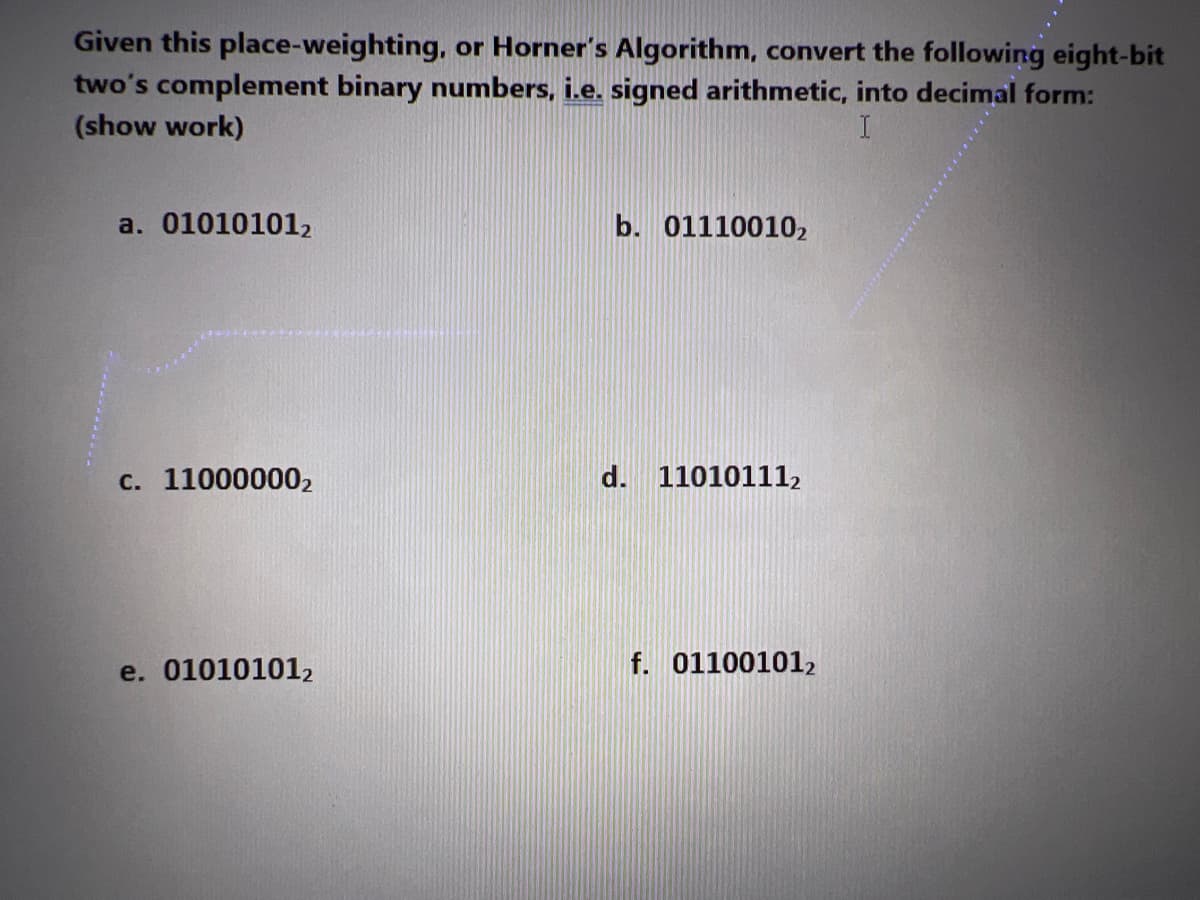
Given this place-weighting, or Horner's Algorithm, convert the following eight-bit two's complement binary numbers, i.e. signed arithmetic, into decimal form: (show work) I
Q: What distinguishes vertical microcode from horizontal microcode is its vertical orientation.
A: Definition: Microcode is a notion in processor design that adds an organisational layer between the…
Q: Write a context-free grammar that accepts the language L = anbmck, n > m, m ≥ 0, k > 1. The alphabet…
A: Context free grammar (CFG) is a formal grammar used to create all possible patterns of strings of a…
Q: please no hand weriting
A: Data mining methods may be used to take use of the data warehouse's capabilities for supporting…
Q: What exactly does it imply when people talk about cascading style sheets? Where does CSS rank in…
A: HTML is used to structure the content on the web page. CSS is used to add style to the content of a…
Q: What certifications are needed to work in artificial intelligence and machine learning?
A: Artificial Intelligence: Artificial intelligence (AI) is the emulation of human intellect in devices…
Q: Using a static route would be suitable in what sorts of situations, and when?
A: The Answer is given below step.
Q: Create comments of the c program (provided below) in every line. #include int main() { char…
A: In this question there is a program of C language has given. We need to write the comments of each…
Q: The usage of artificial intelligence in the classroom is a question that has to be answered.
A: Explanation: The following is a list of some of the beneficial applications of AI that are employed…
Q: Use Java Programming Language Create a Loan Account Hierarchy consisting of the following classes:…
A:
Q: In the context of Java multi-threaded programming, explain the difference between a task and a…
A: Multithreading Multithreading in java is process of executing multiple threads simultaneously.…
Q: What are the stages that must be traversed before an instruction may be carried out? Give a quick…
A: Instruction cycle The instruction cycle is related to the CPU (Central processing unit), a list of…
Q: Give the order of growth for each of the following: 1. 10n + 100/ lg n
A: As per guidelines I can answer only first question. Thank You.
Q: Why is it not common practise to write big application programmes in assembly language?
A: Answer:
Q: How do the addresses of memory get calculated while using Assembly Language?
A: Inspection: A binary digit, often known as a bit, is the smallest unit of information that may be…
Q: MCQ: 1. Which of the following is the correct main method in java? a. Must be declared as a static…
A: Note : As per the company guidelines we are suppose to answer only one Question Kindly post the…
Q: Write a Java Program to add two numbers without using addition operator. Take both numbers from the…
A: Coded using Java.
Q: Many talented engineers around the world want to contribute to his project. The re-discharge flows…
A: Input and output details: The first line of the input contains a single integer TT denoting the…
Q: What is the effect of concurrent programming on the interactions between processes?
A: The answer is given in the below step
Q: Find the minimum (smallest) value in the list D. And draw a flowchart list…
A: Answer the above question are as follows
Q: What are the common characteristics shared by CSS padding and border?
A: The answer of the question is given below
Q: Justify the need of using JAD as a requirement elicitation technique for the depth of data selection…
A: JAD: JAD is a preferred technique in the requirement elicitation process when the choice is based on…
Q: What command displays information about an interface's line, protocol, DLCI, and LMI?
A: Displaying Network Interface Statistics is the function of the display interface command.
Q: As a network administrator, when would you find it helpful to utilise a static route setting?
A: Every router must have a route to know where to send traffic. We compare this to the post office’s…
Q: Explain the following terms in Excel with Example SumIF SumIFS CountIFS Vlook up…
A: “Since you have posted a question with multiple sub-parts, we will solve first three sub-parts for…
Q: → Part 4: Order Up! Complete the function order lunches, which takes two arguments: • stock: A…
A: Python (main.py) #function order_lanches @ two arguments stock(dict) and orders(list) def…
Q: To What Advantages Does the Use of CSS Lead?
A: Given: The advantages of using CSS are then CSS reduces time CSS may be created once and used in…
Q: Create a function that transforms sentences ending with multiple question marks? or exclamation…
A: 1. Created the new method and pass the string arguments2. Add the replace logic.3. return the String
Q: Explain in an easy-to-understand way the primary differences between multiprogrammed batch…
A: Multitasking is a logical: Step after multiprogramming and is often referred to as time-sharing…
Q: Are these two graphs isomorphic? If so, why? If not, why not? (You must provide an explanation for…
A: Consider first graph, Set of vertices= {A, B, C, D, E, F, G} non directional edges are present…
Q: You roll two dice. Each die has six faces, which contain one, two, three, four, five and six spots,…
A: Here no specific language is mentioned so I am using python to write this code.
Q: What's the difference between a web app and a desktop app when it comes to testing?
A: The answer to the question is given below
Q: Concurrency control and locking is the mechanism used by DBMSs for the sharing of data. Lock…
A: Introduction: Lock Granularity Granularity: It is the size of data item allowed to lock. Multiple…
Q: When it comes to application deployment, how can you distinguish the difference between publishing…
A: Application and Deploying: The act of installing, configuring, upgrading, and enabling a single…
Q: What exactly is the difference between a broadcast domain and a collision domain?
A: Difference between a broadcast domain and a collision domain.
Q: What elements influence the appeal of cybercrime to particular people?
A: Introduction: Cybercrime is a type of crime that occurs when a computer is used for illicit…
Q: When it comes to a router's "Data Plane," what is its purpose? The item's function is unclear
A: Answer:
Q: Use the university schema to answer the following question. Fill in the blank to remove the student…
A: SQL (Structured Query Language) is used to perform operations on the records stored in the database,…
Q: Problem: Implement a part of functionality for the Netflix DVD queue. It's a service that allows a…
A: There are 3 files: 1. MovieList.h 2. MovieList.cpp 3. Main.cpp
Q: In PYTHON, write a program that reads elements from a list, where each element from the list is a…
A: logic:- use for each loop to iterate nested loop. for i in numbers: a=i[0] b=i[1]…
Q: Because of their inherent characteristics, wireless networks are prone to a variety of problems. Let…
A: Given: Local wireless networks (WLANs) send and receive data using radio, per the query. Lack of a…
Q: Question 2. Consider the language L = {a^ | n is a prime number}. Is this language regular or…
A: Given language L = {an | n is prime number} ,
Q: o Asap
A: The answer is given below:
Q: What's the difference between a web app and a desktop app when it comes to testing?
A: Desktop apps don't need an internet connection. A web application runs in your browser without being…
Q: blogging and cloud computing?
A: blogging: Social blogging, often known as microblogging, is a subset of blogging that features…
Q: Using a static route would be suitable in what sorts of situations, and when?
A: Information recovery methods by use of two parities By storing two sets of parity data on a…
Q: What is the most crucial aspect of the transition from serial to batch processing?
A: Introduction: The most important change that came about as a result of switching from serial to…
Q: lly Be Carried Out O
A: What Kinds Of Operations Can Typically Be Carried Out On A Data Structure?
Q: A combinational circuit is to be designed which takes 4 inputs and one output. The output = 1, if…
A: The answers to the given questions are in subsequent steps.
Q: Computer science What is ethnography and what is its goal? Is ethnographic research qualitative or…
A: Introduction: Ethnography is a type of study that is carried out by directly watching users in their…
Q: The analytical method relies heavily on the use of data modelling. In order to build a model, we'll…
A: The answer is written in step 2
Step by step
Solved in 2 steps

- Work out the following without using a calculator 111010102 + 21228 + ABC16 - 1238, Give your answer in decimal Given a binary number 11100101, find its equivalent in Decimal using Horner’s Rule Multiply the following binary numbers: 11011.101 by 101.111 Convert A74816 to octal equivalents Using Subtraction by 2’s Complement: 10100.01 – 11011.10Using a "word" of 4 bits, list all of the possible signed binary numbers and their decimal equivalents that are representable in: a) Unsigned integer, b) Signed magnitude, c) One’s complement, d) Two's complementBinary Unsigned IntegerSigned MagnitudeOne’sComplementTwo’s Complement0000000100100011010001010110011110001001101010111100110111101111Convert the fractional number (59.65625) ten to its binary equivalent. Work out the following without using a calculator 111010102 + 21228 + ABC16 - 1238, Give your answer in decimal Given a binary number 11100101, find its equivalent in Decimal using Horner’s Rule Multiply the following binary numbers: 11011.101 by 101.111 Convert A74816 to octal equivalents Using Subtraction by 2’s Complement: 10100.01 – 11011.10
- The binary numbers illustrated below are 4-bit 2's complement binary numbers. Which of the following operations generates an overflow? Justify your answer by converting the operands and outcomes to decimals. a. 1111 + 0111 b. 1001 - 0011 c. 0111 + 0110Here are several ways to express the number 30 in binary, which uses just the lower eight bits of the integer's representation: One's a) Complement; b) Excess-M:?Assume that D has the value 1010101010 and that the 5-bit generator G=10011 is used. What does R stand for? B. C. Does corruption exist? Publish your work. Repetition of parts a and b with the addition of the following: the numbers 1001010101, 0101101010, and 1010100000
- Please explain step by step:Let e = 2.71828183 be the Euler’s number with 8 decimal digits of precision.Find the binary scientific notation of e with five bits after the binary point; i.e. find integer n and bits x1, x2, . . . , x5 such that e = 1.x1x2x3x4x5 × 2 n .Find the single-precision IEEE 754 representation of e. (Hint: Round the result of 223e to the closest integer like m. Convert m to its normalized binary scientific notation and round its fraction to 23 bits after the binary point. Finally, find the normalized binary scientific notation of m/2 23 by subtracting 23 from the power of two in the representation of m).Using 32 bits what would the word "Bob!" look like in hexadecimal and binary. (Do not encode the quotes, just the text inside of the quotes) The answer is not 01000010 01101111 01100010 00100001 and (42 6F 62 21)ha. What decimal number is represented by the following single precisionfloat?1 0111 1100 0110 0000 0110 0000 0000 000b. What decimal number is represented by the following single precisionfloat?1 0101 1100 0110 0010 0110 0000 0000 000c. How many bits are needed to represent 57B(Hex) in binary?
- In an 8-bit binary number, which is the most significant bit (MSB)? What is the decimal representation of each of the following unsigned binary integers? 00110101 b. 10010110 c. 11001100 What is the sum of each pair of binary integers? 10101111 + 11011011 10010111 + 11111111 01110101 + 10101100 Calculate binary 00001101 minus 00000111. How many bits are used by each of the following data types? word doubleword quadword double quadword What is the minimum number of binary bits needed to represent each of the following unsigned decimal integers? 4095 65534 42319 What is the hexadecimal representation of each of the following binary numbers? 0011 0101 1101 1010 1100 1110 1010 0011 1111 1110 1101 1011 What is the binary representation of the following hexadecimal numbers? 0126F9D4 6ACDFA95 F69BDC2A Whatistheunsigneddecimalrepresentationofeachofthefollowinghexadecimalintegers? 3A 1BF 1001…Add the following binary numbers, show your work:101101 + 111000100100 + 1100111111 + 1110110110101 + 1011011111101001 + 1101101001101 + 1101100101010011010 + 110101101Let these 2 variables be signed binary numbers, P=110100 (-12) and Q=000110 (6). a) Multiply P and Q b) Divide P by Q.

