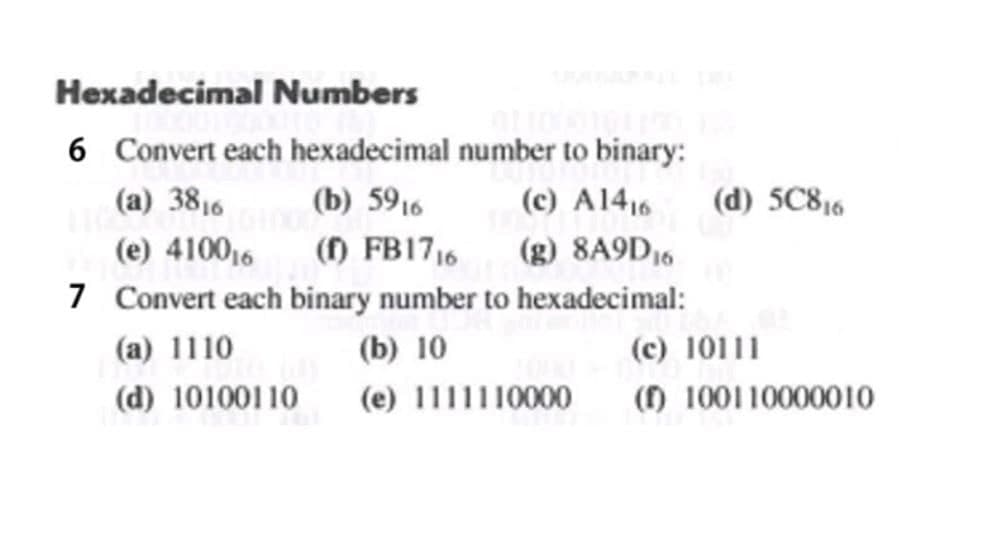
Hexadecimal Numbers 6 Convert each hexadecimal number to binary: (a) 3816 (b) 5916 (c) A1416 (d) 5C816 (e) 410016 () FB17,6 (g) 8A9D16 7 Convert each binary number to hexadecimal: (a) 1110 (b) 10 (c) 10111 (d) 10100110 (e) 1111110000 () 100110000010
Q: Because no new licenses have been issued in the interim, CRLs must be renewed, regardless of when an...
A: Introduction: The CRL (Certificate Revocation List) lists certificates that have had their validity ...
Q: Provide me output screenshot Write a program to read two String variables in DD-MM-YYYY.Compare the...
A: We need to write a program to read two String variables in DD-MM-YYYY, then Compare the two dates an...
Q: What Exactly Is A Tp Monitor In A Client-Server Environment?
A: Intro In a distributed client/server context, a transactional integrity monitor (TP monitor) ensures...
Q: What the following values for the Marketing Team? Use only the x.x.x.x notation for the IP addresses...
A: We Have: The optimal IP address is 98.127.64.0/22 For Technology Team, we require 157 IP addresses, ...
Q: es the square footage of a house given the dimensions of each room. Have the program ask the user ho...
A: As not mentioned I have solved the question in C Language Code: #include <stdio.h> float calcu...
Q: Note: Write Python code to solve the below problem using exception handling. 1. Define a list with a...
A: try: def add(num): # Define function for sum of all element sum = 0 for x in num:...
Q: Data collection from across the organisation is often a catalyst for successful ICT exploitation. An...
A: Introduction: An Enterprise Information System (EIS) is any kind of information system that, via int...
Q: Find the first address, last address and the number of addresses of a network whose one of the IP ad...
A: We are going to find out first address, last address and the number of addresses of a network whose ...
Q: Why does a data warehouse update less frequently than a transactional database?
A: Introduction: A data warehouse is a database that is purpose-built to support business intelligence ...
Q: When it comes to conducting static analysis in-house, what are the benefits and drawbacks?
A: The Answer in step-2.
Q: Recall that within the ArrayBoundedQueue (implemented with the floating-front) the front variable an...
A: ArrayBoundedQueue is nothing but implementing Queue with the help of an array by providing the max s...
Q: Because no new licenses have been issued in the interim, CRLS must be renewed, regardless of when an...
A: Introduction: The CRL (Certificate Revocation List) is a list of revoked certificates. They are publ...
Q: For the first project, we focus on reviewing the basics of Java as you have learned in COMP 110. Wri...
A: The complete working JAVA code is given in next step along with output Array is not used in this cod...
Q: Consider the following list of numbers in order: 3, 6, 8. How the list changes after the execution o...
A: ListRemoveAfter method is used to remove the null values from the list. This function takes two argu...
Q: ask the user for the number of students they want to enter. Each student will have a different numbe...
A: As there is no programming language mentioned, we are using Python for this. Complete solution in ne...
Q: house update less frequently than a transactio
A: Data warehouse update less frequently than a transactional database
Q: What Are the Typical Server Program's Functions?
A: Introduction the question is What Are the Typical Server Program's Functions and here is the solutio...
Q: a. 1+3+5+7+· +999 b. 2+4+8+ 16 + · · . + 1024 d. Σ3 ... n+: с. -i=3
A: Please refer below for your reference: According to the guidelines we are restricted to answer only ...
Q: The choice of a suitable input device for a product frequently depends on the device's nature and ta...
A: Devices for input There are several devices that enter data into the computer, By supplying input, t...
Q: What Exactly Is a Protocol Data Unit?
A: Intro the question is about What Exactly Is a Protocol Data Unit and here is the solution in the ne...
Q: How can you improve the temporal locality of your programs?
A: What is Temporal Locality? Temporal locality is the notion of referencing a resource at a certain mo...
Q: What are some Bluetooth applications?
A: Intro Transferring data files, movies, and photos, as well as MP3 or MP4 files When it comes to wir...
Q: 8.2. Find the sop (sum of Poreluet) of this following Expresion. F(x %;z)= Em[011, 3,5,6)
A:
Q: Write a JAVA program that reads the user's first name and last name, and then use them to create a U...
A: Use an if-else bock to check for the sum of lengths and print respective mail id
Q: What Is the Distinction Between Arp and Rarp?
A: Intro the question is about What Is the Distinction Between Arp and Rarp and here is the solution in...
Q: How do we modify the router ID in an OSPF domain?
A: Please find the answer in the following steps. Open Shortest Path First (OSPF): => Open Short...
Q: Describe how a computer can produce an incorrect answer when performing numerical computations even ...
A: "A computer can produce an incorrect answer when performing numerical computations even though it ha...
Q: Given this Regular expression: (1+01*0)*(01*), define its language in words
A: This is language in which there are any number of 1's between any two occurrences of 0's followed by...
Q: Create a persuasive speech about education
A: Let's see the solution
Q: Explain the functions used to calculate and measure read throughput.
A: Introduction: A function is a collection of statements that work together to accomplish a task. Each...
Q: What exactly is HTML? and how does it function?
A: HTML: The full form of HTML is Hypertext Markup Language which is used to create the layout of web p...
Q: What other questions must be addressed before deciding if database as a service is right for your li...
A: If you're thinking about using a database as a service, consider the following points. If you are no...
Q: How can a modern pipelined computer run a program rapidly and efficiently?
A: Introduction: Pipelines are a succession of interconnected data processing components, where the res...
Q: Hello,,,. I hope you can help me with this code.. The questions to be answered are: (PLEASE REFER T...
A: In step 2, I have provided ANSWERS of both questions------ In step 3, I have provided JAV...
Q: hat are the responsibilities of design patterns in software engineering, and how may they be effecti...
A: Introduction: Design Patterns: Design patterns describe the best practises used by experienced objec...
Q: Why is it critical for a software to terminate an open file as soon as it has finished utilizing it?...
A: Given: Why is it critical for a software to terminate an open file as soon as it has finished utiliz...
Q: When a computer needs a piece of information, does it immediately perform the memory fetch operation...
A:
Q: Explain how a language's coercion rules effect mistake detection.
A: Coercion is a term that refers to an implicit kind of conversion initiated by the compiler.
Q: A global corporation establishes many branches around the country of Pakistan. What form of network ...
A: A global corporation establishes many branches around the country of Pakistan. What form of network ...
Q: What are the advantages and disadvantages of using decimal data types, and how can you use them effe...
A: The advantage of being able to correctly store decimal numbers, at least within a certain range, whi...
Q: What exactly is SDLC? Describe the names of their various phases.
A: SDLC stands for Software Development Life Cycle. It involves the steps that are taken in building an...
Q: What is the structure of a real cache hierarchy?
A: Introduction: The anatomy of a Real Cache Hierarchy must be determined here. The cache hierarchy is ...
Q: Why does a data warehouse update less frequently than a transactional database?
A: Introduction: A data warehouse is a subset of a data management system that is designed to facilitat...
Q: Suppose you want to design and develop an intelligent tutoring system that teaches students in some ...
A: In order to develop an intelligent tutoring system that teaches students in some subject area, we n...
Q: In Artificial Intelligence, talk about Intelligent Agents.
A: The Intelligent Agent is anything that can be viewed as perceiving its environment through sensors a...
Q: Computer Science Develop an inheritance hierarchy based upon a Polygon class that has methods area ...
A: Since no programming language is mentioned, I am using java Code: import java.util.*;abstract class ...
Q: In Artificial Intelligence, talk about Intelligent Agents.
A: Intelligent agent In artificial intelligence, intelligent agent are the computer programs that can ...
Q: Consider an array arr {12, 14, 17,18, 23, 24, 28, 33, 43}. Show using diagram how element 12 can be ...
A:
Q: How to write an essay onTreaps data structure
A: Treaps data structure Treap is a Balanced Binary Search Tree, however not ensured to have height as ...
Q: When referring to the components of a procedure header that appear between the parenthesis, what do ...
A: Procedure Header:- The statement for procedure header is CREATE PROCEDURE. This can be said as a sub...
Step by step
Solved in 2 steps

- 192.67.200.1 in Hexadecimal is: FF:23:C7:01 CA:D3:C8:01 C0:43:C8:01 C0:67:C8:01 C0:43:C8:10Assignment # 11. Convert 82ADh to decimal.2. Convert 11101b to decimal.3. Convert 2BD4h to decimal.4. Convert 95 to binary.5. Convert 2B3Ch to binary.6. Convert 1110101010b to hex.7. Add 3546d and 1872d.8. Add 5B39h and 7AF4h.9. Add 100101111b and 110110.10. Subtract 7283d from 9145d.11. Subtract BA94h from D26Fh.12. Subtract 0111b from 1001.13. Find one’s compliment of 5.14. Find two’s compliment of 5.15. Find two’s compliment of the two’s compliment of 5.16. In many applications, it saves time to memorize the conversions among small binary, decimal, and hex numbers. Fill in the blanks in the following table:Binary Decimal Hex_____ 9 _____1010 _____ __________ _____ D_____ 12 _____1110 _____ __________ _____ B 17. Convert the following binary and hex numbers to decimal:a. 1110b. 100101011101c. 46Ahd. FAE2Ch18. Convert the following numbers:a. 1001011 to hexb. 1001010110101110 to hexc. A2Ch to binaryd. B34Dh to binary19. Perform the following additions:a. 100101b + 10111bb. 100111101b…Assignment # 1 1. Convert 82ADh to decimal. 2. Convert 11101b to decimal. 3. Convert 2BD4h to decimal. 4. Convert 95 to binary. 5. Convert 2B3Ch to binary. 6. Convert 1110101010b to hex. 7. Add 3546d and 1872d. 8. Add 5B39h and 7AF4h. 9. Add 100101111b and 110110. 10. Subtract 7283d from 9145d. 11. Subtract BA94h from D26Fh. 12. Subtract 0111b from 1001. 13. Find one’s compliment of 5. 14. Find two’s compliment of 5. 15. Find two’s compliment of the two’s compliment of 5. 16. In many applications, it saves time to memorize the conversions among small binary, decimal, and hex numbers. Fill in the blanks in the following table: Binary Decimal Hex _____ 9 _____ 1010 _____ _____ _____ _____ D _____ 12 _____ 1110 _____ _____ _____ _____ B 17. Convert the following binary and hex numbers to decimal: a. 1110 b. 100101011101 c. 46Ah d. FAE2Ch 18. Convert the following numbers: a. 1001011 to hex b. 1001010110101110 to hex c. A2Ch to binary d. B34Dh to binary 19. Perform the following additions:…
- The base 10 representation of the largest signed value that can be stored using only 6 bits is: 63 126 31 011111Q1) express binary expression 25610+3210 1310+910 Q2) express binary operation 11100110^2+101011110^2 1000011001^2+11001101^2Represent the following numbers in hexadecimal number system: (85,238)10 (1,056,327)10 (3462)8 (1100101000011101110)2
- Add the following numbers in their respective bases 4568 + 1238 8A5C16 + F39A16 1110002 + 101012Convert the following decimal numbers into the one’s complement and two’s complement binary numbers,assuming 16-bit representation: a. (-124)10 = (-007C)16 = (-0000000001111100)2 =b. (-63)10 = (-003F)16 =(-0000000000111111)2=c. (-39)10 = (-0027)16 = (-0000000000100111)2 =a) 0x92394103 + 0xA04230C8 (b) 0x12345678 – 0xEDCBA988

