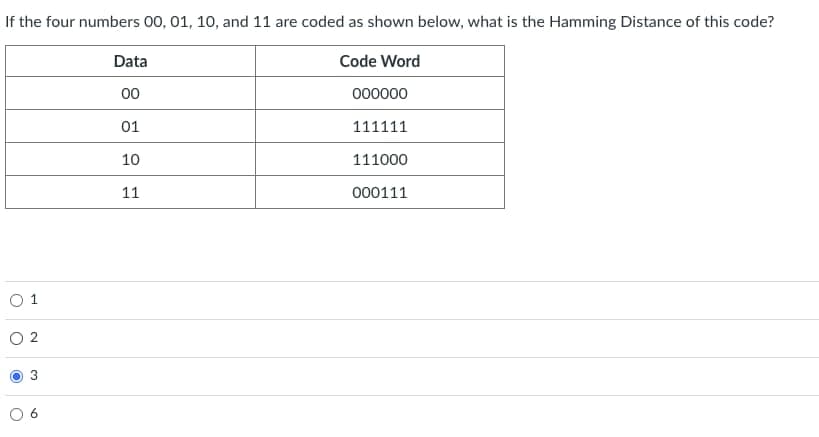
If the four numbers 00, 01, 10, and 11 are coded as shown below, what is the Hamming Distance of this code? Code Word 000000 0 1 2 Data 00 01 10 11 111111 111000 000111
Q: MIME supports multiple representations of the same content using the multipart/alternative syntax;…
A:
Q: Give an example code for bold text tag in html?
A: Given question wants a sample code in html using bold text tag.
Q: When I use the above code it is giving me a syntax error for the line rows +=1
A: Given num_rows and num_cols, print a list of all seats in a theater. Rows are numbered, columns…
Q: What benefits do dynamic routing protocols get from the passive command?
A: To dynamic routing protocols, the passive command provides: According to the status of the…
Q: For the 0-1 knapsack problem using breadth-first-search algorithm: We have 5 items with price and…
A: BFS stands for Breadth first search which is also known as level order traversal. When we are using…
Q: ARP and DNS both depend on caches; ARP cache entry lifetimes are typically 10 minutes, while DNS…
A:
Q: flip a penny and draw a marble from a bag containing 3 red. 5 orange and 2 green. Draw a tree…
A: Answer is mentioned in hand writened images, please find in below
Q: What are events in jQuery and JavaScript? Could you provide some instances of events? What does the…
A: Events in JavaScript and jQuery, how to handle such events, and their significance in interactive…
Q: What do you mean when you refer to operating systems as being partitioned? Give Their Advantages And…
A: The answer of the question is given below:
Q: What function does MVC serve in the overall design of web applications? What advantages can MVC…
A: MIC is an architectural paradigm that partitions an application into the following three logical…
Q: Write a function that inserts the nodes of a binary tree into an ordered linked list. Also write a…
A: This is due to the fact that a templated base class's derived classes inherit from templates. The…
Q: Match the literals to their respective data types:
A: There are different data types in programming language:- Integer Character String float Long…
Q: What do you mean by "partitioning" in terms of operating systems? Consider the benefits and…
A: It's a common practice in the database world to break up huge tables into smaller ones. Queries that…
Q: How does MVC contribute to the creation of web applications? How may an MVC framework be used to…
A: MVC (Model-View-Controller) : It is a product configuration design known as MVC…
Q: A set-associative cache consists of 64 lines, or slots, divided into four-line sets. Main memory…
A:
Q: Discuss the 3 key dimensions of Information Systems and apply these to Amazon, detailing each…
A: Introduction: Amazon information system is overseen, for example, the singular sub-systems the…
Q: ernet function?
A: The most fundamental function of the Internet is to pass electronic information starting with one PC…
Q: After describing the views of the user and the hardware designer on performance, compute the…
A:
Q: In general, what are the strategies for exploiting spatial locality and temporal locality?
A: Temporal locality refers to the reuse of specific data and or resources within a relatively small…
Q: How do hardware and software disruptions interact, and under what circumstances do they play a role?
A: Interrupt: A computer interrupt is a signal or circuit that instructs the computer to halt the…
Q: This question concerns the DES IP box. Please enter all answers as strings of 0's and 1's. Consider…
A: The question is to solve the question related to DES encryption.
Q: DNS servers also allow reverse lookup; given an IP address 128.112.169.4, it is reversed into a text…
A: Domain Name System • During the lookup procedure, we are required to put our faith in the Domain…
Q: Suppose three algorithms A, B, and C, can be implemented to perform a task. The algorithms have the…
A: This is a time complexity problem question. Big-Oh (O) complexity represents the worst-case time…
Q: IPv6 simplifies ARP out of existence by allowing hardware addresses to be part of the IPv6 address.…
A:
Q: Start with the biggest element of the AWS Global Infrastructure and work your way down to the…
A: Start with the biggest element of the AWS Global Infrastructure and work your way down to the…
Q: rmation security, what exactly is privacy? Do all age groups have the sa
A: Introduction: While protection is essentially a security feature, privacy is sometimes defined as…
Q: Base on the Relationship diagram. 19.Display the date of the most recent departure flown by each…
A: Based on the relationship diagram the sql quires are represented in Step 2.
Q: In Html show a strikethrough text in webpage?
A: HTML uses <s></s> tag to strikethrough any text in webpage. I am showing that it in next…
Q: Exercise 5: ■ Write a program that finds the summation for the odd and even numbers [for the numbers…
A: 1.Write a program that finds the summation for the odd and even numbers [for the numbers from 0 to…
Q: Which event delegation model should we employ when creating a graphical user interface (GUI)
A: When creating a GUI, we should employ an event delegation model. This model involves having a single…
Q: Please DRAW the nondeterministic pushdown automaton that relates to the grammar below here. Prove…
A: ((s0, e, e),(s1, S)((s1, a, S),(s1, BBBB) ((s1, a, S),(s1, BBBB) ((s1, a, S),(s1, BB) ((s1, b,…
Q: Explain the differences between the internet, intranet, and extranet
A: Internet This is the global network of computers available to anybody who knows their Internet…
Q: How Can I As A Reader Get My Browser To Recognize My Own Style Sheet?
A: Different Types of browsers are considered here, I am considering Netscape and Internet Explorer 4.0
Q: What does Interrupt Processing really mean?
A: Interrupt: Any processing that needs other work besides the processing of the jobs is done via…
Q: Why we like the GUI programming of the event delegation approach. Describe with suitable instances
A: The modern approach handle events is based on the delegation event model. The delegation event model…
Q: Which event delegation model should we employ when creating a graphical user interface (GUI), and…
A: Graphical User Interface: A graphical user interface (GUI) is a sort of user interface that is…
Q: List three distinct applications or systems that employ DWH, along with an explanation of its usage.
A: Data warehouse: It is a method for gathering and overseeing data and that data is utilized for…
Q: After describing the views of the user and the hardware designer on performance, compute the…
A: Introduction: The Common Industry Specification for the Usability Requirements (Theofanos, 2006)…
Q: Potential usage of blockchain technologies in fields other than crypto currency?
A: Blockchain technology Blockchain is the basic technology that empowers all the cryptographic forms…
Q: What Is the Distinction Between Identity and Class?
A: ID is used when defining a style for one and only one element, whereas class is used when applying a…
Q: For the cache design of the preceding problem, suppose that increasing the line size from one word…
A: As referred to answer for section 4.27 in the textbook, it is known that the Miss penalty for cache…
Q: We are going to create a virtual gateway to solve the gateway problem. Between R1 and R2 we will…
A: Introduction: Below describe the best protocols to create a virtual gateway to solve the gateway…
Q: What are the differences among sequential access, direct access, and random access?
A: In this access method, the memory is accessed in a specific linear sequential manner, like accessing…
Q: Consider the following table employees temployee_id, first name, last name, email, phone number,…
A: Below is the correct answer to above question. I hope this will be helpful for you...
Q: What are writing advantages of using library functions. own function in C program? our over
A:
Q: Write the function int isEven (int x); that returns 1 if x is an even number; otherwise, it returns…
A: please check the step 2 for required c++ code and step 3 for output.
Q: Which of the following statements about JavaFx elements is true? Question 1 options: A Node…
A: Correct Answer is " OPTION - A " So, Correct Answer is " A Node can be placed in a Pane. "
Q: What exactly is the SDLC and what are its stages?
A: SDLC: Change in systems A quality system that meets or exceeds customer expectations is delivered…
Q: Question 2 What is wrong with the following for testing if a vector is sorted? v== sort(v) Matlab It…
A: Answer..
Q: What do you precisely mean when you talk about "partitioning" in terms of operating systems?
A: Operating System: Its operating system is software that controls all other application programs in a…
Step by step
Solved in 2 steps with 2 images

- In the following code, what is the minimum distance for the code? What is the best situation we might hope for in connection with error detection and error correction? (011100) (011011) (111011) (100011) (000000) (010101) (110100) (110011)1. Express the following Excess-3 codes as decimals: 1000001101102 and 01111100100101102. 2. Express the following decimal numbers in Excess-3 code form: 24510, 73910, and 456710.If 8 decimal digits only are allowed, then the rounded representation of the number 0.1234567890.123456789 is 0.123456790.12345679. Select one: True False
- If you store the number 3 using IEEE-754, what will be the 8-bit Exponent? 11001101 10000000 10100011 00110110The assignment is: Determine the decimal value of the following unsigned binary numbers: A. 11000 B. 110001 C. 1111111 D. 1000000000 Please show the end result and please explain how you got the results.Convert the following binary numbers to the decimal number system. kindly and please show all steps clealry a) 0000 0100 b) 0010 0111 c) 0111 0100 d) 1011 0101 e) 1111 1100
- What is the decimal representation of each of the following unsigned binary integers? c. 11110000What decimal number does the bit pattern 0×0C000000 represent if it is a floating point number? Use the IEEE 754 standard.What is the lowest number of bits (digits) required in the binary number approximately equal to the decimal number 0.611710 so that the binary number has the same or better precision?

