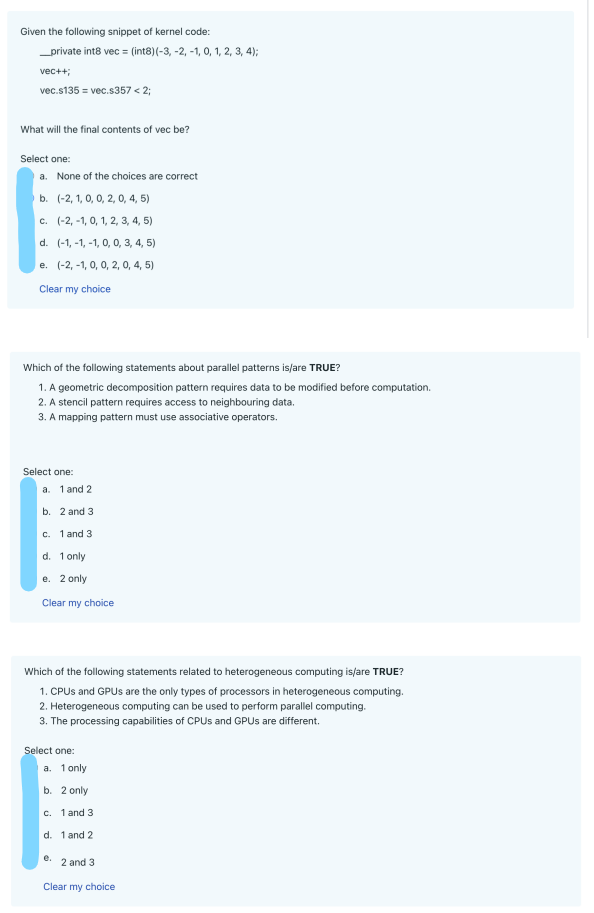
Transcribed Image Text:Given the following snippet of kernel code:
__private int8 vec = (int8) (-3, -2, -1, 0, 1, 2, 3, 4);
vec++;
vec.s135 = vec.s357 < 2;
What will the final contents of vec be?
Select one:
a. None of the choices are correct
b. (-2, 1, 0, 0, 2, 0, 4, 5)
c. (-2,-1, 0, 1, 2, 3, 4, 5)
d. (-1,-1,-1, 0, 0, 3, 4, 5)
e. (-2,-1, 0, 0, 2, 0, 4, 5)
Clear my choice
Which of the following statements about parallel patterns is/are TRUE?
1. A geometric decomposition pattern requires data to be modified before computation.
2. A stencil pattern requires access to neighbouring data.
3. A mapping pattern must use associative operators.
Select one:
a. 1 and 2
b. 2 and 3.
c. 1 and 3
d. 1 only
e. 2 only
Clear my choice
Which of the following statements related to heterogeneous computing is/are TRUE?
1. CPUs and GPUs are the only types of processors in heterogeneous computing.
2. Heterogeneous computing can be used to perform parallel computing.
3. The processing capabilities of CPUs and GPUs are different.
Select one:
a. 1 only
b. 2 only
c. 1 and 3
d. 1 and 2
e.
2 and 3
Clear my choice
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L