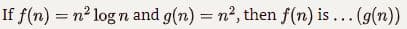
If f(n) = n^2 log n and g(n) = n^2, then f(n) is what O, Ω or Θ (g(n))
Q: 4. An ISP is granted the block 80.70.56.0/21. The ISP needs to allocate addresses for two…
A: No. of addresses= 2^11
Q: Computer science principle: which color is considered by the computer as being made up of no color…
A: In this question we have to answer for computer screen where which color is considered by the…
Q: For the following input, how many times will the for loop iterate? 7 -1 -3 -5 -14 -15 -20 -40
A: Find the required answer with reason given as below :
Q: The oldest and most wel-known (wired) communication network in the world, the telephone network,…
A: Introduction: Circuit switching is a type of network technology used in telecommunications networks.…
Q: Explain the differences between interlacing and progressive scan in video signal transmission and…
A: difference between interfacing and progressive scanning is an given below :
Q: Q1: What is an enterprise system application suite? Describe the capabilities of the individual…
A: INTRODUCTION: Corporate software, sometimes called enterprise application software, is computer…
Q: Michele is an American tourist. He is now in Jordan to visit Petra and he wants to go shopping, he…
A: Explanation: Variable used in this program US: the number of US dollars held by MicheleJOD: the…
Q: Exercise 4 Write a program that uses nested for loops to print literally the following…
A: Note: As No programming Language is mention in the question so I will answer this question using…
Q: Consider computing the overall MIPS * - for a machine A for which the following performance measures…
A: The correct answer is option a. Given, Clock Rate = 400 MHz Cycle Time ( CT ) = 1 / Clock Rate = 1 /…
Q: Because of its defining qualities, wireless networks are inherently problematic, and this gives rise…
A: Wireless networks: Wireless networks are the source of a wide variety of issues due to the basic…
Q: also known as mul
A: Introduction: Within a single process, several threads might emerge, each running independently…
Q: Consider a dataset of 10000 medical images, consisting of 80 cancer images and 9920 normal (i.e. no…
A: True Positives(TP)= 60 Here true positives are the number of positives identified in the tests…
Q: Explain the differences between interlacing and progressive scan in video signal transmission and…
A: institution: In the transmission of visual signals, distinguish between interlacing and progressive…
Q: A network engineer performs the show cdp neighbor command on a number of network devices as part of…
A: Your answer is given below.
Q: What percentage of the time can a decent compiler create better code than an assembly language…
A: Introduction: Although, on average, the compiler will do a far better job than a person would for a…
Q: What are the benefits of using a WYSIWYG editor, as well as any potential drawbacks?
A: Answer: The primary benefits of WYSIWYG HTML editors as I see them Anybody can make sites and put…
Q: Microsoft Word how-tos Title the paper. You may provide a hyperlink to an external file as a…
A: By clicking on a hyperlink in a Microsoft Word document, users may go to a different place, a…
Q: What anti-spyware software is included with Windows 7? a. Microsoft Security Essentials b. User…
A: Introduction: What anti-spyware software is included with Windows 7?a. Microsoft Security Essentials…
Q: How was the NOKIA implementing the concept of design and evaluation together? in human-computer…
A: INTRODUCTION: Nokia, along with Apple, which pioneered the smartphone as we know it today, has been…
Q: active and passive security
A: Introduction of active and passive security scanners.
Q: Why is it necessary to rearrange the database structures?
A: Introduction: Database: It is a logically organized collection of data stored on a computer and…
Q: Compare and contrast a three-tier application design with a two-tier application architecture.…
A: Introduction: In contrast to software programs that run locally and natively on the device's…
Q: Explain in your own words what the point of looking at notes in page view is. Explain. Answer in 2-3…
A: answer is
Q: When it comes to transferring data, why does TCP rather than UDP rule the roost?
A: HTTP, FTP, SMTP, and POP3 protocols need the application data to be received without gaps and in the…
Q: For the following undirected graph (unless otherwise indicated, always visit adjacent nodes in…
A: Given: To give the depth-first and breadth-first traversal of the given graph.
Q: What are the obstacles that cloud-based businesses must overcome? What are the advantages and…
A: Cloud firms, often known as Cloud Service Providers (CSPs), are businesses that provide cloud-based…
Q: : Which of the following is not aper- defined variable in MATLAP pi inf i gravity To print anew line…
A: Answer: Gravity is not a pre defined variable in MATLAP. Hence choice D. gravity is the right…
Q: Explain the three fundamental components of a database management system.
A: Intro A database management system - (DBMS) is a piece of software that allows you to access data…
Q: Explain to management what a database is and how it works?
A: DATABASE TO MANAGEMENT: The term "database management" refers, in its most basic sense, to the…
Q: What are the scenarios in which a network administrator might employ a static route?
A: Institution: Taking advantage of double parity RAID, also known as diagonal-parity RAID, Advanced…
Q: Why is authentication still an issue in today's digital age?
A: Authentication: Authentication is the process of verifying a user. This approach associates incoming…
Q: how communication occurs a cross local ethernet network
A: Introduction: A local Area Network (LAN) is a data communication network that connects multiple…
Q: build a binary search tree from the following numbers ( 1, 20, 14, 18, 7, 4, 9, 3, 5, 8, 25) then…
A:
Q: Explain the differences between interlacing and progressive scan in video signal transmission and…
A: interlacing scan and progressive scan
Q: Provide a string of length 5 that shows the ambiguity of this grammar S → Aa A|AbA|B
A: Please provide all the production rules As from the given production, string of length 5 is not…
Q: Identify and briefly outline the six basic transaction processing operations performed by all…
A: Required: Identify and briefly outline the six basic transaction processing operations performed by…
Q: What are the key advantages and disadvantages of cloud-based data storage?
A: The advantages are as follows: 1) Access your data anywhere: As data is stored remotely in cloud so…
Q: There are several reasons why magnetic tape is so popular.
A: Magnetic: Magnetic tape is a common form of data storage. It is an older technology that is…
Q: A) The path is not a circuit. B) The path is a circuit, but not an Euler circuit. C) The path is an…
A: Given graph contains 6 vertices and it contains many weighted directional edges between them. Euler…
Q: Distinguish between what a file extension is and what its purpose is in your work.
A: A file extension: A file extension (or simply "extension") is a suffix that is placed to the end of…
Q: Compare and contrast the advantages and disadvantages of using agile methods in the process of…
A: Before analysing the benefits of agile approach, it is vital to first grasp how it works. Agile…
Q: Discuss the different matlab built-in functions that are used in solving single non-linear using…
A: Ans:) Some MATLAB built in functions that are used to solve single non-linear equations are defined…
Q: What are some of the circumstances in which you would argue that it is appropriate to use code…
A: Given: The designer may programme in assembly language in terms of the machine instructions that a…
Q: marketing manager at a car accessories company wants to go through the car accessories that are…
A: The answer is given below.
Q: Regarding the incident handling procedure, this activity is done: "check that the antivirus…
A: Antivirus are tools that are made to protect a system from various kinds of fraudulent attacks.
Q: What exactly is the key distinction between connotative and denotative meanings?
A: Connotative significance is when a term offers a group of connections, or it is an imaginative or…
Q: Why is a modem essential for data exchange in computer networks?
A: A modem converts the data to a signal so it can be easily sent and received over a phone line,…
Q: The following is a list of the primary functions that an operating system is responsible for:
A: Operating System (OS): An operating system (OS) is a piece of software that serves as a conduit…
Q: What does this regex do? re.compile(r'[ckCK]ath([e]*r[yi]n[e]*|[yi])') What are 6 stings that would…
A: What does this regex do?re.compile(r'[ckCK]ath([e]*r[yi]n[e]*|[yi])') Answer: The given regex is…
Q: ONLY NEED ANSWER, DO IT FAST What block of Snap code can be used to promot a user for input? A_…
A: What block of Snap code can be used to promote a user for input? Answer: C- Ask and Want
If f(n) = n^2 log n and g(n) = n^2, then f(n) is what O, Ω or Θ (g(n))
Step by step
Solved in 2 steps

- Write a program that reads N from the user and compute the following series: (N-1)-((N-2)^2) /8+ ((N-3)^3) /27-....................+1/N^3Show that the following statements are equivalent, where n is an integergreater than or equal to 2. “n is even” and “n – 1 is odd”2. “n is even” and “n2 is even”3. “n – 1 is odd” and “n2 is even”Assume that for any integer n is greater than or equal to one prove or disprove the following a)n^2 − n + 1 is O(n) b)5^n is O(4^n) c) n(log(n))^4 is O(n^4/3)
- Prove the following: a. [(a mod n) - (b mod n)] mod n = (a - b) mod n b. [(a mod n) * (b mod n)] mod n = (a * b) mod nShow that log(n!) = O(n log(n))please answer the following A) d(n) is O(F(n)) and f(n) is O(g(n) ) show that d(n) is O(g(n)) B) show that n^3 long is omega(n^3) C) show that (summation symbol) n, i = 1 i^2 is O(n^3)

