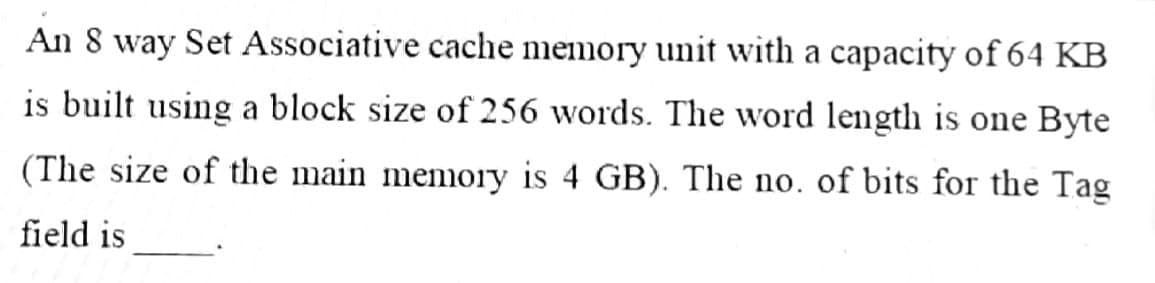
ia capacity of 64 KB ed length is one Byte . of bits for the Tag
Q: In the instruction MOV AX, 100[BP][SI], which segment register can be used to form the source…
A: According to our guideline we solve first one: ================================== Explanation below…
Q: Is the route cipher a two-key algorithm?
A: Asymmetric encryption: Asymmetric key cryptography, often known as public key cryptography, employs…
Q: In the case of a failure, what may possible induce a return to the previously performed instruction?
A: The executable program is a collection of instructions: The term page fault refers to pages that are…
Q: After the SHR instruction is executed in the code sequence below, what is the final value for AL?…
A: Option: The Answer is 0010_0111. The Answer is 0010_1011. The Answer is 0011_0011. The Answer is…
Q: Unintegrated information systems cause a plethora of issues?
A: Information systems: The fact of the matter is that various worries and issues are caused by various…
Q: What is the catastrophe recovery process's principal objective?
A: What is the catastrophe recovery process's principal objective in Below step
Q: Write a C++ program to calculate a rectangle's area. The program consists of the following function:…
A: ALGORITHM:- 1. Declare and define all the methods as required. 2. Call them from the main()…
Q: In a stack, items are added and deleted only at one end, referred to as the of the stack.
A: Stack:- The Stack is a linear data structure that follows a particular order in which the operations…
Q: In the AES decryption algorithm, what is the first step? Replacement of bytes. Rows should be…
A: AES Encryption Standard: Encryption and decryption are critical components of data security while…
Q: castrophe recovery tive?
A: Catastrophe recovery process is also known as disaster recovery plan When disaster happens , then…
Q: describe the three different types of identity verification. For each of these, provide a discussion…
A: Here, are some identity verification methods 1) Two-Factor Authentication - The two-factor…
Q: show how busy beaver function can be used to create non computable functions
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The busy…
Q: What is tha main function of router?
A: Introduction: Routers are computer networking devices used to transport data packets from one…
Q: Design a floating point ALU for multiplication and division. Also draw the flowcharts. Please do it…
A: MULTIPLICATION Example on decimal values given in scientific notation: 3.0 x 10 ** 1 + 0.5 x 10 ** 2…
Q: After the SHR instruction is executed in the code sequence below, what is the final value for AL?…
A: Correct Option is B⇒ 0010_1011
Q: Write a program that keeps reading integers from the user until he enters a negative number. The…
A: Please find the answer below :
Q: A single piece of information included inside a database record is referred to as a table schema…
A: A table is a big collection of data organised in a row and column manner (as a matrix), with rows…
Q: What distinguishes the Harvard computer architecture from the von Neumann computer architecture, and…
A: Introduction: While there are some similarities between the two architectures, the most significant…
Q: Describe the UNIX file system's characteristics, as well as the fundamental folders and directories…
A: Introduction UNIX: A computer operating system. It's frequently used in computers, laptops, and…
Q: 5. Fill in the permissions in Table 4-7 with checkmarks, assuming that all four files are in the…
A: Given that, The mode of permissions is rwxr-xr-x In this mode, r represents read operation w…
Q: Question 2: Class diagram with subclasses (generalization) (3%) Draw a class diagram with m
A: Class diagram for College Library Management System
Q: a) Write the input and output equations b) Derive the state table of the sequential circuit shown in…
A: A) Input equation Ta = x Jb = A.B' Kb=A'+B' Output equation y=A+B
Q: D Create a class Sum with the following fields, constructors and methods: Fields: create two…
A: As per the requirement program is developed. Note: In the question programming language is not…
Q: What exactly is a spanning tree, and what is an MST? Prim's and Kruskal's algorithms are compared…
A: What is the difference between a spanning tree and MST? Perform an algorithmic comparison and study…
Q: Describe the characteristics that any programming language should have. Main characteristics:…
A: In other words, the methods' names, argument types, and results aren't implemented. An ADT is an…
Q: Explain or draw a diagram on how to implement a database using PHP as the interface to a website.
A: Best Way is by using 3 tier Architecture: 1. Client Layer 2. Communication(Middle) Layer 3. Database…
Q: ou are given the following game tree. The top level is a maximizing level. Give the values…
A:
Q: Why will you use the AOP and OOP Mix Strategy? Describe the advantages 2) What is the primary cause…
A: Cross-cutting concerns like logging and security are easily implemented using aspect oriented…
Q: the two types of instruction in PLC.
A: types of instruction in PLC is an given below :
Q: How can we classify information systems?
A: 1. TPS A function covers all product and service purchases, sales, and everyday business…
Q: g) The smallest unit of binary data is the 1. bit. 2. byte. 3. word. Diec h) Which of the following…
A: According to the information given :- We have to fill in the blank on the basic of option mentioned.
Q: As a systems analyst, how can you ensure that a system's design is sound in the first place?
A: Computer system: You may use the strategies and essential components outlined below to provide a…
Q: 3. If the 5-bit 2's complement of X is equal to 10110, then without converting answer the following…
A: The answer is
Q: Make an application problem regarding equations (algebra) Follow these steps - Question - What is…
A: Question: Solve the system of equation Given data: 3x-4y=1 2x+3y=12 Formula/method used:…
Q: On the hard drives it administers, the operating system makes an attempt to store file chunks…
A: Given: Yes, it is still crucial to use SSDs. This difference is confounded by a number of other…
Q: What are the essential fundamentals of software engineering missing?
A: Introduction: What are the essential fundamentals of software engineering missing?
Q: Assume a computer has two network interface cards, NICC1, a Wifi USB, and NIC2, an on-board…
A: The network interface card (NIC) enables computers to interact across a computer network via wired…
Q: What is secondary memory, and what are its characteristics with instances, as well as its advantages…
A: What exactly is second memory? 1) Computer secondary memory Non-volatile, permanent memory that is…
Q: Describe the topology of a point-to-multipoint network.
A: Answer: The Point-to-Multipoint topology (also known as star topology or simply P2MP) is a common…
Q: Create a diagram with one entity set, P erson, with one identifying attribute, Name. For the P erson…
A: An Entity is a component of data, mostly it forms table name in database. Attributes describes…
Q: What are the seven levels of the OSI?
A: Open Systems Interconnection (OSI): Identify the seven levels of the OSI model. The seven layers…
Q: C++ Challenge!! Search Metrics Link to the 100,000 Random Integers:…
A: Program Explanation: 1) Implement the header file. 2) Declare the variable for counting the number…
Q: Using C++ language: Create a program that will accept three numbers and display in…
A: Answer the above program are as follows:
Q: State FIVE(5) elements of an activity bar chart.
A: Five elements of Activity bar chart : The Title The title gives a quick summary of what's in your…
Q: In every way, technology has transformed our lives. Discuss how technology affects communication in…
A: Given: Technology has completely changed our lives. Discuss the influence of technology on…
Q: Questions about operating systems You must use your own sentences; similarities will be…
A: Part(1.1) In computing, multiprocessing is a method of operation in which two or more processors in…
Q: emory of 8 GB, a pag -ytes. How many lev it virtual address sna
A:
Q: After the SHR instruction is executed in the code sequence below, what is the final value for AL?…
A: Introduction: MOV: It is a move instruction that moves the source into the destination. Syntax: MOV…
Q: Operating systems make every effort to store file blocks sequentially on the hard disk. Exactly why…
A: At the very bottom of the stack are the physical components, such as magnetic media, motors,…
Q: Write detailed code for Fibonacci sequence number print in go programming language code and give…
A: 1, Logic:- define a function for Fibonacci series display. Set p=0, q=1 and r=q display p, q use…
Step by step
Solved in 2 steps with 2 images

- If a microprocessor has a cycle time of 0.5 nanoseconds, what’s the processor clock rate? If the fetch cycle is 40% of the processor cycle time, what memory access speed is required to implement load operations with zero wait states and load operations with two wait states?Processor R is a 64-bit RISC processor with a 2 GHz clock rate. The average instruction requires one cycle to complete, assuming zero wait state memory accesses. Processor C is a CISC processor with a 1.8 GHz clock rate. The average simple instruction requires one cycle to complete, assuming zero wait state memory accesses. The average complex instruction requires two cycles to complete, assuming zero wait state memory accesses. Processor R can’t directly implement the complex processing instructions of Processor C. Executing an equivalent set of simple instructions requires an average of three cycles to complete, assuming zero wait state memory accesses. Program S contains nothing but simple instructions. Program C executes 70% simple instructions and 30% complex instructions. Which processor will execute program S more quickly? Which processor will execute program C more quickly? At what percentage of complex instructions will the performance of the two processors be equal?A two way set associative cache can host 32 KB (Kilobyte) of memory data with 16-word block. The memory system has 32 bits address bus. How many total bits does this cache have. (include 1 validation bit for each cache line, assume each word is one byte long).
- A computer has a 256 KB, K-way set associative write-back data cache with block size of 32 B. The address sent to the cache controller by the processor is of 32 bits. In addition to the address tag, each cache tag directory contains 2 valid bits and 1 modified bit. If 16 bits are used to address tag. What is the minimum value of K?A 2-way set-associative cache consists of four sets. Main memory contains 2K blocks of 8 bytes each and byte addressing is used.Q.) Show the main memory address format that allows us to map addresses from main memory to cache. Be sure to include the fields as well as their sizes.The hit rate of the memory closest to the ALU is increased from 75% to 80% in a practical cache memory hierarchy. The hit latency (or hit time) for the closest memory is 20ps, while the miss latency is 20ns. What would the expected reduction in the average memory access latency be?
- A cache memory system with capacity of N words and block size of B words is to be designed. If it is designed as a direct mapped cache, the length of the TAG field is 14 bits. If it is designed as a 4-way set associative cache, the length of the TAG field will be ………… bits.Suppose a byte-addressable computer using set associative cache has 224 bytes of main memory and a cache size of 64K bytes, and each cache block contains 32 bytes. a) If this cache is 2-way set associative, what is the format of a memory address as seen by the cache, that is, what are the sizes of the tag, set, and offset fields? b) If this cache is 4-way set associative, what is the format of a memory address as seen by the cache?Suppose a byte-addressable computer using set associative cache has 8M byes of main memory and a cache of 128 blocks, where each cache block contains 64 bytes. a) If this cache is 4-way set associative, what is the format of a memory address as seen by the cache, that is, what are the sizes of the tag, set, and offset fields? b) If this cache is 16-way set associative, what is the format of a memory address as seen by the cache
- Ifthere is a 64K cache with a block size of 7k, what is the number of bits in the indes field of block address, given the cache is (3) F Associative, (b) Direct Mapped, (¢) 2-way Sct Associative, and ) 4 - way Set Associative. bA certain computer system is consisting of 32 GB main memory and 32 MB cachememory. The cache uses 8 bytes word.a. Using cache direct mapping, determine the size of the tag, line and word.b. Using cache associative mapping, show the main memory address format.c. The computer uses a 2-way set associative mapping cache structure. Show the mainmemory address format.Suppose a byte-addressable computer using set associative cache has 216 bytes of main memory and a cache of 32 blocks, and each cache block contains 8 bytes. a) If this cache is 2-way set associative, what is the format of a memory address as seen by the cache, that is, what are the sizes of the tag, set, and offset fields? b) If this cache is 4-way set associative, what is the format of a memory address as seen by the cache?



