I have to open the CSV to read these data
Q: What is the location of the Windows hosts table?
A: Hosts files are used in Windows and other operating systems such as Linux and Mac OS. In each…
Q: What are the advantages and disadvantages of using internal static analysis? Computer science
A: Introduction We need to talk about the benefits and drawbacks of employing internal static analysis.
Q: What is the relationship between the components of the BI architecture to produce a unit system?…
A: Introduction: 1. A decision must be taken in order to properly coordinate the use of trade insights…
Q: CPU time is a valuable computer resource, and a smart computing system should be designed to make…
A: The DMA module transfers a whole block of data straight to or from memory, one word at a time,…
Q: What is the role of the Mobile Switching Center in the Global System for Mobile Communication…
A: INTRODUCTION: Here we need to tell the role of the Mobile Switching Center in the Global System for…
Q: Describe what vulnerabilities 'WannaCry' exploited to infect its targeted systems
A: In this question we will understand the 'WannaCry' How it will infect the targeted system and what…
Q: Describe the many components of the Internet of Things.
A: There are two major components to the Internet of Things. Thing or object - which you intend to…
Q: What is cloud computing and what is advantages and disadvantages
A: Given To know about the cloud computing and it's advantages and disadvantages.
Q: If the passenger is a datagram, what is similar to the connection layer frame?
A: In the transportation analogy, the frame is analogous to:
Q: Describe in your own wrds what does the import command with python responsible for?
A: Import command in python Import command in python same as # include in C or C++, that is used to…
Q: Make a list of three probable virtualization issues.
A: Virtualization Virtualization is the act of generating a virtual representation of anything (instead…
Q: Internal and external BGP sessions?
A: Border Gateway Protocol (BGP) BGP enables the proper peer to be discovered, authenticated, and…
Q: What would you say to your boss if you were requested to include a project buffer for the whole…
A: Introduction: It might sometimes be difficult to spot inflated job estimates. The adoption of a…
Q: What are the three types of backups that can be utilised in database recovery? Explain what each…
A: Introduction: Actually, database is a system for storing information. MANAGEMENT SYSTEM FOR DATABASE…
Q: n a requirements review, who should be involved? Examine the methods for validating the…
A: Introduction: A requirement review is a process in which a group of individuals read and evaluate…
Q: When it comes to computer science, should the memory of a dataflow system be associative or…
A: justification: A Dataflow's MemoryBecause dataflow machines are built to handle massive volumes of…
Q: hwy immutable memory can be faster in functional programing?
A: The Answer is in step-2.
Q: How to Increase the Size of Your Virtual Memory
A: Introduction: Using Virtual Memory, which makes good use of available space on a hard drive, data…
Q: Describe the internet of things in your own words. What is the difference between these two…
A: Introduction: IoT (Internet of Things):— The Internet of Things (IoT) is a computer technology…
Q: What types of programming languages are there? Each one should be briefly explained.
A: Different types of programming languages are: Declarative language: These types of languages are…
Q: clusion for multim
A: conclusion for multimedia cards
Q: Q3) write True or False answer for the following statements. Correct the false statements a) BGP is…
A: Introduction: We need to find if the given statements are true or false: According to business…
Q: I'm trying to learn CSS and it isn't easy. Can someone help me with this problem? Modify or add one…
A: In this question we have to use CSS properties to change the color of the text using COLOR NAME RGB…
Q: Consider the relation R(A, B, C, D, E), and the decomposition of R into R1(ABC) and R2(ADE). (a)…
A:
Q: Formulate a mapping procedure that provides eight consecutive microinstructions for each routine.…
A: opcode = 6 bitcontrol memory = 2048 words = 11 bits of address
Q: What is the procedure for gathering and sorting data for data entry?
A: Data entry is a broad field with varying data input needs depending on the role, industry, and…
Q: What do firewalls do? What type of firewall is best?
A: Find the answer given as below :
Q: What is software project management, and what are some of the project management tools available?
A: Software project management is the act/discipline of planning and supervising software projects.…
Q: Make a list of five circumstances in which you might use a queue
A: Introduction: Queues operate on a First-In-First-Out basis, which means that the item that was input…
Q: What are the advantages of CSS sprites?
A: Introduction: Because each picture generates an HTTP request on its own, a web page with a large…
Q: Where does the remainder of the system (apart from the kernel) reside?
A: Introduction: An operating system is a sort of software that manages and controls all of the…
Q: Why is MetaData regarded as the most significant component of a data warehouse?
A: Definition: Metadata: "Data about data" is what metadata refers to. The prefix "meta" is employed to…
Q: {: {: a 0 0 (b): Let U = : a, b ER} and W c, d ER} be 0 0 с d two subspaces of M2 (R). Show that U e…
A:
Q: Explain briefly how the hybrid approach should be used to encrypt a long message.
A: In cryptography, a hybrid cryptosystem is one that combines the convenience of a public-key…
Q: What are microcomputers looking for in the first place?
A: Justification: A microcomputer is an electronic device having a central processing unit that is…
Q: What is the significance of database testing for?
A: Introduction Database testing is a sort of software testing that examines the schema, tables, and…
Q: Write a Java Code to remove the whitespaces from a string only for leading & trailing spaces
A: As given, we need to write a Java program to remove the whitespaces from a string only for leading…
Q: What is the classification of database design that accompl
A: A database is an assortment of related information which addresses some part of the real world. Data…
Q: Describe the procedures involved in setting up a fresh new computer for use?
A: The Answer is in step2
Q: Give two reasons why you believe it is critical for a computer programmer to learn about computer…
A: There are several causes for this: 1)If a particular computer programmer wants to determine what has…
Q: Write an algorithm to find maximum of n numbers.
A: In the given question we need to obtain the Maximum Number from n Numbers. For this , we would use…
Q: Describe a circumstance in which changing the caption of a field to request input from the user…
A: Input fields are a crucial component of user interface design because they enable users to enter…
Q: Distinguish between implementing an interface and implementing a derived class.
A: Answer: While implementing an interface, we need to implement all the methods declared in the…
Q: Certain features of a database relation may be encrypted for security reasons. Why are encrypted…
A: Introduction: A value that has been encrypted cannot be indexed unless the value is encrypted to the…
Q: A digital system has a 3-bit input from 000 to 111. We want to design a logic circuit that produces…
A:
Q: Explain how expansion cards may increase the processing capabilities of a microcomputer.
A: An expansion card is an electronic card. It is used to add more extra functionality to computers.…
Q: What is the difference between "systemctl start " and "systemctl enable "?
A: Intro What is the difference between "systemctl start <application name>" and "systemctl…
Q: The JTAG UART is IRO 80. The appropriate set-enable bit is bit in the ICDISERN register at address…
A:
Q: What exactly is the difference between a webpage and a website.
A: Website: A website is a central place where many web pages are kept by a person or organization and…
Q: Identify at least three different threat actors and explain why each was chosen. At least two must…
A: Threat actors are any malicious organizations that initiate violations of organizational security…
I have to open the CSV to read these data
Step by step
Solved in 2 steps with 3 images

- Question 2: B – Write a program that prompts for an input string of variable length. Once input, your program will do the following: Output the length of the string Output the first and last characters of the string Output the middle character of the string (and its position) Transpose (switch) the two halves; 2nd half starts with the middle character. Print the string out in all upper case characters Example Sessions: Please input a string :>> Firewall Program Output: String length is: 8 First char is: F Last char is: l Middle char at position 4 is: w Transpose: wallFire Upper Case: FIREWALL Please input a string :>> Program Program Output: String length is: 7 First char is: P Last char is: m Middle char at position 3 is: g Transpose: gramPro Upper Case: PROGRAMWhat output is produced by the following code? For each output line, describewhether the line begins or ends with a blank or blanks.String aString = "Jelly beans";double d = 123.1234567890;System.out.println("START1234567890");System.out.printf("START%sEND %n %9.4f %n", aString, d);Help convert/show this code to Jupyter Notebook. Comments added in the code is appreciated ... def problem_1(plaintext, shift): ciphertext = "" while isinstance(int(shift), int) == False: # asking the user to reenter the shift value shift = input("Please enter your key (integers only!): ") shift = int(shift) new_ind = 0 # this value will be changed later for i in plaintext: if i.lower() in alphabet: new_ind = alphabet.index(i) + shift ciphertext += alphabet[new_ind % 26] else: ciphertext += i print("The ciphertext is: " + ciphertext) plaintext = input("Please enter your plaintext: ") shift = input("Please enter your key: ") alphabet = "abcdefghijklmnopqrstuvwxyz" problem_1(plaintext, shift)
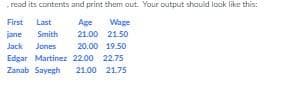
- What output will be produced when the following lines are executed?cout << "*" << setw(5) << 123 << "*"<< 123 << "*" << endl;cout.setf(ios::showpos);cout << "*" << setw(5) << 123 << "*"<< 123 << "*" << endl;cout.unsetf(ios::showpos);cout.setf(ios::left);cout << "*" << setw(5) << 123 << "*"<< setw(5) << 123 << "*" << endl;with ur new code, I still got wrong output and seems like it wouldn't add succesfully A tweet about something controversialRemember to vote!Look at this meme :OA tweet about something controversialRemember to vote!Look at this meme :OThe most frequent word is: aWrite a program that will open the file dataFile.csv Download dataFile.csv, read its contents and print them out. Your output should look like this: First Last Age Wagejane Smith 21.00 21.50Jack Jones 20.00 19.50Edgar Martinez 22.00 22.75Zanab Sayegh 21.00 21.75
- Write a program that will read the file text.txt which is provided and the encryptedmessage in there. Please write back the decrypted message into the output.txt file.When you see the message in the output.txt file, you need to submit the java codefile. You need to use Rot13 class for decrypting the message. Do not need to submit in the output.txt file. file example: public class FileExample { public static void main(String[]args){ try {//create file object for input.txtFile in_file = new File("src/input.txt");//create file object for output.txtFile out_file = new File("src/output.txt"); //read the input.txt file with ScannerScanner read = new Scanner(in_file);//write the output.txt file with PrintWriterPrintWriter w = new PrintWriter(out_file); while(read.hasNextLine()){w.write(read.nextLine());} //don't forget to closew.close(); // while(scan.hasNext()){// System.out.println(scan.next());// } }catch(Exception ex){ex.getStackTrace();}What will be output to the screen when the following code is executed:def PrintMe(x): try: return s * 5 except: print("Error has occured") finally: print("Doing some cleanup")message = "HUE stands for Hadoop User Experience"print(PrintMe(message))-For external input, which of the following instructions is used? Aşayuakiieiuemangisi bir ueyişkeT upr ueyinui Osetlocale Ofor Ocout Oprintf Ocin -Aşayuakiieiuemangisi bir ueyişkeT -Which of the following does not represent a variable type? Ofloat vs Ochar Odouble Oint
- Can you exlplain with comments following data .data prompt byte1 "Input number1:-" mynumber1 byte1 10 prompt byte2 "Input number2:-" mynumber2 byte2 10 .code main PROC cmp mynumber1 , mynumber2 jl Less move Word [temp] , mynumber2 jump both: Less: move Word [temp] , mynumber1 Both: prompt demo "Input Newnumber1:-" demo1 demo10 cmp demo1, temp jl Less move Word [temp] , temp jump both: Less: move Word [temp] , demo1 And the cycle continuesI am trying to run a jar file and I get this error. Error encrypting/decrypting file net.codejava.crypto.CryptoException: Error encrypting/decrypting file Caused by: java.security.InvalidKeyException: Invalid AES key length: 17 bytes at net.codejava.crypto.CryptoUtils.doCrypto(CryptoUtils.java:57) at net.codejava.crypto.CryptoUtils.encrypt(CryptoUtils.java:27) at net.codejava.crypto.CryptoUtilsTest.main(CryptoUtilsTest.java:18) Caused by: java.security.InvalidKeyException: Invalid AES key length: 17 bytes at java.base/com.sun.crypto.provider.AESCrypt.makeSessionKey(AESCrypt.java:1329) at java.base/com.sun.crypto.provider.AESCrypt.init(AESCrypt.java:1053) at java.base/com.sun.crypto.provider.ElectronicCodeBook.init(ElectronicCodeBook.java:97) at java.base/com.sun.crypto.provider.CipherCore.init(CipherCore.java:481) at java.base/com.sun.crypto.provider.CipherCore.init(CipherCore.java:399) at java.base/com.sun.crypto.provider.AESCipher.engineInit(AESCipher.java:311) at…The script in the bash shell of Linux Write a calculator script using if and elif statements called “calc-yourlastname.sh” that will add (add), subtract (sub), multiply (mul) and integer divide (div) two numbers. The script should take 3 arguments from the command line and produce the output. The command line syntax is # ./scriptfile operation number1 number2. Integer division will yield only the quotient and no remainder. You can use `expr expression` or $((expression)) to perform your math For example, your results should appear like: [root@localhost chap7]# ./calc-smith.sh add 3 2 3 + 2 = 5

