if host1 send a connection request at t=1 and host2 send a connection request at t=1 in TCP connection, what will happen to start a connection?
if host1 send a connection request at t=1 and host2 send a connection request at t=1 in TCP connection, what will happen to start a connection?
A+ Guide To It Technical Support
10th Edition
ISBN:9780357108291
Author:ANDREWS, Jean.
Publisher:ANDREWS, Jean.
Chapter7: Setting Up A Local Network
Section: Chapter Questions
Problem 5TC
Related questions
Question
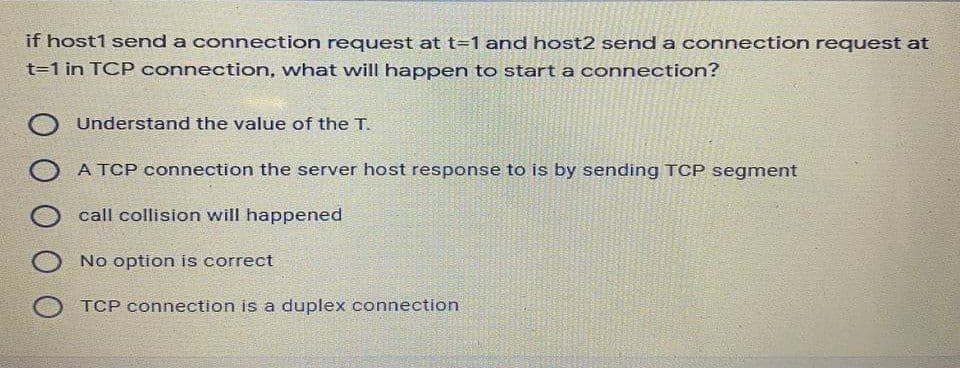
Transcribed Image Text:if host1 send a connection request at t=1 and host2 send a connection request at
t=1 in TCP connection, what will happen to start a connection?
Understand the value of the T.
A TCP connection the server host response to is by sending TCP segment
call collision will happened
No option is correct
TCP connection is a duplex connection
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Recommended textbooks for you

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning