How would I create this function using C?
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter7: Arrays
Section7.1: One-dimensional Arrays
Problem 4E: (Practice) a. Write output statements using cout that can be used to display values from the first,...
Related questions
Question
How would I create this function using C?
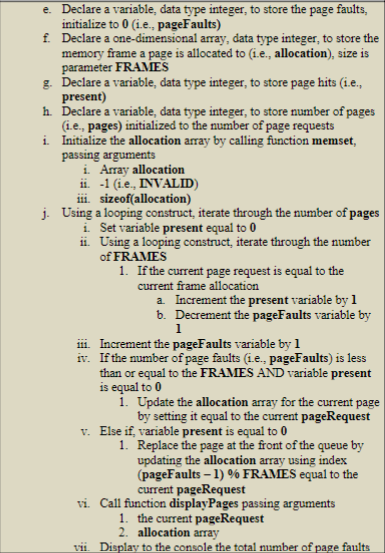
Transcribed Image Text:e. Declare a variable, data type integer, to store the page faults,
initialize to 0 (i.e., pageFaults)
f.
Declare a one-dimensional array, data type integer, to store the
memory frame a page is allocated to (i.e., allocation), size is
parameter FRAMES
g. Declare a variable, data type integer, to store page hits (i.e.,
present)
h. Declare a variable, data type integer, to store number of pages
(i.e., pages) initialized to the number of page requests
Initialize the allocation array by calling function memset,
passing arguments
i.
i. Array allocation
ii. -1 (i.e., INVALID)
iii. sizeof(allocation)
j. Using a looping construct, iterate through the number of pages
i. Set variable present equal to 0
ii. Using a looping construct, iterate through the number
of FRAMES
1. If the current page request is equal to the
current frame allocation
a. Increment the present variable by 1
b. Decrement the pageFaults variable by
1
iii. Increment the pageFaults variable by 1
iv.
If the number of page faults (i.e., pageFaults) is less
than or equal to the FRAMES AND variable present
is equal to 0
1. Update the allocation array for the current page
by setting it equal to the current pageRequest
v. Else if, variable present is equal to 0
1. Replace the page at the front of the queue by
updating the allocation array using index
(pageFaults - 1) % FRAMES equal to the
current pageRequest
vi. Call function displayPages passing arguments
1. the current pageRequest
2. allocation array
vii. Display to the console the total number of page faults
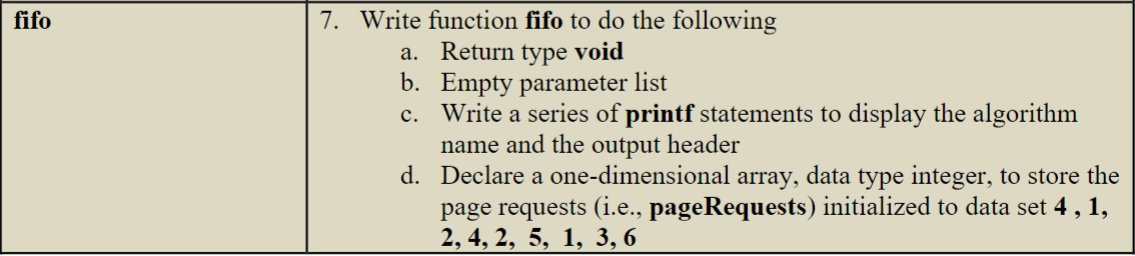
Transcribed Image Text:fifo
7. Write function fifo to do the following
a. Return type void
b.
c.
d.
Empty parameter list
Write a series of printf statements to display the algorithm
name and the output header
Declare a one-dimensional array, data type integer, to store the
page requests (i.e., pageRequests) initialized to data set 4, 1,
2, 4, 2, 5, 1, 3, 6
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning