how you could implement a queue's enqueue and dequeue operations
Q: Write a function square in RISC-V that takes in an integer n ad returns its square. If n is not posi...
A: a function square in RISC-V that takes in an integer n ad returns its square. If n is not positive, ...
Q: What malware traits differentiate a virus programme?
A: Introduction: A malware program is software that is used to obtain access to a victim's computer sys...
Q: WHAT EXACTLY IS A BYZANTINE GENERALS PROBLEM IN DIGITAL CASH TRANSACTIONS
A: Byzantine Generals Problem can be described as the trouble of decentralized frameworks having settl...
Q: What are the advantages of ICT? What is the signifincance of ICT?
A: ICT: ICT stands for Information and Communication Technologies ICT refers to technologies that provi...
Q: (Memory Interface) A read-only memory and a microprocessor need to communicate asynchronously. The p...
A: Given The answer is given below.
Q: Construct an E-R diagram for the following hospital: In this hospital, we have many patients (chara...
A: The entities are have are DoctorPatientTestThe relationship between doctor and patient is one to man...
Q: How can I check whether the given array is mirror inverse or not The array should be taken from user...
A: Required:- How can I check whether the given array is mirror inverse or not The array should be take...
Q: Custom Input Output Tests Executions mains 2. 2nd Smallest by Jemar Jude Maranga Enter cus ton input...
A: As given, we need to write a C program that prints the second smallest digit in an array. And the ma...
Q: A trigger's execution might result in the execution of another action. The depth of nesting in most ...
A: A trigger's execution might result in the execution of another action. The depth of nesting in most...
Q: Explain briefly what Software Outsourcing and Cloud Services are for.
A: Introduction: Cloud computing is utilised by enterprises of all sizes, kinds, and sectors for a vari...
Q: Do you know what the technical term is for robotic optical disk library devices?
A: First let's understand what is robotic optical disk library . As the name suggest we can easily ide...
Q: unique answer only
A: LOGIC DIAGRAM: Given the associative law as x.(y.z) = (x.y).z. Now, the following is the correspond...
Q: Modify the below existing codes to print the output in Python. Explain the changes made to the code...
A: Below i have given the code:
Q: Why are we talking about data structures and algorithms together? What is the relationship between t...
A: Introduction: A computer can solve a problem using an algorithm, which is a well-defined technique. ...
Q: Write a C++ program that allows a cosmetic company to keep track of six different products: lipstick...
A: Use a loop to check the validation of input of each sale in the array and have two integers to track...
Q: Explain in detail what penetration testing is and state the primary outcome from it. Briefly describ...
A: A penetration test, also known as a pen test, is an intelligence gathering and vulnerability assessm...
Q: int foo1(int n) { int i, sum = 0; if (n==1) { return 1; } for(i=1; i<=n; i*=3) { sum += i; %3D }
A: Big Oh notations explains the worst-case running time of an algorithm,in simple words. It is the upp...
Q: As you have been introduced to Python and programming over the past few weeks, what have you found m...
A: Below is the complete explanation about the given python questions in detail. Below contains the inf...
Q: What are the benefits and drawbacks of using a hosted software solution to "test drive" a potential ...
A: benefits: the reduced total cost of ownership, lower risk of implementation, device maintenance out...
Q: In this section, we will look at the function that wireless networks play in developing countries. W...
A: -The wireless network allows the average man in developing countries to connect to the rest of the g...
Q: Name two well-known data transfer protocols supported by the Transport Layer. Give a brief descri...
A: The two well-known data transfer protocols supported by the Transport Layer are : TCP , UDP TCP :It ...
Q: Describe FOUR(4) possible countermeasures against network scanning.
A: At border routers and firewalls, filter inbound ICMP message types. To effectively map your network,...
Q: Write short notes on Graphical User Interface (GUI) and its importance in developing business applic...
A: Graphical user interface:- It can be considered as a method that includes the use of symbols, desig...
Q: Draw the Logic Diagram, Truth Table and execute the following Boolean Laws in the proteus software a...
A: Given expression: x.(y.z)=(x.y).z To find: Truth table Logic diagram Verify
Q: . Following is the static list of data you need to maintain in the application 1/ Static list of t...
A: The API has been created there but the function is empty you can use that. to run the project do the...
Q: 6.19 LAB: Driving costs - functions Write a function driving_cost() with input parameters miles_per_...
A: Functions: Functions are subprograms that compute a value or perform a task. Functions decrease the ...
Q: Write a menu driven program with the options below: Choose one of the following options: 1. Input a ...
A: Let's see the solution in the next steps
Q: Why should the organization embrace Agile Methodology?
A: Step 1) Agile methodology : The term agile means the ability of response to changes from requiremen...
Q: There are many different ways to "data mine," but what is it called? How does data mining help compa...
A: Introduction: Data mining is the process of analyzing massive quantities of observational data to un...
Q: Query Board Python or Java(Preferred Python please) Thank you! Programming challenge de...
A: Matrix: A matrix could be a assortment of numbers organized in rows and columns.The elements of the...
Q: For the instruction being executed: add $s1, $s2, $t0 use the following delays for each block/action...
A: Explanation: First, read the registers. and, Instruction access memory. and, Decode and register fil...
Q: why it is necessary for solid-state drives. According to our previous discussion, wearleveling is cr...
A: given - Explain what wear leveling is and why it is necessary for solid-state drives. According to o...
Q: Different security management techniques, as well as the theories that underpin them, should be exte...
A: Some Security management techniques are - Information Security Management - It generally consists o...
Q: convert each NFSA from problem 1 into a DFSA using the subset construction studied in class.
A: ANSWER:-
Q: ar a grinding noise as the printer attempts to move the carriage, what should you do
A: Printer cart is a combination of holding ink cartridges and slide back and forth to transfer ink t...
Q: Disjoint and overlapping constraints are two different types of rules.
A: The disjoint rule forces subclasses to have disjoint sets of entities. The overlap rule forces a sub...
Q: Write a program to convert a US Customary System length in miles, yards, feet and inches to a Metric...
A: Logic:- read miles, yards, feet and inches. Use formula to calculate total_inches,total_meters and...
Q: Explain the difference between the while loop and the for loop using an example C++ application.
A: As per the requirement explanations is done. Algorithm: Step 1: Write the main method Step 2: Using ...
Q: Imagine that you are putting in place for your university's first time a new room reservation system...
A: Introduction: The availability of infrastructure, particularly buildings, has a significant impact o...
Q: hout internet ?
A: given - How does censorship grow and thrives in a place without internet ?
Q: How blockchain could allow transferability?
A: Introduction: Blockchain is a safe technology that allows you to send and receive digital data via a...
Q: Write a program to convert à US length in miles, yards, feet and inches to a Metric System length in...
A: I give the code in Python along with output and code screenshot
Q: blic int merge(BST nbt) { /*See BST.java for method specification */ // Hint: traverse bst using pre...
A: public class BSTImpl implements BST { private Node root; private int size; public BSTI...
Q: ment is a term
A: given - The prototype technique of software development is a term that means different things to dif...
Q: tly is a Compiler?
A: given - What exactly is a Compiler?
Q: x0=3001. (iii)Comment on the sequence generat
A: Class Publication is created with two data members, ISBN of type String and title of type double, bo...
Q: Explanation of the several forms of data protection available in MS-Excel. Give examples to substant...
A: Intro The following are the many methods of data protection that MS-Excel offers: The explanation a...
Q: What is zoned-bit recording, and how does it work
A: Zone bit recording (ZBR) is a mechanism in use by disc drives to optimise the tracks for enhanced da...
Q: 10. Determine whether the following argument is valid or invalid. Include a truth table and a few wo...
A: Given: If 12 divides 709,438 then 3 divides 709,438. If the sum of the digits of 709,438 is divisibl...
Q: Produce a context-free grammar (CFG) for each of the following lan- guages, assuming Σ = {0,1}: (a) ...
A: S → 0X1 | 1X0 X → 0X | 1X | ε Note, the from the start variable S, we make sure that if a string sta...
Step by step
Solved in 2 steps

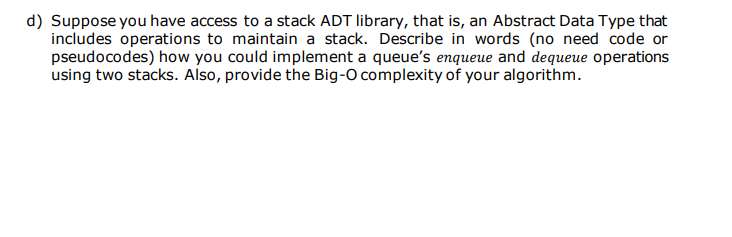
- Suppose you have access to a stack ADT library, that is, an Abstract Data Type that includes operations to maintain a stack. Describe in words (no need code or pseudocodes) how you could implement a queue's enqueue and dequeue operations using two stacks. Also, provide the Big-O complexity of your algorithm.Explain thoroughly the answers to the following questions: When is it appropriate to implement stack or queue using singly linked list, and when is it appropriate to implement them using doubly linked list? A queue can be implemented using stack. Explain how.We are given a Queue data structure that supports standard operations like enqueue()and dequeue(). We need to implement a Stack data structure using only instances ofQueue and queue operations allowed on the instances. Hint: A stack can be implemented using two queues but we dont allow to use build in function , make 3 files .h,.h.cpp like Queue.h , MyQueue.h ( in with all function performe ) and the last one main.cpp
- (2) Answer the following questions concerning lists, stacks, and queues Please be thorough with explanatio! (d) Suppose you are implementing a list of stacks. Let's say you decide to implement both the general list (the list of stacks) and each individual stack using a double linked list. Assume that there are currently N stacks in the list, and each stack has a maximum of K items, where N and K are both large. You are going to iterate through the general list and apply a single operation to each stack as you encounter it. Now answer the following four questions, using big-Theta notation: What is the average-case time complexity of pushing one additional item into each stack? What is the worst-case time complexity of pushing one additional item into each stack? What is the average-case time complexity of popping one item from each stack? What is the worst-case time complexity of popping one additional item from each stack? (For pops, if the stack is empty, you can assume that the pop…(2) Answer the following questions concerning lists, stacks, and queues: Please be thorough with explanation! (b) Now consider implementing a stack as a class that relies on a vector, keeping track of the current size and capacity of the vector in the main object. You consider two possibilities. The first is to push (insert) to the beginning and pop (remove) from the beginning of the vector. The second is to push to the end and pop from the end of the vector. (Either way, if the vector is full and a push is applied, the vector will be resized to double its current capacity.) Is one of these possibilities better than the other? Briefly explain your answer.Q3:- Consider an empty stack STK of size 5 (array-based implementation). What will be the output after applying the following stack operations? Draw a diagram in support of your answer. How many elements are there in the stack at the end of the processing? POP(), PUSH(25), PUSH(20), POP(), POP(), PUSH(45), PUSH(15), POP(), PUSH(30), PUSH(17), PUSH(33), PUSH(24), PUSH(54), POP(), PUSH(99)
- S and Q are integer stacks and priority queues, respectively. C mod 3 is the priority of an element C joining the priority queue Q. In other words, the elements' priority numbers are either 0 or 1 or 2. What is the output of the following code if A, B, and C are integer variables? However, the queue procedures have been modified to work on a priority queue. 1.A = 102.B = 113.C = A+B4.while (C < 110) do5. if (C mod 3) = 0 then PUSH (S,C)6. else ENQUEUE (Q,C)7. A = B8. B = C9. C = A + B10.end11.while not EMPTY_STACK (S) do12. POP (S,C)13. PRINT (C)14.end15.while not EMPTY_QUEUE (Q) do16. DEQUEUE (Q, C)17. PRINT (C)18.end10.12 It is possible for one linear structure to be more general than another.(a) Can a Queue be implemented using a Stack? What is the level of complexity of each Queue operation? (b) Can a Stack be implemented using a Queue? What are the various Stack techniques' complexities? 10.13 Explain how we could efficiently build a Queue as a pair of Stacks, known as a "stack pair." (Hint: Consider one of the stacks to be the head of the queue and the other to be the tail.)1. consider an array based queue implementation. suppose we wish to use an extra bit in the queue records to indicate whether a queue is empty. a. Modify the declarationsand operations for a circular queue to accomodate this feature. b. Would you see the change to be worthwide.
- Two major issues of simple Queue data structure are 1) Memory wastage, and 2) limitation of using the same array indices again after the queue elements are deleted. How can you solve these problems? Briefly explain your proposed solutions.What changes you need to make in the following enqueue() function, so that the above-mentioned problems will not happen again.Perform this task on paper, take a clear picture of solution and paste it in answer section. void enqueue(int val) { if(isFull()) cout<<”Queue is Full”<<endl; else myArray[++rear] = val; }Short answer: Answer the following in your own words: 1) Your friend says they implemented a stack as a linked list with reference pointers to both a head and the tail node (i.e. they implemented a stack as a double endedlinked list). They said this significantly improved the performance for all functions (push, pop, search, and update). Are they correct? Why or why not?10.12 There is a possibility that one linear structure is more universal than another.(a) Can a Stack be used to implement a Queue? What is the degree of difficulty of each Queue operation? (b) Can a Queue be used to implement a Stack? What are the complexity of the various Stack techniques? 10.13 Describe how we may efficiently construct a Queue as a pair of Stacks, referred to as a "stack pair." (Hint: Think of one stack as the head of the queue and the other as the tail.) 10.12 There is a possibility that one linear structure is more universal than another.(a) Can a Stack be used to implement a Queue? What is the degree of difficulty of each Queue operation? (b) Can a Queue be used to implement a Stack? What are the complexity of the various Stack techniques? 10.13 Describe how we may efficiently construct a Queue as a pair of Stacks, referred to as a "stack pair." (Hint: Think of one stack as the head of the queue and the other as the tail.) 10.12 There is a possibility that…

