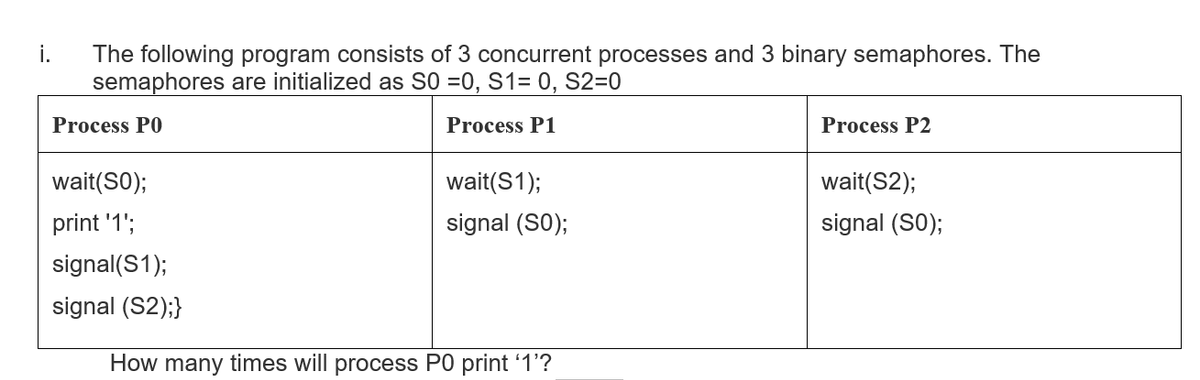
i. The following program consists of 3 concurrent processes and 3 binary semaphores. The semaphores are initialized as S0 =0, S1= 0, S2=0 Process PO Process P1 Process P2 wait(SO); wait(S1); wait(S2); print '1'; signal (S0); signal (S0); signal(S1); signal (S2);} How many times will process P0 print 1'?
Q: I'm not sure what the point of routing is or how it works. Separate and contrast the differences…
A: Introduction: Routing is the term used to describe the process of moving between pages. It may be…
Q: Cache memory is critical in today's computers because it allows programs to be loaded quickly. How…
A: Introduction: Cache memory is the chip-based computer component that retrieves data at a high rate,…
Q: Write a program that will allow a teacher to calculate the average test score for a certain number…
A: def average(arr): avg = 0 # initialize avg to 0 for j in range(len(arr)): # add jth value to avg…
Q: Given the following fragment C program that convert from degrees Celsius to degrees Fahrenheit,…
A: double c = 20;double f;f = (9/5) * c + 32.0;f = 52.0 b first 9/5 = 1 because 9 is int and 5 is int…
Q: What are the basic elements and traits to search for in descriptive models, and how do you identify…
A: Introduction: A descriptive model will use previously recorded data in databases to provide an…
Q: Think of a ‘existing relationship of things’ that are connected together that reflect the kind of…
A: We need to think of a ‘existing relationship of things’ that are connected together that reflect the…
Q: We feel that Flynn's taxonomy should be enlarged by one level. A higher-level computer has a more…
A: Introduction: Flynn's taxonomy is a categorization system for parallel computer architectures. From…
Q: When it comes to modifying the RFI route, what alternatives do you have?
A: Introduction: Some background information about your organisation (to provide context to potential…
Q: Windows distinguishes between four different kinds of disc volumes. Explain the four sorts of…
A: Introduction: A disc volume is a location for storing data made up of accessible free space on…
Q: What are the fundamentals of taking into account edge computing and cloud computing in an Internet…
A: introduction: IoT System: An IoT system is a system that operates on the internet of things and is…
Q: 4. A software company sells game cartridges for $99. Quantity discounts are given according to the…
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining…
Q: what are the main differences between C-ITS and TCP/IP protocol stacks and what are the main…
A: At the physical and lower MAC layer, the G-ITS stack has an equivalent version of the IEEE 802.11p…
Q: 27. A memory connected to a microprocessor has 20 address lines and 16 data lines. What will be the…
A: Let's see the solution that what will be the memory capacity
Q: where: a=2; and b=3; c1='A'; c2='a'; printf("The NUMERIC VALUE of %c is…
A: Ascii value of A=65 Ascii valued of a=97
Q: Given input {71, 22, 21, 99, 53, 69, 39} and a hash function h(x) = x mod 10, show the resulting:…
A: HASH TABLE IS:
Q: Write a program to determine the cost of an automobile insurance premium, based on driver's age. and…
A: Code: import java.io.IOException;import java.util.Scanner;class Main { public static void…
Q: I'm not sure what the point of routing is or how it works. Separate and contrast the differences…
A: Answer :
Q: Write (or borrow) a program in one of the following languages (C, C++ or Java). The program (or…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: I'm not sure what the point of routing is or how it works. Separate and contrast the differences…
A: In networking, routing is a process of moving data packet from source to destination. Routing is…
Q: What would happen if you set reboot.target or runlevel 6 the default runlevel/target for your…
A: The runlevel command is used to find the current and previous runlevels on Unix-like operating…
Q: if(adultRB.isSelected() == true) decBaseFee = decADULT FEE; here what is isSelected? a. class b.…
A: The code given in the question is a conditional statement.
Q: Write a Java Program to take 3 integers(a.b.c) from the user, print "Great Number" if one of b or c…
A: Find greater number, far number or ugly number as per the given condition.
Q: Name the Operators that cannot be Overloaded.
A: Answer the above questions are as follows:
Q: Are embedded computers and general-purpose computers different in terms of what they do?
A: Embedded Computers is also known as embedded systems.
Q: unix (linx) system A folder D1 has three files f1,f2, and f3. Write the commands required to…
A: A folder D1 has three files f1,f2, and f3. Write the commands required to ensure that you get a…
Q: Q2- Write a program to create a vector matrix A(10) from input. Then print only the numbers that…
A: The program is written in C++. Check the program screenshot for the correct indentation. Please…
Q: A certain computer has a cell size of 128 bits. Give an advantage and disadvantage of this cell size
A: CPUs that process 128 bits at a time, as opposed to 8, 16, 32, or 64 bits. There are no 128-bit…
Q: Explain how a cloud storage program varies from traditional client storage software in terms of…
A: Introduction: I am a proponent of the ease and value that cloud technology provides, since I now use…
Q: ct PatientInfo string name; int age; string problem; program must have a StaticQueue class that…
A: Code is below:
Q: Make use of as many examples as you can to support your point of view. The bottom-up or the top-down…
A: The answer is given in the below step
Q: Which search engines are legal and ethical in their operations?
A: Introduction: Ethical considerations with the usage of search engines include (1) search-engine bias…
Q: What exactly is the duty of an informatics nursing specialist?
A: The informatics nurse specialist combines medical knowledge with computer technology (IT). It's a…
Q: Describe how a current operating system is able to support a feature of a previously installed…
A: Introduction: A computer operating system maintains and controls computing devices such as…
Q: 2. Differentiate RAM to ROM (100 to 150 words)
A: Given Question: Distinguish between RAM and ROM (100 to 150 words)
Q: Give one advantage and one disadvantage of the Microkernel operating system over the Monolithic…
A: There are two types of kernels present in Operating system. They are as follows:- 1. Microkernel 2.…
Q: Can you think of a Linux package management system that you have tried or that you are thinking…
A: Software updates from specified Linux repositories (repos) may be installed, updated, removed, and…
Q: What is the procedure for implementing multifactor authentication? What role does it play in…
A: Introduction: On the desktop, go to Settings > Security and Login to get to it. On the right,…
Q: What variables had a role in the development of computer security into the present state of…
A: Introduction: Computer security, often known as cybersecurity, refers to the safeguarding of…
Q: What are the advantages and disadvantages of caching write operations on a disk?
A: Introduction: Advantage: Ensures rapid retrieval while also ensuring that the data is stored in the…
Q: What separates the TPC from the SPEC in terms of emphasis?
A: SPEC and TPC: The TPC, or Transaction Procession Council, is an organization that establishes…
Q: What are the two most compelling arguments in favor of using layering protocols? Give specific…
A: What are the two most compelling justifications for layered protocols? A layer's changes have no…
Q: 1) What are the difference ways that a file can be opened and what is the implication of both of…
A: The answer for the given question is as follows.
Q: Utilize a request for proposal to collect information on hardware and system software, as well as to…
A: Introduction: Without computer software, computer hardware is almost worthless. The term "software"…
Q: what are input and output devices?
A: Input and output devices: input output devices allow the computer to communicate with outside the…
Q: IoT systems are becoming more complex. What are the preconditions for contemplating the usage of…
A: Introduction: However, all full IoT systems have a common characteristic in that they are comprised…
Q: if(adultRB.isSelected() == true) decBaseFee = decADULT_FEE; here what is isSelected? a. class b.…
A: The isSelected() method is used to check if an element is selected or not. It returns a boolean…
Q: Describe how a current operating system is able to support a feature of a previously installed…
A: NOTE :- Below i explain the answer in my own words by which you understand it well.…
Q: Cache memory is critical in today's computers because it allows programs to be loaded quickly. How…
A: Introduction: Cache memory is crucial because it enhances data retrieval performance. It saves…
Q: An incident response (IR) is a collection of operations that are carried out in the course of a…
A: What is an IR plan and when is IT used Incident response planning contains specific directions for…
Q: antages and disadvan
A: Open Source Operating SystemOpen source refers to computer software or applications in which the…
Step by step
Solved in 2 steps

- The following program consists of 3 concurrent processes and 3 binary semaphores. The semaphores are initialized as S0 = 0,S1 = 1 and S2 = 1. Process P0:while (true) { wait (S0); print '1';release(S1);release(S2);} Process P1:wait (S2);release (S0); Process P2:wait(S2);release(S0); How many times will process P0 print '1'?Modiflow y the beprogram given to include response time program;SJF CPU SCHEDULING ALGORITHM #include<stdio.h> #include<conio.h> using namespace std; int main() { int p[20], bt[20], wt[20], tat[20], i, k, n, temp; float wtavg, tatavg; printf("\nEnter the number of processes--"); scanf("%d", &n); for(i=0;i<n;i++) { p[i]=i; printf("Enter Burst Time for Process %d--", i); scanf("%d", &bt[i]); } for(i=0;i<n;i++) for(k=i+1;k<n;k++) if(bt[i]>bt[k]) { temp=bt[i]; bt[i]=bt[k]; bt[k]=temp; temp=p[i]; p[i]=p[k];…Modiflow y the beprogram given to include response time program;ROUND ROBIN CPU SCHEDULING ALGORITHM #include<stdio.h> #include<conio.h> using namespace std; int main() { int i,j,n,bu[10],wa[10],tat[10],t,ct[10],max; float awt=0,att=0,temp=0; printf("Enter the no of processes--"); scanf("%d",&n); for(i=0;i<n;i++) { printf("\nEnter Burst Time for process %d--", i+1); scanf("%d",&bu[i]); ct[i]=bu[i]; } printf("\nEnter the size of time slice--"); scanf("%d",&t); max=bu[0]; for(i=1;i<n;i++) if(max<bu[i]) max=bu[i]; for(j=0;j<(max/t)+1;j++) for(i=0;i<n;i++) if(bu[i]!=0) if(bu[i]<=t) { tat[i]=temp+bu[i];…
- Answer the given question with a proper explanation and step-by-step solution. Consider the following source code, where k,l and m are constants declared with #define. The struct lnode is as defined as: struct lnode { char *str; // points to 32-character string struct lnode *next; // points to next node address struct lnode *prev; // points to prev node address }; You will need to determine the values for k, l and m, which are the dimensions of a 3-D array named A. struct lnode A[k][l][m]; int store_ele(int h, int i, int j, struct lnode dest) { A[h][i][j] = dest; return sizeof(A); } On compiling this program (with gcc -O2 -S -fno-asynchronous-unwind-tables) ,gcc generates the following assembly code for the store_ele function: store_ele: endbr64 movslq %edi, %rdi movslq %edx, %rdx movslq %esi, %rsi movdqu 8(%rsp), %xmm0 movq %rdi, %rax leaq (%rdx,%rdx,2), %rdx salq $6, %rax subq %rdi, %rax salq $4, %rax leaq (%rax,%rdx,8), %rax leaq (%rsi,%rsi,4), %rdx leaq (%rsi,%rdx,4), %rdx leaq…Develop a program in C to create three processes A, B and C. Job of these individual processes are as follows: Process A: Reads n numbers from the keyboard and counts the number of odd numbers in it. Then this count will be sent to the Process B. Process B: Reads the count from Process A and determines the fibonacci sequence of that count. This fibonacci sequence result will be sent to the process C. Process C: This process reads the fibonacci sequence from process B and sort the numbers in descending order.Write a C program to Implement a system of three processes which read and write numbers to a file. Each of the three processes P1, P2, and P3 must obtain an integer from the file (these instructions must be executed 200 times). The file only holds one integer at any given time. Given a file F, containing a single integer N, each process must perform the following steps 1. Fork two processes For 200 times: 2. Open F 3. Read the integer N from the file 4. Close F 5. Output N and the process' PID (On the screen) 6. Increment N by 1 7. Open F 8. Write N to F (overwriting the current value in F) 9. Close F b) Briefly describe why the processes P1, P2, and P3 obtain/read duplicates of numbers (why does a particular integer x appear in the output of more than one process)? Suggest a solution (you do not need to implement it) to guarantee that no duplicate numbers are ever obtained by the processes. In other words, each time the file is read by any process, that process reads a distinct…
- ) Consider the following sequence of virtual memory references (in decimal) generatedby a single program in a pure paging system:100, 110, 1400, 1700, 703, 3090, 1850, 2405, 2460, 4304, 4580, 3640a. Derive the corresponding reference string of pages (i.e. the pages the virtual addressesare located on), assuming a page size of 1024 bytes. (Assume that page numberingstarts at 0)b. For the page sequence derived above, determine the number of page faults for each ofthe following page replacement strategies, assuming that two (2) page frames areavailable to the program.i. LRUii. FIFOiii. OPT (Optimal)Write a C program Producer – Consumer as a classical problem of synchronizationStep 2. Write a program* that solves the producer - consumer problem. You may use the following pseudo codefor implementation.*program to write: produce -consumer problem to produce and consume the alphabet.//Shared data: semaphore full, empty, mutex;//pool of n buffers, each can hold one item//mutex provides mutual exclusion to the buffer pool//empty and full count the number of empty and full buffers//Initially: full = 0, empty = n, mutex = 1//Producer threaddo {…produce next item…wait(empty);wait(mutex);…add the item to buffer…signal(mutex);signal(full);} while (1);//Consumer threaddo {wait(full)wait(mutex);…remove next item from buffer…signal(mutex);signal(empty);…consume the item } while (1); it consumes and produce the alphabets not numbers sample output is attached you please also attach your sample outputUse C, C++, python or matlab to develop a program whose main routine accepts two parameters n and k, i.e. when you invoke your program from the shell, you pass it two parameters, n and k, where n >=16 and k >=3 and is in powers of 2 (e.g. 2, 4, 8, 16, etc.). Your main routine shall generate a random page trace of size n, where the page numbers have values ranging from 0 to ? − 1. Develop a subroutine within your program that implements the LRU page replacement algorithm (as a separate function within your program). Your algorithm shall use the doubly linked list stack implementation as outlined in slide 29 of lecture 10). The function shall accept a page trace and a parameter f for the number of frames allocated. Your main routine shall then apply the random page trace to the subroutine implementing the page replacement algorithm, multiple times (using only one trace, randomly generated), passing a parameter f (number of page frames used) that ranges from 4 to k. Your main…
- Use C, C++, python or matlab to develop a program whose main routine accepts two parameters n and k, i.e. when you invoke your program from the shell, you pass it two parameters, n and k, where n >=16 and k >=8and is in powers of 2 (e.g. 8, 16, 32, etc.). Your main routine shall generate a random page trace of length n, where the page numbers have values ranging from 0 to ? − 1. Develop a subroutine within your program that implements the FIFO page replacement algorithm (as a separate function within your program). The function shall accept a page trace and a parameter f for the number of frames allocated. Your main routine shall then apply the random page trace to the subroutine implementing the page replacement algorithm, multiple times (using only one trace, randomly generated), passing a parameter f (number of page frames used) that ranges from 4 to k. Your main routine shall then record the number of page faults for each run (i.e. for each f).Run your program using a page…The reader-writer problem can be stated as follows: A shared memorylocation can be concurrently read by any number of tasks, but when atask must write to the shared memory location, it must have exclusiveaccess. Write a Java program for the reader-writer problem.Write a python code in multiprocessing (from mpi4py import MPI) to create a system with 3 processes, the master process sending a string (Take string as user input) to the child processes 2 and 3. The child process 2 prints the vowels in the string while process 3 prints the consonants in the string. In the above cases, print the details of who is printing and what is being printed. (Use mpi4py Python Package)

