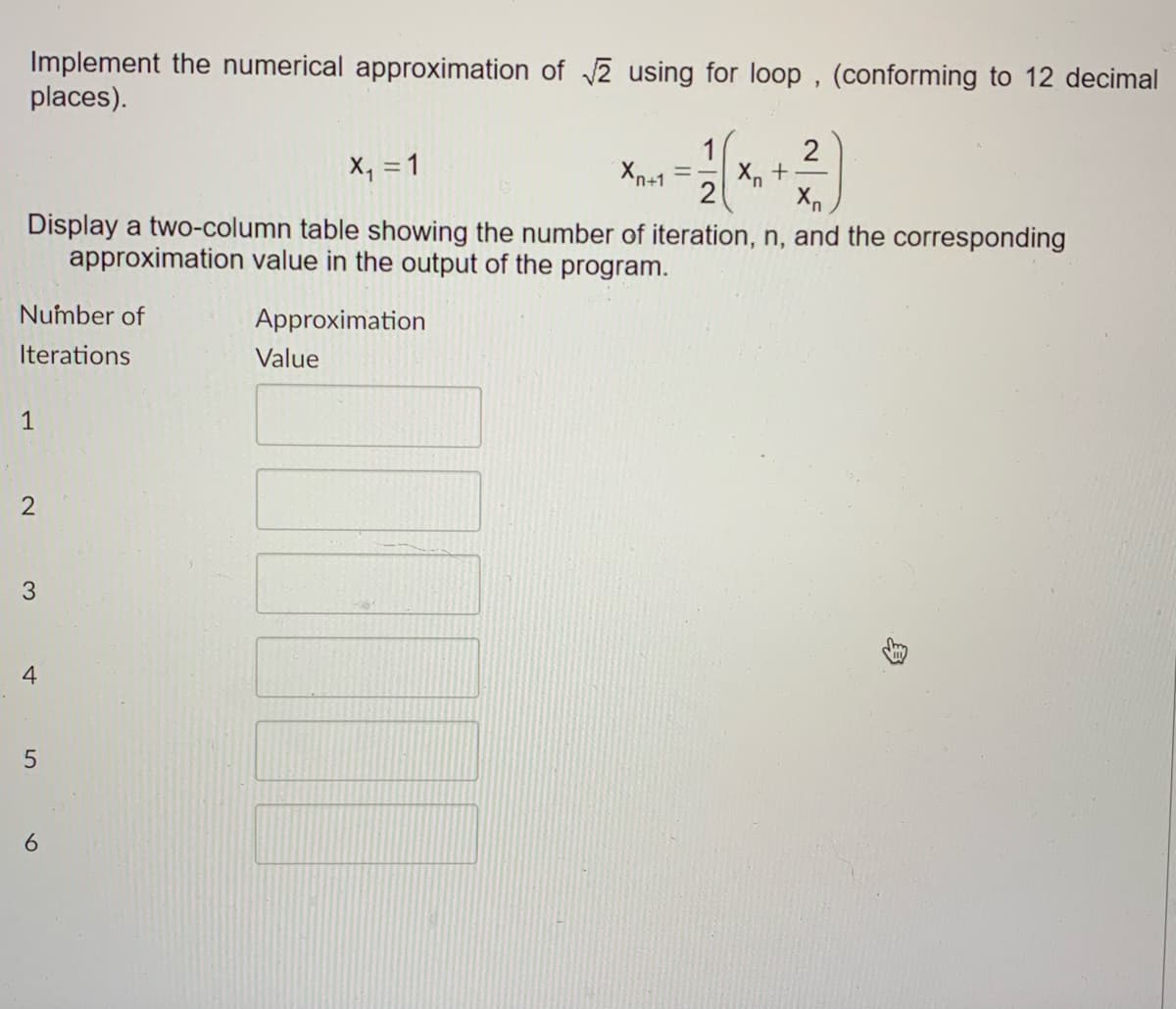
Implement the numerical approximation of √√2 using for loop, (conforming to 12 dec places). 2 X₁ = 1 Xn+1 == Xn + 2 Xn Display a two-column table showing the number of iteration, n, and the corresponding approximation value in the output of the program.
Q: Consider, for instance, the database of a large airline that relies on snapshot isolation in its…
A: Introduction: Consider, for instance, the database of a large airline that relies on snapshot…
Q: What are some of the things that you might put in the abstract for the purpose of developing your…
A: Abstraction: An abstraction is a piece of the software that conceals low-level information in favor…
Q: Discuss in brevity the most suitable technology. Recognize and explain how a particular piece of…
A: With the advent of technology in modern times, there are innumerable tasks that are being done with…
Q: Think about the ways in which you can use Structured English to explain processes that aren't…
A: Institution: The process of studying a method or company to discover its goal and objectives and…
Q: Should we use a synchronous or an asynchronous bus when connecting the central processing unit (CPU)…
A: The above question is solved in step 2:-
Q: What are the key differences between the Core i3 architecture and the ARM architecture?
A: Core i3 processor The graphics of the Core i3 processor are integrated. Core i3 is compatible with…
Q: write a code in c++ to solve any question with any function an any value to solve using newton…
A: Program in c++: #include<bits/stdc++.h>#define EPSILON 0.001using namespace std; // An example…
Q: What are the key distinctions between high-contact and low-contact service models?
A: A high-contact service is one in which the service provider and the client communicate directly with…
Q: What are your ideas on digital media protection, and how do you think devices like this will aid or…
A: What do you think about DMP, and will it aid mobile device investigations? (Use scholarly sources to…
Q: Describe the two competing perspectives on operating system kernel design that exist today.
A: Describe the two competing perspectives on operating system kernel design that exist today.
Q: What are the most important differences that can be made between the three protocols known as SMTP,…
A: Given: Sending messages through SMTP (from the sender's email client to the receiver's email server)…
Q: What good is being bilingual if you're a systems analyst? In this situation, which organizations may…
A: Multilingualism gives you a significant competitive advantage in many workplaces. As the U.S.…
Q: When you start a new Visual C# project, what is produced and displayed in the Designer?
A: Introduction: Launch of a new visual C# project:
Q: Are you able to provide a definition of the operating environment as well as an explanation with an…
A: Operating Environment: In computer software, an operating environment or integrated applications…
Q: Describe the five different categorization strategies that Christopher Lovelock developed. Provide…
A: Deeds, cycles, and exhibits are all examples of services. However, the growing interest in the…
Q: When compared to the Waterfall Model, the Incremental Model has FOUR advantages that make it…
A: Introduction: When comparing incremental development to waterfall devilment, what are the three…
Q: Describe some of the difficulties you have in communicating with others when enrolled in an online…
A: COMMUNICATION BARRIERS: The following is a list of the many sorts of communication difficulties that…
Q: Give a short explanation of each component of a typical operating system kernel, then list all of…
A: Kernel: Kernel is an OS's core PC software. Since the OS has influence over the framework, the…
Q: To what extent does the use of partitions in Linux affect its functionality?
A: Partition editors, such as fdisk, are used in disc partitioning, which is the act of separating a…
Q: A repository plays an important part in the development of software systems.
A: A software repository is a central place to keep resources that users can pull from when necessary.
Q: When describing processes that are not included in a systems analysis, it is a good idea to give…
A: Given: When describing processes that aren't part of a systems analysis, it's worth considering…
Q: Why did the initial Linux developers choose for a kernel that was not preemptible? In a single…
A: Given: Why did the initial Linux developers decide to implement a non-preemptible kernel? In a…
Q: What conclusions and recommendations may be drawn from this research on cybercrime?
A: Illegal activity aimed towards or involving a computer, computer network, or networked device is…
Q: Investigate the similarities and differences between the time-honored Waterfall model and the…
A: GIVEN: We've discussed a few key distinctions between the traditional waterfall approach and the…
Q: Use structured language to explain non-systems-analysis processes.
A: Introduction: A process is a sequence of actions that are performed in a certain order to achieve a…
Q: Gain a comprehensive understanding of the concept of social networking. What precisely is meant by…
A: The activity of using a specialized online platform to keep in touch, connect, and collaborate with…
Q: What does the term "computer integration" mean?
A: Introduction: Integration of computer systems is the process of connecting information,…
Q: What are the key distinctions between high-contact and low-contact service models?
A: Given: A high-contact service is one in which the service provider and the client communicate…
Q: your website is to include videos and photos in your website. 4. The only thing necessary for your…
A: 4. False Things necessary for your website is self interest and user interest.
Q: Define the Pareto principle and explain how it pertains to system needs prioritisation.
A: INTRODUCTION: Here we need to define the Pareto principle and prioritize how it relates to the…
Q: User training and help desks are two examples of acts that fall under the umbrella of user support.
A: Find the required answer given as below :
Q: The need for Software Configuration Management should be explained in this context as well.
A: Management of Software Configuration: It is a set of disciplined software development approaches,…
Q: Exercise 5-1: Create a Visual Basic Project to find the value of the following series. x2 x4 x6…
A: Answer
Q: What are some of the primary benefits associated with the abstraction of operating systems?
A: An operating system connects the user to the computer's hardware.
Q: In what ways might you put Queueing Analysis to use in the area of Engineering?
A: Queueing analysis is a mathematical analysis method which is mainly used to predict the length of…
Q: In this lecture, we are going to contrast and compare two different models: the Rational Unified…
A: Introduction: SDLC procedure: Cascade programming entails extensive ahead preparation as well as…
Q: Write a C program that reads a matrix of n × m numbers, transpose the matrix, then print it out…
A: Sol: #include <stdio.h> #include <stdlib.h> void main() { int a[10][10], r, c, i,…
Q: Is it feasible to describe all of the components that make up the kernel of a standard operating…
A: Given: Provide a one-sentence description of the role of each kernel component in a typical…
Q: It would be helpful if you could describe how one of the cache protocols really works.
A: It would be helpful if you could describe how one of the cache protocols really works In below step.
Q: Write a code to reverse string using reverse function in java
A: In this java based programming question, it is asking for code to reverse string using inbuilt…
Q: Do all of an organization's needs can be met by cloud computing? issues with IT infrastructure at…
A: The solution to the given question is: Cloud Computing : Cloud computing is now taking over the IT…
Q: A Derangement is a permutation of n elements, such that no element appears in its original position.…
A: Code: #include <iostream>using namespace std;int DerangementsCount(int n){// Base casesif (n…
Q: In one phrase, summarise the kernel components of a typical operating system.
A: A kernel is the heart and soul of any operating system. The Kernel has power over everything because…
Q: I created a directory with 3 counties, states in that county, and the towns in that state, I need a…
A: Geocoding is the process of converting addresses (like "1600 Amphitheatre Parkway, Mountain View,…
Q: Reserve monitor is used to check status values against normal value check generator MW output on all…
A: Correct option is a( check status values against normal value) below i explain why other is wrong.…
Q: When it comes to operating systems, what are the key differences between those that operate in real…
A: Please upvote, I am providing you the correct answer. Please please please.
Q: In the process of designing the microkernel of an operating system, what is the overarching notion…
A: Answer
Q: Today's computers are so powerful that this is a reality. Was it always this prevalent in schools,…
A: Computer: A computer is a data storage and processing device. Most computers utilize a binary…
Q: Is moving to the cloud a good or a bad idea?
A: Given: Cloud migration allows cloud computing, in which mobile devices, laptops, and desktops are…
Q: ry integer. The single output P is required to be 1 if the input is me number (zero may be taken as…
A: Well, the first thing you do is to figure out how you are going to convert four bits to two bits.…
Step by step
Solved in 3 steps with 2 images

- Write a program in java language to find the average of given range of number without using any loop... Range is from 50 to 90 (both are inclusive) .Write a Java program that prints out the sum of 1 + 2 + .. + 10 reversely (using a for loop) and show in every iteration the partial sum like follows: Sum of 10 + 9 + .. + 1 is 10 in iteration 1Sum of 10 + 9 + .. + 1 is 19 in iteration 2....Sum of 10 + 9 + .. + 1 is 54 in iteration 9Sum of 10 + 9 + .. + 1 is 55 in iteration 10Implement a method to output every combination of n pairs of parentheses that is legitimate (that is, correctly opened and closed).EXAMPLE \sInput: 3 \sOutput: (( () ) ) , ( () () ) , ( () ) () , () ( () ) , () () ()
- Write a program that gets a list of integers from input, and outputs non-negative integers in ascending order (lowest to highest). Ex: If the input is: 10 -7 4 39 -6 12 2 the output is: 2 4 10 12 39 For coding simplicity, follow every output value by a space. Do not end with newline. simple pythona program that computes the loop of all even,-numbers 2-100 inclusiveUsing arrays in java, create a program that takes two integer command-line arguments n and trials and performs the following experiment, trials times: Come up with a birthday for the next person, uniformly at random between 0 and n−1. make it so that that person enters the room. If that person shares a birthday with someone else in the room, stop; if not, repeat it.
- Write a program that gets a list of integers from input, and outputs negative integers in descending order (highest to lowest). Ex: If the input is: 10 -7 4 -39 -6 12 -2 the output is: -2 -6 -7 -39 For coding simplicity, follow every output value by a space. Do not end with newline.Implement *IN LEGV8 CODE* in DS-5 that accepts a number n, and produces the nth Fibonacci number using the efficient O(n) version. The number should be in the .data segment of your program. Your code must print the nth Fibonacci numberusing printfWrite this using java Write a complete version of the Bresenham Midpoint algorithm to handle ALL slope values. m = 0 m > 0 m < 0 m = 1 m > 1 swap the rolls of x and y m < 1 m = infinity ( needs special test case) Include appropriate tests for ‘special case’ conditions. Insteadof “WritePixel” write to the screen the coordinates of the pixel that would be drawn.
- Simplistic Algorithms with a Fixed Number of Integers (with C++) Write a program that takes three integers and outputs them in reverse order of how they were entered. For example, if the user enters 39, 51, 16 then the program should output 16, 51, 39.Here is my question that my professor gave to me as a homework from my algorithm's class. Use asymptotic notations to describe the running times of the nested loops below. You may assume that n is a power of 2.Write a Java program that uses two nested for loops and the modulus operator (%) to detect and print all prime numbers from 1 to 10,000. Prime numbers are integral numbers that are only evenly divisible by themselves and one (1). Display all the prime numbers found.

