Identify the socket pair from the output line highlighted in green color.
Identify the socket pair from the output line highlighted in green color.
Chapter12: Network Configuration
Section: Chapter Questions
Problem 13RQ
Related questions
Question
Analyze the output given below.
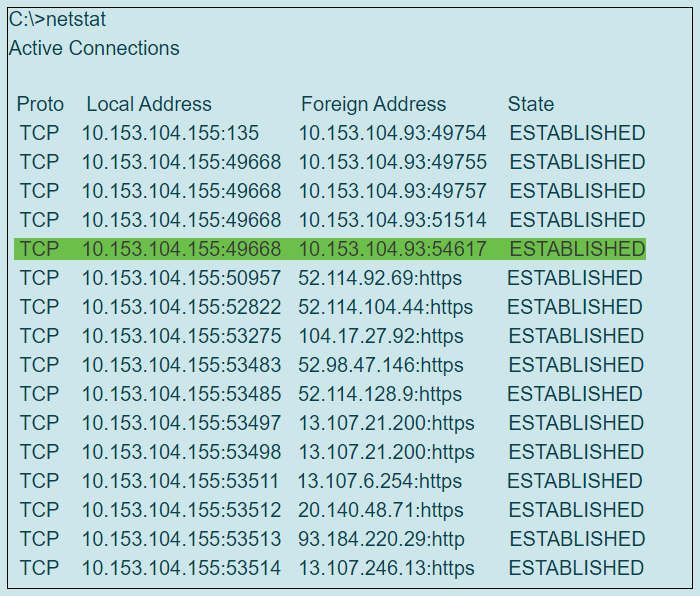
Transcribed Image Text:C:\>netstat
Active Connections
Proto Local Address
Foreign Address
State
TCP 10.153.104.155:135
10.153.104.93:49754 ESTABLISHED
TCP 10.153.104.155:49668 10.153.104.93:49755 ESTABLISHED
TCP 10.153.104.155:49668 10.153.104.93:49757 ESTABLISHED
ТСР
10.153.104.155:49668 10.153.104.93:51514 ESTABLISHED
TCP 10.153.104.155:49668 10.153.104.93:54617 ESTABLISHED
TCP 10.153.104.155:50957 52.114.92.69:https
ESTABLISHED
TCP 10.153.104.155:52822 52.114.104.44:https
TCP 10.153.104.155:53275 104.17.27.92:https
ESTABLISHED
ESTABLISHED
TCP 10.153.104.155:53483 52.98.47.146:https
ESTABLISHED
TCP 10.153.104.155:53485 52.114.128.9:https
ESTABLISHED
TCP 10.153.104.155:53497 13.107.21.200:https
ESTABLISHED
TCP 10.153.104.155:53498 13.107.21.200:https
ESTABLISHED
TCP 10.153.104.155:53511 13.107.6.254:https
ESTABLISHED
TCP 10.153.104.155:53512 20.140.48.71:https
ESTABLISHED
TCP 10.153.104.155:53513 93.184.220.29:http
ESTABLISHED
TCP 10.153.104.155:53514 13.107.246.13:https
ESTABLISHED
Transcribed Image Text:Identify the socket pair from the output line highlighted in green color.
Your answer::
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L