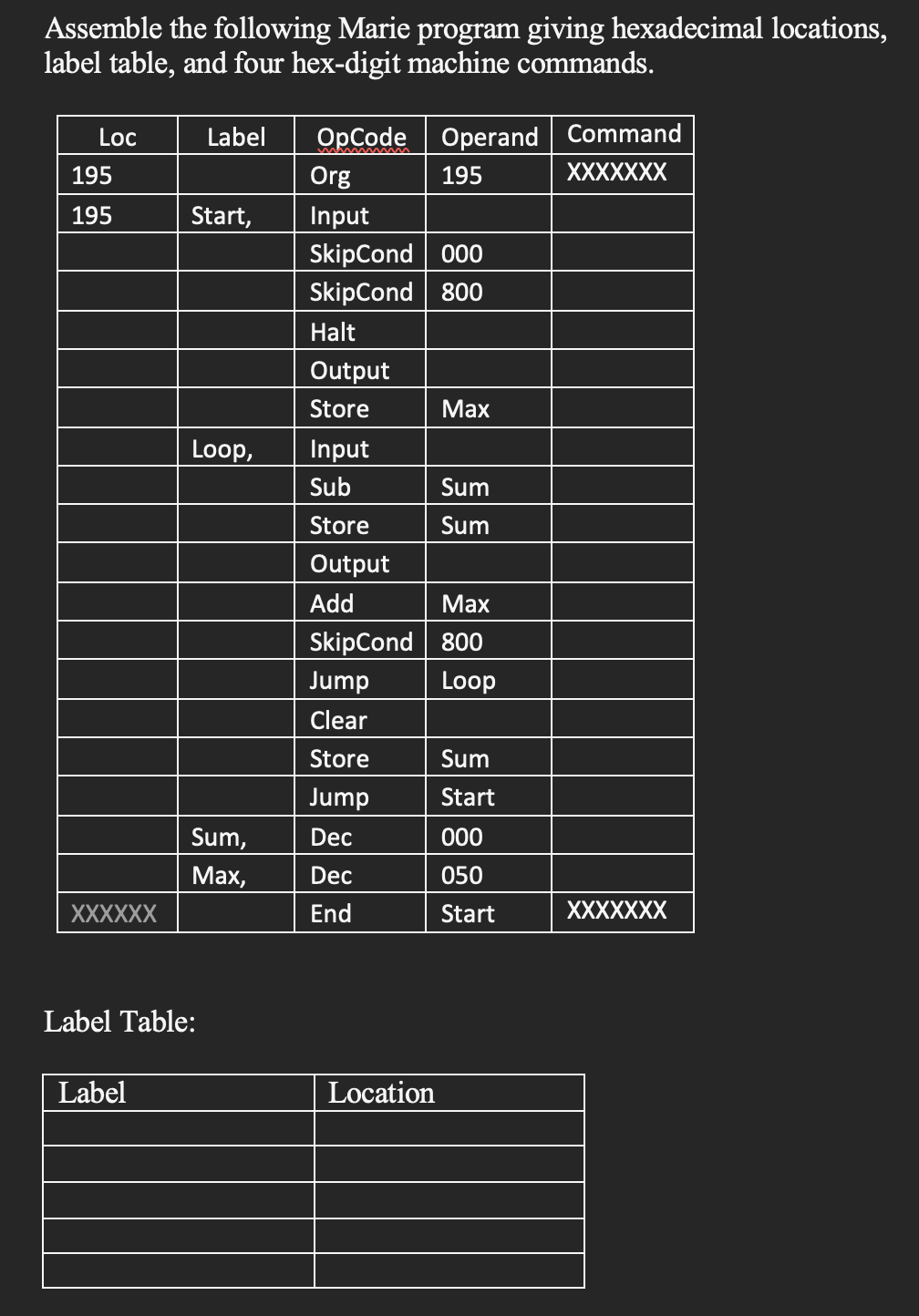
Hello, can you help me with this please? Please make sure that the command column is in four digits hex (for example 0x5000). Thank you
Q: Write a Matlab function that sorts arbitrarily given 9 numbers in the order of largest to smallest…
A: 1. Initialization: Store the nine input numbers in an array: numbers = [a, b, c, d, e, f, g, h,…
Q: What are the key components of a WAN infrastructure, and how do they differ from those of a LAN?
A: Two main players arise in the ever-connected world of modern networking: the Wide Area Network (WAN)…
Q: Describe the waterfall model in system design. What are its phases, and how does it differ from the…
A: The Waterfall Model is a conventional and sequential method for developing software and systems. It…
Q: What is the importance of fault tolerance and redundancy in system design? Provide examples of how…
A: Fault tolerance and redundancy are critical concepts in system design, particularly in…
Q: Define system design and its importance in the development of software and hardware systems.
A: System design is a crucial phase in the development of both software and hardware systems. It is the…
Q: Explain the concept of cognitive radio and its potential applications in wireless networks.
A: Cognitive radio or CR is a form of wireless communication in which a transceiver can intelligently…
Q: Describe the role of routers in WAN connectivity and how they facilitate data transmission across…
A: Routers play a role in connecting geographical areas through Wide Area Networks (WANs).They ensure…
Q: 1. Why we need Web Engineering?
A: In the ever-evolving digital landscape, the internet has become an integral part of our daily lives,…
Q: Write a Matlab script that collects the components of a vector of 10 numbers in two separate vectors…
A: Input: A vector, vv, of 10 numbers.Output: Two vectors: pp (positive numbers, including zero) and nn…
Q: Explain the principles of object-oriented system design and provide examples of object-oriented…
A: In order to create systems and applications, object-oriented system design (OSD) employs the…
Q: Discuss the challenges and solutions in securing wireless communication networks.
A: Securing wireless communication networks can be challenging due to:Unauthorized Access: Wireless…
Q: Describe the role of protocols like TCP/IP in enabling communication across a WAN. How does it…
A: TCP/IP, also known as Transmission Control Protocol/Internet Protocol is a collection of networking…
Q: How does system design differ between hardware and software systems?
A: Designing systems, whether hardware or software involves a phase that requires approaches and…
Q: Discuss the role of security and privacy considerations in the design of systems and applications.
A: Security and privacy are considerations when designing computer science engineering systems and…
Q: What are the primary challenges or limitations associated with wireless transmission technology?
A: The advent of transmission technology has completely transformed the way communicate and access…
Q: Describe the significance of IT security measures, including firewalls and antivirus software, in…
A: IT security measures are crucial for protecting computer systems from threats and vulnerabilities.…
Q: In the context of embedded system design, discuss the trade-offs between hardware and software…
A: In this question we have to understand the trade-offs between hardware and software components in…
Q: Explore the concept of system scalability in design. Provide examples of systems that require…
A: A system, application, or infrastructure is said to be scalable if it can handle an increase in…
Q: What are the key advantages of using wireless transmission technology over wired communication…
A: Our everyday lives depend on communication in a connected world. Transmission mode is crucial to…
Q: Discuss the concept of domain-driven design (DDD) and how it can be used to model complex systems…
A: Domain-driven design (DDD) is an approach to software development that aims to align the development…
Q: Using your knowledge of knock-out options and their pricing via Monte Carlo simulation, demonstrate…
A: Set the option parameters, including the initial stock price, strike price, barrier price, time to…
Q: What is the purpose of database normalization in the field of relational databases, and why is it…
A: Database normalization is a fundamental concept in relational databases, essential for data…
Q: Describe the fundamental principles of radio wave propagation in wireless communication
A: Radio wave propagation in communication is a concept that plays a crucial role in the operation of…
Q: Explain the concept of system architecture and its role in system design.
A: In the field of computer science, engineering system architecture is an aspect of system design..It…
Q: Explain the concept of denormalization in databases. When and why might denormalization be used, and…
A: In order to improve read efficiency and make complicated queries simpler, denormalization is a…
Q: Discuss the integration of CRM with other enterprise systems such as ERP (Enterprise Resource…
A: Enterprise Resource Planning, or ERP, is a category of software used by enterprises to coordinate…
Q: What is an operating system and its types.
A: The basis for controlling a computer's hardware and software resources is its operating system (OS),…
Q: Explore the concept of Information Technology governance and its role in ensuring compliance, risk…
A: Information Technology (IT) governance plays a pivotal role in the contemporary landscape of…
Q: Discuss the trade-offs and considerations involved in denormalization, and explain when it might be…
A: Denormalization is a technique used in database design where redundancy is intentionally introduced…
Q: Discuss the concept of system design patterns and provide examples of commonly used patterns in…
A: Normalized solutions are much of the time expected for repeating issues in the field of software…
Q: Discuss the concept of Multiple Input Multiple Output (MIMO) technology in wireless communication.…
A: Multiple Input, Multiple Output (MIMO) is a critical technology in wireless communication systems…
Q: How can a CRM system be customized to cater to the unique needs and workflows of different…
A: CRM systems are tools that are widely used in industries like healthcare and finance to effectively…
Q: Discuss the challenges and ethical considerations associated with collecting and using customer data…
A: Software development is the process of designing, creating, and maintaining computer programs or…
Q: What are the security challenges associated with wireless transmission technology, and how can they…
A: Wireless transmission technology has become ubiquitous in our interconnected world, enabling…
Q: Describe the various wireless communication protocols commonly used in IoT (Internet of Things)…
A: Communication protocols enable data exchange and connectivity in the Internet of Things (IoT)…
Q: What are the potential security vulnerabilities in wireless transmission technology, and how can…
A: In this question we have to understand the potential security vulnerabilities in wireless…
Q: How does system scalability impact the design of large-scale systems? Provide techniques for…
A: Hello studentSystem scalability is crucial for large-scale applications and services, ensuring they…
Q: How does system design for real-time and embedded systems differ from general-purpose computing…
A: System design plays a role in developing both software and hardware systems.There are differences in…
Q: Investigate the challenges and solutions related to spectrum allocation and management in wireless…
A: Hello studentIn the world of wireless communication systems, the allocation and management of radio…
Q: An ice cream manufacturer supplies different types of ice cream to the local restaurant in different…
A: In this question we have to write a python code for the given problem statement Let's code and hope…
Q: Briefly explain the hierarchy of network protocols used by web browsers/web servers, starting from…
A: The concept of network protocols revolves around establishing the rules and conventions that…
Q: What are the key considerations when designing a real-time embedded system, and how does it differ…
A: Hello studentDesigning systems, especially large-scale ones, demands a deep understanding of various…
Q: Explain the importance of Introduction to Packet Tracer, the installation process, and its practical…
A: Packet Tracer, developed by Cisco Systems is a network simulation tool in the fields of networking…
Q: Why do computers use the binary system instead of other systems?
A: The binary system, also known as the base-2 system, is a positional numeral system that uses only…
Q: How does the choice of programming language impact system design? Provide examples
A: The choice of a programming language plays an important role in system design.. It can affect…
Q: Explain the challenges associated with achieving low-latency communication in 5G networks. How are…
A: Given,Explain the challenges associated with achieving low-latency communication in 5G networks. How…
Q: In the context of cybersecurity, how do you see the evolving threat landscape impacting the…
A: The evolving threat landscape has become a critical factor shaping how organizations safeguard their…
Q: The program should accept decimal entries like 52.31 and 15.5 for the cost of the meal. The program…
A: Calculating the whole cost of a dinner, including the tip, has become a commonplace process in a…
Q: How does IoT (Internet of Things) influence the development of wireless transmission technology?…
A: The Internet of Things (IoT) has had a sizeable effect on the development of the wireless…
Q: How does cloud computing influence system design, and what are the key considerations for…
A: 1) Cloud computing refers to the delivery of various computing services, including servers, storage,…
Hello, can you help me with this please? Please make sure that the command column is in four digits hex (for example 0x5000). Thank you
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- onvert the following C code snippet into the corresponding x86 assembly instructions. 1) if(x error_outlineHomework solutions you need when you need them. Subscribe now.arrow_forward Question Asked Aug 11, 2020 1 views Convert the following C code snippet into the corresponding x86 assembly instructions. 1) int n = 5; for(int i = 0; i <= 10; i++) { cout<<n<<” x ”<<i<<” = ”<<n*i<<endl; }Assemble the following Marie program giving hexadecimal locations, label table, and machine commands. Loc Label OpCode Operand Command 100 Org 100 100 Start, Input SkipCond 000 SkipCond 800 Halt Output Store Max Loop, Input Add Sum Store Sum Output Sub Max SkipCond 800 Jump Loop Clear Store Sum Jump Start Sum, Dec 000 Max, Dec 050 End Start Label Table: Location Label CommentsWrite a MARIE program simulation the following Python code. The MARIE program must generate the output similar to Python's. The program must have a loop. Python code: num = [1,2,3,4,5,6]for i in num: print (i) This is what I have so far but it only prints from 1 to infinity: ORG 100START, LOAD NUM STORE COUNT OUTPUT LOAD NUM ADD ONE STORE NUM LOAD NUM SUBT COUNT SKIPCOND 400 // Salta si COUNT < NUM JUMP START HALT ONE, DEC 1NUM, DEC 1COUNT, DEC 1 END START
- Provide neat answers. Show all necessary steps. Translate the following code snippet written in C programming language into an instructionsequence written in MIPS Assembly language. You may assume that the values of the variables x,y, a, b, and c are in the general-purpose registers $s0, $s1, $s2, $s3, and $s4. if(x == y) {c = a - b;} else {c = b - a;}x = x + c;y--;1. T/F - if (B)=006000 (PC)=003600 (X)=000090, for the machine instruction 0x032026, the target address is 003000.2. T/F – PC register stores the return address for subroutine jump.3. T/F – S register contains a variety of information such as condition code.4. T/F – INPUT WORD 1034 – This means Operating system should reserve 1034 bytes in memory5. T/F - In a two pass assembler, adding literals to literal table and address resolution of local symbol are done using first pass and second pass respectively.Assume that the state of the 8088’s registers and memory just prior to the executionof each instruction in problem 15 is as follows: * in photos*What result is produced in the destination operand by executing instructions (a)through (k)? *only b,c,e,g* b) ADC SI, AX(c) INC BYTE PTR [0100H] (e) SBB DL, [0200H] (g) NEG BYTE PTR [DI]+0010H
- What will be the value of BL (in Hexadecimal) after the execution of the following instructions: MOV CL,52 MOV BL, 19 CMP BL, CL MOV CL,2 RCR BL, CLAssume that the state of the 8088’s registers and memory just prior to the executionof each instruction in problem 15 is as follows: * in photos*What result is produced in the destination operand by executing instructions (a)through (k)? *only h through k* (h) MUL DX(i) IMUL BYTE PTR [BX+SI](j) DIV BYTE PTR [SI]+0030H(k) IDIV BYTE PTR [BX][SI]+0030HUsing the table, Create MARIE assembly language code to compute in the following two inputs and find following logarithmic result. Where A is a base and B is an exponent of A. C is the output of the C= Log AB. Input A Input B Output C 2 16 4 3 9 2
- q) Evaluate the performance of a 32-bit and a 64-bit computer when the same size of resources such as memory and hard disk is used on them. After attending a system programming class, members were tasked to perform the following activities b) Write an assembly language code to subtract a variable stored at SS from that stored at AA and store the answer at AN. You are to use only 2’s complement addition.Consider the following instruction:Instruction: Add Rd, Rs, RtInterperation: Reg[Rd] = Reg[Rs] + Reg[Rt] RegWrite MemRead ALUMux MemWrite ALUOp RegMux Branch a, What are the values of control signals generated by the control in Figure 4.2 for the above instruction? b, Which resources (blocks) perform a useful function for this instruction? c, Which resources (blocks) produce outputs, but their outputs are not used for this instruction? d, which resources (blocks) produce no output for this instruction?11. The content of the accumulator after the execution of the following 8085 assembly language program, is:MVI A, 42HMVI B, 05HUGC: ADD BDCR BJNZ UGCADI 25HHLT a. 82 H b. 78 H c. 76 H d. 47 H

