Help me solve the problem by looking at the program
Q: Unified Communications Systems' traits? Why do companies utilize them?
A: An on-premises or cloud-based unified communication system integrates several forms of modern…
Q: TCP comes in a few distinct flavors, the most common of which are connection-oriented service and…
A: According to the query, we must distinguish between TCP's Full-duplex and Connection-oriented…
Q: The Social Media Language (SML) has the following built-in data types: comment message account…
A: We need to find the answers to questions based on the given language specification.
Q: Task 4: Control the length of generated completion You can also control how long text samples the…
A: model to process and generate more words, which requires more computing resources and time.…
Q: Find the four components of a computer-based instrumentation system.
A: Computer-based measurement systems are used in a wide assortment of utilizations. Computer-based…
Q: What seems to be happening is that ICMPv6 Neighbor Solicitations are being sent out as multicasts…
A: To troubleshoot such problems, network administrators can use various analysis and monitoring tools…
Q: As a consequence its IT infrastructure of using cloud computing services, are all of an…
A: Computing in the cloud: A sort of computing known as "cloud computing" is one that does not rely on…
Q: In the context of evolving technology, what does the term "digital privacy" mean? Can you provide…
A: Introduction: The term "evolution technology" refers to the consistent growth and improvement of…
Q: What distinguishes the computer and information technology environment from a non-computer medium?…
A: Introduction: A particular hardware or software setup. The term "environment" refers to a hardware…
Q: Anywhere it makes sense to do so, object-oriented design need to be used. When the circumstances…
A: Designing with objects in mind: To no one's surprise, this kind of programming relies on objects.…
Q: What sets the input and output at the BIOS level apart from the various forms of input and output…
A: When a computer is powered on, its Processor launches a software called the BIOS (basic input/output…
Q: Make this nonlinear program to a BINARY INTEGER PROGRAM. Max z = x2y + 3x3yw subject to…
A: To convert the given nonlinear program to a binary integer program, binary integer variables: Let a…
Q: Explanation of the metrics and methods used to determine read throughput.
A: Read throughput refers to the rate at which data can be read from a storage system or device, such…
Q: Compared to print statements, what are the benefits and drawbacks of manually walking through code?…
A: What Is the Meaning of Linear Debugging? This is accomplished by a process known as print statement…
Q: Java programming For an array of 20 integers (Declare all necessary variable). Write separate code…
A: Below is the java code for finding and displaying the numbers whose values are between 0 and 50…
Q: It is feasible for a business to defend itself against cybercriminals by closing down its accounts.
A: TYPES OF HACKS AND VIRUSES: The following is a list of the many kinds of cyberattacks and viruses: A…
Q: how l can open my file vb
A: Introduction: Opening a file in VB.NET 6.0 is a relatively simple process that can be done using the…
Q: Provide an explanation of the methods for the creation of databases and applications that make use…
A: Agile methods and development Agile development is described as the process of collecting needs and…
Q: Use java programming. Write a program that helps a person decide whether to buy a hybrid car. Your…
A: pseudocode //Define all the variables and constants neededCostOfNewHybridCar = 0CostOfUsedHybridCar…
Q: Explaining the differences between data buses, address buses, and control buses
A: In computer architecture, a bus is a set of wires that are used to transfer data, memory addresses,…
Q: How should RSA be used to verify a receiver's identity? How can the sender be sure the intended…
A: The answer for the above question is given in the following step for your reference.
Q: What draws so many people to particular websites? What other options are there for low-income…
A: There are several factors that can draw people to particular websites, including: Content: People…
Q: What connection exists between the terms bit, byte, nibble, and word?
A: Bit, byte, nibble, and word are the units of information in computer memory and data storage. 1 Word…
Q: What advantages does the deep web provide to companies that rely on IT systems?
A: Management information systems (MIS) or information management systems (IMS) are corporate tools…
Q: What do you anticipate will be the most common use for 3D printing in the year 2020?
A: As more individuals join the market, 3D printing technology is expanding quickly. The rising number…
Q: Operating systems try to store file blocks on sequential storage media blocks. Why is it essential…
A: It is important for operating systems to store blocks of files on consecutive blocks of storage,…
Q: Name a Linux package management you've tried or are curious about. Why is it superior?
A: Give the name of a Linux package management that is familiar or would want to learn more about. Why…
Q: hods one to convert US dollars to Canadian dollars and the other method to convert the US dollars to…
A: Java program that includes two methods to convert US dollars to Canadian dollars and to Euros, and…
Q: Some people who create content have gone so far as to form their own communities. In general terms,…
A: Google's network: The term "Google's network" is used to describe places where AdWords ads show up.…
Q: Cloud computing is now being included into the information management systems of a significant…
A: Cloud computing: The term "cloud computing" refers to the on-demand access, via the internet, to…
Q: Consider the following database with the below relations: customer-id 192-83-7465 019-28-3746…
A: The answers are given in the below step
Q: as the administrator, are responsible for the operations of StormWind Studios. The process of…
A: We have to explain whihc powershell command is responsible for making the necessary provisioned…
Q: Can you imagine scenarios where default values improve data integrity and situations where they…
A: Default values: Default values are used to prevent problems when no entry exists. The default…
Q: Modifying the model "temperature" How do you think the "temperature" parameter affects the model…
A: The temperature parameter in language model is a scaling factor that controls the level of…
Q: Think about how crucial wireless networks are in today's developing nations. Local area networks…
A: Consider the significance of wireless networks in developing nations today. In specific locations,…
Q: Explain private-key and public-key encryption to pupils. Explain when and why each term may be used…
A: In the case of encryption using a private key, the same key is used to encrypt and decrypt the…
Q: Please share the resource link or website or author reference - how to download or extracted the…
A: To access the crime data provided by the City of Los Angeles Open Data Portal, you can visit the…
Q: Please provide at least three different instances of the tasks that the WinMain (beginning) function…
A: The WinMain (startup) method is responsible for performing the following tasks: Get a handle on the…
Q: Why do voice and video traffic need to be handled differently from other types of network traffic?…
A: As compared to other types of data sent across a network, why do speech and video need to be…
Q: Consider implementing a method of error detection that can smooth out spikes in bad data.
A: Burst error: The Hamming algorithm is inefficient and may even be rendered unusable in some…
Q: Can you name the top two elements that affect cloud computing effectiveness?
A: Introduction: Cloud computing has become an integral part of modern technology infrastructure,…
Q: Why do compilers use parsing techniques that are only efficient for a portion of all grammars?
A: Rationale for using parsing algorithm by the compiler: Parsing is the act of dividing a data string…
Q: Examining the features, similarities, and differences of Excel and Microsoft Access to see whether…
A: differentiating and contrasting a Excel spreadsheet and a Microsoft Access data set Microsoft gives…
Q: In what kinds of situations would it make sense to use the query "select * from student natural full…
A: The query "select * from student natural full outer join takes natural ful" conducts a full outer…
Q: The age of computer programming.
A: Computer programming is necessary for today's society to maintain the functionality of the systems…
Q: Anywhere it makes sense to do so, object-oriented design need to be used. When the circumstances…
A: The choice between object-oriented design and structured design depends on several factors, such as…
Q: What happens if a processor request hits the cache while a write buffer block is being written back…
A: Below is the complete solution with explanation in detail for the given question about what will…
Q: Which statement is NOT CORRECT when mapping the above EER model to a relational model? AIRLINE…
A: Answers:- A graphical representation of entities and their connections to one another is called an…
Q: It is essential to do research on and make comparisons between the ideas of virtual machines and…
A: Below is the complete solution with explanation in detail for the given question about the…
Q: What do you mean by "informally" when talking about the parts of a procedure header that are located…
A: protocol Header: It's what the stored procedure is called. which has to be different from any other…
Step by step
Solved in 3 steps

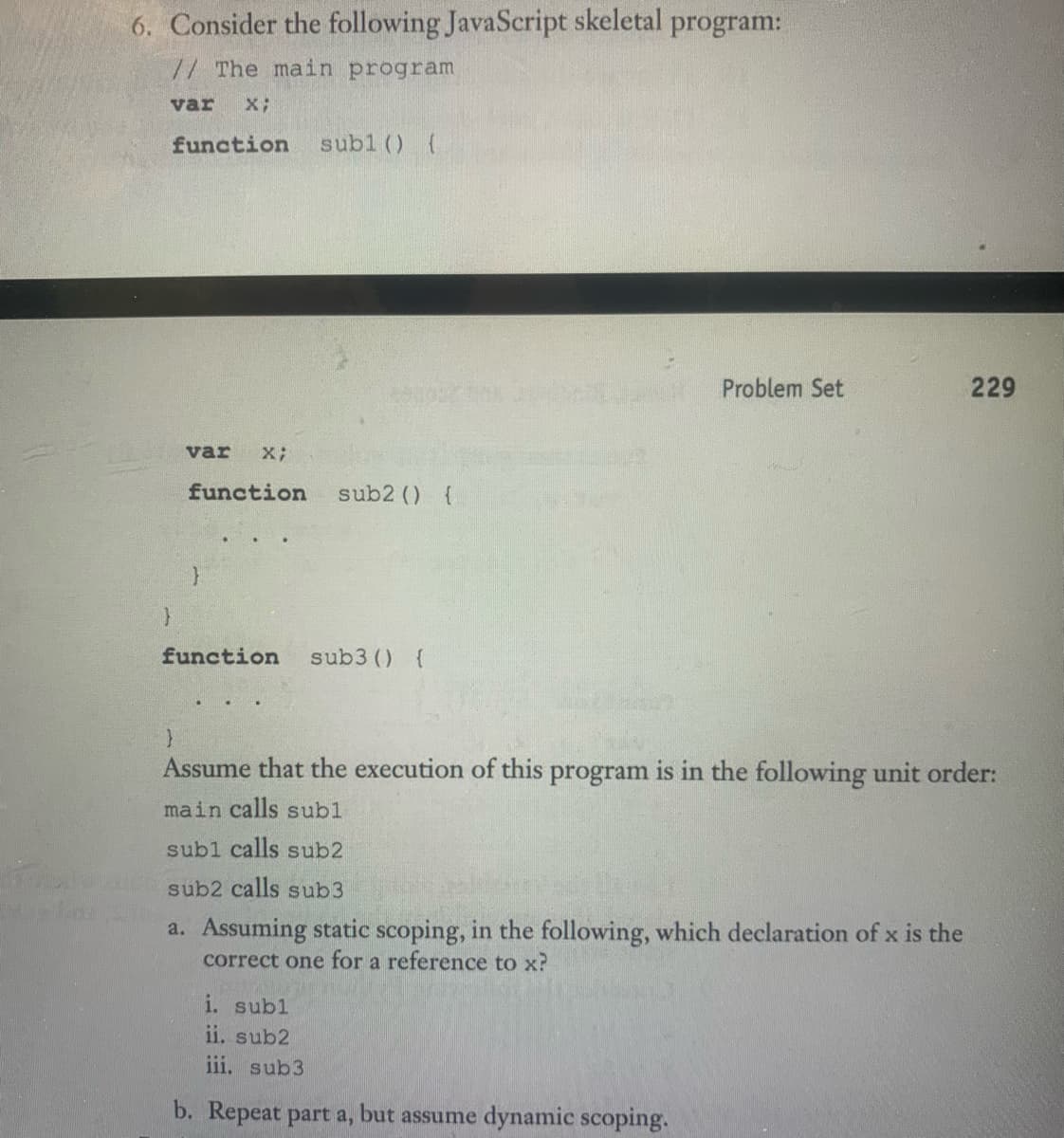
- Concepts of programming language Consider the following JavaScript program: var a, y, c;function sub1() {var b, z, c;function sub2() {var a, b, y;. . .}. . .}function sub3() {var a, x, w;. . .}List all the variables, along with the program units where they are declared,that are visible in the bodies of sub2 when the sequence of function call is:“sub1 calls sub3 and sub3 calls sub2”, assuming dynamic scoping is used.Consider the following JavaScript skeletal program: //The main program var x; function sub1() { var x; function sub2() { . . . } } function sub3() { . . . } Assuming Static scoping, which declaration of x will be used inthe following functions: a) sub1() b) sub2() c) sub3() You can consider the first declaration of x as x1 and the second as x2Question 2. Consider the following skeletal C program. void fun1(void) {int a, b, c;// call another function} void fun2(void) {int d, e, f;// call another function} void fun3(void) {int c, d, e;// call another function} void main () {int a, f, e;// call another function} Given the following calling sequences and assuming that dynamic scoping is used, whatvariables are visible during execution of the last function called? Include with each visiblevariable the name of the function in which it was defined. a. main calls fun1; fun1 calls fun3.b. main calls fun3; fun3 calls fun1.c. main calls fun1; fun1 calls fun3; fun3 calls fun2.d. main calls fun3; fun3 calls fun2; fun2 calls fun1
- With regard to the following JavaScript program, function main() { function sub1() var x = 10; function sub2() { var y = x; } function sub3() var x = 5; var x = 20; } 1) If it is interpreted using static-scoping rules. What value of x is displayed in functions sub1, sub2, and sub3 respectively? Why? 2) If it is under dynamic-scoping rules, what value of x is displayed in functions sub1, sub2, and sub3 respectively? Why?Consider the following JavaScript skeletal program: //The main program var x; function sub1() { var x; function sub2() { . . . } } function sub3() { . . . } Assuming Dynamic scoping, which declaration of x will be used inthe following functions: a) sub1() b) sub2() c) sub3() You can consider the first declaration of x as x1 and the second as x2Need help in this question Consider the following skeletal C program:void fun1(void); /* prototype */void fun2(void); /* prototype */void fun3(void); /* prototype */void main() {int a, b, c;. . .}void fun1(void) {int b, c, d;. . .}void fun2(void) {int c, d, e;. . .}void fun3(void) {int d, e, f;. . .}Given the following calling sequences and assuming that dynamic scopingis used, what variables are visible during execution of the last functioncalled? Include with each visible variable the name of the function inwhich it was defined.a. main calls fun1; fun1 calls fun2; fun2 calls fun3.b. main calls fun1; fun1 calls fun3.c. main calls fun2; fun2 calls fun3; fun3 calls fun
- Write a C++ program with two user defined functions. The first function named “functionWithArray” takes two user input arguments of character types and return True if first argument is smaller than the second argument (alphabetically) and returns False otherwise. Write the second function named “functionWithPointers” which behaves like the first functions but uses pointers to receive the arguments. You may assume that both character arrays contain only lower-case letters, and no blanks or other non- alphabetic characters. Write a suitable Main function to test these two functionsAssume the following JavaScript program was interpreted using staticscoping rules. What value of x is displayed in function sub1? Underdynamic-scoping rules, what value of x is displayed in function sub1?var x;function sub1() {document.write("x = " + x + "");}function sub2() {var x;x = 10;sub1();}x = 5;sub2();Write C++ code for the following tasks: Write a prototype for the function named fsum() that accepts two parameters: an array A of integer pointers and a variable x of type double. The return type of this function is int. Store three integer values entered as command line arguments in an integer array A. Insert the string “ Offline” after the first occurrence of character „o‟ in the string s1= “Hello World”. Also, print the ASCII value of each character in this modified string after insertion. Define a function replace() that receives an integer number as parameter and replaces it with a number formed by rearranging the digits of the original number. The return type of the function is void. Define a class A that declares a static variable count of type integer. Initialize the value of count to zero. Use the variable count to count the number of objects of the class A.
- Exercise 5. 1 Write a C++ program with two user defined functions. The first function named “functionWithArray” takestwo user input arguments of character types and return True if first argument is smaller than the secondargument (alphabetically) and returns False otherwise. Write the second function named“functionWithPointers” which behaves like the first functions but uses pointers to receive the arguments.You may assume that both character arrays contain only lower-case letters, and no blanks or other nonalphabetic characters. Write a suitable Main function to test these two functions. Sample Output:Enter First String: C++ProgrammingEnter Second String: JavaProgrammingAccording to functionWithArrays: 'c++programming' is smaller than 'javaprogramming'.According to functionWithPointers: 'c++programming' is smaller than 'javaprogramming'.Define a function CalcPyramidVolume with double data type parameters baseLength, baseWidth, and pyramidHeight, that returns as a double the volume of a pyramid with a rectangular base. Relevant geometry equations:Volume = base area x height x 1/3Base area = base length x base width.(Watch out for integer division). #include <iostream>using namespace std; /* Your solution goes here */ int main() { double userLength; double userWidth; double userHeight; cin >> userLength; cin >> userWidth; cin >> userHeight; cout << "Volume: " << CalcPyramidVolume(userLength, userWidth, userHeight) << endl; return 0;}Consider the following defintion: data Term = Var String | Application Term Term | Lambda String Term Construct a Haskell function: alphaRename :: Term -> String -> Term Where it performs an alpha renaming. (alphaRename t x) substitutes x for the formal parameter of t, which must be a lambda expression. You can assume that x is not free in t, i.e., not free in the body of t. Please provide your function code with an example input for the above operation.

