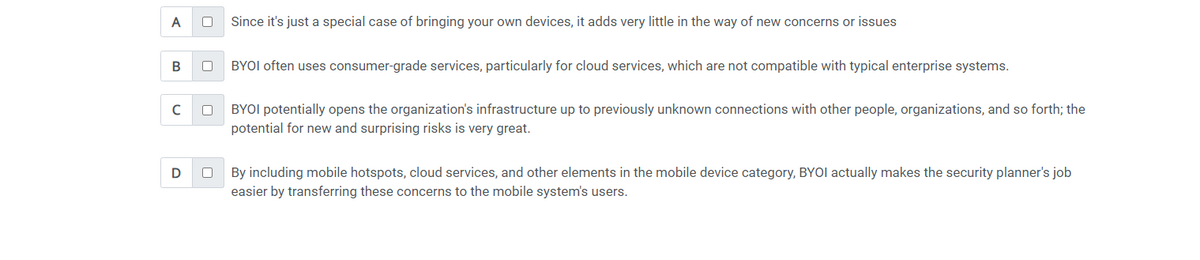
how does bring your own infrastructure (BYOI) affect information security planning?( choose all that apply)
Q: 6. Create a Python programme that accepts a user-inputted phrase string and counts the amount of…
A: def count_words(phrase): # Remove leading and trailing whitespaces phrase = phrase.strip()…
Q: What exactly do we mean when we use the term "networking?" Explain both the pluses and minuses of…
A: Networking refers to the process of creating and nurturing professional connections with individuals…
Q: Can the need of taking precautions to protect sensitive information in the digital era be…
A: The Importance of Protecting Sensitive Information in the Digital Era In today's digital age, data…
Q: Write a script in Assembly language for the (emu8086) emulator that will arrange the ASCII alues for…
A: The question asked to create a program using emu8086, an emulator for the 8086 microprocessor, to…
Q: Is there any logic to forcing all threads in a VM to share the same method space?
A: What is virtual: Virtual refers to something that is not physically present but is created or…
Q: Please summarise the compiler and elaborate on the concept of testability.
A: Software testing is the process of evaluating a software application or the system to identify any…
Q: Modelling is done on systems. How can I get started making models?
A: Understanding the system, defining the scope, selecting appropriate modeling techniques, and…
Q: what do you have to do differently to protect virtual machines, as compared to protecting your…
A: When it comes to protecting virtual machines (VMs) compared to physical hardware systems, there are…
Q: Give me an example of a real SQL database, please.
A: What is database: A database is a structured collection of data that is organized, stored, and…
Q: How complex is it to create a compiler that consistently produces good code? When designing a…
A: Creating a compiler that consistently produces good code can be a complex task that requires careful…
Q: When designing new software, how do you choose between an Object Relational Mapping (ORM) framework…
A: What is software: Software refers to a collection of computer programs, data, and instructions that…
Q: Problem 5 Solve this problem inside the files problems-library.c and problem5-library.h. Do not…
A: For problem5-library.c Start. Include the header file "problem5-library.h" which likely contains…
Q: To that end, I was wondering which of the Compiler Phases you think is the most important. An…
A: While all compiler steps are vital and work together to transform source code into executable…
Q: Find out whether your information is stored in any databases. Where does the data for these…
A: A database is any collection of information systematized for easy searching and retrieval using a…
Q: If you're doing a system analysis and design project, why should you choose an object-oriented…
A: For a project involving system analysis and design, selecting an object-oriented analytical method…
Q: - In C++ using Visual Studio - Seperate the files if there is any .cpp, .main or .h files. PART 1…
A: Here is your solution -
Q: 1. Find the asymptotic upper (big O), lower (Omega) and tight (Theta) bound for the following…
A: Asymptotic: Asymptotic refers to the behavior or characteristics of a function or algorithm as the…
Q: Modelling is done on systems. How can I get started making models?
A: If you're interested in getting started with modeling, whether it's in the field of data science,…
Q: What is the inner workings of the different Compiler Phases, and what are their primary…
A: According to the information given:- We have to define inner workings of the different Compiler…
Q: Find the addressing mode based on the description on the right. is that no memory reference other…
A: Given blank statements are: 1) The advantage of _________is that no memory reference other than the…
Q: How to Making multiple Plots in the same figure using plot superimposition with separate plot…
A: A superimposition plot refers to the technique of overlaying multiple plots on the same graph or…
Q: The most widely used protocols on the internet are detailed below. Before security to be utilised…
A: Answer is given below
Q: As an acronym, "Open System Interconnection" (OSI) stands for what? Do a side-by-side analysis of…
A: Open System Interconnection" (OSI) is a conceptual framework that standardizes the functions of a…
Q: 3. How would you explain APIs to non-technical stakeholders?
A: An API is a set of routines, protocols and tools for building applications and software. It allows…
Q: The OS tracks free and full partitions using bitmap data. Allocation unit processes or holes in…
A: Bitmaps be a statistics organization second-hand in operating systems (OS) to keep track of resource…
Q: 4. Let A = {0,1}. (a) Give an example of a non-empty relation on A that is reflexive but not…
A: Relation: In discrete mathematics, a relation refers to a set of ordered pairs that establish a…
Q: Some may find cybercrime thrilling while others find it repulsive.
A: Cybercrime, a pervasive issue in the digital age, elicits contrasting responses from individuals.…
Q: What are some of the drawbacks of implementing network connectivity company-wide? In addition to a…
A: Hello student Greetings
Q: don't see the point in having so many different partitioning algorithms for operating systems.
A: There are several reasons why there are different partitioning algorithms for operating systems.…
Q: As an added bonus, object-oriented analysis and design may also be used to system analysis and…
A: Object-oriented analysis and design (OOAD) is a methodology that can be applied to system analysis…
Q: As an acronym, "Open System Interconnection" (OSI) stands for what? Do a side-by-side analysis of…
A: The Open Systems Interconnection (OSI) model and the Transmission Control Protocol/Internet Protocol…
Q: In what ways are OOPS different from other types of programmes?
A: OOP is a powerful and flexible method for building complex software systems because of these…
Q: Please explain in your own words why "expandability" is an important consideration when choosing…
A: What is network: A network system refers to the interconnected devices, equipment, and communication…
Q: Is there a formal language that can be used to express the analysis and construction of OO…
A: The analysis and construction of object-oriented (OO) programs require clear and precise methods of…
Q: the point in having so many different partitioning algorithms for operating systems.
A: The existence of multiple partitioning algorithms for operating systems serves several purposes and…
Q: Does anybody have a clear and concise definition of what "optimise compilers" means? When, as a…
A: "Optimise compilers" refers to software tools or programmes that raise a compiler's productivity and…
Q: In what way does the government feel about cybercrime?
A: The CIO's information security plan must include computer ethics. An information security strategy…
Q: Microsoft Office has been the industry standard for the last decade. Do any suitable replacement…
A: Microsoft Office has indeed been the industry standard for productivity software for the past…
Q: Is there a standard procedure that Phases of Compiler use to do this, or do they handle matters as…
A: The handling of testability matters in the phases of a compiler can vary depending on the specific…
Q: If an array is given, identify the next bigger element for each element in the array, if one exists.…
A: Algorithm: Step 1: Begin. Step 2: Create an empty stack and a result array that is the same length…
Q: Discuss the challenges of deploying microservices and how they can be addressed.
A: Discuss the challenges of deploying microservices and how they can be addressed answer in below…
Q: Draught a call for bids for a replacement mobile app ordering system for KFC.
A: Dear Prospective Bidders, We are delighted to announce this call for bids for the development and…
Q: Given the critical nature of the enterprise network, identify three protocols that provide security…
A: Enterprise networks are vulnerable to a wide range of security risks, including threats such as…
Q: What are the advantages of adopting an object-oriented methodology that works for you, one that puts…
A: An approach to software development known as "object-oriented methodology" centres on the idea of…
Q: What are the operations that when undertaken on a bit array can (i) toggle or invert a specific bit…
A: Bitwise operations can be used to toggle or invert particular bits or the entire bit array when…
Q: Prototyping is a valuable tool in the field of software engineering.
A: Prototyping is a software expansion model where a model, an early rough reckoning of the final…
Q: What role does investigation play in the context of cybercrime?
A: The Importance of Cybercrime Investigation As cybercrime continues to grow and evolve, the role of…
Q: How much of a role does education have in cybercrime?
A: Education plays a significant role in cybercrime, both in terms of preventing individuals from…
Q: Write a C++ PROGRAM INCLUDE THE BSTREE.h, MAIN CPP, AND BSTREE.CPP and the text file and show the…
A: Prompt the user to enter the name of the file to analyze. Open the input file and check if it was…
Q: audits through the lens of Governance and Management, and see where the two overlap and where they…
A: Look at IT audits through the lens of Governance and Management, and see where the two overlap and…
how does bring your own infrastructure (BYOI) affect
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- “Mr. Ahmad is a cloud computing professional, you asked him for a free advice about cloud providers for your new small company. He gave you full explanation and recommended some good providers. There is another provider which may be better but he did not recommend since he is in dispute after doing some work for them.” Did Mr. Ahmad did anything wrong as an IT professional? Is his behavior not ethical or illegal and why? Are there any consequences of his action? Analyze this case in depth and write your conclusion.Multiple chocie questions related to AWS : Question1: Your team is looking for a service to automatically replace impaired instances in your environment. Which service should your team use? a. Amazon CloudWatch b. AWS Lambda c. AWS Auto Scaling d. AWS Systems Manager Question 2 Your website is experiencing latency issues when delivering video content to end users. What can you create to increase the speed of your website? a. Content delivery network (CDN) b. Auto Scaling group c. Connected network d. Cloud delivery group Question 3: A company wants to establish an identity federation solution for their AWS account. They want to use a single centralized directory for identity management. Which AWS identity federation solution is the best option for the company to employ? a. AWS CloudTrail b. AWS Single Sign-On c. AWS CloudFormation d. AWS ConfigQ2 Smart-Toys-Smart Kids CEO (Part 2) Smart-Toys-Smart Kids has decided to install a new e-mail package to streamline communications within the company. Fred would like to have one common calendar for his all 200 employees. The expected features of the new e-mail package are “background processing” that doesn't get a great deal of attention. This includes managing connections, checking for errors in commands and e-mail messages, and reacting accordingly. The e-mail software vendors offered two different e-mail system for solution. One vendor is offering an SMTP-based two-tier client server architecture. The second vendor is offering a Web-based e-mail architecture. Fred doesn't understand either one. a) Briefly explain to Fred, in layman's terms, the differences between the two. b) Outline the pros and cons of the two alternatives c) Make a recommendation to Fred about which is better for his company ANSWER Classification SMTP-based two-tier client server…
- In this discussion board post, you will analyze and list the advantages and disadvantages of Cloud Computing over on-premise computing. You will also analyze the advantages and disadvantages of each one of the Cloud Deployment models and what approach is best for protecting each. Finally, you will analyze the risks and threats associated with Cloud computing and the best practices to follow. Answer the following: What are the advantages and disadvantages of Cloud computing over on-premise computing? What are the advantages and disadvantages of each one of the Cloud Deployment models? What approach is best for protecting each? What are the types of risks and threats associated with Cloud computing? What are the best practices to follow to better protect your cloud implementations?"PE 9-6. Consider the narrative that follows (originally introduced in PE 2-8) and answer the following questions: a. Based on this description, which types of client devices does the system utilize? What are the user roles for each client device type? b. What type of network connectivity does the organization need within its facility? c. Which elements of the system require connectivity between the company and its customers using the public internet? d. Are there component types in the story that we didn’t discuss in this chapter? How important are those for this business? e. Based on this description, what are the most important non-functional requirements for this system? f. Identify candidates for separate applications within the system. Use a diagram similar to Figure 9-13 to illustrate the applications and their relationships with each other. g. Assume the company wanted to find…which risk is unable to be highlighted from the outset in a cloud service contract? Result of an unforeseen event Introduction of new technology Changes resulting from contract renewals Sunsetting of aging technology
- A bank has hired your firm to investigate the fraud carried out by one of their employees. Thebank uses three 40TB workstation machines on a Local Area Network (LAN). Let’s assume youhave been asked not to remove the workstations, but you have access to consult theiradministrator who is familiar with the stored data.Discuss the strategy and process that you will use to collect evidence and discuss the relevantguidelines for collecting digital evidence.Please send me answer within 10 min!! I will rate you good for sure!! Please solve all the questions with proper explaination!! Question (1). Which of the following best describes a private cloud? The interactions can include remote access by systems outside the organization. The interactions are considered to be limited to entities within an organization. Data is allowed to be stored via public Internet provider clouds Data is normally limited within the organization but can be backed up remotely on a public cloud provider's storage. Question (2). A cloud migration solution that is useful for companies who want cloud based services and savings but are hesitant to commit to a full private cloud is known as ________. Public Private Community Hybrid Question (3).Which of the following are advantages of a public cloud? Efficiency in the use of hardware Lower allocation of square footage and related building costs Increased security No data migration needed Question (4). Identify which of…1- A properly designed extranet allows companies to reduce internetworking costs and gives participating companies a competitive advantage, which can lead to increased profits. After reading the information presented in this module and other sources, write a one-page paper that identifies three companies that are using extranets as an internetworking platform. List two applications of this platform in each company. What are two challenges that must be overcome for designing a successful extranet?2- Ask MD is a popular medical app. After reading the information presented in this module and other sources, write a one-page paper that summarizes some of the features of this app. What are three other examples of medical apps for iOS and Android devices?3- The human resources departments of many organizations are creating intranets to improve the efficiency and effectiveness of the departments’ operations. After reading the information presented in this module and other sources, write a…
- the different cloud delivery models and services as described in the book. The summary should include the definition of each model and the services that may utilize that model. Include examples of services that are available. Given what you have now learned, please determine the best model for a small business of 10-20 employees to provide secure email with 24/7 accessibility from anywhere on any device. Why did you choose that particular model?One ongoing concern for Vivobarefoot is the quality and speed of the Internet service available to itsoffice in central London. Given that, do you think it made sense for the company to move more of itsIT services to the cloud? Go online and do some research about Microsoft’s Office 365 product. Whatoptions does it offer for working offline if Internet service is not available? Does that change youropinion about Vivobarefoot’s shift to the cloud?Describe your experience with the following, in detail: a. Microsoft Operating System Software, including the setup of DNS, DHCP, DFS, Group Policies, Active Directory, Forests/Domains, etc. b. Virtualization, storage, and backup technologies c. Cisco and/or other networking equipment d. Enterprise software solutions e. Cybersecurity solutions and controls. Could you answer this question ASAP, if possible please. Thank you!



