Hello how to fix this issue? please help!
Q: 1. What do you do if your friend(s) getting cyberbullied? 2. Do you think online bullying is worse…
A: Here's so many ways you what you do when your friend is cyberbullied -> Do not send or share any…
Q: Do you have any recommendations for securing the company's network from cyberattacks?
A: Do you have any recommendations for securing the company's network from cyberattacks in below step
Q: mov ax, FFØ0H inc ah
A: 1. mov ax, FF00h :: This instruction will move FF00h to ax register. ax register is a addition of…
Q: MCQ 8: Which of the following AWS service would help you determine who took action? (A) AWS EC2…
A: Given mcq is based on Amazon web services.
Q: What is the minimum Hamming distance of the code?
A: Hi there,I am adding answer below with calculation please go through it thank you To compute…
Q: Lectures in your college use WhatsApp for sharing exam question papers with each other. Briefly…
A: C-I-A-A was formally known as Confidentiality – Integrity - Availability now “Accountability” is…
Q: ology with DRaaS: Disaster Recovery as a Service. How might Razor Technology and DRaaS (Disaster…
A: Disaster recovery is the process of quickly restoring critical business services when they are most…
Q: A staff person sends a help desk ticket stating they received an "Error 404" on the department's…
A: Here is the explanation to all the options:
Q: What ethical guidelines would you recommend to Facebook to stop data breaches?
A: Introduction Ethical issues:- When a moral conflict emerges in the workplace, ethical questions must…
Q: You've been warned about a ransomware assault known as Ryuk. Assume that each infected device will…
A: Introduction: Ryuk is a type of ransomware employed in targeted attacks when threat actors encrypt…
Q: We'd want to get your thoughts on how Facebook can prevent data breaches.
A: Ethical concerns must be resolved when a moral conflict occurs at work. In other words, it is a…
Q: When you initially started searching for answers online, what did you hope to discover? Exists a…
A: Start: The Internet is a technology that allows various computer networks all over the world to…
Q: "You should go and kill yourself because you don't mean anything i When 18-year-old John William…
A: i) Three causes that involve computer crimes: Self-loathing: A bully and a victim attitude have a…
Q: What can you do to ensure that this issue does not recur in the future?
A: The step-by-step procedure for avoiding stalemate is outlined inWhen two or more processes wait for…
Q: How essential do you believe it is for FIMC and other organizations providing roadside assistance…
A: EXPLANATION AND ANSWER: Importance for FIMC and other roadside assistance providers: The following…
Q: 6. There are a number of consequences if a security breach occurs in an organization. Which of the…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: You are the new IT manager for a small company. There are 10 PC's and all of them use Microsoft…
A: What are the different types of software licenses? There are five types of common software license…
Q: b) Discuss the “trinity of the computer system” and evaluate the technical functions of each of the…
A: As there are 3 questions, I am compelled to do only 1 question that is the first question due to…
Q: Provide solution thanks 2
A: Given :-Use the definition of big Theta, to find an f(n) that satisfies the expression: nlogn + 2n2…
Q: n effective backup option? Do you agree or disagree? How can th
A: Introduction: RAID technology enhances drive capabilities and unifies individual discs in a group…
Q: Make five recommendations for increasing email privacy in an organization after reading this chapter…
A: A data leakage incident often referred to as an information leakage incident is the unlawful…
Q: The entire world band's terms of service may be found at www. Wholeworldband. Com/about. Summarize…
A: Introduction: Whole World Band is a massive platform that enables users to cooperate with others to…
Q: (Choose ALL) Which of the following are recommendations for improving users' awareness and attention…
A: Choosen recommendation is one of the most widely used for improving user's awareness and attention…
Q: Can i please get help with this question: This is all the information needed for the question...I…
A: The primary significant network protection pattern of 2021 stems from 2020. While WFH is certifiably…
Q: Which of the following statements about cybersecurity are true? (select all that are true and omit…
A: Stating true and false statements with reasons.
Q: Leela is new to salesforce and don't know how to changes a user email address and profile. So can…
A: As per the given problem statement we are assigned a task to change the user email and the profile…
Q: Based on your reading of the chapter and what you now know about the issues, list at least three…
A: As we know, Charley and Iris met for the lunch and Charley recommended to the Iris. Based on my…
Q: I need help with this problem for my Strategic Management class. Thank you You have received word…
A: Given: You have received word of the Ryuk threat, a ransomeware attack. Assume $100 per infected…
Q: Discuss backups and analyze at least five (5) backup methods stating their respective benefits and…
A: Discuss backups and analyze at least five backup methods stating their respective benefits and…
Q: Do you have any suggestions for protecting the business's network from cyberattacks?
A: We need to give suggestions for protecting the business's network from cyberattacks.
Q: eed quick.. Tha
A: Here, we have to provide programs for the above question. So, I am providing answers in python…
Q: Question:
A: Hacking alludes to exercises that try to bargain advanced gadgets, for example, PCs, cell phones,…
Q: What are Facebook ethical issues and legal compliance issues of the 2019 data breach?
A: Let us see the answer Introduction Ethical issues:- When a moral conflict emerges in the workplace,…
Q: 300 words on how can Kali help system administrators.
A: Kali Linux is a working framework very much like some other working framework like Windows yet the…
Q: 04) Write a Thank You letter to the hiring manager of Huawei company, who helped you to find a job…
A: A letter shall represent all the details corresponding to the job requirements.
Q: 6. There are a number of consequences if a security breach occurs in an organization. Which of the…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: Which problems were hoped to be remedied by the preliminary investigation conducted through the…
A: A preliminary investigation is a kind of investigation where police first respond to a report when…
Q: 6. There are a number of consequences if a security breach occurs in an organization. Which of the…
A: Ans :- Option - A :- According to the option given above , Application shutdown would not be…
Q: data in one clock cycle,
A: Solution :- A data bus with clock cycles, data word transmitted and frequency is given in the above…
Q: Urgent Please 2. Is credit checks important? Explain your answer by writing an email to the CEO.
A: The answer is given below:-
Q: You'll need to provide accurate, comprehensive, and detailed responses. Every other situation…
A: The headers are utilized to convey between the client and the server. The headings are utilized to…
Q: Write any ten points for internet safety practices Just answer without explanation please
A: Following are the 10 points for safety practices: 1. Keep your confidential data online -->…
Q: The equation F(A.B.C) = B'C + A'B has a 1-hazard at: m1 - m3 m0 - m2 m2 - m3 m1 - m5 none of these
A: Here in this question we have given a boolean function and we have asked this function has 1 hazard…
Q: What is dorks? What is a Google dork? What is it used in? Is it helpful for hacking?
A: A Google dork query, often known as a dork, is a search query or term that makes use of…
Q: Hey, can you answer all the questions from ‘a’to ‘k’? I only see 3 answered here. Thank you
A: Asper the guidelines we need to answer three subparts of the question. In the given solutions we…
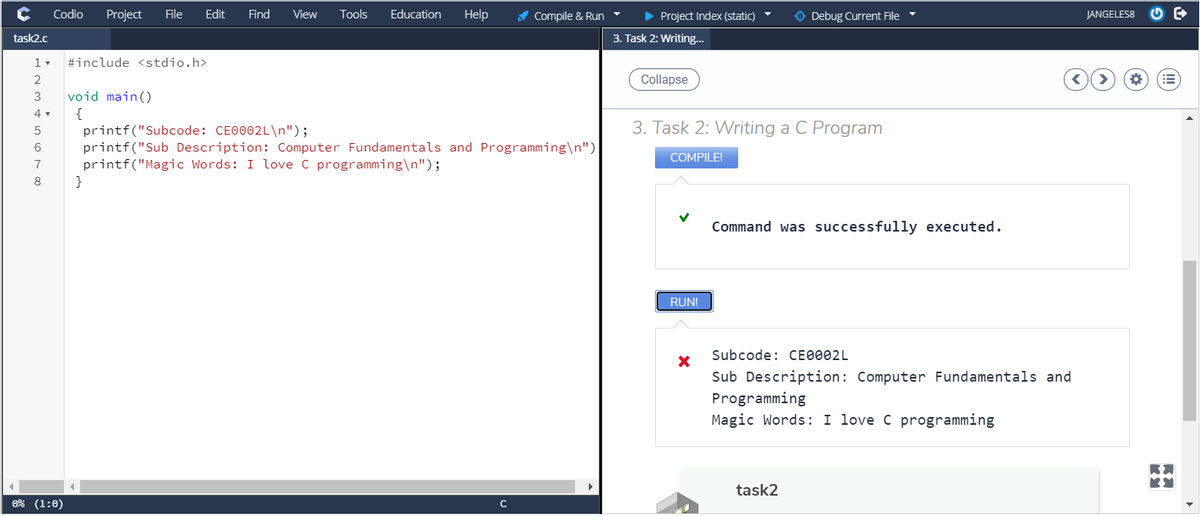
Hello how to fix this issue? please help!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- In C, using this interface: void setSortThreads(int count);void sortThreaded(char** array, unsigned int count); How can you modify the following quicksort program in order to use multithreading, with the goal of performing faster than qsort for large data sets? Use basic parallelization and limit the number of threads to the amount held by the global variable maximumThreads, specified by the user (when they call setSortThreads in the main function). If possible it would be helpful to test the code on a big text file, like maybe the dictionary. I'll include a sample main function at the end that I have been using. You would need your own text file to test it on, though. #include <stdlib.h>#include <string.h>#include <pthread.h>#define SORT_THRESHOLD 40typedef struct _sortParams {char** array;int left;int right;} SortParams;static int maximumThreads; /* maximum # of threads to be used *//* This is an implementation of insert sort, which although it is *//*…In C, using this interface: void setSortThreads(int count);void sortThreaded(char** array, unsigned int count); How can you modify the following quicksort program in order to use multithreading, with the goal of performing faster than qsort for large data sets? Use basic parallelization and limit the number of threads to the amount held by the global variable maximumThreads, specified by the user (when they call setSortThreads in the main function). If possible it would be helpful to test the code on a big text file, like maybe the dictionary. I'll include a sample main function at the end that I have been using. You would need your own text file to test it on. #include <stdlib.h> #include <stdio.h>#include <string.h>#include <pthread.h> #include <time.h>#define SORT_THRESHOLD 40typedef struct _sortParams {char** array;int left;int right;} SortParams;static int maximumThreads; /* maximum # of threads to be used *//* This is an implementation of…Someone tries to fix the stack based buffer overflow problem as follows, is it secure now? why? Are there any other issues within the function's implementation below? int bof(char *str, int size) { char *buffer = (char *) malloc(size); strcpy(buffer, str); return 1; }
- sing good OOP, write a C++ program that will read an input file to manage a list of students waiting to register for a ourse using a linked list. The input file name is WaitList.txt and is located in the current directory of the project. The file layout is as follows: action student name Actions are defined as follows: 1 - add student name to the end of the linked list2 - add student name to the beginning of the linked list3 - delete the student at the beginning of the linked list4 - delete the student at the end of the linked list Actions #1 and #2 require student names. Actions #3 and #4 do not. For example, if the input file contents contained: 1 Sally Sue Student1 Peter Pupil1 Sam Scholar42 Terri Tutor1 Abby Achiever32 Bill Brain The program would display the wait list as follows: The Wait List: 1. Bill Brain2. Sally Sue Student3. Peter Pupil4. Abby Achiever End of List. Then the program will prompt the user if they wish to delete a student by name. If…Can you fix the code of the completion time based on the last execution of each process in the gantt chart and the output of the completion time must be the same as the image below?Code: #include <iostream>#include <queue>#include <string>#include <vector> struct Process { int processId; int burstTime; int priority;}; void print_gantt_chart(const std::vector<std::pair<int, int>>& gantt_chart) { std::cout << "Gantt Chart:" << std::endl; std::cout << "----------------------------------------------------------------------------" << std::endl; std::cout << "| "; for (const auto& process : gantt_chart) { std::cout << "P" << process.first << " | "; } std::cout << std::endl; std::cout << "----------------------------------------------------------------------------" << std::endl; std::cout << "0 "; int currentTime = 0; for (const…You are required to demonstrate the running time difference between a linked listand a binary search tree while searching the data. Read the following instructionsand then implement a C++ program that can address the above requirement.1- choose byself a .csv file containing the data named Dataset.csv The dataset file contains a record of 100000 sales records of astore. By using the text file reading method in C++, read the data of the file in alinked list and a binary search tree. (In a single program) After reading the data validate the data reading by implementing a print() method. Take a sales id as an input from the user and search that ID in the linked listand binary search tree. Display the running time difference of both data structures during the searchoperation.
- Someone tries to fix the stack based buffer overflow problem as follows, is it secure now? why? Are there any other issues within the function's implementation below? Explain your reasoning. int bof(char *str, int size) { char *buffer = (char *) malloc(size); strcpy(buffer, str); return 1; }In python, rite a recursive function, displayFiles, that expects a pathname as an argument. The path name can be either the name of a file or the name of a directory. If the pathname refers to a file, its filepath is displayed, followed by its contents, like so: File name: file_path Lorem ipsum dolor sit amet, consectetur adipiscing elit... Otherwise, if the pathname refers to a directory, the function is applied to each name in the directory, like so: Directory name: directory_path File name: file_path1 Lorem ipsum dolor sit amet... File name: file_path2 Lorem ipsum dolor sit amet... ... Test this function in a new program.The question should be done in C++, please give explanation and running result. 1. For this question, we need to provide more information about where the mismatch of the text file is happening. Write a recursive function called list_mismatched_lines that takes 2 filenames as input arguments and displays to the screen all mismatched lines in those files. This function should use hashing techniques and shall not compare strings to detect mismatch. The signature of this function should be: void list_mismatched_lines(std::string file1, std::string file2); In file1.txt, it contains "My dear C++ class. I hope that you enjoy this assignment. " In file2.txt, it contains "My dear C++ class. I hope that you like this assignment. " Example: Running the following line of code, should print to the screen the mismatched lines only, from both files. list_mismatched_lines(file1, file2); The following output should be seen on the screen: file1.txt: I hope that you enjoy this assignment.file2.txt:…
- C Programming: Write a separate program that takes one command line argument indicating a binary stack file (e.g., stack.bin). Provide an appropriate error message in case of a missing filename or error opening it. The sample output is shown below that it must print out. Show the full code with the sample output being run in the terminal. There must be no errors at all. Sample Output: function: 0x5639db7fc2ca, caller: 0x7f8b8f372290, frame pointer: 0x7ffd23831070stack frame: 0x7ffd23831080-0x7ffd23831070, time: 0.003484 (2158-5642)address range initial final0x7ffd2383107f-0x7ffd2383107c: 00007f8b | 00007f8b0x7ffd2383107b-0x7ffd23831078: 8f372290 | 8f3722900x7ffd23831077-0x7ffd23831074: 00000000 | 000000000x7ffd23831073-0x7ffd23831070: 00000001 | 00000001 function: 0x5639db7fc1d9, caller: 0x5639db7fc2f3, frame pointer: 0x7ffd23831050stack frame: 0x7ffd23831060-0x7ffd23831030, time: 0.002587 (2173-4760)address range initial…2. For the code below, draw a picture of the program stack when the function partition() is called the 2nd time. # extracted from suquant's reply at # https://stackoverflow.com/questions/18262306/quicksort-with-python def partition(array, begin, end): pivot = begin for i in range(begin+1, end+1): if array[i] <= array[begin]: pivot += 1 array[i], array[pivot] = array[pivot], array[i] array[pivot], array[begin] = array[begin], array[pivot] return pivot def quicksort(array, begin, end): if begin >= end: return pivot = partition(array, begin, end) quicksort(array, begin, pivot-1) quicksort(array, pivot+1, end) # added calling code if __name__ == "__main__": mylist = [8, 2, 17, 4, 12] quicksort(mylist, 0, 4)I need help on this home work: Using OOP, write a C++ program that will read an input file to manage a list of students waiting to register for a course using a linked list.The input file name is WaitList.txt and is located in the current directory of the project. Waitlist.txt content: 1 Samuel Stone1 Brett Bacher2 Emily Evans44331 Zachary Zillings2 Carson Cummings1 Penny Plumber31 Tammy Thompson The file layout is as follows:action student nameActions are defined as follows:1 - add student name to the end of the linked list2 - add student name to the beginning of the linked list3 - delete the student at the beginning of the linked list4 - delete the student at the end of the linked listActions #1 and #2 require student names. Actions #3 and #4 do not.For example, if the input file contents contained: 1 Sally Sue Student1 Peter Pupil1 Sam Scholar42 Terri Flowers1 Abby Achiever32 Bill Brain The program would display the wait list as follows: The…











