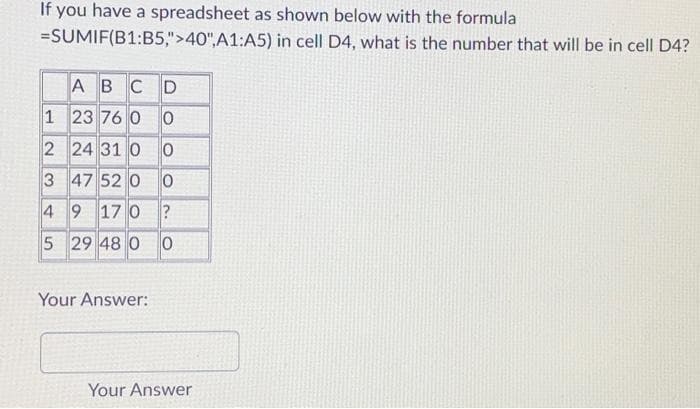
If you have a spreadsheet as shown below with the formula =SUMIF(B1:B5,">40",A1:A5) in cell D4, what is the number that will be in cell D ABCD 1 23 76 00 2 24 31 00 3 47 52 0 0 4 9 170? 5 29 48 0 0 Your Answer:
Q: What is BIOS (Basic Input/Output System) on a motherboard, and why is it essential for system…
A: Regarding computers, BIOS (Basic Input/Output System) is a firmware part found on the motherboard.It…
Q: Explain the concept of data fragmentation and distribution in DDBMS. Provide an example.
A: In Distributed Database Management Systems (DDBMS) data fragmentation and distribution strategies…
Q: Discuss the CAP theorem and its relevance in the context of distributed databases.
A: The CAP theorem, also known as Brewer’s theorem, is a concept in distributed systems and databases.…
Q: Discuss the concept of data fragmentation in distributed databases. How does horizontal and vertical…
A: Hello studentGreetingsIn the realm of distributed database systems, the concepts of horizontal and…
Q: What is the CAP theorem, and how does it relate to distributed databases? Discuss the trade-offs…
A: The CAP theorem, also known as Brewer's theorem, is a fundamental concept in distributed systems and…
Q: Explain the concept of data transparency in distributed databases and its significance in data…
A: Data transparency in distributed databases refers to the ability of a distributed database…
Q: Compare and contrast the advantages and disadvantages of using a wired Ethernet connection versus a…
A: Wired Ethernet and wireless Wi-Fi are two primary methods of connecting devices in a home…
Q: challenges associated with ensuring the security and privacy of IoT devices an
A: In today's interconnected world, the Internet of Things (IoT) is transforming how we interact with…
Q: Analyze the potential environmental impacts of a massive deployment of IoT devices. How can IoT be…
A: Internet of Things (IoT) devices refer to a diverse range of interconnected, sensor-equipped objects…
Q: Investigate the role of motherboard BIOS/UEFI updates in maintaining system security and…
A: System Security:System security refers to the set of measures, practices, and technologies put in…
Q: Analyze the potential biases and ethical considerations in data analysis, especially in AI-driven…
A: When it comes to AI-driven decision systems, analyzing data brings up biases and ethical…
Q: What are some key industries that extensively use IoT applications, and how does IoT benefit them?
A: The use of the Internet of Things (IoT) has brought changes, to industries.By connecting objects to…
Q: In the context of machine learning, discuss advanced methods of feature selection and dimensionality…
A: Feature selection and dimensionality reduction are critical steps in the machine learning pipeline…
Q: Explain the concept of edge computing in the context of IoT. How does it address latency and data…
A: Edge computing is a paradigm in computing that has gained significant importance in the context of…
Q: How does data quality impact decision-making in organizations, and what are some common data quality…
A: The quality of data plays a role in shaping how organizations make decisions.When data is of quality…
Q: How can persuasive technology be applied to influence healthy behaviors in users? Provide practical…
A: Persuasive technology refers to digital tools and devices designed to change users attitudes or…
Q: Discuss the challenges associated with big data analysis and the potential benefits it offers to…
A: In this question we have to understand about the challenges associated with big data analysis and…
Q: What are some common real-world applications of IoT technology in the healthcare industry?
A: The term "Internet of Things" (IoT) technology describes a network of interconnected physical…
Q: Provide a detailed overview of IoT applications in the automotive industry, including connected…
A: The Internet of Things (IoT) has revolutionized the automotive industry, leading to the emergence of…
Q: Critically assess the role of ethnographic research in gaining insights and conducting analysis in…
A: Ethnographic research is a qualitative research approach that entails extensive and extended…
Q: the Fogg Behavior Model and its relevance in designing persuasive technology. Provide real-world…
A: The question asks for an explanation of the Fogg Behavior Model, its relevance in designing…
Q: Explore the concept of distributed data warehousing for global organizations. How can data from…
A: In the ever-evolving landscape of business intelligence (BI), the principles of distributed data…
Q: Analyze the role of IoT in smart agriculture. Provide specific examples of how IoT technologies can…
A: The Internet of Things (IoT) plays a role in modernizing and perfecting farming practices within…
Q: What is the significance of the BIOS (Basic Input/Output System) on a motherboard? How does it…
A: The Basic Input/Output System (BIOS) plays a role in the functioning of a computer.The firmware is…
Q: What is a distributed deadlock, and how can it be detected and resolved in a distributed database…
A: A distributed deadlock in a distributed database occurs when multiple transactions, running on…
Q: Analyze the role of machine learning and artificial intelligence in enhancing IoT applications.…
A: Machine Learning (ML) and Artificial Intelligence (AI) play pivotal roles in enhancing Internet of…
Q: Describe the process of query processing in a distributed database system. What are the key…
A: Query processing in a distributed database system involves the evaluation and execution of queries…
Q: What are some key industries that extensively utilize IoT technologies for various applications?
A: Given,What are some key industries that extensively utilize IoT technologies for various…
Q: Explain the concept of IoT ecosystems and their importance in the development of IoT applications.
A: The Internet of Things (IoT) refers to a network of devices or "things" that communicate and share…
Q: How does a distributed query processing system work? Provide an example scenario.
A: A software element that handles and coordinates the execution of database queries across several…
Q: Explore the use of IoT in industrial automation. What are the advantages and potential risks of…
A: Industrial automation is the practise of automating manufacturing and industrial processes in order…
Q: Explore innovative methods of analysis, such as sentiment analysis of social media data or network…
A: In recent times there has been a growing interest in the use of analysis methods across various…
Q: Discuss the challenges of real-time rendering in the gaming industry. How do hardware advancements…
A: In the gaming industry, real-time rendering is about generating and displaying graphics to create…
Q: How does data replication work in a distributed database system, and what are the benefits and…
A: Data replication in a distributed database system involves copying and maintaining the same data…
Q: What are the challenges associated with achieving realistic lighting and shading effects in the…
A: 3D, short for three-dimensional, refers to the representation of objects or environments in a space…
Q: Discuss the steps involved in conducting a PESTEL analysis and its application in strategic…
A: PESTEL analysis is a framework used to evaluate and analyze the macro-environmental factors that can…
Q: Describe the basic components found on a typical motherboard, including CPU socket, RAM slots, and…
A: A motherboard, also called a mainboard or system board, is a computer's printed circuit board…
Q: Explore the role of PCIe (Peripheral Component Interconnect Express) slots on a motherboard. How are…
A: PCIe slots on a motherboard play a role in expanding a computer’s capabilities.These slots enable…
Q: Discuss the role of IoT in healthcare. Provide examples of IoT applications in the healthcare…
A: The integration of the Internet of Things (IoT) into the healthcare business has heralded a new era…
Q: Explore the role of persuasive technology in healthcare, specifically in encouraging healthy habits…
A: In healthcare, technology has made strides in influencing individuals’ behaviors, promoting habits,…
Q: Describe three real-world applications of IoT technology and explain how they benefit businesses or…
A: The Internet of Things (also abbreviated as IoT) technology emerged from a convergence of various…
Q: Explore the concept of Digital Twins in IoT. How do they contribute to real-time monitoring and…
A: Digital Twins are replicas of objects or systems on the Internet of Things (IoT).They are created…
Q: write a C++ program. In the heyday of the British empire, Great Britain used a monetary system based…
A: Initialize Variables:Declare three integer variables: pounds, shillings, and pence.Input:Prompt the…
Q: Analyze the role of the motherboard in supporting advanced storage technologies like NVMe SSDs and…
A: Motherboard: A motherboard is the main circuit board in a computer that houses the central…
Q: Explain the concept of data replication and its benefits in distributed DBMS. What strategies can be…
A: To ensure effective data processing and storage across several sites, a distributed database is…
Q: Describe the concept of sharding in NoSQL distributed databases and its advantages.
A: NoSQL distributed databases are a subset of database management systems created to manage…
Q: Discuss the concept of data fragmentation and allocation in a distributed database, including its…
A: In a distributed database system, data fragmentation and allocation are crucial aspects that…
Q: Describe the concept of data replication in distributed databases. What are the benefits and…
A: Data replication in distributed databases refers to storing copies of the same data across multiple…
Q: Discuss the role of IoT in healthcare. What applications are transforming the healthcare industry?
A: The integration of the Internet of Things (IoT) into the healthcare sector has ushered in a…
Q: Analyze the long-term effects of persuasive technology on user behavior and well-being
A: Persuasive technology refers to systems that aim to influence users' behavior and attitudes using…
Step by step
Solved in 3 steps

- Y7 Construct a spreadsheet that estimates what the maximum social security payment will be in 40 years based on the following criteria: Retiring at age 70 (current maximum monthly Benefit is $4,555) The average Cost-Of-Living-Adjustment (COLA) of 3% Please build a spreadsheet like the one used in last weeks module that shows the year (working backwards from age 70 in forty years (ie your hypothetical is of a 30 year old) Using that spreadsheet, tell me how much that payment would be in todays dollars assuming a 2.5% inflationary factorThe small black square in the lower right corner of a selected spreadsheet cell is called the: range finder data marker fill handle value axisIn designing a spreadsheet, it is a good idea to embed numeric constants in formula? A.True B. False
- From worksheet Laptop, in cell I5, find the category if : 600 < Price <=1030 then Category is “C1” 500< Price <= 600 then Category is “C2” 400< Price <=500 then Category is “C3” Price <=400 then Category is “C4” Replicate the formula to the cell range I6:I13.Imagine a spreadsheet with the following rows: NAME AGE WINS Samantha 15 8 Carrie 22 5 Charlotte 38 3 Miranda 19 9 The first row is a header. By default, sorting on Name, what would the rows look like? Which non-header row would be first if you sorted on WINS using Excel’s default sort option?Scenario: You are the inventory manager of an automotive parts distributor. From experience, you know that you will need to reorder parts when inventory reaches a certain level. In the Parts spreadsheet, expand the spreadsheet to show that you will need to reorder parts when they get below the order point. Modify the spreadsheet to add a column saying "order more" or "available." Write the formula that you used in cell E2 to accomplish this:
- The following table shows a list of pets and their owners that is used by a veterinarian service. P_Name Type Breed DOB Owner O_Phone O_E-mail Kino Dog Std. Poodle 3/27/97 M. Downs 5551236 md@abc.com Teddy Cat Chartraux 4/2/98 M. Downs 1232343 md@abc.com Filo Dog Std. Poodle 2/24/02 R. James 2343454 rj@abc.com AJ Dog Collie Mix 11/12/95 Liz Frier 3456567 liz@abc.com Cedro Cat Unknown 12/10/96 R.James 7865432 rj@abc.com Woolley Cat Unknown 10/2/00 M. Trent 9870678 mt@abc.com Buster Dog Collie 4/4/01 Ronny 4565433 ron@abc.com a. Describe 4 problems that are likely to occur when using this table. b. Break the table into two tables in a way that fixes the four problems.INSTRUCTIONS Using spreadsheet software enter the following table below that shows the number of tourists visiting the following countries over a five-year period. Use Times New Roman and Font size 12. Name the worksheet Table. COUNTRIE S 2014 2015 2016 2017 2018 ‘000 ‘000 ‘000 ‘000 ‘000 Grenada 350 465 375 250 485 Antigua and Barbuda 153 160 155 149 256 Barbados 573 625 725 680 740 St. Kitts 347 515 538 178 384 St. Lucia 600 436 368 535 858 Trinidad and Tobago 379 563 475 415 563 Jamaica 416 200 500 300 475 Bahamas 300 450 550 460 470 Aruba 208 367 415 500 684 Dominica 135 317 279 350 465 Insert a column to the right of the table with the heading “Total Visitors”. In that same column compute the total number of tourists that visited each country over the years. Insert a row heading Maximum to show the maximum number of visitors for each given year. Sort the data in ascending order based on the Countries. Insert a row heading Minimum to show the minimum number of visitors for…Write a SQL query to delete all duplicate email entries in a table named Person,keeping only unique emails based on its smallest Id.+----+------------------+| Id | Email |+----+------------------+| 1 | john@example.com || 2 | bob@example.com || 3 | john@example.com |+----+------------------+Id is the primary key column for this table.For example, after running your query, the above Person table should have thefollowing rows:+----+------------------+| Id | Email |+----+------------------+| 1 | john@example.com || 2 | bob@example.com |+----+------------------+Note:Your output is the whole Person table after executing your sql. Use deletestatement.
- Don't you dare give me AI generated answer or plagiarised answer. If I see these things I'll give you multiple downvotes and will report immediately. This is Java query.For a day, monitor your queries on a search engine. Suppose someone had access to those queries, knew they came from you, and knew your name. Might an analyst derive any wrong inferences about you from your queries?Suppose that a website contains two tables, the Customers table and the Orderstable. Write a SQL query to find all customers who never order anything.Table: Customers.+----+-------+| Id | Name |+----+-------+| 1 | Joe || 2 | Henry || 3 | Sam || 4 | Max |+----+-------+Table: Orders.+----+------------+| Id | CustomerId |+----+------------+| 1 | 3 || 2 | 1 |+----+------------+Using the above tables as example, return the following:+-----------+| Customers |+-----------+| Henry || Max |+-----------+

