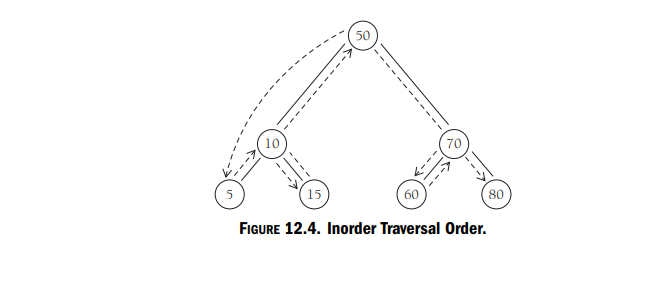
how to Traversing a Binary Search Tree. To demonstrate how this method works, implement a program that inserts a series of numbers into a BST.as given in figure.
Q: What are the types of Multiplexers?
A: There are mainly three types of Multiplexing given below:
Q: Refer to the sample table and data below. mysql> SELECT * FROM zip_code; | zip | city | state | |…
A: Here zip_code have total 6 lines of records. Created one view 'local_zip' with state condition and…
Q: What is Real Time Systems? Explain With Examples.
A: A real-time system is one that is put under real-time conditions, meaning that the system must…
Q: Discuss The Important Features Of Unsigned Numbers.
A:
Q: Hello I'm having some trouble with my python code in making a Caesar's cipher. First, I'm only…
A: Python:- Advantages:- 1. Simple Syntax 2. Easy-to-use Data Structure 3. Learning Ease and Support…
Q: some radio stations refused to play or promote the songs of which of the following acts, because of…
A: To state whether some radio stations refused to play or promote the songs has been provided in the…
Q: Write a Note on Chomsky Hierarchy.
A:
Q: U is currently i
A: Dear Student, The answer to your question is given below -
Q: Program 3 would print out your first name which is passed in as an argument on the command line.…
A: Start. Ask the user to input the name Pass the argument on the command line. Print the name.…
Q: What is Software?
A:
Q: What are pointers and index registers?
A:
Q: Discuss The Alternative Way To Label The K-Map.
A:
Q: Algorithm to Enumerating All Elements Input : a permutation group G; a base and strong generating…
A: given data: Input : a permutation group G; a base and strong generating set for G; the sets U (i) ,…
Q: What exactly is Bayes' Theorem? What role does it play in machine learning?
A: It is represented mathematically as the true positive rate of a condition sample divided by the…
Q: Explain Characteristics Of Embedded System.
A: Explain Characteristics Of Embedded System answer in below step.
Q: (FIB Question) Consider branch that is not taken 100 times and taken once, what is the accuracy of…
A: Your answer is given below.
Q: is the method of preventing the buffer overflow by randomly moving around the address space…
A: The concept here is about detecting and preventing the buffer overflow and identifying the method…
Q: Explain Applications Of Embedded Systems.
A: Introduction of Embedded system : An embedded system is a computer system that works as a part of a…
Q: Explain The Sign Magnitude Numbers.
A: Sign magnitude number: The representation of decimal number in daily business is known as sign…
Q: Describe one possible change to the design, location, programming or planning of the social media…
A: Spotify is a social media platform which provides music streaming services. It is one of the mostly…
Q: Python question, please help with this problem. Please have a docstring and comments throughout the…
A: Please find the answer below :
Q: how to Traversing a Binary Search Tree. To demonstrate how this method works, implement a program…
A: In this question we have to understand and write a code to traverse a BST as Inorder Traversal Order…
Q: Python question please include all steps and screenshot of code. Also please provide a docstring,…
A: The python program is given below:
Q: Which of the following is a false statement regarding the mitigation of the buffer overflow? Choose…
A: The concept here is to identifying false statements regarding the mitigation of buffer overflow. It…
Q: What is Spark support for machine learning?
A: Data scientists are freed from the complications of distributed data with the help of Apache Spark's…
Q: What are the advantages of segmented memory?
A: The following are some of the benefits of memory segmentation in the 8086: Memory segmentation…
Q: Why is it important to have a robust set of metrics for machine learning?
A:
Q: state diagram
A: State diagram: State diagram is also called state machine diagram or state chart diagram. It is a…
Q: Port help client and server to fulfill their task, how it can help the client side. I think it is…
A: A computer network refers to interconnected computing devices that can exchange data and share…
Q: What is simplex and duplex transmission?
A:
Q: Write the features of 8255 A.
A: 8255A The 8255A is a universally useful programmable I/O gadget intended to move the information…
Q: Write code to determine how many different ways there are to represent n cents given an infinite…
A: As a result of the fact that this issue is recursive, let's determine how to compute makeChange(n)…
Q: Discuss The Types Of Digital Systems.
A: Operating System "OS" System software that manages a computer's hardware and software resources and…
Q: Explain What Are Gated Latches.
A:
Q: Traversing a binary search tree: preorder, inorder, posto 20 610 12 22 30 14 (3 7
A: Inorder root visit nods in the following order 3,6,7,2,8,10,11,14,12,15,22,27,30,20 Preorder…
Q: IN JAVA Write a function that takes in user input as a string. For all characters which are numeric,…
A: Introduction A class called Scanner may be found in the java.util package and is used to get input…
Q: Explain Partial Recursive Function.
A: If a partial function is created through recursion, composition, or minimization on the initial…
Q: Construct a predictive-parsing table for this grammar. 3.18. A grammar for regular expressions is…
A: Solution:-
Q: 18. What is wrong with the following query? SELECT FROM LEFT JOIN ON Customers.CustomerID =…
A: As per Bartleby's rules, we can answer 1 question at a time As 18, 19 and 20 are separate questions,…
Q: Discuss The Types Of Digital Systems.
A: Operating system. The "OS" stands for "operating system," which refers to the software that controls…
Q: 3. Which of the following network types are supported by IS-IS? A. Broadcast B. P2P OC. NBMA D. P2MP
A: Introduction: The IS-IS (Intermediate System - Intermediate System) protocol is an Interior Gateway…
Q: Answer all of the following questions as they are connected altogether: 3. How can we access the…
A: How can we access the class members ? ---> Let's understand this concept one by one . When we…
Q: ch one of the following languages is vulnerable to buffer overflow? Choose an answer A
A: Solution - In the given question, we have to tell which language is vulnerable to buffer overflow…
Q: Create a Function procedure called calculate cost that calculate the cost of an item and return that…
A: Dear student, the answer is provided below.
Q: b.Consider the following two assignments: my_module = ['Part', '1', 'Block', '2', 'TMA02']…
A: Python: Python is an object-oriented and structured programming language. It multiparadigm language.…
Q: From the social media platform, Spotify, who seems to benefit from this technology the most?
A: Technology:- Technology is the systematic and repeatable application of knowledge to the…
Q: Python question please include all steps and screenshot of code. Also please provide a docstring,…
A: ALGORITHM : 1. Create an empty dictionary2. Open the file and read each line3. Remove the newline…
Q: How to Retrieving the Keys and the Values Separately From a Hash Table?
A: As no particular language is mentioned so I used java. Code along with output and code screenshot is…
Q: Explain PTR & GROUP
A: Computers can communicate thanks to DNS's PTR resource record. PTR translates IP addresses to domain…
Q: What is Real Time Systems? Explain With Examples.
A: A real-time system is one that is put under real-time conditions, meaning that the system must…
how to Traversing a Binary Search Tree.
To demonstrate how this method works, implement a program that inserts a series of numbers into a BST.as given in figure.
Step by step
Solved in 3 steps with 1 images

- IN C LANGUAGE When inserting a node into a linked list, where (in memory) will that node be placed if there is no overflow? A) The location of the AVAIL pointer B) The next contiguous spot of memory from the last node C) The very end of the contiguous memory block D) A randomized memory locationint F(node<int>&p){int c=0; while(p!=0){p=p->next; c++; } return c;} This function is a. return the number of items in the linked list b. return the number of items in a linked list and destroy the linked list c. None of these d. destroy the list and free all allocated nodesA linked list is frequently used to create a collection of variously sized objects. A linked list's elements each have their own memory block and a reference to the following block. A linear collection is more effective than a linked list. What causes that, exactly?
- 1.3.14 Create a class called ResizingArrayQueueOfStrings that implements the queue abstraction using a fixed-size array. Then, as an extension, utilise array resizing in your implementation to get rid of the size restriction. 1.3.15 If standard input contains k or more strings, create a Queue client that accepts the command-line argument k and outputs the kth string from the last string located there.Assume a linked list contains following integers: 2, 2, 4, 5, 8, 3, 15 and the pointer head is pointing to the first node of the list. What will be the value of variable a after the following statements are executed: Node<int> *curNode=head; int a=0; Node<int> *aNode; while(curNode->getItem()<7){ aNode=curNode; curNode=curNode->getNext(); } a=aNode->getItem(); A. 5 B.8 C.0 D.7Assume a linked list contains following integers: 7, 2, 9, 5, 8, 3, 15 and the pointer head is pointing to the first node of the list. What will be the value of variable a after the following statements are executed: Node<int> *curNode=head; Node<int> *aNode; int s; while(curNode!=NULL){ { aNode=curNode; curNode=curNode->getNext(); } s=aNode->getItem(); A. 15 B. 3 C. 7 D. 2
- /*** CircularArrayQueue represents an array implementation of a queue in * which the indexes for the front and rear of the queue circle back to 0* when they reach the end of the array.* * @author ITSC2214* @version 4.0*/public class CircularArrayQueue<T> implements QueueADT<T>{private final static int DEFAULT_CAPACITY = 100;private int front, rear, count;private T[] queue; /*** Creates an empty queue using the specified capacity.* @param initialCapacity the initial size of the circular array queue*/public CircularArrayQueue (int initialCapacity){front = rear = count = 0;queue = (T[]) (new Object[initialCapacity]);}/*** Creates an empty queue using the default capacity.*/public CircularArrayQueue(){this(DEFAULT_CAPACITY);} /*** Adds the specified element to the rear of this queue, expanding* the capacity of the queue array if necessary.* @param element the element to add to the rear of the queue*/public void enqueue(T element){if (size() == queue.length)…If the following is a circular array based queue of size 99 43 54 76 93 77 18 If rear is at index 1 and front is at index 6, what is the size of the queue?Find the in order traversal, pre order traversal, and post order traversal USING this B T S code. -------------- class BinarySearchTreeNode: def __init__(self, data): self.data = data self.left = None self.right = None def add_child(self, data): if data == self.data: return # node already exist if data < self.data: if self.left: self.left.add_child(data) else: self.left = BinarySearchTreeNode(data) else: if self.right: self.right.add_child(data) else: self.right = BinarySearchTreeNode(data) # function to build the BST def build_tree(elements): print("INPUT NUMBERS:", elements) root = BinarySearchTreeNode(elements[0]) for i in range(1, len(elements)): root.add_child(elements[i]) return root # function to find maximum value from the tree def getMaxFromBST(root): # storing value in temporary variable temp = root # looping over the right subtree while(temp.right): temp = temp.right # returning the rightmost leaf data return temp.data # function to find minimum value from the tree…
- Suppose you are trapped on a desert island with nothing but a priority queue, and you need to implement a stack. Complete the following class that stores pairs (count, element) where the count is incremented with each insertion. Recall that make_pair(count, element) yields a pair object, and that p.second yields the second component of a pair p. The pair class defines an operator< that compares pairs by their first component, and uses the second component only to break ties.Code: #include <iostream>#include <queue>#include <string>#include <utility> using namespace std; class Stack{public: Stack(); string top(); void pop(); void push(string element);private: int count; priority_queue<pair<int, string>> pqueue;}; Stack::Stack(){ /* Your code goes here */} string Stack::top(){ /* Your code goes here */} void Stack::pop(){ /* Your code goes here */} void Stack::push(string element){ /* Your code goes here */} int main(){ Stack…Assume a linked list contains following integers: 5, 2, 4, 6, 8, 3, 15 and the pointer head is pointing to the first node of the list. What will be the value of variable a after the following statements are executed: Node<int> *curNode=head; int a=0; curNode->setNext(NULL); while(curNode!=NULL){ a+=curNode->getItem(); curNode=curNode->getNext(); } A.5 B.2 C.43 D.38Use the standard linked list below to answer True/False statements 9-10: 9) The “head” pointer of this list is pointing to Node 4 10) If we called “insert(5)”, the new node’s “next” pointer will point to Node 8

