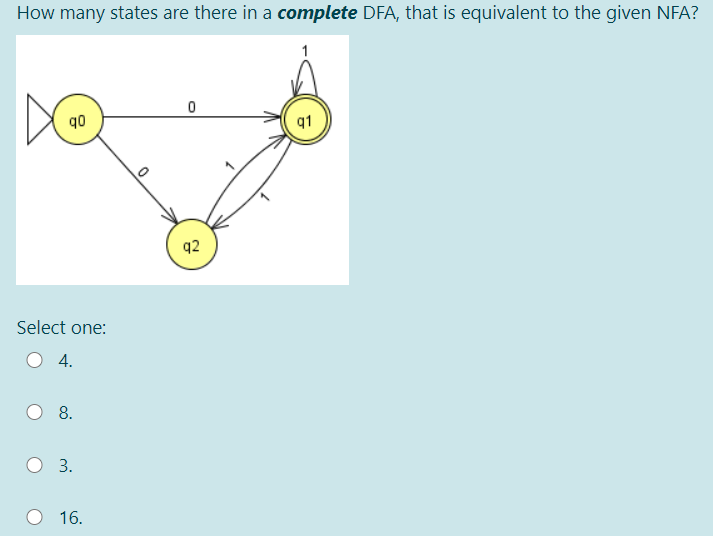
How many states are there in a complete DFA, that is equivalent to the given NFA? 1 q0 q2 Select one: 4. 8. 3. O 16.
Q: Given the below conditional CMP r0,r1 ADDEQ r2,r0,r1 SUBGT r2,r0,r1 RSBLT r2,r0,r1
A: The correct is questions in Option("r2=15,N=1")
Q: Your company is building a computer network, and you are asked to develop a scheme for dealing with…
A: Introduction: Deadlock: Deadlock is a situation where a set of processes are blocked because each…
Q: What is "Kill Switch"? Support your answer with one example while explaining "Kill Switch".
A: To define Kill Switch
Q: An interrupt is more than a simple mechanism for coordinating I/O transfers". Justify the…
A: The Answer is
Q: od (45, 5) and div (45, 5). mod(45, 5)=? div(45, 5)=?
A: The mod operator will return the remainder. The division operator will return the quotient.
Q: Draw Gantt Chart and calculate the average waiting time using the given table ?? Burst Time 10…
A: All process values:
Q: How would I decrypt an RSA message? Let's say we're given C, p, q, e.
A: Steps to decrypt an RSA message:The formula to get the plain text from cyber text using RSA…
Q: . What is the eneryption value for the following parameters using the RSA algorithm? p-3; q-11; e-7,…
A: Given values are as follows p=3 q=11 e=7 M=5 So, n = p*q = 33 ∅(n) = (p-1)*(q-1) = 20
Q: Suppose that you have four processes p1-p4 with a burst time (3, 5. 4, 1) and they are all arrived…
A: PLEASE DO SUPPORT FOR MY EFFORTS THANKS! ANSWER:
Q: 4. Does the following group communication of 4 computers respect the FIFO order? p1 p2 p3 physical…
A: Below is the answer of the above query. I hope this will help.
Q: We can refresh the results of NETSTAT by using this switch: Group of answer choices No switch, just…
A: These commands are used to operate Linux Systems, these commands help in accessing the root…
Q: Draw Gantt Chart and calculate the average waiting time using the given table ?? Burst Time 10 1 2 1…
A:
Q: Consider the following Unix dialogue carried out by user flower: $ Is -R х хх ххх у уу ууу хх: хх аа…
A: Required:
Q: Given the following burst time and arrival time for four processes along with Gantt chart: Process…
A: Lets see the solution.
Q: Your company is building a computer network, and you are asked to develop a scheme for dealing with…
A:
Q: Let consider a process iin which one state is Blocked and waiting for some input/output service.…
A: Let consider a process iin which one state is Blocked and waiting for some input/output service. And…
Q: ymuch time will the program takes to execute?, frequency=10Mhz, W=2 ple : addwf PCL retlw 23 retlw…
A: It is defined as the number of waves that pass a fixed point in unit time; also, the number of…
Q: Suppose there are three processes A, B and C. All clock runs at the same rate but initially A’s…
A: Answer (a): A will sends message to B from 10 to 0, but it takes 4 units. So it will receive on B's…
Q: For CTR, on the lecture notes, it shows the decryption rule is P = C E (IV +n, K) 1. Is Ea typo?…
A: No, it’s not a typo as a many algorithm uses the E meaning encryption to decrypt the real meaning of…
Q: This problem is taken from exercise 1.10b. Let A = {w/w contains at least two Os and at most one 1}…
A: Given: A= { w| w contains at least two Os and at most one 1's} We have to design NFA for this…
Q: Which of the states in the DFA produced using the powerset method from the following NFA (with…
A: The Answer is in Below Steps
Q: Given two sets s1={2,3,5,'*' , 2,6,'#',3} and s2={2,'o',3,5,6,8,'€'}, write down three commands give…
A: Here 2 set are given, we have to perform differently operation on them and print them.
Q: Consider the following python program and write the output str="Network systems 75…
A: The output of the program is: 6 3 15 Computer systems
Q: What exactly do you mean when you talk about a cascading termination?
A: Answer in step 2
Q: Consider the DFA, M = ({go, 91, 92), (0, 1}, 6, go, (go, q1)) where the transition function defined…
A: Language = 1*00* The string of language are 0 , 10, 110.... Let's try drawing DFA where initial…
Q: Consider the following snapshot of a system: Allocation Max Available ABCD АВСD АВСD T. 3141 6473…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: Evaluate the result of this operation? a = pow (-2,floor (3.5)); O a is 8.00 O a is -16.00 O a is…
A: #include <iostream>#include <cmath>using namespace std; int main(){float a;…
Q: * First Come First Serve (FCFS) and * Round Robin (RR) with quantum time = 3 Process Arrival Time…
A: Solve the given CPU scheduling problem
Q: 00 01 00 1,0 100 11 1/1 00 1/1 00 010 1/4 Assuming all possible states are covered, the state table…
A: Given the state diagram , assume all possible states are covered the state table corresponds to the…
Q: Consider the following processes and answer the questions, the burst time for processes p1 to p4 is…
A: Shortest Job First (SJF) is an algorithm in which the process having the smallest execution time is…
Q: Identify the strings whether either ACCEPTED or NOT ACCEPTED by the given PDA. NOTE: a, & / XXX…
A: 1. The string is read by head. Initially the head is at first character of the string. 2. See the…
Q: Suppose that you have four processes p1-p4 with a burst time (3,5, 4,1) and they are all arrived at…
A: Round Robin algorithm works on time slice or time quantum, Given: Tq=2 Process=4 AT=0 Bt
Q: Consider system with 12 DVD and 3 processes. Check whether the system currently in a safe state>…
A: System is in safe state explained below:
Q: Knowing that the states A, B, C and D are coded as 00,01,10 and 11 respectively, choose the state…
A: EXPLANATION: Given that the binary values for various states: A - 00 B - 01 C - 10 D - 11 Then…
Q: Given 4 processes P1, P2,P3,P4 with burst time 4,5,8,1 respectively. What will be the order in which…
A: SJF algorithm stands for Shortest Job First, in this algorithm the process with least burst time is…
Q: i have an assignment to design a newtork for a chosen organization.. with a scenario that include at…
A: Your computer network infrastructure is the backbone of your business. All your devices,…
Q: What does it mean to say that a nonce is a once-in-a-lifetime value? In whose lifetime?
A: A nonce is a value used by a protocol once in a lifetime to determine if the sender is alive…
Q: 1. Calculate average waiting time for the following table using round robin algorithm, if time Plase…
A: Round robin scheduling algorithm is the one of the scheduling algorithm and it having the time…
Q: Given x=0:pi/100:3*pi; y=sin(x); write a script to plot the two lines with different colors in one…
A: We can plot the two lines using the figure and hold on and hold off.
Q: Given: PDA Transition Diagram 0,E/X 1,X/E qo 91 9: 1,$/$ E,X/X E,$/$ ar Identify the strings whether…
A: Please upvote. I am providing you the correct answer below. please please please.
Q: Draw Gantt Chart and calculate the average waiting time using the given table ?? Burst Time Arrival…
A: Given table contains the Processes and their Burst time, priority and Arrival times. Priority is…
Q: In a CFG: S- OA1C | DOD А — СЕ → 1C | 00 C → 0 D - D010D E - 10 Which variables are useless ? A and…
A: Defined the useless variable
Q: Draw Gantt Chart and calculate the average waiting time using the given table ?? Burst Time 10 1 2 1…
A: Below is the following solution of your question:
Q: 3. Does the following group communication of 4 computers respect the FIFO order? p1 p2 p3 physical…
A: Here, p4 sends_message A and p2 sends_message B. The first_message is_sent by p4 and_then by p2.so,…
Q: A document was digitally signed by you and later you find out that two characters in one of the…
A: Digital signatures are a regular component for the most cryptographic protocol libraries and are…
Q: 8a. What does the following piece of Python code print to the terminal ? 1st = [1, 2, 3] for i in…
A: B. 0 1 2 Output screenshot :
Q: Which of the following is true about the given state diagram? S0/0 S1/0 S2/0 S3/0 (S4/1 Select one:…
A: Answer: Select one it detects the sequence 1001 with overlapping.
Q: WHO wants to know when this process will stop, i.e., when all N viruses will have the same type. Can…
A: According to the given problem statement, we need to create a C ++ code that includes a number of…
Q: Approximately how much entropy does a password consisting of a single random English word have?…
A: log2(RL) 1: r=26 l=8 =log2(268) =37.6035 2: r=52 as both cap and low letter and l=8
Q: Given N = 1,842,338,473, where N = 56,843 32,411 In the context of RSA, which is a value 'e' that…
A: Given that N=1,842,338,473, where N= 56,843*32,411 The value of “N” is, From the above equation,…
Step by step
Solved in 2 steps with 2 images

- First give the Trs for this NFA: Trs(q1, 0) = {} Trs(q2, 0) = {} Trs(q2, 1) = {} Then give the following Trs for a set of current states: Trs({q1, q2}, 0) = { } What are the possible states you end up in after reading 0011 ? Trs*(q1, 0011) = { } Should 0011 be accepted? Why?**There are no external tools**Just by looking at the Petri net's structure, it is possible to infer the possible order of events. Justify the lack of a clock or other means of tracking the passage of time inside a Petri net.Suppose N people want to communicate with each of N – 1 other people using symmetric key encryption. All communication between any two people, i and j, is visible to all other people in this group of N, and no other person in this group should be able to decode their communication. How many keys are required in the system as a whole? Now suppose that public key encryption is used. How many keys are required in this case?
- In the Diffie-Hellman Protocol, each participant selects a secret number x and sends the other participant αx mod q for some public number α. What would happen if the participants sent each other αx for some public number αinstead? Give at least one method Alice and Bob could use for agreeing on a key. Can Eve break your system without finding the secret numbers? Can Eve find the secret numbers? In TLS, why is there a separate Change Cipher Spec Protocol, rather than including a change_cipher_spec message in the Handshake Protocol?Asynchronous renaming in the message passing model. Code is for processPi, 1 ≤ i ≤ n.How can you identify the various computer networks apart from one another? Make advantage of a fictitious scenario to illustrate
- One potential limitation of a digital signature is that for a given signature σ of a message m corresponding to a public key pk, one could generate a pk', sk' that produces a signature σ' for m, such that σ' = σ. Given a signing function S, a verification function V, that each takes corresponding private and public keys for generating and verifying a signature and is vulnerable to these duplicate keys, please generate S' and V' that are immune to a duplicate keys attack.Try recognizing the following tokens with the given state diagram. For each part, describe how the token is accepted or reject. a) -.453 b) 0.000032Massages exchange between managers is possible in: A) SNMPv2 only B) SNMPv1 & SNMPv2 C) SNMPv2 & SNMPv3 D) SNMPv1 only
- Is it problematic that there are so many distinct kinds of computer networks at work? How do we go about fixing these problems, if at all?A Man-in-the-Middle attack on the Diffie-Hellman key exchange protocol may be effectively carried out if the adversary produces two public-private key pairs for the assault. Could the same assault be carried out with a single pair? Justify and describe the event in full.What happens when the MTTR reaches 0? Is the situation realistic?

