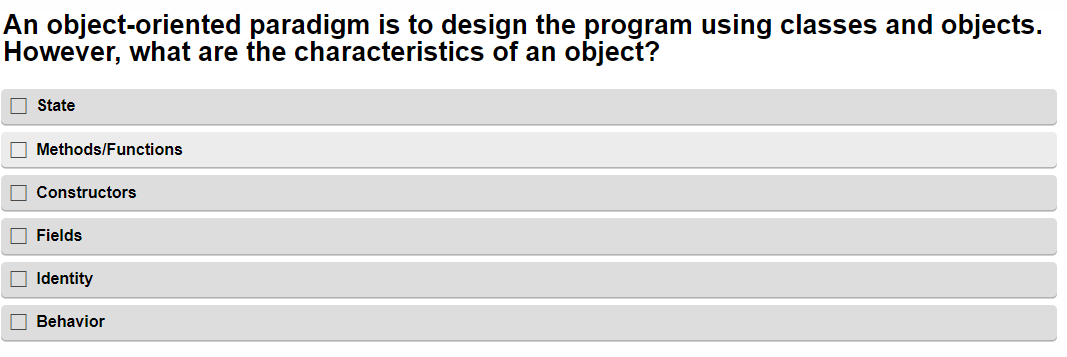
However, what are the characteristics of an object? State Methods/Functions Constructors Fields Identity Behavior
Q: Lambda expressions are used primarily to define inline implementatic of a functional interface.…
A: We have given two statements , we have asked which of them is/are true regarding Java.
Q: What are the requirements for administering a server remotely?
A: INTRODUCTION: IT administrators may control Windows Server roles and features from a Windows 10 PC…
Q: 1. ArrayList class extends AbstractList class and implements the List interface II. ArrayList…
A: The above question is solved in step 2:-
Q: Compare three-tier vs two-tier application designs. Compare. Which is better for web app…
A: Given: The distinction a between two-tier and three-tier application architecture is sought in this…
Q: Take into consideration the advantages of using an agile approach to the creation of software in…
A: Given: Let's begin with a definition of the software engineering. Two terms make up the phrase…
Q: 38, Where does a neural network's "knowledge" lie? In its pattern of weights and thresholds…
A: The problem is based on the basics of neural networks in deep learning.
Q: What exactly is meant by the term "dynamic memory allocation," and how does one go about…
A: Work on dynamic memory allocation - When an active application asks that the OS, or operating…
Q: Who are the persons engaged in the Waterfall Model's phases
A: Introduction Waterfall model is software development model which contains linear sequential phases.…
Q: Before you utilize a file extension, you should make sure you understand what it is and what role it…
A: Definition: A file extension (or simply "extension") is a suffix that is placed to the end of a…
Q: Allow for discussion regarding the usage of tablet computers and smartphones in the workplace.
A: Intro Here are some examples of corporate tablet and smartphone use: Access to Information…
Q: Explain the significance of Network Address Translation (NAT) for IPv4 (at least two reasons).
A: Introduction Computer network: A group of computer systems or computer nodes that are connected to…
Q: What exactly is artificial intelligence (AI)? With an example, explain how the control system plays…
A: Artificial intelligence is a wide-ranging branch of computer science concerned with building smart…
Q: Comparison should be made between the routing protocols DSDV, AODV, and DSR with regard to the…
A: Given: Contrast the routing protocols DSDV, AODV, and DSR . Response: DSDV stands for Distance…
Q: Although wired and wireless networks each have their own set of benefits and drawbacks, wireless…
A: Wireless Networks: A network comprised of wired connections. A wired network connects computers via…
Q: # 1) 41, 65, 20, 11, 29, 50, 91, 32, 72, 99 #3) 29 #4) 32 #6) 67, 75 #7) 20 #9) 50
A: Note: This is a multiple-question-based problem. As per company guidelines, only the first question…
Q: 1-Write a programto set (bit- 15) and clear (bit-0) thatstored in memory locations form (01F0)Hto…
A: #Code org 100h.DATANUM DW 1111H,2222H,3333H,4444H,5555H,6666H,7777H,8888H.CODEMOV AX,@DATAMOV…
Q: Provide an explanation to management on what a database is and how it operates.
A: A database management system operates like this in a nutshell: It organizes database files and gives…
Q: Why are logic bombs such a common type of assault among dissatisfied or former employees? What can…
A: Introduction: Logic bombs are complex cyberattacks that are difficult to detect, but they can do…
Q: As a result of advances in technology, the vast majority of today's home appliances can communicate…
A: Introduction: Wireless data transfers are used to connect network nodes in Wi-Fi networks. Wireless…
Q: As a consequence of this, users may choose to enter data through the command line rather using the…
A: Users are able to become proficient with the use of a graphical user interface (GUI) far more…
Q: When explaining dynamic programming, utilize real-world examples.
A: Given: In the not-too-distant future, drivers of electric cars will be able to charge their…
Q: What options are available to improve data privacy?
A: Intro What methods are there for improving data privacy? in the following section, we will be…
Q: It is essential to have a solid understanding of the many challenges that are faced by embedded…
A: It is essential to have a solid understanding of the many challenges that are faced by embedded…
Q: What can we learn from cybercrime in terms of advice and conclusions?
A: Introduction: It is a crime that occurs predominantly or exclusively online that is referred to as…
Q: As a helpful amenity for customers making electronic payments, certain credit card issuers provide…
A: Given: Every time a user makes an online purchase, he enters his PIN and then enters the one-time…
Q: What types of usability testing methodologies, including cognitive walkthroughs, are available for…
A: Introduction: Candidate Usability analysis methods, Usability analysis methods will provide input on…
Q: Please explain what is unstructured data and give an example.
A: Big Data is a collection of data that is huge in volume, growing exponentially with time. This…
Q: Why isn't "store-and-forward network" technology used in general communications any longer? Also,…
A: Solution: Store and forward packet-switching ensure high-quality data packet delivery. Because…
Q: F A B D E Enter a valid depth-first search traversal when D is the starting vertex. Ex: A, B, C, D,…
A: Here in this question we have given a graph and we have asked to find a valid DFS sequence for this.
Q: Composer is used to transform higher-level programs into ones with a lesser degree of complexity.…
A: Compilers transform sophisticated programs into machine code. So, it's crucial beyond CPU and…
Q: What do you feel are the most significant elements to consider while creating a physical database?
A: Intro At the point when you are certain about joining your different information sources and taking…
Q: What is the purpose of an abstract class
A: Introduction Abstract class: The abstract keyword must be used to turn any class into an…
Q: Make a distinction between the general and the specialized types of requirements, both of which…
A: Given that : The following is a list of the several categories of needs that have been outlined for…
Q: Is anything wrong with the following code? void func() { int number1 = 100, number2 = 3; float…
A: Given: Is there anything wrong with this code?
Q: What kind of a part does linear programming play in the process of making financial decisions?
A: When a linear function is exposed to several restrictions, linear programming, a modeling technique,…
Q: What do you think are the most significant factors to take into account when selecting an operating…
A: Given: Things to take into account while picking an operating systemA high degree of dependability…
Q: class Main { public static void main (String[] args) { Test sample = new Test("Finals", 87);
A: Data types in programming plays very important roles to initialize and provide appropriate space in…
Q: What exactly does "personal information protection" imply? What are the top five methods for…
A: 1. Protection of personal information: The Protection of Personal Information Act (POPIA) is South…
Q: What exactly do you mean when you talk about vulnerabilities that are header-based? Which three…
A: Given: When launching high-impact, routing-based SSRF assaults, it is occasionally also acceptable…
Q: Problem 3 Using the in the following table, use the gradient descent algorithm to learn the…
A: We have trained the gradient descent algorithm to learn the parameter weight and biases. And we need…
Q: What are some of the benefits of cloud computing? What are the risks and challenges associated with…
A: Note: This is a multipart-based problem. As per company guidelines, only the first three parts are…
Q: developing a system, employing agile methodologies may have both positive and negative effects.…
A: In software development, agile (sometimes written Agile) rehearses include necessities disclosure…
Q: The use of several threads in place of a large number of independent background processes is…
A: The term "multithreading" refers to a technique in computer programming that enables numerous…
Q: Can dynamic programming build interconnected judgments? Now what?
A: Dynamic programming: Dynamic programming is used to solve issues that may be subdivided into smaller…
Q: Solve the given problem. Represent your solution by pseudocode and flowchart. Implement your…
A: START Initialise discount Input amount, cardholder If cardholder == 'n' discount = 0 Else If…
Q: d to UDP, is the
A: I by and large, applications like Voice over Internet Protocol (VoIP), online gaming, and live sound…
Q: Which of the following r-values indicates the weakest relationship between two variables? + 0.45 -…
A: Two variables are said to be strongly related if change in one effects the others. For strong…
Q: As a convenience, several credit card companies give one-time-use credit card numbers for electronic…
A: Intro Every time a user makes an online purchase, he enters his PIN and then the one-time code that…
Q: What are some of the challenges that come with building software for embedded devices?
A: Develop program for embedded systems: Basic embedded system software, such as C, C++, ADA, and…
Q: -5 then the matrix A is 3 -3 1 -1 .a a symmetric matrix .b a Hermetian matrix .c an orthogonal…
A: The above matrix is a skew- symmetric matrix.
Step by step
Solved in 2 steps

- Encapsulation and polymorphism, both object-oriented ideas, are linked with object models.Encapsulation in the context of an object-oriented method refers to what?How would one go about utilizing an object initializer in order to make an instance of the class Book and populate it with default values for its properties? Regarding the programming language known as C#
- Object-oriented ideas such as encapsulation and polymorphism are linked with object models.Object-oriented programming relies heavily on encapsulation. When a developer use an encapsulated property, they are unaware of its implementation. He or she is solely familiar with the public setter and getter methods. What facts does the Bible encapsulate or conceal? Give one or more examples of encapsulation or information concealment.Encapsulation, polymorphism, and object models are all linked in object-oriented programming.
- When it comes to object-oriented programming, one question that often comes up is why it is necessary to put in more effort and code in order to prevent having classes that are connected together unnecessarily. What would you say are the three most essential reasons for taking the position that you do?subject: object-oriented programming in your library there are two types of books. one category is literature books and the second category is generals. litrature books have the authorID, authorname literature theme language, publisher, volumn,, yearofpubication, journal have attributes volumn, issue, publisher,yearofpublication,journalID, technical sponser. design a parent class books extend two classes literaturebooks and journel from parent class make constructor , setter, and getterA essential but insufficient characteristic of object-oriented programming is encapsulation. A programmer is ignorant of the implementation specifics when they utilize an encapsulated property. Only the public setter and getter methods are known to him or her. What facts is the Bible encapsulating or hiding? Give one or more instances of information being encapsulated or hidden. 300 to 350 words maximum. APA style must be used for all citations. A letter of reference from a university is required.
- There must be classes and objects.Attributes are of type publicUse one or two constructors.Write a program in Object Oriented Java language that adds and subtracts two polynomials of the form ax2 +bx+cObject-oriented programming requires, but does not require, encapsulation. A programmer is ignorant of the implementation specifics when they utilize an encapsulated property. He or she only knows the public setter and getter methods. What facts does the Bible encapsulate or conceal? Give one or more instances of information encapsulation or hiding. From 300 to 350 words. Citations must be in APA format. An academic institution's recommendation letter is required.an object-oriented program that runs and generates actual output. It features a class called BankAccount that models a checking account at a bank. The programcreates an account with an opening balance, displays the balance, makes a deposit and a withdrawal, and then displays the new balance.



