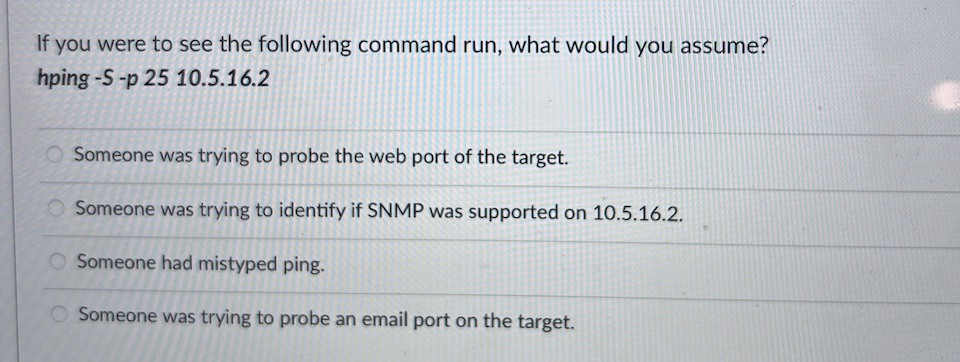
If you were to see the following command run, what would you assume? hping -S-p 25 10.5.16.2 Someone was trying to probe the web port of the target. Someone was trying to identify if SNMP was supported on 10.5.16.2. O Someone had mistyped ping. Someone was trying to probe an email port on the target.
Q: What tool should John (White-hat tester) use for his website penetration assignment for searching…
A: what too should john use for his website penetration assignment for searching common…
Q: How can data collection methods be enhanced in order to increase the quality of data stored in…
A: Answer:
Q: To interact with other devices using IPv4, a host must be able to connect to a network and use one…
A: Unicast communication refers to one-to-one communication between a single source and a single…
Q: A centralized database and a distributed database are two instances of this.
A: A database, or electronic database, is a collection of data or information that has been primarily…
Q: A new user wants to access their account information on a bank's website. Considering the privacy…
A: - We need to talk about the multi factor authentication that can be used in a bank. - The options…
Q: Are there any benefits to using cloud computing over on-premises systems? What are the hazards and…
A: Given: The ease with which cloud solutions may be accessible is another advantage over on-premise…
Q: Every company should know how to archive data.
A: Information that has been transformed into a more efficient form for movement or processing is…
Q: What is the rationale behind using Histogram of Oriented Gradient (HoG) features instead of…
A: Answer: The rationale behind using Histogram of Oriented Gradient (HOG) features instead of…
Q: Harris Corner Detector aims to find such points in the image where the cornerness function has:…
A: Answer: λ1 and λ2 are the eigenvalues of M. So the upsides of these eigenvalues conclude whether…
Q: a) You are the network administrator for the Commtel Telecom Company. Domain controllers are running…
A:
Q: What are the components of a CPU?
A: What are the components of a CPU? Lets see the answer in step 2
Q: What are the parts of a CPU, and how are they connected?
A: Introduction: The operating premise of a computer is that it is essentially a computational…
Q: Q17
A: Given question are multiple choice selected.
Q: Completely grasp the notion of social networking. What is autonomous computing, and what function…
A: Using online social media to engage with friends, family, or classmates is known as social…
Q: PLEASE DEFINE!!!!! WITH SAMPLES Define the following: 1. flip-flops 2. state table 3. state…
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly…
Q: There are two sorts of data flow charts, and this article will describe the distinctions between…
A: DFD (Data Flow Diagram): A data flow diagram (DFD) shows how data moves through a system or process.…
Q: B. Given a block of IP addresses represented by 192.168.200.0/24, you are being asked to create one…
A: Introduction: Given IP Address: 192.168.200.0/24 /24 indicates that there are 24 network bits and 8…
Q: What is the return type open() ?method in ofstream library
A: Answer: open() method returns a boolean value indicating whether the file is opened or some error…
Q: IP addresses play a crucial function in computer networks, and understanding what they signify and…
A: Introduction: A computer's internet protocol (IP) address permits it to send and receive data over…
Q: Write a program called "pointerArray.cpp" using knowledge of pointer. The program must illustrate…
A: I give the code in C++ along with output and code screenshot
Q: Explain the significance of distinguishing between the development of user requirements and the…
A: Given: Requirements for Users and System RequirementsThe following activities make up the…
Q: What concerns does database use offer to people's privacy and civil liberties?
A: Start: The purpose of this inquiry is to draw attention to the dangers that databases pose to…
Q: What is the orientation relationship between an edge and its gradient?
A: Thank you _______ The gradient will be steepest when it is perpendicular to the edge of the…
Q: What is the return type open() ?method in ofstream library С++ Answer
A: - We have to talk about the return type of the open() function in ofstream library in C++.
Q: What is swapcase() function in the Python?
A: Python is a programming language for creating the websites and software, as well as automating…
Q: How are the data obtained for each database? If so, can you obtain a list of what each database…
A: The collecting of information is known as data collection or needs gathering. In each database, the…
Q: Consider the following non-invertible affine transformation: A :V → W that collapses the vector…
A: Answer: Consider the following non-invertible affine transformation: A: V → W that collapses the…
Q: Given an integer array nums that may contain duplicates, return all possible subsets (the power…
A: Powerset - Any set which has all the subsets including empty and the set itself is called a…
Q: What is the purpose of the Python's swapcase() function?
A: swapcase() method returns the string where all uppercase characters are converted to lowercase, and…
Q: C language implement a normal distribution number generator.
A: C Program: #include <stdlib.h>#include <math.h>#include <time.h>#include…
Q: Consider this: Database management technologies and data warehousing strategies are today's largest…
A: Database Management System: Management system for databases. Connolly and Beg define a database…
Q: Write a program that enters a set of numbers and calculates only the frequency of the number 5,…
A: I give the code in C++ along with output and code screenshot
Q: Q23
A: Answer c is correct Text files including the text Administrator:500:
Q: How to remove whitespaces from a string in Python?
A: whitespace is a pre-introduced string utilized as string steady. In Python, string. whitespace will…
Q: The Transport layer is where firewalls do their function. In other words, they may execute the…
A: The issue is whether a firewall can serve as a router. A router is referred to as the connecting…
Q: Browser-to-server communication may be made more secure by using SSL or TLS.
A: HTTPS: Secure Hypertext Transfer Protocol HTTPS is an extension to HTTP that provides secure network…
Q: Which of the following image regions contain useful keypoints for feature extraction? Şelect one: O…
A: According to the information given:- we have to choose the correct option to satisfy the statement.
Q: How does a one address instruction handle operations that require two operands (like addition)?…
A: One address format: Here One of the operand is in the accumulator and the other is in the register…
Q: A system requirements engineer should demonstrate how to keep track of both functional and…
A: First, let us discuss what is functional and non-functional requirements:- Functional requirements…
Q: What is the Internet's underlying mechanism?
A: Justification: The internet is a worldwide computer network that distributes a wide variety of data…
Q: What is utilized to improve the design of the system? Design of the body Planned approach What's the…
A: Physical design : "logical design" refers to an abstract representation of the system's data flow,…
Q: Process data flow diagram questions: how to explain and evaluate?
A: Data-flow diagram A data flow diagram (DFD) visually depicts how data flows through a system or…
Q: Write a C++ program to generate a random vehicle registration number that is a string of length 10…
A: -> I explained the code in the comments of the program. -> in this problem i use rand()…
Q: What are the main differences between hardware and software? What similarities do they share?
A: To find differences between hardware and software, and their similarities.
Q: What is the return type open() ?method in ofstream library C++ Answer
A: We are asked the return type of open() method in ofstream library. I have attached the solution in…
Q: How may a company set up a DNS server for usage on their own network?
A: How would a business setup a DNS server for its network? A DNS server is a computer that has been…
Q: inction between wireless networking issues that may develop when two stations are simultaneously…
A: Introduction: Below the distinction between wireless networking issues that may develop when two…
Q: The distinction between data and information may be explained by using examples.
A: answer is
Q: It is impossible to store both data and instructions in the sa
A: It is impossible to store both data and instructions in the same area in the Hack design. In what…
Q: How to remove leading whitespaces from a string in the Python?
A: strip() - function in python remove the leading and trailing whitespaces from string. lstrip() -…
Q25
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- The netstat programme, available for Linux and Windows, provides a list of active network connections. Describe how to use this command to identify whether a web page is not terminating connections or, if connection pooling is being used, is not returning connections to the pool. You may do this by looking at whether or not the connection is being returned to the pool. There is a possibility that connection pooling will not immediately terminate the connection.For this lab, you will write a shell script called nethelper.sh that: 1. Reads in a list of hosts from a host file that is passed in as a parameter 2. Repeatedly, until the user selects quit (q), ask the user if the user wants to ping a host or look up a hosts DNS name 3. Once the user has selected an action, prompts the user for which host and then applies the action. Note that for the ssh action, the script must also ask the user for the user name that will be used to log into the host. Step 1 To accomplish step 1 above (reading in a list of hosts from a file), you will write a function called read_hosts. Functions in bash scripts have the following syntax: function name { # function body goes here } You can put any bash syntax inside the function as the function body. Also, note that the parameters to a function act like the parameters passed in at the command line. In other words, the parameters to the function are place in variable named $1, $2, and so on. So, how do you read the…Hello, I am struggling with this assignment. I have a Ubuntu VM built out in AWS and i got a firewall shell script built out and ran on the server. But this instructor calls for testing inbound connection, like web, email, etc. How do I test this if it's just a plain Ubuntu build, no desktop? After that he wants us to modify the script to allow just SSH, HTTP and HTTPS and test those connections TO the machine. How do I do this? Did I set this firewall script up correctly? And how do I test steps 2 and 3 for just a plain jane Ubuntu command line only server? Install and configure a Linux operating system (e.g. Ubuntu, Fedora, Debian) on a virtual machine or physical machine. --> You can use an EC2 instance in AWS or DigitalOcean. Install the iptables firewall tool using the package manager of the Linux operating system you installed in step 1 (e.g. sudo apt-get install iptables for Ubuntu). 1. Create a firewall script that blocks all incoming traffic except for incoming SSH…
- An attacker tries to do banner grabbing on a remote web server and executes the following command:$ nmap -sV hackme.com -p 80 He gets the following output:Starting Nmap 7.90 ( http://nmap.org ) at 2020-09-26 22:47 ESTNmap scan report for hackme.com (108.58.137.114)Host is up (0.048s latency).PORT STATE SERVICE VERSION80/tcp open http Apache httpdService detection performed. Please report any incorrect results at http://nmap.org/submit/.Nmap done: 1 IP address (1 host up) scanned in 7.36 seconds What did the hacker accomplish? nmap can’t retrieve the version number of any running remote service. The hacker successfully completed the banner grabbing. The hacker should have used nmap -O host.domain.com. The hacker failed to do banner grabbing as he didn’t get the version of the Apache web server.Write a script to find and print a "ping sweep"? Use the following code: import os my_ip="192.168.10.103" # sub your ip address os.system('ping -n 4 {}'.format(my_ip))How would someone go about doing the following? A RedHat9 VM machine is hosted in a structure with the IP address: 10.11.19.12. There is an nweb service on port 7684. You will write an exploit to theintended target. Your exploit will be sent to the target machine and must return a shell to a controller machine at the IP address 10.11.19.11. You will be using a Kali Machines metasploit to do this.
- Step 1: Write a script to find and print your local IP address Use the following code: import socket hostname = socket.gethostname() local_ip = socket.gethostbyname(hostname) print(local_ip) Step 2: Write a script to find and print your OS platform and release (for example, "Windows version 10") Use the following code: import platform print(platform.system ()) print(platform.release ()) Step 3: Write a script to find and print a "ping sweep"? Use the following code: import os my_ip="192.168.10.103" # sub your ip address os.system('ping -n 4 {}'.format(my_ip)) Step 4: Write a script to find and print current day and time import time now = time.localtime() print(time.strftime("%m/%d/%Y %I:%M:%S %p", now)) Extra Credit: Add code to Step#4 which prints a greeting, either "good morning", "good afternoon", "or good evening", depending on the current time.Assume a web server can only receive TCP connections on port 80 (HTTP) and 22 (SSH), but not on any other ports. The web server can only establish connection to a database server hosted on private IP 192.168.100.100 on port 3000, but to no other machines inside or outside the network. Imagine this web server is running Linux, and we’re using iptables to define host-based firewall rules for it. Show the set of iptables commands to install necessary rules for this security policy.In which of the following applications, UDP is a suitable transport layerprotocol? (a)In SMTP, a user can send a long e-mail message, which may includemultimedia. When a user sends a message, the recipient does not expectto receive a response quickly. (b)A user needs to download a very large text file from the internet. Theuser doesn’t want part of the file to be missing or corrupted when he/sheopens the file. The delay created between the delivery of the parts arenot an overriding concern for him. (c)In DNS, a client needs to send a short request to a server and to receive a quick response from it. The request and response can each fit in one userdatagram.
- On servers with Linux operating system, access logs are kept under which of the following directories by default?A) /var/log/B) /var/log/auth/C)/log/D)/log/auth/ Which of the following would an attacker prefer to run operating system-level code with MSSQL?A) MSSQL cannot run code at the operating system level.B) MSSQL agentC) xp_cmdshellD) There are no options. As a network administrator, you want to reduce the attack surface on your systems. Which of the following helps?A) Creating shared folderB) Make sure that only the necessary services are activeC) To record access activitiesD) monitor network traffic Which of the following products can an institution prefer to use if its antivirus software is up-to-date on the computers in its network?A) FirewallB) DLPC) Web ProxyD) NAC When John enters the mobile banking app on his smartphone, he sees his account balance is decreasing. What would it be better for John to do first to fix this situation?A) Closing and reopening the mobile…Assume that our LastPass web server is configured to use port 7777 rather than the default HTTP port. Also assume that two users on the website, X and Y, are using their home computers to visit the web server at the same time. Are all of the requests from X’s computerand Y’s computer being sent to the same socket at the web server? If yes, how does the webserver distinguish the requests from different clients? If not, do the different sockets both have port 7777? Why? Assume that the LastPass web server uses persistent connections.1. Persistent HTTP requires?a. 2(round trip times) + file transmission timeb. as little as two RTT for all the referenced objectsc. one file transmission timed. as little as one RTT for all the referenced objects 2. UDP has no connection between client & server?a. RCVR extracts sender IP address and portb. sender explicitly attaches IP destination address and portc. three other answers are incorrectd. no handshaking before sending data 3. A socket in computer networks is correctly defined as?a. A combination of IP address and port number, connected by a "/" symbolb. sender explicitly attaches IP destination address and portc. RCVR extracts from the socket, sender IP address and portd. A combination of IP address and port number, connected by a"." symbol 4. The data link layer provides?a. the functional and procedural means to transfer data between network entities and the means to detect and possibly correct errors that may occur in the link layer.b. the functional and procedural…

