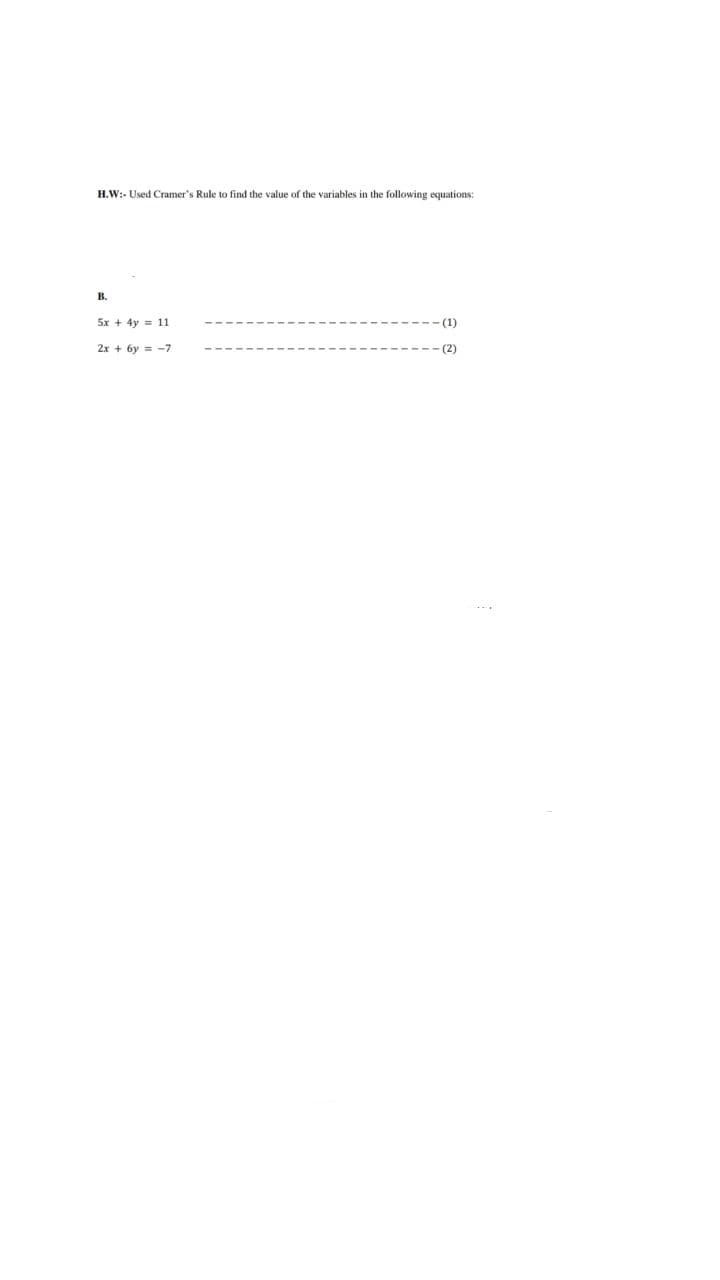
H.W:- Used Cramer's Rule to find the value of the variables in the following equations: B. 5x + 4y = 11 - (1) 2x+6y= -7 -(2) I
Q: Service management is more difficult than manufacturing.
A: Input variability tends to be higher in many service environments than in manufacturing.
Q: When explaining processes that aren't included in the systems analysis process, you can find it…
A: The answer is given in the below step
Q: Hank develops a craving for ice cream while bringing a liver for transplantation to a local…
A: Start: Compensation for workers.Workers' compensation for workers who have suffered and died, or…
Q: As a systems analyst, how can you make sure that the basis for system design is solid and stable?
A: answer is
Q: Q. In sql how to fetch the records of all employees from a Employee table .
A: Select Statement: We use SELECT statement to fetch the data from a table. To fetch the all data use…
Q: 5- To print the result of the equation m=x+4d in the program, it is at next figure
A: To display output to the screen in FORTRAN language the print* statement is used. This print*…
Q: When describing processes that are not part of a systems study, structured language might be useful.
A: Introduction: According to the definition, systems analysis is "the act of studying a procedure or…
Q: Is it possible for two different network interfaces to have the same MAC address? Or not? Is it…
A: Given: On a local network, no two devices should have the same MAC address. If this occurs, both…
Q: word. (a) What is the probability that T(w) = 10100011? (b) What is the probability that T(w) =…
A: The answer is
Q: To completely define a variable, including its 'type' and 'additional characteristics' Variables…
A: Please refer to the following step for the complete solution of the problem above.
Q: Services allowed for usage in the cloud, including information on how to get started and create an…
A: Cloud computing has been credited with increasing competition by reducing costs, greater…
Q: In what ways is it important that software testing be done in stages? It's a well-known fact that…
A: Software testing determines whether the actual software product matches the expected requirements…
Q: Give an explanation of what the term "Software Engineering" means. The paradigm of softw
A: The answer is
Q: How many interfaces exist between functions so that they may interact with one another? Explain…
A: Functions may interact with one another in five distinct ways: line of code (CLI) user interface…
Q: Create a Python program to load the iris data from a given csv file into a data frame and print the…
A: Question given - Read iris data set and perform given operations on this. Solution - Programming…
Q: Answer Needed in Assembly Language please! Store the two 8 bit numbers in registers • compare them…
A: We need to write an assembly code for the given scenario. The architecture used is 8085.
Q: Explain and briefly explain how transportation experts assess the unique hazards that their firms…
A: Transportation experts have noted the following risk factors:
Q: What kinds of cultural and global political factors, such privacy rights, are taken into account…
A: Development: Data is pricey and every business's fuel. Today, data is shared abroad and used to make…
Q: Do several methods of authentication have any negative effects? What precisely does it do to assist…
A: Given: Next, we will walk you through an explanation of what multi-factor authentication is, as well…
Q: Acquire as much information as possible about social media. What exactly is autonomous computing,…
A: Understand every aspect of social media. How can autonomous computing benefit the cloud computing…
Q: studying the inner workings of computers to better understand the processes that make them so…
A: The use of computers in education: Computers are used to aid students' learning in a range of…
Q: In Exercises 11 to 14, use the greedy algorithm to find a Hamiltonian circuit starting at vertex A…
A: Using the Greedy algorithm we find the optimal solution by selecting the best option available at…
Q: When developing software system models, what points of view should be considered?
A: Introduction: The software system is a collection of interconnected software components that form…
Q: What are the four most significant qualities in software development? Consider the other four…
A: Launch: To jot down the four most significant traits Every software design is evaluated first and…
Q: What are the benefits of ICT in business, trav
A: ICT plays a major role in all industries and in everyday life.ICT helps to make a business more…
Q: Why must a systems analyst translate? Who may be involved?
A: Analyst translate: To know about the System Analyst. A systems analyst must function as a…
Q: What problems have been detected in the router's layer 2 protocol? What ramifications does this find…
A: Layer Two Protocol Problems: The Data Link layer is the second tier of the OSI architecture. It…
Q: When creating software system models, what points of view should be taken into account?
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: Summary
A: The UML Sequence diagram for the given scenario is as follows
Q: See whether there are additional applications for Structured English besides just systems analysis.
A: Let's have a look at the response: Introduction:- Structured English is used: Structured English is…
Q: Using Python, create a function that takes a string S as a parameter. This function should return a…
A: Here I have defined the funcition named mostFrequentCharacter(). Inside the function, I have created…
Q: Explain the concept of software engineering using just your own words and your own knowledge of it.
A: The answer of this question is as follows:
Q: In what ways might you put Queueing Analysis to use in the area of Engineering?
A: Queueing analysis is a mathematical analysis method which is mainly used to predict the length of…
Q: Fill in the missing words. CODE SNIPPET
A: Given:
Q: What makes phyton such a desirable cryptocurrency for use in cloud computing? Why is it selected…
A: Python: Python is perfect for cloud-based streaming analytics applications because it offers rapid…
Q: Because of the characteristics that are inherent to them, wireless networks are susceptible to a…
A: Wireless networks: Wireless networks that are reliable and secure are becoming more important to the…
Q: Question 4: Plot the function y = 3x³-26x+10, and its first and second derivatives, for -2≤x≤4. all…
A: Since no programming language is mentioned, I am using Matlab. Code: syms x y=@(x)…
Q: Why risk enabling BYOD?
A: BYOD: Allowing workers to carry or use their own device for official work is not a new concept; in…
Q: Try using Structured English to explain other kinds of processes, even if they have nothing to do…
A: Introduction:
Q: What is the advantage of using Host-Based Behavior-Blocking Software instead of fingerprinting or…
A: Answer
Q: What does the term "system design" mean? A good response is one that is supported by examples
A: the term "system design" mean?
Q: Discuss the social and ethical consequences of using and utilizing information technology.
A: Introduction: The following are some of the social and ethical consequences of using and deploying…
Q: Which of the following steps do you recommend we take to increase the conversion rate on our…
A: Launch: The goal of your website's usability, the relevance of revenue visitors, brand trust, and…
Q: Write in MIPS Assembly language a well-documented program consisting of the two following functions.…
A: .globl main .textmain: jal driver # call function driver…
Q: Write a Java program to define a method that finds and returns the maximum number among integers…
A: Answer:
Q: What exactly does it mean to have a secure physical environment? What are the most significant…
A: What exactly does it mean to have a secure physical environment? When working in cybersecurity,…
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let…
A: The answer is
Q: What are the many sorts of technical systems available, as well as the present level of technology?
A: The range of technical advancement: If innovation is not used, the globe has become an inhabitable…
Q: Write a C program that reads a matrix of n × m numbers, transpose the matrix, then print it out…
A: Sol: #include <stdio.h> #include <stdlib.h> void main() { int a[10][10], r, c, i,…
Q: from collections import Counter How does counter works in Python? Kindly provide some examples as…
A: The sample program is written in Python. Check the program screenshot for the correct indentation.…
Step by step
Solved in 2 steps with 2 images

- Use DeMorgan's law to determine if each of the following pairs of statements are equivalent or not. a) ~(~p V q), p V ~q b~(p V ~q), ~p^q6. B) Write equivalent expressions for each of the following by using De Morgan’s Law. !(a || b) !(y > 2 && !found )Minimize the following expression using Boolean rules: F=XY+X(Y+Z)+Y(Y+Z)
- QUESTION 6 P6.8 Simplify the following Boolean expression using Boolean algebra laws: XY[Y +(XY)]′1) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’yz+x’yz’+xy’z’+xyz+xyz’ , can be written as: 2) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’y’z+x’yz+x’yz’+xy’z’+xyz’ , can be written as: 3)convert the following decimal fractions to binary with a maximum of six places to the right of the binary point: 1)25.84375 2)57.55 3)80.9065 4) Convert the following binary fractions to decimal: 1)100001.111 2)111111.10011 3)1001100.1011 5) Fill in the blank. The representation of 60 in binary using 8-bit signed magnitude is ______, in ones complement is ______, in two’s complement is ______, and in excess-127 is ______.Simplify the following expressions by applying Boolean rules. (XY)(YZ)
- 71. Evaluate the expression given below if A= 16 and B = 15.A % B // A a. 0.0 b. 0 c. 1.0 d. 1(Practice) State whether the following variable names are valid. If they are invalid, state the reason. prod_a c1234 abcd _c3 12345 newamp watts $total new$al a1b2c3d4 9ab6 sum.of average volts1 finvolt(Mechanics) The deflection at any point along the centerline of a cantilevered beam, such as the one used for a balcony (see Figure 5.15), when a load is distributed evenly along the beam is given by this formula: d=wx224EI(x2+6l24lx) d is the deflection at location x (ft). xisthedistancefromthesecuredend( ft).wistheweightplacedattheendofthebeam( lbs/ft).listhebeamlength( ft). Eisthemodulesofelasticity( lbs/f t 2 ).Iisthesecondmomentofinertia( f t 4 ). For the beam shown in Figure 5.15, the second moment of inertia is determined as follows: l=bh312 b is the beam’s base. h is the beam’s height. Using these formulas, write, compile, and run a C++ program that determines and displays a table of the deflection for a cantilevered pine beam at half-foot increments along its length, using the following data: w=200lbs/ftl=3ftE=187.2106lb/ft2b=.2fth=.3ft



