Given two IPV6 nodes would like to communicate using IPV6 datagram, but they are connected to each other through IPV4 routers. Which of the following solutions is best implemented in this scenario?
Given two IPV6 nodes would like to communicate using IPV6 datagram, but they are connected to each other through IPV4 routers. Which of the following solutions is best implemented in this scenario?
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter8: Network Infrastructure And Troubleshooting
Section: Chapter Questions
Problem 2TC
Related questions
Question
please help with these practice problems
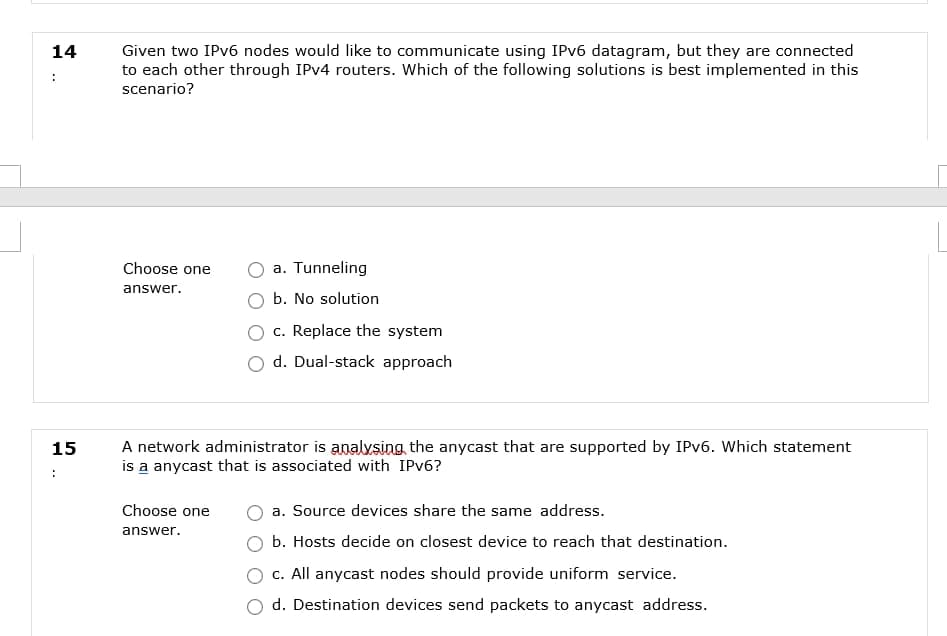
Transcribed Image Text:Given two IPv6 nodes would like to communicate using IPV6 datagram, but they are connected
to each other through IPV4 routers. Which of the following solutions is best implemented in this
14
scenario?
Choose one
a. Tunneling
answer.
b. No solution
c. Replace the system
d. Dual-stack approach
A network administrator is analvsing the anycast that are supported by IPV6. Which statement
is a anycast that is associated with IPV6?
15
:
Choose one
a. Source devices share the same address.
answer.
b. Hosts decide on closest device to reach that destination.
c. All anycast nodes should provide uniform service.
d. Destination devices send packets to anycast address.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,