I need someone experienced with mips please Only question 9 please
COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
1st Edition
ISBN:9780357392676
Author:FREUND, Steven
Publisher:FREUND, Steven
Chapter4: Financial Functions, Data Tables, And Amortization Schedules
Section: Chapter Questions
Problem 8AYK
Related questions
Question
I need someone experienced with mips please Only question 9 please
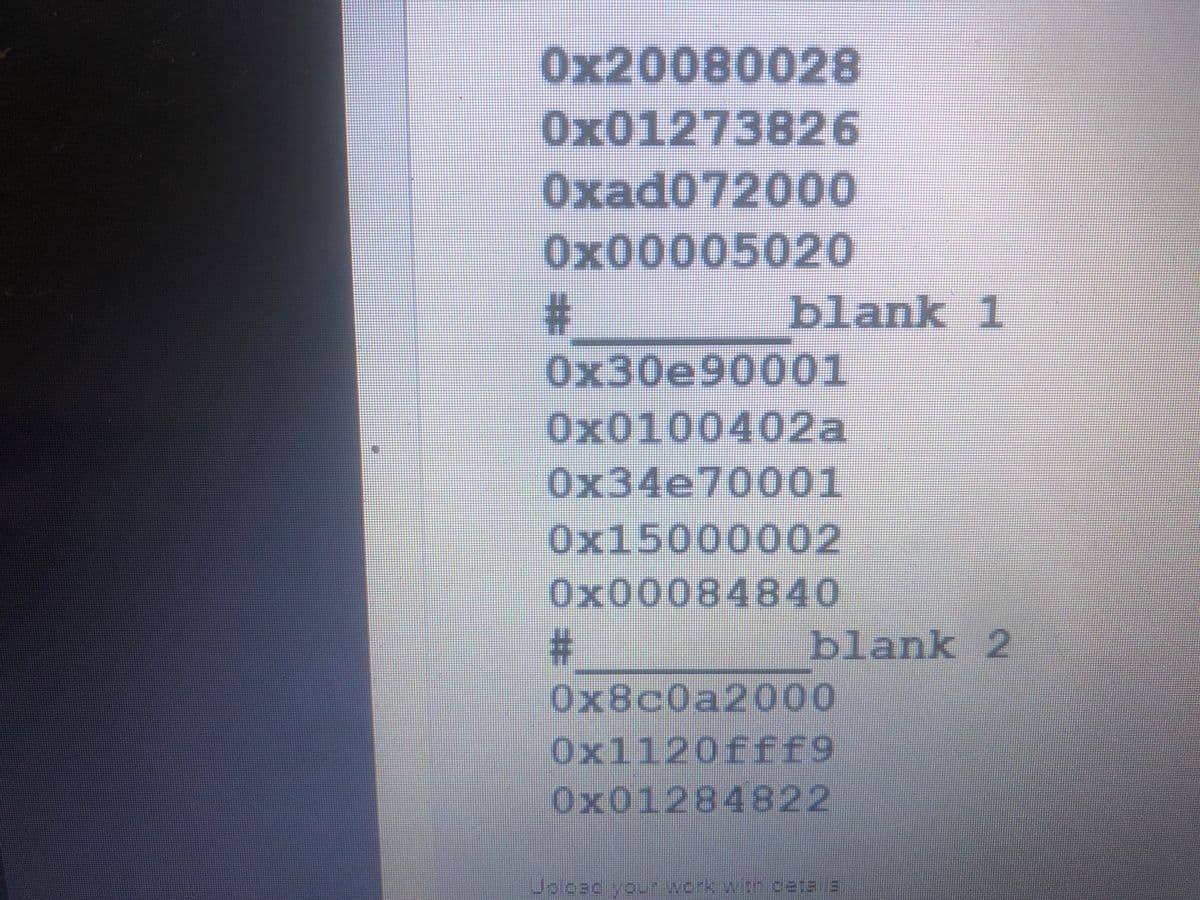
Transcribed Image Text:0x20080028
0x01273826
Oxad072000
0x00005020
blank 1
0x30e90001
0x0100402a
0x34e70001
0x15000002
0x00084840
blank 2
0x8c0a2000
0x1120fff9
0x01284822
Jalcac you-work wth cata la
%23
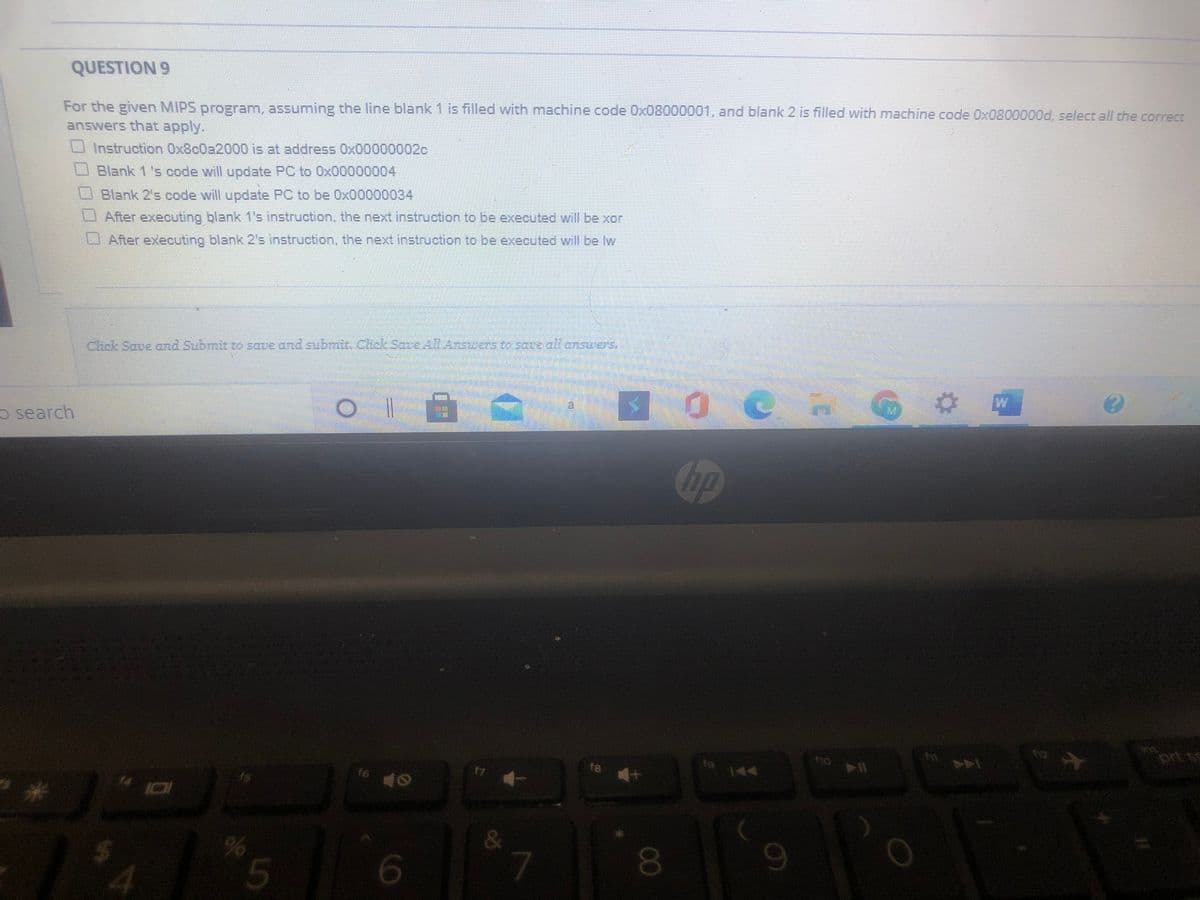
Transcribed Image Text:QUESTION 9
For the given MIPS program, assuming the line blank 1 is filled with machine code Ox08
answers that apply.
000001, and blank 2 is filled with machine code Ox0800000d, select all the correct
Instruction Ox8c0a2000 is at address 0x00000002c
Blank 1 's code will update PC to 0x00000004
O Blank 2's code will update PC to be Ox00000034
After executing blank 1's instruction, the next instruction to be executed will be xor
After executing blank 2s instruction, the next instruction to be executed will be lw
Chck Saue and Submit to saue and subit. Chck Sare Answers to sare all onsrers,
W
o search
hp
prt s
fo
f8
144
17
f6
&
080
5
9.
%24
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Recommended textbooks for you

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L