hat is the decimal representation of the following: (a) (100000111) 2. (a) (1000111.011011011011) 2. (2). What is the binary representation of the following: (a) (64.37109375) 10- (b) (122.3) 10. (3). (a) Approximate by 27. Find the absolute and the relative error.
Q: Find (49.3)10 - (00110110.0010) BCD = (?), BCD
A: The answer is
Q: Define the terms in brief. 1.Data pre processing 2.Data visualization 3. Machine learning
A: Data preprocessing: It is a data mining approach that is utilised to convert the raw data in a…
Q: Q: Suppose a Jini client caches the tuple it obtained from a JavaSpace so that it can avoid having…
A: Introduction: Consider that a Jini clint caches the tuple it acquired from a Java space in order to…
Q: Experiment with Hypercard or another hypertext system if you have access to one. As you work through…
A:
Q: Convert the following decimal numbers into binary (show the steps): i) 75, ii) 64, iii) 1023
A: Decimal to binary conversion of i) 75:
Q: size, approximately how big is o(n) compared to n?
A: The answer is
Q: .Q: Assume a client calls an asynchronous RPC to a server, and subsequently waits until the server…
A:
Q: RCS adopts a reverse delta approach for storing multiple versions of a file. For example, assume a…
A: Answer: Revision Control System In my point of view and based on the research I have done, RCS can…
Q: . Q: Consider Globe. Outline a simple protocol by which a secure channel is set up between a user…
A: The question has been answered in step2
Q: Description of an open set face recognition problem. How to find threshold? [computer Vision course]
A: Open set face recognition: Whether the probes are real people or frauds must be determined by an…
Q: Q: Does totally ordered multicasting by means of a sequencer and for the sake of consistency in…
A: Total order multicast is a primitive that sends messages to a set of destinations and enforces a…
Q: Senario Programming Competition System – Schools and Universities always want to participate in a…
A: The User Requirements for an automated competition system would include a registration procedure, an…
Q: Someone has attempted to censor my strings by replacing every vowel with a Luckily, I've been able…
A: You have not mentioned any specific language so I provide the code in JavaScript along with output…
Q: Write a 32-bit assembly program and flowchart that clears the screen, locates the cursor near the…
A: CODE SEGMENT START: ASSUME CS:CODE MOV AX,0600H ;06 TO SCROLL & 00 FOR FULLJ SCREEN MOV…
Q: Translate the E-R diagram on page 1 (diagram) to database schema using MySQL Workbench (export as…
A: An Entity Relationship (ER) Diagram is a type of flowchart that illustrates how “entities” such as…
Q: The program below misses the function declaration and definition of Sum_Of_Squares function.…
A: Dear Student, the answer is provided below.
Q: g infix expressions to po
A: Solution - In the given question, we have to convert the given infix expression into postfix…
Q: The biggest three IaaS cloud computing service providers are AWS (Amazon), Azure (Microsoft) and…
A: We need to write a detailed comparison for each given service.
Q: When I input the program the out put is incorrect. Can someone correct the code to output 011?
A: According to the information given in previous question. To implement you have to open Corel…
Q: Define fragmentation and explain why the IPv4 and IPv6 protocols need to fragment some packets. Is…
A: The solution is given in the below step
Q: Write a Java Program that exhibits the syntax of ArrayList declaration and instantiation. Element…
A: Answer:
Q: WHAT IS THE RELATION OF METASTABILITY TO MEMORY ELEMENTS? OWN ANSWER PLEASE. THANK YOU. ILL UPVOTE.…
A: Metastability refers to an energetic state inside a dynamical system other than its condition of…
Q: What is the maximum number of callers in each cell in an IS-95 system?
A:
Q: b. What are the first valid host and last valid host of 4th Subnet?
A: The answer is
Q: Assume you are part of the IEEE committee that will revise the IEEE 1074 standard. You have been…
A:
Q: We have discussed greedy algorithm during lectures. A greedy algorithm is an algorithm that…
A: The correct answer for the above mentioned question is given in below steps.
Q: A number is said to be Disarium if the sum of its digits raised to their respective positions is the…
A: 1) Since you have not specified programming language., I have written below program in python…
Q: What is the relationship between TPS, VPs, and VCs?
A: A transmission path (TP) is a physical connection between a user and a switch or between two…
Q: Please code this in Java. Write a program to input a phone number and output a phone directory with…
A: Hello student Please do like if this solution will help you I really work hard for getting accurate…
Q: Hello. Please help me complete the code. A picture of the problem statement has been provided, as…
A: Ball.java public class Ball { private int x, y; private int rightWallX, rightWallY; private…
Q: How modern compilers perform the same parsing of an n length input string in O(n) time with the same…
A: The modern compilers perform the same parsing of an n length input string in O(n) time with the same…
Q: When do you want to use these loops in java A) a for loop B) a while loop C) a do loop
A: ANSWER:
Q: The TCP/IP Networking Model is called a "de facto" standard, while the OSI Networking Model is…
A: TCP/IP networking model (De facto standard) The third type of the standard often seen in the…
Q: Convert the following binary numbers into decimals (show the steps): i) 11101010, ii) 10111001,…
A: The answer is written in step 2
Q: Describe and discuss the difference between public and private IP addressing. Give one example of a…
A: In this question we need to explain difference between private and public IP addressing with one…
Q: Three types of packets may be transmitted using IPv4: Unicast, Multicast, and Broadcast. Describe…
A: The answer to the question is given below:
Q: Given the following MIPS assembly fragment: bge $s0, $s2, Exit beq $s0, $s1, Process bne $s2, $s3,…
A: Given MIPS fragment: bge $s0, $s2, Exitbeq $s0, $s1, Processbne $s2, $s3, ExitProcess: add $s1, $s3,…
Q: Case Study Hello Holidays Management System Hello Holidays is a travel company based in Selangor.…
A: The question has been answered in step2
Q: (a) How should the description in Problem 5.30 (a) be written to have the same behavior when the…
A: In verilog, (<=) operator is termed as non-blocking assignment operator.In this,the assignment…
Q: Explain the relative advantages and disadvantages of an embedded OS based on an existing commercial…
A: Operating system An operating system goes about as a middle person between the client of a PC and…
Q: Design a schema and show a sample database for that application for 5 different organisations
A: Hello student I am writing this solution as per my best of knowledge Please do like this solution…
Q: Q2/ Write c# function of this following int min ; x = 4; float 2 = 1 ; long y = 1; int a {1,3,9, 10,…
A: As per the given question, we need to implement the following functions in c#: 1. MinMax(a, out m,…
Q: Describe the clocking methodology.
A: ANSWER:
Q: 2. Consider the following network address: a. How many subnets are there in this network? b. What…
A: Introduction The Given network address is 209.15.6.0/28 Means till 28th bits the network id will be…
Q: Write a program that asks the user to enter an integer consisting of 4 digits only, and check how…
A: C programming language is used below to solve the given problem. Algorithm: Start Initialise the…
Q: The Burroughs Adding Machine Company dominated the mechanical calculator market in the 1890s, and…
A: The Burroughs Adding Machine Company surpassed its competitors by combining with an excellent…
Q: What is the distinction between the virtualization approach advocated by Xen and the style of…
A: Let's look out what exactly are the differences between the vitualization approach and the…
Q: We have discussed greedy algorithm during lectures. A greedy algorithm is an algorithm that…
A: Note : Put Main.java and TestInput.txt in same folder 1. Then open command prompt go the folder…
Q: First, read in an input value for variable valCount. Then, read valCount integers from input and…
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT--------------------
Do No 1 for me
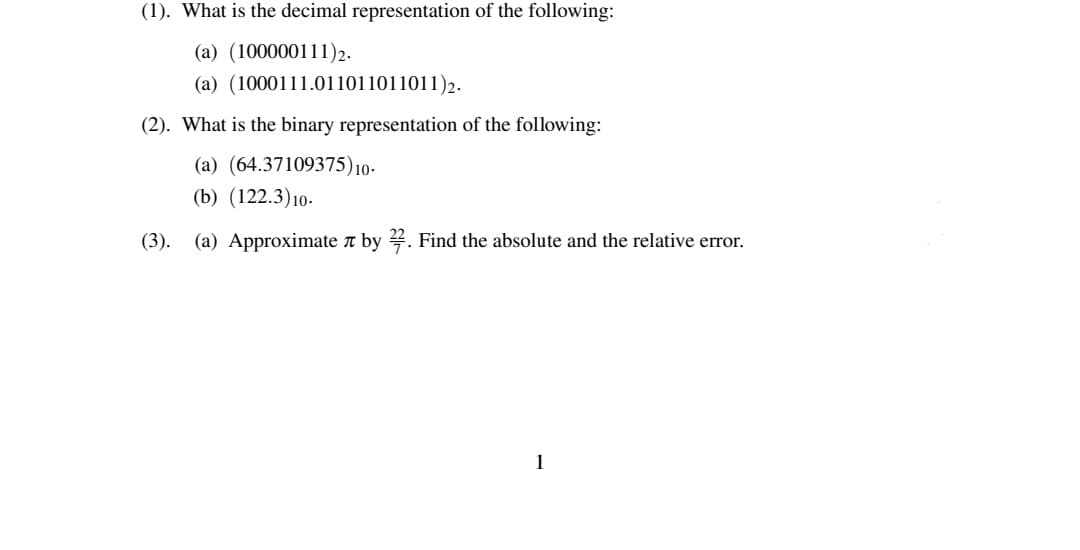
Step by step
Solved in 3 steps

- 8. Add the following two 8-bit binary numbers, producing an 8-bit result. Indicate the status of the carry and overflow bits at the end of the addition by circling the appropriate choices. The space in between is only for readability. 1111 0010 + 1101 0110 ----------- Overflow? Yes or No Carry? Yes or NoNegative signed binary numbers What is the decimal representation of the 2-bit signed binary number 11? What is the decimal representation of the 16-bit signed binary number 1111_1111_1111_1111? How do the signed binary representations differ (ignoring the underscores)? What is the decimal representation of the 8-bit signed binary number 1001_0001? What is the decimal representation of the 16-bit signed binary number 1111_1111_1001_0001? How do the signed binary representations differ (ignoring the underscores)? What is the decimal representation of the 9-bit signed binary number 1_0001_0001? What is the decimal representation of the 16-bit signed binary number 1111_1111_0001_0001?1) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?
- 1)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?1) 0xBEAD (in hex) can be written in decimal (base 10) as: 2) 23.2578125 (decimal) is expressed in binary (base 2) as: Do no use any spaces within your representation. Use 8 bits to represent the integer part, and an additional 8 bits to represent the fractional parts (i.e., 8 bits before the radix point and after the radix point).Convert IEEE Single-Precision Binary Format Real number 11000100101001000010101000000000 to decimal. Please show all the steps. a) [1] What is the sign? b) [1] What is the biased exponent value? c) [1] What is the unbiased exponent value? d) [2] What is the normalized representation of the number in BINARY? e) [1] What is the unnormalized representation of the number in BINARY? f) [1] What is the decimal value of the whole number part of the number? g) [2] What is the decimal value of the fractional part of the number? h) [1] What is the real number in base 10
- Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.6. Convert the following numbers from unsigned binary notation to decimal notation, and from 6-bit 2's complement notation to decimal notation: i) 110011, ii) 001101, iii) 101101 7. Show how each of the following floating point values would be stored using IEEE-754 single precision (be sure to indicate the sign bit, the exponent, and the significand fields): a. 12.5 b. −1.5 c. 0.75 d. 26.625 8. The following is a representation of a decimal floating value using IEEE-754 single precision. Find out the value in decimal. 0 10000011 10101000000...0Assume we have a byte system for the fixed number representation (the whole number is presented with 8-bits (one byte) and the fractional part is presented with 2-bits), find the 2's complement of 0110 0010.01 The answer should be formatted as a fractional 2's complement binary number representation with the exact format of the answer that is required of this particular calculation. I've gotten an answer of 1001 1110.00 but it says its wrong please help
- Calculate (4.41762275 *10-3 + 6.34225625 *10-3) * 1.05225 * 102 by hand, assuming each of the values are stored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.8) Obtain the 1’s and 2’s complements of the following binary numbers correctly:(a) 10010000(b) 00000000(c) 11011010(d) 10101010(e) 10100101(f) 11111111 9) Convert decimal +49 and +29 to binary, using the signed-2’s-complementrepresentation and enough digits to accommodate the numbers. Thenperform the binary equivalent of (+29) + (-49), (-29) + (+49), and (-29) + (-49). Convert the answers back to decimal and verify that they are correct.Calculate (3.41796875 *10-3 * 6.34765625 *10-3) by hand, assuming each of the values arestored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 roundbit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer inthe 16-bit floating point format.

