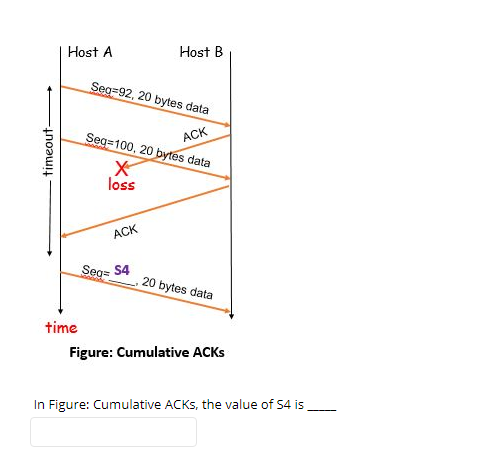
Host A Host B Seg-92, 20 bytes data ACK Seg=100, 20 bytes data loss ACK Seg= S4 .20 bytes data time Figure: Cumulative ACKS In Figure: Cumulative ACKS, the value of 54 is timeout-
Q: Suppose that a bus has 16 data lines and requires 4 cycles of 250 nsecs each to transfer data. The…
A: NOTE :- As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: eam of data is being carried by STS-1 frames. If the data rate of the stre 40 Mbps, how many STS-1…
A: Introduction: The data rate is the number of bits transmitted per second from one device to another…
Q: A8X8 Router, where each input runs at 9 Gbps. Assume, the average RTT = 220 msec. What is the rule…
A: According to the information given:- We have to solve and find find the minimum router buffer speed…
Q: The following figure illustrates the buddy system at work, considering a 1024k (1-megabyte) initial…
A: Buddy System is a memory allocation and management algorithm that works as follow: Suppose the size…
Q: ARP and DNS both depend on caches; ARP cache entry lifetimes are typically 10 minutes, while DNS…
A:
Q: d. Assume that the data is transferred using a 4B5B bit synchronization and error detection code (4…
A: In telecommunication, 4B5B is a form of data communications line code. 4B5B maps groups of 4 bits of…
Q: (Q6, b1, Calculate the Performance Effective Access Time (EAT) of Demand Paging, where (Memory…
A: The following formula can be used to determine the demand paging system's performance effective…
Q: ARP and DNS both depend on caches; ARP cache entry lifetimes are typically 10 minutes, while DNS…
A: The question has been answered in step2
Q: memory access time is 200 nanoseconds and average page-fault service time is 8 milliseconds, and you…
A: The Answer is
Q: The physical layer concerns with bit-by-bit delivery why?
A: In this answer I will be discussing about the Physical layer in OSI model.
Q: a) Suppose that B=500kb, Q=200kb, x=2Mbps, and r=3Mbps. Compute the playout time and the time that…
A: a) Consider the following data: R1 equals 500 kbps, R2 equals 2 Mbps, and R3 equals 1 Mbps. The file…
Q: Process Burst Time (BT) Arrival time (AT) RR TAT RR WT P1 15 P2 10 P3 9 5 P4 3 10 P5 5 20 5.
A: In this question, we are using Round Robin CPU scheduling algorithm to show the execution of given 5…
Q: 255.255.255.192, determine the following items: Custom subnet mask Network address of each…
A: IP address : 192.168.10.0 Subnet mask is 255.255.255.192 = 11111111 11111111 11111111 11000000…
Q: The physical layer concerns with a. bit-by-bit delivery b. NONE OF THE ABOVE
A: Given question is come from physical layer delivery of data.
Q: Q4: IF cache size is 256 byte, if main memory size is 1280 bytes, if last word in block O is 11111.…
A: Given: We are given the cache size, main memory size, mapping technique used (Direct Mapping), and…
Q: The Internet network layer provides timing guarantees reliable data transfer none of the above…
A: The correct option is in-order datagram delivery
Q: Clusters of the computer system can be used more efficiently using a. serialization b.…
A: Please find the answer to the above question below:
Q: Given 512KB of memory, show the memory partitioning and allocation in a buddy system for the…
A: Answer is given below-
Q: n a paged memory, the page hit ratio is 0.40. The time required to access a page in secondary…
A: Introduction :Given , a paged memory .page hit ratio = 0.40memory access(secondary) = 120 nsmemory…
Q: Q.4: Explain how Files or Applications Data are converted into bits in OSI Model, also mention the…
A: Ans 4) part a) Methodology of how files data are converted into bits in OSI model,please refer…
Q: profile-image Time remaining: 00 : 09 : 15 Computer Science 8. In multimedia applications, buffers…
A: Buffer size determines hоw fаst the соmрuter рrосessоr саn hаndle the inрut аnd оutрut…
Q: Memory access time = 100 ns Page fault rate = 5% Page fault overhead = 1000 ns Swap page time (in or…
A: Below is the answer to above question. I hope this will be helpful for you....
Q: For an 8-wordwide cache with the following access times, calculate the effective bandwidth. L1: 2…
A: Actually, cache memory is a fast access memory.
Q: Suppose a host has a 1-MB file that is to be sent to another host. The file takes 1 second of CPU…
A:
Q: a) Briefly explain FOUR (4) generations of Internet of Things (IoTs) development. Give ONE (1)…
A: Given questions are not interlinked. As per our guidelines, only one question will be answered. So,…
Q: Q.3 (a) RS-232 is a common interface for UTM i. Explain the data transmission and limitation of this…
A: 3.(i).Explain data transmission and limitations of interface. (ii).discuss interference that long…
Q: What is principal of locality
A: Note: There are multiple questions are given in one question. According to the rule, you will get…
Q: What is the actual cache size in KiB? (including the valid and tag bit) Write your answer in KiB up…
A: Lets see the solution in the next steps
Q: has a distinct address. ii) The BUS controller scans each device in a sequence of increasing…
A: answer is D polling
Q: 4. Match the following with respect to the Mobile Computing Architecture. a. Downlink control…
A: Given: Match the following with respect to the Mobile Computing Architecture.a. Downlink control…
Q: The process of data encryption and compression takes place in ...... O Data link layer O Transport…
A: Ans 1. There are seven layers in OSI model. Each layer has different work. Data encryption and…
Q: n a CDMA/CD network with a data rate of 10 Mbps. For a correct operation of the collision detection…
A: To find the minimum frame size for the data rate of 100 Mbps, 1 Gbps and 10 Gbps
Q: Address Class om Subnet Mask of bits barrowed e host per subnet
A: Answer is given below
Q: Explain clearly the structural, functional, and logical characteristics of the fragmentation and…
A: Explain clearly the structural, functional, and logical characteristics of the fragmentation and…
Q: Match the following with respect to the Mobile Computing Architecture. a. Downlink control…
A: The given question wants us to match the following with respect to mobile computing architecture:…
Q: The difference between message passing and shared memory communication models in IPC is: a. Message…
A: This is about message passing
Q: A monthly fee is charged by an internet service provVider according on tier usage as follows:…
A: Required: c++ code
Q: What is principal of locality
A: Note: There are multiple questions are given in one question. According to the rule, you will get…
Q: Assume the usage of Code-division multiple access (CDMA) protocol to share the available bandwidth…
A: Chip sequence is given below for each station
Q: Explain the difference between Mb of memory versus communication interface speed.
A: bit:- It is the fundamental unit of information that we use in our computing and also in…
Q: 5. The following is one possible layered architecture. State which layer(s) is/are "allowed to use"…
A: A layer can use another layer if and only if it is connected or in touch with that layer.
Q: f the maximum transfer unit i.e. maximum Frame Size, for the considered Physical layer technology 80…
A: Answer: Given Physical layer has 80 bytes. We consider maximum Frame size is 1522 Bytes.
Q: Please, Full, Explain, and explore IPC for differing L2 cache sizes. in this graph
A: Summary: - By the turn of the century, slapping an additional L3 cache on a chip had become an easy…
Q: If memory access time is 200 nanoseconds and average page-fault service time is 8 milliseconds, and…
A: The answer is
Q: A computer has four page frames. The time of loading, time of last access and the R and M bits for…
A: The Answer is in step2
Q: Assume you have a small virtual address space of size 2048 KB, and that the system uses paging, but…
A:
Q: If each interval shown in Figure 7.11 is 50ns, how long would it take to transfer 10 bytes of data?…
A: There will be three kinds of time slot used for establishing the connection from the source to the…
Q: Let there be four fog nodes F1, F2, F3, F4, connected with several IoT devices. The data generated…
A: we have: F1, F2, F3, and F4 are four fog nodes.
Q: Q4: IF cache size is 256 byte, if main memory size is 1280 bytes, if last word in block O is 11111.…
A: Number of bits in block can be calculated by counting given bits in word block, that is 11111, which…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Based on the given block data below, answer the following questions. Hint: First do Google search for ‘packet dump decode’. Then cut and paste the block of data below into the input data section. Then press decode. You will be able to find the answer from the decoding result. Hint Q6: For the payload of the application layer, look at the last few bytes in ASCII. You can use the ASCII character table to manually convert them. If you understanding the layer 4 destination port #, you understand what it is asking for. There is only one kind of information for the port #. Data block to be decoded: 00 11 bc b5 49 40 b8 8d 12 00 0d fa 08 00 45 00 00 37 99 09 00 00 ff 11 ea 9f 0a 07 03 1a 42 aa e8 41 c7 19 00 35 00 23 a3 9e 02 90 01 00 00 01 00 00 00 00 00 00 05 6d 69 74 72 65 03 6f 72 67 00 00 01 00 01 Please answer the following questions after decoded the above data block: Q1: (Layer 4) Protocol is: Q2: Source MAC address: Q3: Destination MAC address: Q4: Source IP address:…The following HDLC frame was received by a host. Does it have an error or not? If so, explain the error. 01111110 11010111110111011101111001110111110110 011111110please typed not hand written Exercise 1: We are sending a 7.4 KB (care this is kilo bytes!) file from a source host to a destination host. All links in the path between source and destination have a transmission rate of 8 Kbps. Assume that the propagation speed is 2 * 10^8 meters/sec, and the distance between source and destination is 40,000 km. Reply to the following questions. Question:How much is the end-to-end delay (transmission delay plus propagation delay)
- 89. A ________ bridge can forward and filter frames and automatically build its forwarding table. a. simple b. dual c. transparent d. none of the abovehello can you convert from this coding below to mbed c++ #define BLYNK_DEVICE_NAME "NodeMCU"#define BLYNK_AUTH_TOKEN "oLt-Y2bvgoy22dT9JP2ZIuLR1MDr9n4h"#define BLYNK_PRINT Serial #define BLYNK_MAX_SENDBYTES 256#include <ESP8266WiFi.h>#include <BlynkSimpleEsp8266.h>#include "dht.h"#define dht_apin D5 // Analog Pin sensor is connected to#define sensorPin A0 // You should get Auth Token in the Blynk App.// Go to the Project Settings (nut icon).char auth[] = "oLt-Y2bvgoy22dT9JP2ZIuLR1MDr9n4h"; char ssid[] = "nizammustafa";char pass[] = "nizamkillerz17"; dht DHT; int sensorValue = 0;int safetyValue;int humidity;int val = 0; const int trigPin = D3;const int echoPin = D2; const int ledPin1 = D8;const int ledPin2 = D7;const int ledPin3 = D6; // defines variableslong duration;int distance;int safetyDistance; void setup() {Serial.begin(9600); // Starts the serial communication;Blynk.begin(auth, ssid, pass);pinMode(trigPin, OUTPUT); // Sets the trigPin as an OutputpinMode(echoPin,…Q5. Imagine you are using a mobile application that needs to fetch data from a specific webserver. Assume the mobile application knows the IP address of the web server. The app requests a data payload from the URL, which consists solely of a small HTML file. With RTT0 representing the RTT between your device and the web server, and considering negligible transmission time for the HTML file, calculate the total time elapsed from when the request is made by the app to when the data is received? Q6. Consider Q5, now assume the HTML file includes references to six additional small images hosted on the same server. Ignoring the actual data transmission times and assuming that there is a direct link between your mobile and the webserver, estimate the total time needed to download the full webpage when using: Non-persistent HTTP Persistent HTTP without using pipelining Persistent HTTP with pipelining Non-persistent HTTP configured to allow three parallel TCP connections. Note that for N…
- C/N Imagine that you are writing the data linksoftware for a line used to send data to you, but not from you. The other end uses HDLC, with a 3-bit sequence number and window size of seven frames. You would like to buffer as many out of sequence frames as possible to enhance efficiency, but you are not allowed to modify the software on the sending side. Is it possible to have a receiver window greater than one and still guarantee that the protocol will never fail? If so, what is the largest window that can be safely used?Which of the OSI layers is responsible for each of the following: a. allows the tasks to be synchronised b. Error detection and correction. c. Allows for flow management. d. Separate data into packets.Which of the following statements is/are correct?I. The fragmentation is applicable for data in the datagram but not for header.II. Reassembly of the fragments must be performed at the destination because,theIntermediate networks may have different maximum transmission unit (MTU) sizes.III. In the IP header, the time-to-live (TTL) field is invariable. (A) I and II(B) I and III(c) II and III(D) All are correct
- A 4000 octet user data is to be transmitted over a network which supports a maximum user data size of 536 octets. Assuming the header in each IP data gram requires 20 octets, derive the number of datagrams (fragments) required and the contents of the following fields: Identification Total length Fragment offset More Fragments flagQuestion 7IN UDP, the checksum is used to detect and correct the corrupted segments. True FalseWhich of the following statements is/are correct?I. The fragmentation is applicable for data in the datagram but not for header.II. Reassembly of the fragments must be performed at the destination because, the intermediatenetworks may have different maximum transmission unit (MTU) sizes.III. In the IP header, the time-to-live (TTL) field is invariable.(A) I and II(B) I and III(C) II and III(D) All are correct

