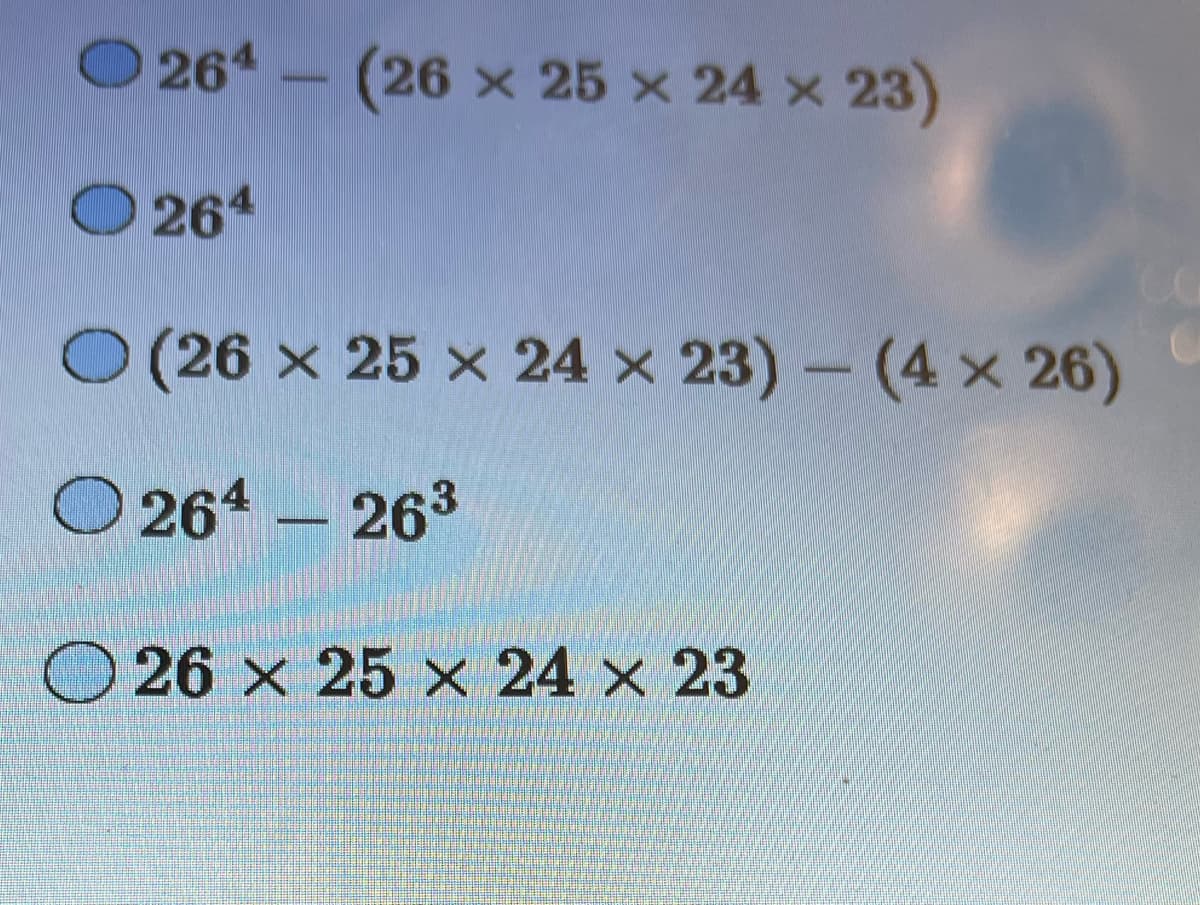
How many strings of length four of uppercase English letters are there which have to be repeated letters?
Q: Is there a specific data processing method I need to be aware of? If at all possible, provide…
A: Given: Is there a particular method of working with material of which I ought to be conscious and…
Q: During a TLS transaction using a different cipher specification, what role does the MAC play, and…
A: In TLS cypher specification is a cryptographic algorithm used to encrypt and decrypt the data being…
Q: Think about the characteristics of big data and how different forms of data are defined in terms of…
A: Big data analysis describes the process of uncovering trends, patterns and correlations in large…
Q: Please provide two justifications for why data should be replicated across various data centers that…
A: Disaster Recovery: Replicating data across different data centers located in different parts of the…
Q: When it is beneficial to do so, processes and programs that are executed on a big computer should be…
A: Introduction: Hardware and software are the two primary components that may be separated when…
Q: javascript, not java code
A: Given, Write the Java Script code Devise an algorithm to scan an input array a of n elements, and…
Q: Sequential and direct access locate memory data. Today's society debates direct access to vital…
A: Sequential access describes watching a movie in order. Direct access means accessing a record…
Q: While working with Microsoft Power BI, you should keep in mind the significance of modeling. A…
A: Data Modeling is one of the features utilized to link diverse information sources in BI tools via a…
Q: DNS records by kind. Explain their use using examples. Can a business's web and mail servers share…
A: DNS records by kind. Explain their use using examples. Can a business's web and mail servers share…
Q: Track system architecture's evolution, focusing on the personal computer and Internet. If possible,…
A: 1) A computer is an electronic device that can process data and perform various operations based on…
Q: 1. Creating an Influencer from Different Platforms by Codechum Admin Year 2020 - the sprout of…
A: The question is asking the reader to create a program that models online influencers from different…
Q: Database management system lab project: Project Topic- Hall manage system. [N.B : use sql…
A: The Hall Management System is a database management system project aimed at simplifying the process…
Q: When you say "partitioning operating systems," what exactly do you mean by that? Explain the…
A: Given: When you talk about the partitioning of operating systems, what exactly do you mean by that?…
Q: Describe a database management system's purpose and characteristics.
A: Database management system is basically a system software which is designed to the management of…
Q: Which hardware methods make virtual memory systems efficient? How do they work? Two must occur.
A: There are several hardware methods that make virtual memory systems efficient. Two of the most…
Q: When you successfully construct an instance of a structure, what do you get exactly?
A: Explanation: All the fields in a structure are initialised to 0 when a new instance is created. The…
Q: Troubleshooting requires expertise and equipment for all technicians. To help technicians discover…
A: A technician's toolkit for troubleshooting operating system faults typically includes diagnostic…
Q: Walk me through the stages involved in the process of reading and writing files.
A: Given, Walk me through the stages involved in the process of reading and writing files.…
Q: Cybercrime Conceptual Framework? Reference your answer.
A: Several people, businesses, and governments commonly rely on the Internet daily. The way…
Q: In the context of information systems, how would you define the concept of risk management?
A: An information system are the collection/group of people, processes, and technology that work…
Q: ake use of a statement to initialize a new instance of the Transcript class.
A: here is an example statement to initialize a new instance of the Transcript class: Transcript…
Q: What are the two main advantages of layered protocols? Give evidence.
A: Introduction: Several Protocols: A protocol is a set of guidelines that spells out how two entities…
Q: Think about how important wireless network infrastructure is in today's underdeveloped countries. In…
A: Local area networks (LANs) may be maintained efficiently and effectively with the aid of a robust…
Q: Define test-driven development success criteria. How would you improve it as a teaching tool at your…
A: Test-driven development (TDD) is a software development approach that involves writing automated…
Q: In this grammar, "S" is the starting symbol, which generates a sentence by combining a noun phrase…
A: Let's first go through the fundamentals of parse trees and context-free grammars. A set of…
Q: This part will offer you with a real-world SQL database to work with.
A: It is more effective to learn SQL by focusing on the queries you want to answer rather than on…
Q: What are the four most common kinds of database failures that people experience?
A: The answer to the question is given below:
Q: Why is a bridge built in the first place? A device known as a bridge connects two local networks…
A: Introduction of Bridge in Networking: A bridge is a networking device that operates at the data link…
Q: What does the acronym RGB stand for?
A: Red, Green, and Blue are abbreviated as "RGB" for convenience. In computing, the RGB colour scheme…
Q: What does it mean for "Systems Analysis and Design" if we have a cloud that is deployed across…
A: Deploying a cloud system across several locations would require a more complex systems analysis and…
Q: What precisely is an evildirect attack on a wireless network, and how does it function? We ask that…
A: A man-in-the-middle attack known as a "evil twin" occurs when a malicious wireless access point is…
Q: Briefly
A: Introduction: The Agricultural Revolution was a significant period in human history that marked a…
Q: Sort DNS entries based on the kind of records each one contains. Provide instances of each and a…
A:
Q: When starting a new process to execute a command, how does the shell determine whether or not a file…
A: When starting a new process to execute a command, the shell determines whether a file is executable…
Q: What exactly is "spaghetti code," and which instruction from which programming language is utilized…
A: Required: What is spaghetti code, and what style of programming language instruction produces it?…
Q: What does GSM stand for? SIM cards power phones.
A: Under the query, the European Telecommunications Standards Institute (ETSI) produced the Global…
Q: What kind of impact has the algorithm for deleting files had on Symbian, Android, and the iPhone?
A: Symbian was a defunct mobile operating system (OS) and computing platform developed primarily for…
Q: Analyze the differences and similarities between online and batch data entry processes. Included in…
A: The batch input and the online input are the two independents methods, that occur at different times…
Q: What are the benefits of establishing parent-child ties amongst different classes
A: Parent-child ties, or parent-child relationships, refer to a concept in object-oriented programming…
Q: Explain why Al technology must prioritize ethics.
A: AI stands for Artificial Intelligence, which refers to the ability of machines and computers to…
Q: The read position advances in the file as more data is read from it, bringing it closer and closer…
A: In many programming languages and libraries, file handling functions allow you to read data from…
Q: Identifying Web Vulnerabilities Instructions To protect data on the web, e-commerce, social…
A: Protecting online apps is crucial because they store and transmit sensitive information, including…
Q: What exactly is meant by the term "multifactor authentication," and how does the process work? In…
A: Multifactor Authentication
Q: What exactly is an expert system, and how can a data warehouse be of assistance in developing one?
A: An expert system is computer software that uses artificial intelligence (AI) to simulate the…
Q: What exactly does it mean when we talk about the conceptual framework of cybercrime? Provide…
A: Introduction:- Many people, businesses, and governments rely heavily on the Internet to function. It…
Q: Included in this document need to be a description of the five most common network topologies. Which…
A: Network topology is the description of the arrangement of nodes e.g networking switches and routers,…
Q: Where Do Addressing Modes Come From?
A: Addressing modes specify how an instruction represents the effective address of an operand. Another…
Q: There are eight discrete intervals of time that make up a "TDMA frame" in GSM. The 577 microseconds…
A: TDMA:- Each individual can only send during predetermined periods. (Time slots). Different people…
Q: What are the characteristics that are shared by a derived class and the base class from which it was…
A: In object-oriented programming, a derived class is a class that is created by inheriting properties…
Q: What do you think to be the most important factors when designing a physical database architecture?
A: The following are some of the most crucial considerations when designing a database architecture:…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- B: 16 C:101 D: 1024 Plz helpᴜꜱɪɴɢ ᴍᴀᴛʟᴀʙ (ᴍᴀᴛʟᴀʙ ᴏɴʟʏ) ꜱʜᴏᴡ ᴛʜᴇ ᴄᴏᴅᴇ ᴛʜᴀɴᴋꜱ!(ʜᴇɪɢʜᴛ = 701 x 1) (ᴡᴇɪɢʜᴛ=701 x 1) 1.) ᴄʀᴇᴀᴛᴇ ᴀ ʙᴏxᴘʟᴏᴛ ᴏꜰ ᴛʜᴇ ʜᴇɪɢʜᴛ ᴍᴇᴀꜱᴜʀᴇᴍᴇɴᴛꜱ ᴜꜱɪɴɢ ᴛʜᴇ ʙᴏxᴘʟᴏᴛ ꜰᴜɴᴄᴛɪᴏɴ.2.) ᴀᴅᴅ ᴀɴ ᴀᴘᴘʀᴏᴘʀɪᴀᴛᴇ ʟᴀʙᴇʟ ᴛᴏ ᴛʜᴇ ʏ-ᴀxɪꜱ ᴜꜱɪɴɢ ᴛʜᴇ ʏʟᴀʙᴇʟ ꜰᴜɴᴄᴛɪᴏɴ.LA=33bit PA=24bit Page size=2kb System is byte addressable. Find total number of pages and frames.
- 254. In OOOVBOVB, V stands for violation and B stands for a. Bit b. Baud c. Bandwidth d. BipolmConvert 800 J to eV Convert 400 GBq to Ci1011 BASE 2 + 1011 BASE 2 + 1101 BASE 2 + A BASE 16=_______BASE 10 444 BASE 8 + 222 BASE 8 + 101 BASE 8 + F BASE 16 = ________BASE 16 101101 BASE 2 + 1110101 BASE 2 + 11101 BASE 2 + 0101 BASE 2= _______BASE 2
- Discuss the role of integers in error-correcting codes, particularly in error detection and correction mechanisms used in data storage and transmission.Sort the following using the specified algorithm: 3. LSD Radix, MSD Radix 3289, 239, 345, 2345, 1789, 2400, 78, 45, 235asap please Dont use answers from other websites please! Please type your answer not picture Show the MIPS assembly codes to implement each of the following. 1) $t3 = $t0 - $t1 - $t2 2) $t2 = ($t1 + 2) * 3 3) $t1 = -$t2 4) $t0 = $t1 * 3 (use addition) 4) $t1 = $t2 * 3 (use multiplication)
- Data communication systems. The solution time of the problem is 30 minutes. It is desired to be multiplexed in the time plane of 10 channels, each of which is 720 kbps. 3 ASCII characters are taken per unit time from each source. There are also 16-bit sync bits available.Based on this information, how many bits is the frame size?A) 256 B) 46 C) 32 D) 248 E) 242ᴜꜱɪɴɢ ᴍᴀᴛʟᴀʙᴀ.) ᴄʀᴇᴀᴛᴇ ᴀ ᴍᴀᴛʀɪx ɴᴀᴍᴇᴅ ᴍᴀᴛ ᴛʜᴀᴛ ʜᴀꜱ ɴᴜᴍʙᴇʀꜱ 2, 3, ᴀɴᴅ 4 ɪɴ ᴛʜᴇ ꜰɪʀꜱᴛ ʀᴏᴡ ɪɴ ᴛʜᴀᴛ ᴏʀᴅᴇʀ, ᴀɴᴅ ɴᴜᴍʙᴇʀꜱ 9, 7, ᴀɴᴅ 8 ɪɴ ᴛʜᴇ ꜱᴇᴄᴏɴᴅ ʀᴏᴡ ᴀʟꜱᴏ ɪɴ ᴛʜᴀᴛ ᴏʀᴅᴇʀ. ʙʏ ꜱɪᴍᴜʟᴛᴀɴᴇᴏᴜꜱʟʏ ᴍᴏᴅɪꜰʏɪɴɢ ᴍᴜʟᴛɪᴘʟᴇ ᴇʟᴇᴍᴇɴᴛꜱ, ᴀꜱꜱɪɢɴ ᴢᴇʀᴏ ᴠᴀʟᴜᴇꜱ ɪɴ ᴛʜᴇ 2ɴᴅ ᴀɴᴅ 3ʀᴅ ᴄᴏʟᴜᴍɴꜱ ᴜꜱɪɴɢ ᴛʜᴇ ᴢᴇʀᴏꜱ ꜰᴜɴᴄᴛɪᴏɴ. ʙ.) ᴜꜱɪɴɢ ᴛʜᴇ ᴄᴏʟᴏɴ ᴏᴘᴇʀᴀᴛᴏʀ ᴀɴᴅ ᴛʜᴇ ᴛʀᴀɴꜱᴘᴏꜱᴇ ᴏᴘᴇʀᴀᴛᴏʀ, ᴄʀᴇᴀᴛᴇ ᴀ ᴄᴏʟᴜᴍɴ ᴠᴇᴄᴛᴏʀ ᴍʏᴠᴇᴄ ᴛʜᴀᴛ ʜᴀꜱ ᴛʜᴇ ᴠᴀʟᴜᴇꜱ -1 ᴛᴏ 1 ɪɴ 0.5 ꜱᴛᴇᴘꜱ. ᴛʜᴀɴᴋꜱ ɪ ᴡɪʟʟ ɢɪᴠᴇ ᴛʜᴜᴍʙꜱ ᴜᴘ ɪꜰ ᴄᴏʀʀᴇᴄᴛ163. How many states are represented by 1 bit? a. 1 b. 0 c. 3 d. 0 and 1

