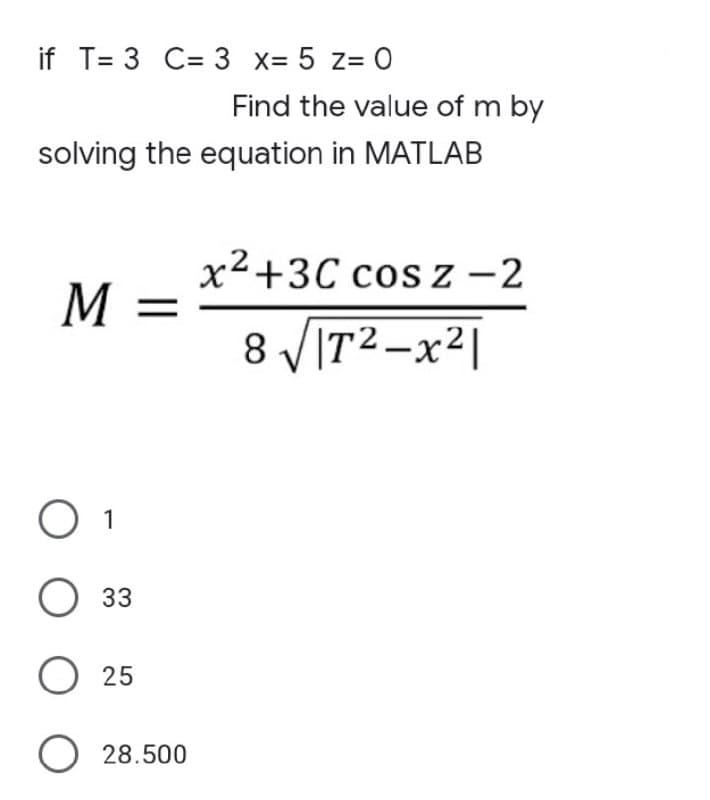
if T= 3 C= 3 x= 5 z= 0 Find the value of m by solving the equation in MATLAB
Q: The input file will be organized as follows: • The first number in the file indicates the number of…
A: Solution - Programming language used -Java All solution steps are included in program code as…
Q: How important are firewalls in network security and network defense? Explain the phrase in a…
A: Solution: In response to the query, we must explain the importance of network scanning and…
Q: In this lesson, we'll discuss the distinction between primary and candidate keys.
A: Introduction: In this lesson, we'll discuss the distinction between primary and candidate keys.
Q: When it comes to safeguarding customer data from unauthorized access, what steps should a business…
A: Introduction: Security risks are on the rise in today's world, and sadly, many organizations lack…
Q: What are the six stages of computer forensics? Any three of the six stages should be explained.
A: What are the six stages in a computer forensic investigation? Solution: Forensic Investigation is a…
Q: 4. Define a method in JAVA that should take 4 numbers as the parameters and returns the average of…
A: Given: Define a method in JAVA that should take 4 numbers as the parameters and returns the average…
Q: Assume the relation r is the only reference in the view v definition. Is it required that a user…
A: Answer: Views are virtual representations of the base table. Select access to a view does not imply…
Q: State the advantages of using pseudocode in a program development cycle.
A: answer is
Q: How will the Internet of Things (IoT) affect us? Give an example of a smart device or app.
A: Answer: The Internet of Things is still in its early stages as a peculiarity. Notwithstanding this,…
Q: What are the six stages of computer forensics? Any three of the six stages should be explained.
A: Given: The phases of identification, preservation, collection, examination, analysis, and…
Q: Write a program that will insert a word in the following sentence, "I own a blank car." that is…
A: No programming language is mentioned so we will be using python. As per the question statement we…
Q: Please describe how a company can prevent hackers from accessing its accounts and defining hacks and…
A: Introduction: Here we are required to explain how a company can prevent hackers from accessing its…
Q: a. %3D b. 17. What is the python reserved word that we use in two-way if tests to indicate the block…
A: Below is the complete solution with explanation in detail for the given question.
Q: a. Consider the following (2, 4) tree: (2, 4) Tree 4 3 6 10 What is the sequence of keys encountered…
A: Here in this question we have given a 2 4 tree and we have asked to find out the sequence for…
Q: What Makes up a Computer System's Components? Give a short summary of what you're trying to achieve.
A: DRAM: DRAM is a kind of semiconductor memory that stores data or programme code needed by a…
Q: Give a real-world example of the word "foreign key" and explain what it means.
A: - We need to talk about the foreign key.
Q: The distinction between computer organisation and computer architecture is one that may be made.…
A: Given: The properties of a system that are visible to a programmer, or, to put it another way, those…
Q: Write a C++ program that contain a menu rto call user defined functions on a one dimendional array :…
A: Solution: Given, 1- fill the array with integers >20 2- print the content of the array 3- find…
Q: What measures should be followed to assure the stability and availability of a local area network?
A: Answer :
Q: - Explain any two structures of Operating Systems Services.
A: Answer:
Q: What is the reason for a data object not being included in a data model?
A: What is the reason for a data object not being included in a data model? Data models are visual…
Q: Take WPA2 as an example of your chosen wireless access technique. What makes this choice superior…
A: WPA2: WiFi- Protected Access 2 (WPA2) is a WiFi standard. This is a wireless network security…
Q: 4. Define a method in JAVA that should take 4 numbers as the parameters and returns the average of…
A: Given: Define a method in JAVA that should take 4 numbers as the parameters and returns the average…
Q: What distinguishes a hacktivist from a cyberterrorist in your opinion? Is using hacktivists against…
A: Answer : Hacktivism is the fusion of hacking and activism; politics and technology. In essence, this…
Q: What are the issues that a simultaneous multithreading architecture in an operating system must deal…
A: Start: Parallel multithreading (SMT) is a technique for increasing the overall efficiency of…
Q: 2nd: Write a shell script program (evenodd.sh) which adds the odd numbers in odd lines and adds the…
A: ANSWER:-
Q: Compare and Contrast technical similarities and differences between TinyC, C and C++ Compilers
A:
Q: Identity theft is a widespread kind of cybercrime. Tell us about the ways in which hackers might…
A: Introduction In today's digital environment, cybercrime is one of the most common crimes. Solution:…
Q: Are context switches between processes and threads in Distributed Computing cost-effective?
A: In computing, a context switch is the procedure of storing the kingdom of a procedure or thread, in…
Q: In the OSI model, there are seven stages. Explain?
A: The Open Systems Interconnection (OSI) model defines seven layers through which computer systems…
Q: Explain how devices on one network may connect with those on another through a gateway.
A: let us see the answer:- Introduction:- Different networks, such as TCP/IP and DEC net, are connected…
Q: What do you mean by "data abstraction" and how do you define it? Describe the three main levels of…
A: Let us see the solution in the next steps
Q: Create a program that creates and runs 3 threads A, B, C and displays the string “Thread complete”…
A: C Code: #include <pthread.h>#include <stdio.h>#include <unistd.h>#include…
Q: A personal database system and an enterprise-class database system vary greatly in terms of features…
A: DBMS: DBMS refers to a database management system.Every organization has its database management…
Q: Write a python program to convert an input temperature from user in Fahrenheit to Celsius. Hint: C…
A: Solution : Here the code is implemented based on the Hint given with the question for calculating…
Q: In order to avoid being hacked or infected by a virus, what measures should a corporation take?
A: INTRODUCTION: Cybersecurity is essential for all organizations. Hackers are criminals who obtain…
Q: Give the normalized single and double-precision representation of the number -1.25 2^-4 in HEX.
A: Please upvote I am providing you the correct answer below. Please please please. Given : 0.0625 x…
Q: Question 7: Prove the non-regularity of the given language L using pumping lemma. L={a"b?na2n}
A: Pumping lemma: Pumping lemma is used to prove non regularity of the language. The regular language…
Q: Write a python program that reads the data file…
A: Code screenshot:
Q: 21. In the following code (number added), which will be the last line executés successi (1) astr -…
A: Correct Answer is a 1. After this second line will throw an error. Let us understand why
Q: Data transformation may take various shapes and forms, ranging from a simple change in data format…
A: Given: Transformation of data from one format to another, often from the format of a source system…
Q: What are the advantages of a self-descriptive database?
A:
Q: What is a conflict shift? How is it resolved in LRfamily parsers?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. In the…
Q: The hardware and software components of a computer system are inseparable. Discuss.
A: Start: Hardware and software are two sides of the same coin in a computer system. Discuss. Computer…
Q: What exactly is dynamic memory, and how does it vary from static memory, is a question many people…
A: Introduction: Dynamic memory: Its space is allocated in runtime. Facilitate the user to add or…
Q: The goal of forensic software is to give particular investigation skills, but how exactly does it…
A: Explanation: Forensic software can automate numerous review operations, in addition to taking disc…
Q: 1)what is the degree of vertex v5 2)how many paths of length 3 are between vertex v1 and v3 3)does…
A: Here in this question we have given a graph in matrix form.and from that graph we have asked to find…
Q: 1:If the hexadecimal value 0xF0A2 is a two’s complement, halfword value, what would it be in base…
A: According to the information given:- We have to choose the correct option to satisfy the statement.…
Q: Explain the importance of firewalls in network security and cybersecurity. In a commercial…
A: Firewalls: In order to adequately respond to the issue, we must first describe the significance of…
Q: *:Turing machine can be represented by state diagram
A: Thank you _______ Answer all the mentioned Transition table Queue and Input tape All of the…
Step by step
Solved in 2 steps with 1 images

- y(t) = 01 + 02x(t) + O3x² (t) + O4x*(t) + 0sx* (t) + O6x*(t) +0,x°(t) Solve tjro matlab.Plot y = cos x and z = 1- (x^2)/2 + (x^4)/24 on the same plot. And you can assume x values and then plot on matlabQ17: Given that A and B are real variables with values 1.5, and 2.5 respectively, and C is integer variable with value 3, evaluate the following: NOT (A < 0) AND (B/C <= 0).
- Write a program that computes the following: sigma summation i=0 to N (i^3 +2N)Let x(t) = u(cos(2nt)) (u(t)- u(t-2)) and h(t)=etu(t), and let y(t) = x(t) *h(t). What is the value of y (2) ? Hint: u(x) is the unit step functionLet X = {l ∈ Z | l = 5a + 2 for some integer a}, Y = {m ∈ Z | m = 4b + 3 for some integer b}, and Z = {n ∈ Z | n = 4c − 1 for some integer c}. Is X ⊆ Y ? Is Y ⊆ Z?
- Write a program to calculate the B power of Afor non-negative value of B. A" = Ax Ax A...xA Without using the pow(A,B) function.If S = { x | 0 ≤ x ≤ 10}, A = { x | 1 ≤ x ≤ 5}, B = { x | 1 ≤ x ≤ 6}, and C = { x | 2 ≤ x ≤ 7}(a) S ⋃ C(b) A ⋃ B(d) A’ ⋂ C(c) A’⋃ (B ⋂ C)(e) (A ⋂ B) ⋃ (B ⋂ C) ⋃ (C ⋂ A)write dynamic programming algorithm that accepts two whole numbers X and N and calculates the exponential XN. (Hint: XN = X times)
- If f = (log n)^2, g = n log n; what is the relationship between f and g? Choose all that applies. a. g= O(f) b. f = O(g) c. g= Ω(f) d. f = Ω(g)Write a program to compute sin(x) for given x. The user should supply x and a positive integer n, where sin (x) = x - x 3 /3! + x5 /5! - x 7 /7! + x9 /9! +……+x n /n!Given int x = 3; int y = 7; double z = 2.5; and double w = 0.5; evaluate the C++ expressions if possible (i.e., show the actual number you have computed). If it is not possible, state the reason.a) (x + y) % yb) x % y + wc) x % (y + z)d) (y + z) / w



