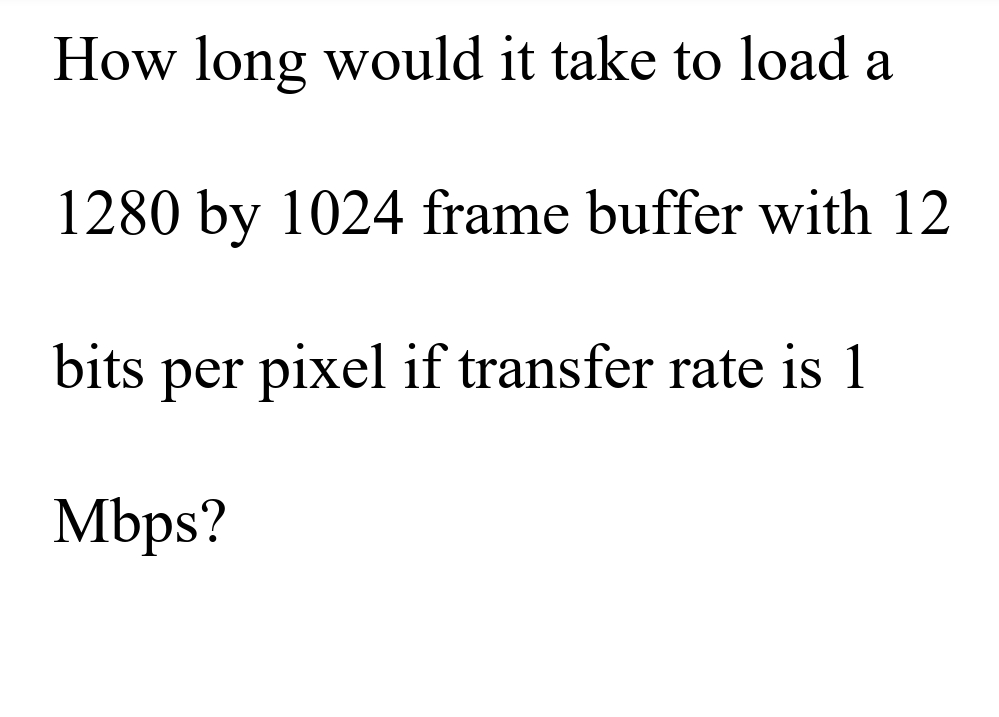
How long would it take to load a 1280 by 1024 frame buffer with 12 bits per pixel if transfer rate is 1 Mbps?
Q: Choosing a hash function to work with keys is more difficult and should be chosen carefully. A…
A: The hash function you use will depend on the key's data type.The simplest function, if your key is…
Q: Translate the following code into python import java.util.Scanner; public class Main {…
A: Here is the python code of the above problem. See below steps.
Q: What part does technology play in one's educational experience?
A: Answer the above question are as follows
Q: const
A: Dear Student, const keyword is used to store a constant value, and double is used to store a decimal…
Q: te
A: Dear Student, PPD-21 designates DHS as the responsible agency to provide strategic guidance to the…
Q: ut two separate topics, therefore he plans to utilize a Boolean operator to do it. Kevin has to know…
A: Introduction: However, in this case, since we are comparing two outcomes, we use AND.If more than…
Q: Write a short note on Aspect Ratio.
A: Introduction: A picture's aspect ratio is nothing but a ratio of its width to the height. The width…
Q: & largest. Write down the algoris
A: Solution - In the given question, we have to sort the given array using any algorithm.
Q: Provide realistic examples of each of the risk response strategies for both negative and positive…
A: Risk response strategies are used to address risks that have been identified in a project. There are…
Q: Is there a list that describes the many types of malware and what each one does?
A: Malware:- Malware includes malware, ransomware, and spyware. Malicious software is cyber-attacker…
Q: Exactly what is the meaning of the term "clustering," anyway? How does it function in the context of…
A: Clustering is a data analysis technique that involves grouping disparate data objects into…
Q: Create a list of the two external and two internal barriers that prevent you from hearing well.
A: HEARING BARRIERS Unfortunately, barriers sometimes prevent people from listening effectively. These…
Q: Do you believe that the emergence of the knowledge worker is being caused by the development of…
A: The above question is solved in step 2 :-
Q: One indication of the adaptability of big data is the fact that information may be obtained in a…
A: The above question is solved in Step 2 :-
Q: 1.) The source register values are as follows: $s1 0000 0000 0000 0000 0000 0000 0000…
A: 1.) The source register values are as follows: $s1 0000 0000 0000 0000 0000 0000…
Q: Once a filesystem has been formatted on a hard disk drive, all of the partitions on that hard disk…
A: On a hard disc drive, a partition is comprised of the following: Utilizing the graphical…
Q: What are the three levels of abstraction that may be applied to data?
A: According to Bartleby Guidelines we need to answer only one question so I have answered first…
Q: Discuss what is meant by the term "OpenGL display callback function".
A:
Q: How does DeMorgans law show that the negation of a k-map will give the same answer as the original…
A: Introduction: The disjunction of the negations is the same as the negation of a conjunction,…
Q: What are the key distinctions between.DLL NET's and EXE files??
A: The key distinctions between.DLL NET's and EXE files is given below -
Q: Numerous engineering and scientific applications require finding solutions to a set of equations.…
A: class Main : @staticmethod def main( args) : x1 = 0 x2 = 0 y1 = 0…
Q: The objective of checking a toolpath on the screen of a CAM system before writing the computer code…
A: Introduction: The semiconductor industry has accepted that Moore's Law is creating new market niches…
Q: Pipelining does not work when using the computer paradigm developed at Princeton. Give an…
A: Introduction: PC engineering is based on John von Neumann's 1945 depiction of the von Neumann model.…
Q: For the Human Resource department you choose, show how that department can be computerized since…
A: (a) Department of human resource can be computerized by using a computer system instead that can…
Q: All these three trees below are proper binary trees. check the picture sent a. true b. false
A: In this question we have been given some binary trees and we need to determine whether all the given…
Q: Specify the IT frameworks and resources that characterize IT project management.
A: Definition: Every firm has high-stakes project management. Tracking project phases is essential.…
Q: This solution does not work for the question asked. The question submitted clearly shows 2 list…
A: Provided the C# coding for Dorm and Meal Calculator. The code and output screenshot is given below:…
Q: What are some examples of the ways in which the effect of technology on education could manifest…
A: Introduction: The use of technology for teaching and learning is still a problem. Despite many…
Q: Construct a PDA that recognizes the language a²nf³n
A: PDA for a2nb3n see the below PDA
Q: How has the advancement of technology affected the way we live?
A: Introduction: Technology has long disrupted our lives. Senior technology has created amazing tools…
Q: Explain the Rasterization and Scan Conversion.
A: Introduction: Altering a video feed's vertical and horizontal scan frequencies is a standard video…
Q: , this is a java programming question, I'll attach the image and type the question Implement the…
A: Program Approach: 1- As mentioned in the assignment created the class name as Library and Book.2-…
Q: During this step of the ETL process, the goal is to collect data from a variety of sources and then…
A: Introduction; Extract, transform, and load is what's meant by the acronym ETL.The process of…
Q: How does wire speed work in the virtualization?
A: Answer: network administrators to enjoy the benefits of virtualization, such as reduced costs and…
Q: According to our recommendations, Flynn's taxonomy need to be expanded by one level. What sets a…
A: Flynn's taxonomy's widespread acceptance is attributed to two things. These include: how many…
Q: Describe the key distinctions that exist between constrained and unbounded stack implementations.
A: According to the information given:- We have to define the difference between constrained and…
Q: Combination of Function Pass-by-value and conditional Statement in C LANGUAGE. Provide: write a…
A: An example of C code using Function Pass-by-value, Looping Statement, and Conditional Statement is…
Q: Write a program whose input is two integers. Output the first integer and subsequent increments of 5…
A: The above question is solved in step 2 :-
Q: about data privacy in our time
A:
Q: How do system services and user applications communicate with one another when using a microkernel…
A: Introduction: In a microkernel design, how do system services and user applications communicate with…
Q: What kind of changes have been brought about by the advent of the Internet in terms of system…
A: Introduction: Computer architecture: The term "computer architecture" refers to a specification that…
Q: If a processor sends a cache-unfulfilled request at the same time as a block is being pushed out to…
A: Both the cache and the write buffer operate in a completely separate manner from one another. The…
Q: Explain Vector Scan/Random Scan Display.
A:
Q: Design a deterministic Turing machine with input alphabet Σ = {a, b, $} that accepts the language L…
A: The complete in JFLAP software is below:
Q: Assume that there is a consistent roundtrip delay between the sender and the receiver, and that the…
A: The Reliable Data Transfer protocol has been updated to its most recent and improved version, RDT…
Q: Finish the constructor for the KickBall public class Ball ( public double diameter, public…
A: The solution is given below
Q: How have programming languages progressed over history?
A: Programming languages have progressed significantly over history, becoming more sophisticated and…
Q: compare windows OS security policy with the Clark-Wilson model. Does its security mechanism satisfy…
A: Let's see the answer:
Q: SHOW THE MV COMMAND WITH ONE OPTION AND EXPLAIN.
A: MV COMMAND MV is short for move. In a file system like UNIX, the mv command is used to relocate…
Q: Is this the right answer or the wrong answer? Assume that the most recent SampleRTT for a TCP…
A: Definition: Sample RTT is used while communicating through TCP. The Transmission Control Protocol…
Step by step
Solved in 2 steps

- Suppose an SD card has a capacity of 4 Gigabytes. How many photographs could be stored in the card if each takes 8 million pixels with 24-bit True-Color encoding?Construct 8x4 bit ROM using a decoder of a suitable size.when we view video on a computer the analog video is digitized and stored in the frame buffer of the video frame grabber card.suppose that a vedio is digitized at integer frame rate size 640*480 pixel and bit depth of 24 bit explain why you dont see a flicker effect on your workstation screen when display this video at NTSC frame rate ?
- Consider a raster system with resolution of 640*480. What size frame buffer is needed to store 12 bits per pixel? How much storage is required if 24 bits per pixel are to be used?Calculate the total memory required to store a 10 minute video in a SVGA system with 24 bit true color and 25 fps.One way for reducing the power consumed in IoT devices is using compression. For the following input: 11111111111111100000000000000000001111 calculate the resulting compressed output. Compare the power needed to transmit the resulting output against that of the original.
- What is the maximum theoretical data transfer rate (in Gbps) of a PCIe 4.0 x16 slot, assuming a 128b/130b encoding scheme?Suppose a RGB raster system is to be designed using an 8 inch by 10 inch screen with a resolution of 100 pixels per inch in each direction. How long would it take to load this raster system in frame buffer with 24 bits per pixel, if 10^5 bits can be transferred per second?Calculate the raw memory requirement in megabytes (MB) for an uncompressed 10bit GB 4:4:4 colour image in UHD-1. Write down the full calculation that you perform(* as multiply, / or : as division)..

