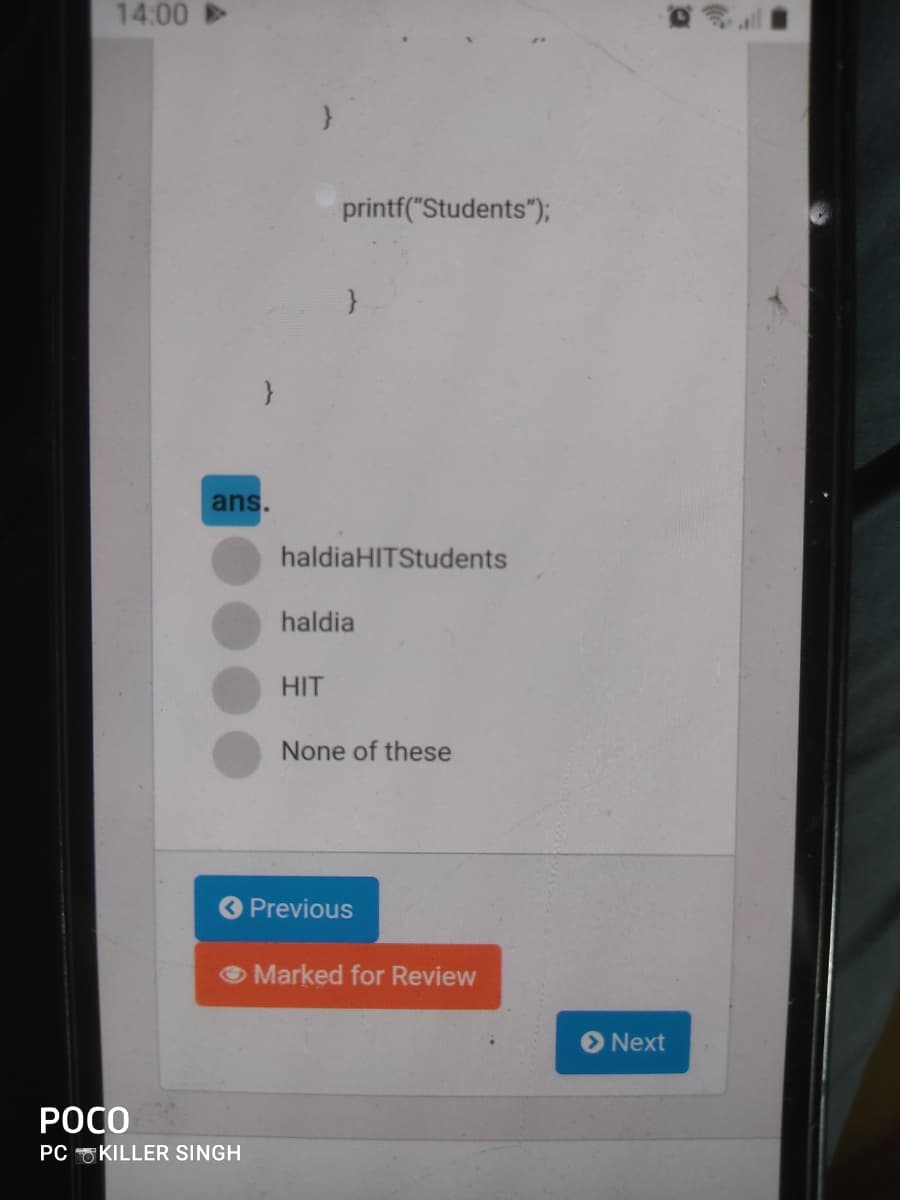
haldiaHITStudents haldia HIT None of these
Q: copy the value of the 8th element of a word array to the 5th element. The starting address of the ar...
A:
Q: What is the time complexity of the: 1+를 +1+1++ O 0(1) O 0 (n) O O (nlgn) O O (lg n)
A: The answer is given below:-
Q: Find regular expressions for the languages accepted by the following automata.
A: The anser is given below:-
Q: mplementation of DFS for water jug problem using python
A: DFS is the depth-first search technique in which first to visit the element and then explore the ele...
Q: What is the output of the following code. Enter the numbers with only one space between them for(int...
A: the answer is
Q: the following system of periodic tasks is scheduled and executed according to a cyclic schedule. Cho...
A: Lets see the solution in the next steps
Q: Demonstrate DFA for the given NFA M= ({qo, q1, q3}, {a, b}, a, {qo}, {q3}) where d is given as a qo ...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: A GSM syatem uses 124 channels and each channel is divided into 8 time slols. What is he masimum num...
A: The answer is
Q: Write a loop to display the powers of 2 exactly as shown below: 16 32 64 128
A: As per answering guidelines since no language mentioned using c++ language.
Q: What exactly is dual-channel memory architecture, and how does it function?
A: Introduction: Computer Memory: In computer science, several forms of memory are utilized. Memory is ...
Q: Design a Java Animal class (assuming in Animal.java file) and a sub class of Animal named Cat (assum...
A: According to the information given:- We have to follow the instruction to get the desired output.
Q: What is the difference between reloading a service and restarting it?
A: Introduction: Despite the fact that the command reload instructs the service to give its configurati...
Q: Please provide two scenarios where asymmetric and symmetric would be used. What advantages does asym...
A: Uses of asymmetirc ecryption - NIST suggested the digital signatures standard, which is described ...
Q: What is the length of the array: int[] intArray = { 1, 2, 3, 5, 6, 7 }; Select one: O a. None of the...
A: length of the array is b. 6
Q: Write a Java program that reads a line and a line segment and then determines whether they intersect...
A: Given :- Write a Java program that reads a line and a line segment and then determines whether they ...
Q: What is the point of having a motherboard?
A: answer is
Q: Consider the following Deterministic Finite Automaton (DFA) with the 5-tuple of (Q,E,90,F,6): 91 q3 ...
A: A string is said to be accepted when we end at one of the final states from the initial state q0. Th...
Q: Disks and all processes share a common memory through a bus, which makes it easier for all of them t...
A: All the processes on a computer share a single memory, called the memory bus. This means that when a...
Q: Who was the first to come up with the idea for a mainframe computer?
A: Introduction: The Harvard Seal According to most sources, I was the first mainframe computer. The ma...
Q: 4. A primary school is conducting a survey on the popularity of certain colours. Students ar asked t...
A: The algorithm is a collection of a finite number of steps to perform a specific task. An algorithm g...
Q: In what cases would you advocate the use of assembly language code in the creation of application so...
A: Introduction: Mnemonic codes, analogous to English words, are used in assembly language. Although de...
Q: Examine the advantages and disadvantages of various system models.
A: System modeling is constructing abstract models of a system, each of which gives a different view or...
Q: Display employees (by name and address) from "Chicago" and with an annual salary between 60000 (incl...
A: The database management system is a collection of data and information and SQL languages are used fo...
Q: Explain how you would choose which of TPCC, TPC-H, or TPC-R best fits the application.
A: Performance Council for Transaction Processing: Using the Transaction Processing Performance Council...
Q: What makes BIOS-level input and output different?
A: BIOS stands for basic input and output which is preloaded program stored in EPROM.
Q: consecutive Os. For example, 1011011101, 011010 etc. How many good binar strings of length k are the...
A: SUMMARY: - Hence, we discussed all the points.
Q: a. Study the algorithm below and implement quickSort method . Additionally you will also need to imp...
A: Python code for quick sort: def partition(arr, low, high): i = (low-1) pivot = arr[high] # pivot...
Q: e number of control
A: Use bezier curve to model the letter 'D
Q: checksum implimentation in c language for the dataword "have a nice day"
A: let us see the answer:- Introduction:- The Checksum is an error detection mechanism that detects err...
Q: Question 1 A) Why we need Artificial Intelligence? B) Explain importance of Turing Test
A: Artificial intelligence : it is basically ability of a computer or a robotic machine to be controlle...
Q: Build the following in Packet Tracer. When complete upload here. • Use network 100.100.100.0/24 as t...
A:
Q: n a C++ program, using loops code this problem, The game of "23" is a two-player game that begins w...
A: Explanation: Include the necessary header files. Ask the human whther human want to play or not. If...
Q: In a Layer 1 frame, what information is normally provided?
A: Answer: In the OSI reference model, there is seven-layer. 1. Physical Layer 2. Data Link Layer 3. N...
Q: Question:: Regardless of how user level threads are implemented, if a programme has two or more user...
A: Ans Before giving ans First of all we need to consider about below points. What exactly is a thread...
Q: Which of the following is a valid multidimensional array? Select one: O a. All of these O b. inti00 ...
A: The general Array declaration (say1-D) in java include is like data_Type[] arrayName; or dat...
Q: . Let S1 and S2 be two stacks. Write a procedure Push(x, S) that pushes element x onto stack S, whe...
A: First of all we should know why two stacks start from the opposite side.This is because so that we c...
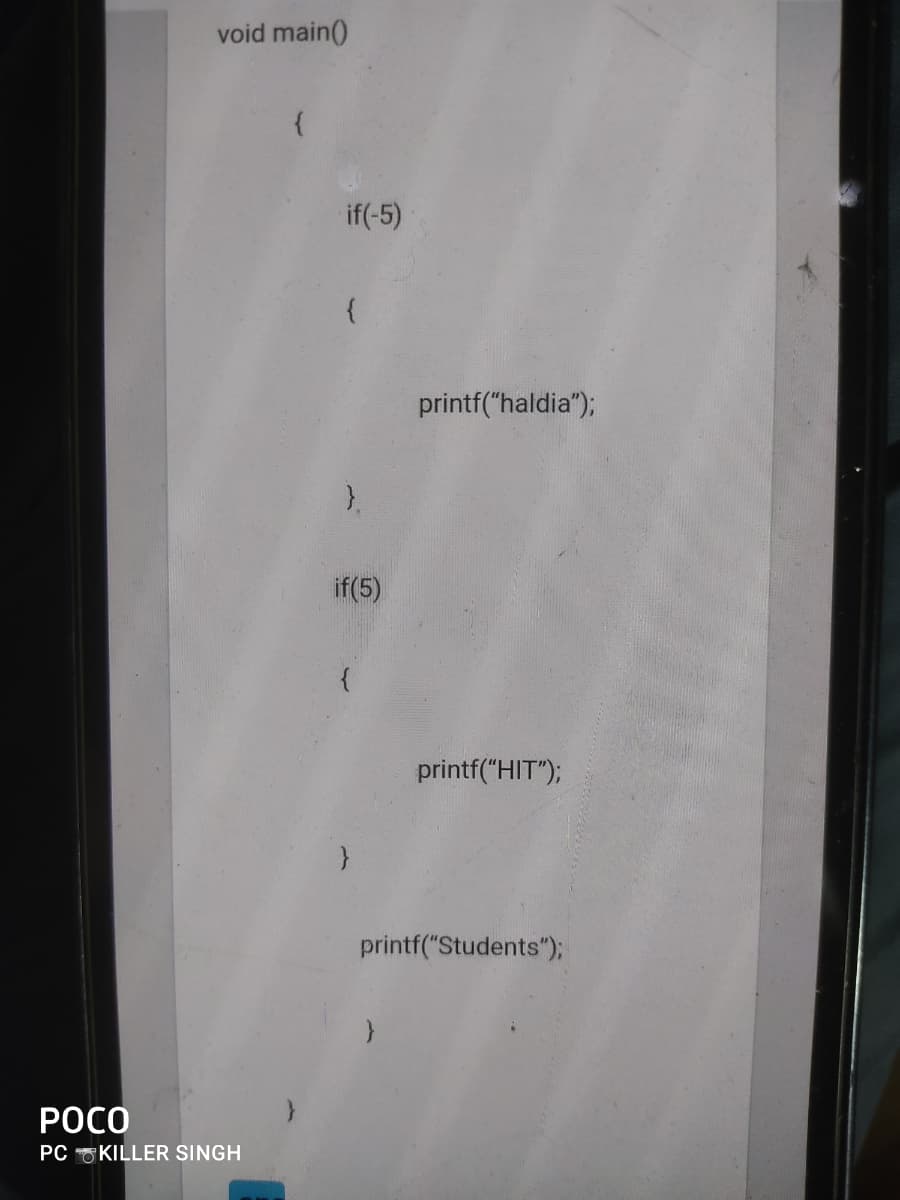
Q: program controls
A: A program is a set of logical instructions that is developed in order to obtain a solution to a prob...
Q: Question : By using jakob Nielsen usability attributes, evaluates a system/interface/equipment ? Not...
A: INTRODUCTION: Tell about the usability attributes.
Q: Which is correct with respect to the size of the data types? ans. double > char >int char>int> float...
A: Option C Char<int<double
Q: Write a code in C++ / cpp to solve the following problem In a hypothetical island, one can buy land...
A: Approach: Follow the steps to solve the problem: •Check if the given N contains digit D or not. If f...
Q: A transaction processing system may not be able to grow at the same rate as it does now. In each of ...
A: Introduction: In a transaction processing system, many factors work against linear scaling up.Parall...
Q: a) A computer program consists of five modules M1, M2, M3, M4, and M5. A relation R on the set of mo...
A: Below is the answer to above question. I hope this will helpful.
Q: Why could the time it takes to access a memory location in a shared-memory architecture vary dependi...
A: Introduction: Shared memory architecture employs the following two models: I Memory access that is c...
Q: Explain how you would choose which of TPCC, TPC-H, or TPC-R best fits the application.
A: Lets see the solution in the next steps
Q: Give the output of this code in c: #include int main() { int x = 5866, y = 5455; int z = x...
A:
Q: A(n) ________________array is a kind of array that utilises two indices
A: Answer: An ................. array is a kind of array that utilises two indices.
Q: Consider the following Haskell functions: step x y = y + 1 mystery iL = foldr step 0 iL What will ...
A: Computer Science Consider the following Haskell functions:step x y = y + 1mystery iL = foldr step 0...
Q: In what circumstances would you recommend using assembly language code in the building of an applica...
A: Assembly language can be defined as a low level programming language that is designed for specific t...
Q: Develop an EER model for the following situation using EER notation, as specified by your instructor...
A: Here is the detailed explanation of ER diagram
Q: Explain oops concepts..with suitable example
A: Object-oriented programming is a programming paradigm in which there is a specific way of writing co...
Step by step
Solved in 2 steps

- Java Programming 1. Write a recursive method to convert from decimal to Binary. 2. Write a recursive method to count the number of vowels in a given string. 3. Write a recursive method to find a character in a string. Your answerjava ..... please solve the questions 1 and 2Question should be done in Java

