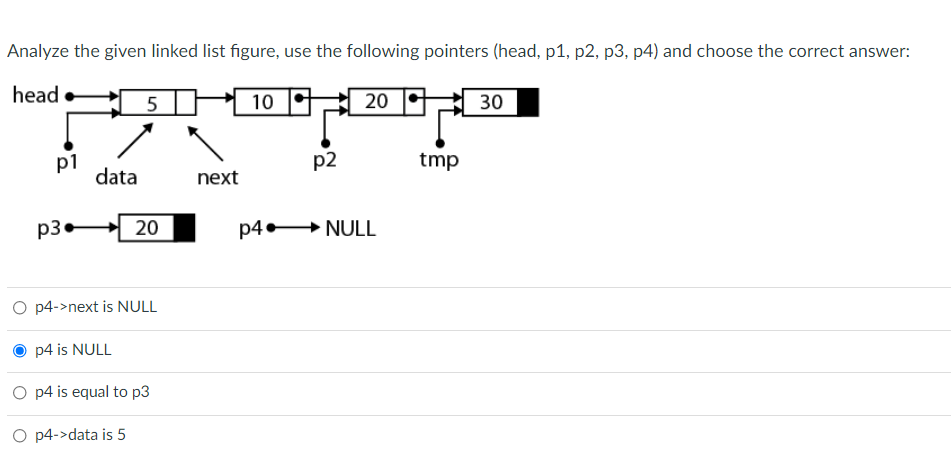
head TP 10 20 - 30 p1 data p2 tmp next p3 20 p4 + NULL
Q: Describe Relationship between "SendBase" and "LastByteRcvd" variables.
A: To be determine: Describe Relationship between "SendBase" and "LastByteRcvd" variables.
Q: Angular sends and receives session data to and from the server without requiring any modifications.…
A: Angular sends data through the server without any changes and also it can recieves. It is true. So…
Q: TUTOR (Tutoro. CertDate, Status) Tuturto CertDate Status 200 1/05/2008 1/0s/2008 1/0/2008 S/22/2008…
A: Explanation: In SQL, to join two or more tables, we make use of the primary key and the where…
Q: Write FIVE SETS of MYSQL COMMANDS, based on the following subtopics: 1. MAX 2. AVERAGE 3. COUNT 4.…
A: Given MySQL subtopics are MAX, Average, Count, Comparison operators and Special operators (In). MAX…
Q: Show and upload your SOLUTION. Include the starting address, ending address and limit. Code a…
A: Solution:-
Q: 5. Web services serve their data to a browser. True False 6. When MVC is applied to a Web…
A: 5. Web services use HTTP(Hypertext Transfer Protocol) for sending requests and responses over web.…
Q: Given the following link list, please do the following: head 2000 2800 1500 3600 2000- 17 2800 92…
A: As per company guidelines we are supposed to answer only 1 question . Kindly re-post other questions…
Q: What is a SELECT statement in MySQL and give write examp
A: MySQL It is an open-source relational database control system (RDBMS). It is an aggregate of…
Q: ASK with more than two input levels allow a data transmission faster than an ASK with only two input…
A: Below is the answer:
Q: Mr. R. k. is new to salesforce and he want to fetch a record type id without using a SOQL query. Can…
A: As per the given problem we need to fetch a record type id of an object. To fetch record type Id…
Q: INSERT command is part of the Data Definition Language (DDL) Select one: True False
A: Insert – is used to insert data into a table. It is a Data Manipulation Command(DML)
Q: book.xml XML block book 29.99 Xml 1.1 Bible 39.95 principles of comiler…
A: a) Find books having lang attribute and also their price is below 30? Answer : ENG is the only book…
Q: Source DI MS Factor ? ? 115.1387 3.698 ? Block ? ? 72.1750 Error ? ? ? Total
A:
Q: Which of the following datasets has tidy data? Dataset 1 # A tibble: 4 x 3 country '1992 '1997 1…
A: ANSWER Dataset 2 Data set 2 has a tiny set of data compare to other data sets Dataset 2 has less…
Q: Mr.Jo Jo found that "tweetid, created-at and username" columns are sensitive thus decided to mask…
A: Answer: Python Source Code: import pandas as pddf = pd.DataFrame({"tweet_id":[3017, 412, 1702, 3463,…
Q: : statsmodels.formula.api as sm matplotlib.pyplot as plt ap.random.normal (0, 1, 100) (1 + 3 1 + X2…
A: Correct statements b. Either X1 or X2 should be excluded, as the second regressor does not add any…
Q: Which of the following is the first step in the algorithm used to decode data encrypted using AES?…
A: Here in this question we have asked that which of the following is the first step in the algorithm…
Q: You may download and use the CIFAR-10 dataset in keras using the following code: from keras.datasets…
A: The answer is
Q: Update any table is a Select one: a. Role O b. DDL c. Dectionary d. System privileges e. TCL O f.…
A: The UPDATE ANY TABLE is a system privilege that allows us to update values in table.
Q: Client Server SYN 1 seqNo: rwnd =| 2 Time 1: The client sends a SYN segment with seqNo = 300.…
A: The Answer is
Q: using jupyter notebook) You are going to compute the summary statistics for the data set Iris,…
A: In questions with many questions, we must do 3.
Q: Hw@gondor:--ssh -p 9003 gondor.tek.bth.se flwanallifrey:~/unix/lab2/sql_lib_demo$ cd…
A: The caution characteristic is very useful for debugging wayward makefiles. Because the caution…
Q: 2. (1 pas) TRUE. resulting schedules are always serial. 3. TRUE. FALSE. The 2PL protocol guarantees…
A:
Q: org 100h .data mov ah, 9 INT 21H inMsg db "Enter a character ",'$' newline db Odh,0ah,'$' outMsg db…
A: org 100h.data inMsg db "Enter a character ",'$' newline db 0dh,0ah,'$' outMsg db "User enter…
Q: Which of the following is a sorted list? OA. {ALISHA ALISSON ALISON ALIYA} OB. (154 125 652 700} OC.…
A: Sorted list: The sorted list contains values which are sorted either in ascending order or…
Q: In Flow Table ______________ is not used when processing packets but used by the controller to…
A: 1) In OpenFlow for packet-based network, each switch contains a flow-table. 2) Each flow-table entry…
Q: SELECT MAX(duration_weeks) FROM streams UNION SELECT MIN(duration_weeks) FROM streams;
A: Given query is SELECT MAX(duration_weeks) FROM streams UNION SELECT MIN(duration_weeks) FROM…
Q: prt arcpy = r"d:\temp\mygdb.gdb\airports" # assume the path is valid n arcpy.di.SearchCursor (fc,…
A: It is defined as a powerful general-purpose programming language. It is used in web development,…
Q: Using the book.xml file find the answer to the following queries ****(write XPath expressions)****…
A: <?xml version="1.0" encoding="UTF-8"?> <bookstore> <book category="COOKING">…
Q: 3DES block cipher uses a total key size (
A: the 3DES block cipher key consists of a concatenation of three DES keys, each of which has the size…
Q: In a wide or long formatted dataset, which of the following would be represented by the rows?…
A: Introduction Given , In a wide or long formatted dataset, which of the following would be…
Q: Question 15 Consider the following linked list: 2000 17 2000 info link 2800 92 1500 info link 1500…
A: Given: We are given a linked list that contains nodes. Each node has two parts first is the value…
Q: Based on the code below choose the incorrect option: O a. code is part of the DTD code O b. BR…
A: Given code is <!ELEMENT BR EMPTY> Incorrect option is Option d- Br is an attribute
Q: The permission associated with a program called Program1 and a dataset called Data1 are as follows:…
A: The permission associated with a program called Program1 and a dataset calledData1 are as…
Q: The following step is used to remove first node from the AVAIL list. NEW: =AVAIL AND AVAIL:…
A: A Connected List is a set of items called nodes that are stored in memory at random.A node has two…
Q: A single node can be used as both master and proxy node. Select one: True False
A: A master node is used for managing services and allocating resources, scheduling and monitoring. A…
Q: Searches with and without iteration, authoritative and root servers, and DNS record lookups are all…
A: Domain Name System The DNS, or domain name system, is the Internet's telephone directory. People…
Q: In DNS recursive query the Local DNS server first checks the DNS root then The Local DNS server…
A: In DNS recursive query the Local DNS server first checks the DNS root then the local DNS server…
Q: 18. The following table shows the fields of DNS resource records. Complete the table. Type Name…
A: The full table is giving below.
Q: stio implements the Envoy proxy as a sidecar. Select one: True False
A: we can currently mechanically inject Envoy sidecar proxies into the pods of a namespace that has the…
Q: Identify the TCL statement that will save all the changes permanently after executing the below SQL…
A: The sql statement that will save all the changes permanently after executing the statement is:
Q: Select the DDL command from the following. O a. delete O b. create O c. select O d. update
A: Dear Student, In SQL DDL is data definition language so all those commands which define a database…
Q: What is the decimal value of the smallest positive normal number? Give the answer first in decimal…
A: Smallest positive number will be 1 as decimal, and in IEEE, it will be 1.0 * 2^0, hence sign 0,…
Q: Q2: create a script file to generate NXN matrix in form like: [1 2 1 2 1 21 2 1 2 1 2 1 1 2 1 2 1 2…
A: N = input("Enter the value of N: "); mat =zeros(N,N); for row = 1 : N for col = 1:N…
Q: Datamxlsread (Rehabil year.xlsx'); Data (1)= Data (3) : for jal:length (Data) a end min_no - Data…
A: Given Code:
Q: Opsequences alert x1x op5 x2:X op1 op2 x3:X op3 y1:Y op4 op2 op3 Z1:Z new remove ZA
A: Answer: Belwo are the right options. a. The op2 message of x2 invoked by the object x3 is not the…
Step by step
Solved in 2 steps

- Use the standard linked list below to answer True/False statements 11-12: 11) If we called “delete(10)”, Node 7’s “next” pointer will point to Node 8 12) If we called “search(20)”, the “head” pointer will be at Node 4 after the search function endsConsider the following linked list: Give the correct sequence to steps to the list be like below: I Move current pointer to the position to delete i.e. node D, II Move the previous pointer behind the current pointer i.e. node C III Make the node C to point to next of node D. IV Delete the node D Select one: A.II, I, IV, III B.I, II, III, IV C.IV, I, II, III D.IV, III, II, IUse the standard linked list below to answer True/False statements 9-12: 9) The “head” pointer of this list is pointing to Node 4 10) If we called “insert(5)”, the new node’s “next” pointer will point to Node 8 11) If we called “delete(10)”, Node 7’s “next” pointer will point to Node 8 12) If we called “search(20)”, the “head” pointer will be at Node 4 after the search function ends
- Modify the given code to move the string from leftmost side to the rightmost side of the screen (no trails). Given Code: .model small.stack.data strg db 'Lemon$' row db 12 col db 0.codemain proc mov ax,@data mov ds,ax mov ah,6 mov al,0 mov bh,7 mov ch,0 mov cl,0 mov dh,24 mov dl,79 mov cx,40again:push cx mov ah,2 mov bh,0 mov dh,row ;row mov dl,col ;col int 10h mov ah,9 mov dx,offset strg int 21h inc col mov cx,10 push cx mov cx,0ffffhx: loop x pop cx loop y pop cx loop again mov ah,4ch int 21hmain endpend mainPlease implement this function: void swap(int pos1, int pos2) {}. There's an answer from the previous teacher but he added '' node** hRef " in the function (see below) please correct without the href. For LinkedList, to maintain integrity of data in the structure, you are not to swap directly the element, nor remove a node. Instead, you are to only change the nodes' next pointers. PLEASE CORRECT THIS ONE void swap(node** hRef, int pos1, int pos2) { if (pos1 == pos2) return; node *prevNode1 = NULL; node* currNode1 = *hRef; while (currNode1 && currNode1->index != pos1) { prevNode1 = currNode1; currNode1 = currNode1->next; } node *prevNode2 = NULL; node *currNode2 = *hRef; while (currNode2 && currNode2->index != pos2) { prevNode2 = currNode2; currNode2 = currNode2->next; } if (currNode1 == NULL || currNode2 == NULL) return; if (prevNode1 != NULL) prevNode1->next =…Select true or false for the statements below. Explain your answers if you like to receive partial credit 10) Which of the following is true about the linked list functions where the linked list onlycontains a head pointer?a. If the linked list is ordered, you can use binary search and improve theperformance to O(log n)b. The worst case performance of the delete function is in the same Big-Ocategory as the worst case performance of the delete function with anunordered arrayc. If the node you are deleting is at the end of the list, the performance is O(1)
- how to answer the following question screen shot show figure 6.3 The figure 6.3 represents storage of a linked list in an array. The stored list is: A. B – A – D – C. B. 1 – 6 – 4 – -1. C. A – B – C – D. D. A1 – B6 – C4 – D(-1). The order in which we add information to a list has no effect on when we can retrieve it. True or FalseQuestion 11 If N represents the number of elements in the collection, then the contains method of the ArrayCollection class is O(1). True False Question 12 With the text's array-based list implementation, the set of stored elements is scattered about the array. True False Question 13 The add method of the LinkedCollection class places the new element at the beginning of the underlying linked list. True False Question 14 If N represents the number of elements in the list, then the index-based add method of the ABList class is O(N). True False Question 15 The attributes of a class that are used to determine equality of objects of the class are called the key attributes. True False Question 16 According to the text's specifications, a collection is a list. True False Question 17 O(1) is the order of growth execution time of the add operation when using the ArrayCollection class, assuming a collection size of N. True False Question 18 When an object of class LBList…q15) Which of the following structure is used to implement dynamic stack? a. Structures b. Linked List c. Unions d. Arrays
- Consider the following linked list: Give the correct sequence to steps to the list be like below: I Move pointer to position to insert i.e. node K II Point the new node to next of node K III Point the node K to the new node. IV Create new node S Select one: A.IV, I, II, III B.IV, I, III, II C.IV, III, II, I D.I, II, III, IVConsider the following piece of pseudocode:new DynamicArray dd[1] ← 1d[2] ← 2d[3] ← 3d[2] ← Ød[1] ← ØWhich of the following describes a linked list implementation of this pseudocode?a. Create a new empty linked list, insert a node (with value 1) with next pointer to null, insert a node (with value 2) at the end of list, insert a node (with value 3) at the end of list, remove end node.b. reate a new empty linked list, insert a node (with value 1) with next pointer to null, insert a node (with value 2) at the end of list, insert a node (with value 3) at the end of list, remove middle node, remove first node.c. Create a new empty linked list, insert a node (with value 1) with next pointer to null, insert a node (with value 2) at the beginning of list, insert a node (with value 3) at the end of list, remove end node.Which of the following statements regarding linked lists and arrays is correct? Group of answer choices: a. A dynamically resizable array makes insertions at the beginning of an array very efficient. b. Using a doubly linked list is more efficient than an array when accessing the ith element of a structure. c. A dynamically resizable array is another name for a linked list. d. Any type of list tends to be better than an array when there are a set number of maximum items known beforehand. e. If many deletions at any place in the structure were common, a linked list implementation would likely be preferable to an array



