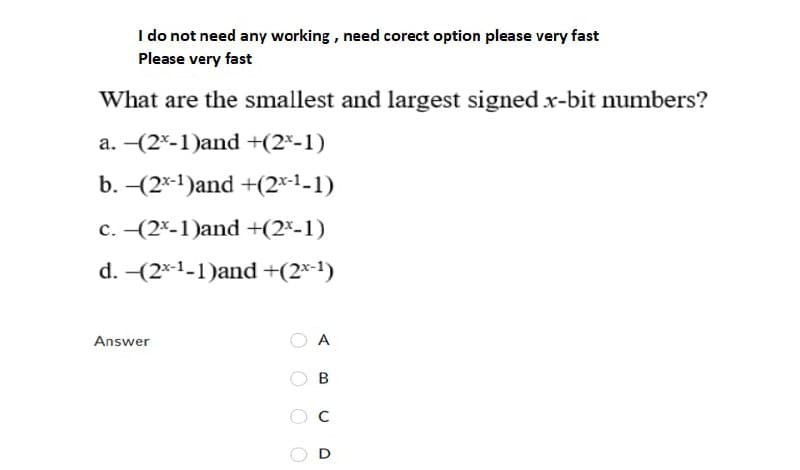
I do not need any working , need corect option please very fast Please very fast What are the smallest and largest signed x-bit numbers? a. (2*-1)and +(2*-1) b. -(2*-1)and +(2*-1-1) c. -(2*-1)and +(2*-1) d. -(2*-1-1)and +(2×-1) Answer A B
Q: Describe how HDFS and MapReduce compliment one other.
A: Hadoop Distributed File System (HDFS): Hadoop Distributed File System (HDFS) is the primary data s...
Q: 23 ___ 2 == 5 Which operator would make this expression true?
A: 23 can be written as 00010111. The Right Shift Operator shifts the bits of the number towards right ...
Q: Create a Personal Information table with the following field's First name, Gender, Nationality, add...
A: NOTE : AS PER BARTLEBY GUIDELINES WE ARE ALLOWED TO ANSWER ONLY THE FIRST 3 QUESTIONS OF ANY MULTIPL...
Q: Please perform test cases according to the intructions provided. Box code is given below. Question i...
A: java is a compiled language that follows the concept of oops to make projects. It is used to build v...
Q: List five Internet-based services that are not now accessible but that you believe will become avail...
A: The answer is given below:
Q: Emergency stop. /usr/local/texlive/2021/texmf-dist/tex/latex/fontspec/fontspec.sty, 45 l.45 \ms...
A: let us see the answer:- This indicates your project makes use of the fontspec package, which can o...
Q: a.) Explain three reasons why modern operating systems are more robust and efficient than earlier on...
A: Here is the detailed explanation of the solution
Q: 1. The following is a (silly) decision structure: a, b, c = input('Enter three numbers: ') if a > b:...
A: First note that there are some errors in the program -- clearly the author wrote this for python 2 a...
Q: What exactly is a Linux runlevel for a particular service or application? What command allows you to...
A: Introduction: A runlevel is a mode of operation in machine operating systems that implements Unix Sy...
Q: Find sop (sum of Poreluct) of this the follow ing Expresion. F(xY,z)= Em[012, 3,5,6)
A:
Q: There should be a discussion on each of the Interrupt classes that are offered. Determine where the ...
A: Introduction: When a cycle or event requires immediate attention, interrupt is a signal emitted by e...
Q: Discuss the purpose and importance of mathematical writing.
A: Perusing, composing, and arithmetic are, or ought to be, indivisible. Involved math can invigorate i...
Q: 2. Given the following format for the "Date" Bits 9-15 year Bits 5-8 month Bits 0-4 day Set the year...
A: Find the answer with calculation given as below :
Q: What exactly is the stated mission of the SANS organization? Specifically, what role does it play in...
A: Introduction: The SANS Institute is a for-profit organization that provides data security and intern...
Q: One of the benefits of a Hadoop installation is the high level of compute redundancy. Why is this so...
A: Introduction: One of the benefits of a Hadoop installation is the high level of compute redundancy. ...
Q: when a software application invokes a virtual function using base class pointers or references in or...
A: Introduction: A virtual function or method is an inheritable and overridable function or method that...
Q: Why does OCaml's language have separate arithmetic operators for integers and floating-point values?
A: Introduction: Why does OCaml's language have separate arithmetic operators for integers and floating...
Q: Modify the following program so it can add two numbers between the values 0 and 9. The current progr...
A: Below Im modifying the code
Q: For each of the following values, specify the proper primitive numeric data type: 12 bananas
A: Introduction: For 12 bananas, the proper basic numeric data type is:
Q: Write a program in C-language that will accept any positive number and will count up, starting from ...
A: Introduction: Looping reduces the difficulty of complicated tasks or problems to a manageable level....
Q: In the field of computer science, the words "random access" and "sequence access" are used interchan...
A: Introduction: Sequential access is a method of accessing data in an ordered manner.
Q: Discuss the new cloud computing characteristics that enable for scalability, as well as why these as...
A: Introduction: Customers may utilise cloud computing to access equivalent applications through the in...
Q: Given tle following Floyd Warshall algorithm, prove that there exists a vertex x with dist[x][x] < 0...
A: There are two ways to check this: 1. Check the main-diagonal entries of the result matrix for a nega...
Q: Explain the general concept of sensor clouds and the protocol architecture in the context of a block...
A: Introduction: A sensor is a device that recognizes and quantifies beneficial properties and data.Sen...
Q: You have many filesystems on your hard drive, each of which is mounted to a different directory in t...
A: Introduction: You have many filesystems on your hard drive, each of which is mounted to a different ...
Q: Q9. i. What are the different forms of Web testing security issues? ii. What are some of the most...
A: Introduction: i. Some Web testing security problem types are listed under: DOS(Denial of Service...
Q: List five uses for nonlinear data structures.
A: Solution Unlike Array and Connected List, the tree is a hierarchical (or nonlinear) data structure...
Q: Write a C++ program that contains the following: Template Stack In main() write code demonstrating ...
A: PROGRAM INTRODUCTION: Include the input output libraries. Start the definition of the class to repr...
Q: c program of On the spelling test, Jorge missed 4 words and was marked 92%. Find out how many words ...
A: #include<stdio.h> int main() { int x; int miss=4; float percent=92; x=miss/(1-(percent/100)); ...
Q: Make a note of the answers to the following questions. 1)Explain the evolution of requirements. ...
A: Introduction The satisfaction of users’ requirements through a developed system is inherently uncert...
Q: Which of these are predefined JavaScript objects? O document O browser O window O htmlDocument O nav...
A: answer is
Q: Explain why object-oriented analysis is important in the development of an information-system design...
A: Explanation:- To make this more accessible, I shall outline the application of object-oriented analy...
Q: Complete the following protocol message so that it represents a potentiometer reading of 987: (write...
A: Here, I have to provide a solution to the above question.
Q: What are the benefits of utilizing cloud computing services? What are the dangers and concerns relat...
A: Introduction : Here's everything you need to know: There are various benefits to storing data over t...
Q: What exactly is an ID column?
A: Introduction: Column for identifying yourself
Q: Discussions on the use of digital evidence in criminal and civil court cases are encouraged.
A: Introduction: The importance of digital evidence:- Because of the widespread usage of electronic dev...
Q: Data Structures and Algorithms is a course that teaches students about data structures and algorithm...
A: Introduction Stack is a dat structure which follows LIFO (Last In First Out) principle where the el...
Q: olution
A: given - Don't copy other experts solution.
Q: What is the return result of a function that lacks a return statement or has an empty return stateme...
A: Introduction: The return value of a function is the final value that was returned back to the calli...
Q: Computer science In a few sentences, describe machine learning and deep learning.
A: The science of teaching computers to learn without being explicitly taught is known as machine learn...
Q: Show a left-derivation for the following grammar based on the for the string aaaab 1. S→ AB 2. А — а...
A: Here in this question we have given a grammer and we have asked to do a left derivation for the stri...
Q: public class AverageWithSentinel public static final int END_OF_INPUT = -500'; %3D public static voi...
A:
Q: Discuss intents and how they may be used in Android programming. Make a point of mentioning the two ...
A: Intents and their purpose in Android Application: An intent is an object that performs certain task...
Q: Items for mobile users are controlled through a "Application Store" interface. Users may browse, dow...
A: Intro Browse. Download install
Q: Describe how the implementation of the following style rule differs between Internet Explorer operat...
A: Explanation: Internet Explorer shows a mild difference when running in Quirks mode and standard mod...
Q: What type of storage typically shares files utilizing standard network protocols, such as Server Mes...
A: According to our guidelines, we are allowed to solve only the first question. Please post the other ...
Q: PYTHON!! Solve pro blem by using PYTHON Program to remove the ith occurrence of the given word in li...
A: To write python code to remove the ith occurrence of the given word in list where words can repeat.
Q: 1. Apply quicksort to sort the list E, X, A, M, P, L, E in alphabetical order. Draw the tree of the ...
A: The Answer is
Q: What is the distinction between sequential and random access?
A: Introduction: We look at how data is written or read to a computer programme when we talk about sequ...
Q: To what extent has computer technology and its applications had an impact up to this point?
A: Given: To what extent has computer technology and its applications had an impact up to this point?
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- IEEE 754-2008 contains a half precision that is only 16 bits wide. The leftmost bit is still the sign bit, the exponent is 5 bits wide and has a bias of 15, and the fraction is 10 bits long. A hidden 1 is assumed as part of the significand just like the IEEE-754 format we learnt in the class. Write down the bit pattern to represent −0.15625 × 100 in IEEE 754-2008 half-precision format. You need to find out the bits for the sign, the exponent, and the fraction. To answer this question, you need to convert the decimal fraction to its binary representation. Check out the link given in Q1. You have to show all steps including the fraction conversion (from decimal to binary).Please enter all answers as strings of 0's and 1's. Consider the 64 bit DES block below. 00100000001000010001000000000000000000000000000000000000000000000010000000100001000100000000000000000000000000000000000000000000 Suppose that this is the initial input to DES. What will the block look like after the initial permutation (IP) is applied?If we apply the IP−1−1 transformation to the above, what will the result be?What is overflow and how is it detected when adding unsigned binary numbers; and how is it detected in two's compliment? Thank you
- Dont use others answers please!! will leave you feedback!! Thank you! 6 a. We have seen how to turn bits on, and how to turn them off. What bitwise operator allows us do this turning off/on at the SAME time for several bits? b. Given the byte: 10101010, now suppose we want to TOGGLE bits 4, 5, 6 and 7, but leave Bits 0, 1, 2 and 3 in whatever state they are in. Show the value, mask and the result of the bitwise logical operation.For each number, perform the following bitwise operations. You don't have to show work for each conversion. Format your answers in the following ways, points will be deducted if answers are not formatted correctly. Answers are numbered. Write all hexadecimal numbers using the 0x notation to differentiate between other number systems. Write all binary numbers in groups of 4 bits XXXX XXXX or groups of 8 bits XXXXXXXX What is the resulting bit pattern after applying bitwise exclusive OR (^)?00110100 01001010 11010001 1010101011010101 11011110 01101010 11101010-----------------------------------???????? ???????? ???????? ???????? What is the resulting bit pattern after applying bitwise inclusive OR (|)?01010110 01101011 10111010 1100101011111001 10110110 00110010 11111011-----------------------------------???????? ???????? ???????? ???????? What mask value will make the following expression true when applying bitwise AND (&)?11001011 00001111 01010101 00110011???????? ????????…Please for thi question, kindly explain into details for me. This seems a new topic to me altogether. Thanks a lot. A bit string is a sequence of numbers consisting of 0’s and 1’s. Answer the following questions with explanation and/orclear computations.(a) How many bit strings of length 5 are there?(b) How many bit strings of length 5 contain at least three 0’s?(c) How many bit strings of length 6 are palindromic (i.e., read the same from left to right as from right to left)?(d) How many bit strings of length 8 contain at least two 1’s?
- We have 18sources, each creating 400nibble (4-bit)per second. Since onlysome of these sources are active at any moment, we use statistical TDM tocombine these sources using character interleaving. Each frame carries 15slotsat a time, butwe need to add 9-bit addresses to each slot. Answer the following questions: a. What is the size of an output frame in bits? b. What is the output frame rate? c. What is the duration of an output frame? d. What is the output data rate?Four computers are sending the digital data over a multiplexed line as shown in the Figure below. A). Show how the messages are multiplexed into frames using synchronous TDM and Asynchronous TDM. B). How many frames are generated if you are using Synchronous TDM? C.) How many frames are generated if you are using asynchronous TDM with frame size 3?One way of detecting errors is to transmit data as a block of n rows of k bits per row and adding parity bits to each row and each column. The lower-right corner is a parity bit that checks its row and its column, Will this scheme detect all single errors? Double errors? Triple errors?
- For each number, perform the following bitwise operations. You don't have to show work for each conversion. Format your answers in the following ways, points will be deducted if answers are not formatted correctly. Answers are numbered. Write all hexadecimal numbers using the 0x notation to differentiate between other number systems. Write all binary numbers in groups of 4 bits XXXX XXXX or groups of 8 bits XXXXXXXX What mask value will make the expression true when applying bitwise inclusive OR (|)?10011001 11101100 10101010 11001100???????? ???????? ???????? ????????-----------------------------------11111111 11101111 10101010 11001111Express the mask as an 8 digit hexadecimal number. Given the following:unsigned int result = 0;unsigned int num1 = 0x41;unsigned int num2 = 0x78;unsigned int num3 = 0x43;unsigned int num4 = 0x7A;result = (num1 << 24);result = result | (num4 << 16);result = result | (num2 << 8);result = result | num3;A) Express the value of…(a) How many bit strings of length 13 either starts with three consecutive 1s or end with 2 consecutive 0s? (b) How many bit strings of nine lowercase letters start with a vowel, if letters cannot be repeated?Which of the following encoding methods does not provide for synchronization? a. NRZ-L b. RZ c. NRZ-I d. Manchester

