import java.beans.Statement; import java.sql.Connection; import java.sql.DriverManager; import java.sql.ResultSet; import java.sql.SQLException; import javax.swing.JOptionPane;
import java.beans.Statement; import java.sql.Connection; import java.sql.DriverManager; import java.sql.ResultSet; import java.sql.SQLException; import javax.swing.JOptionPane;
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
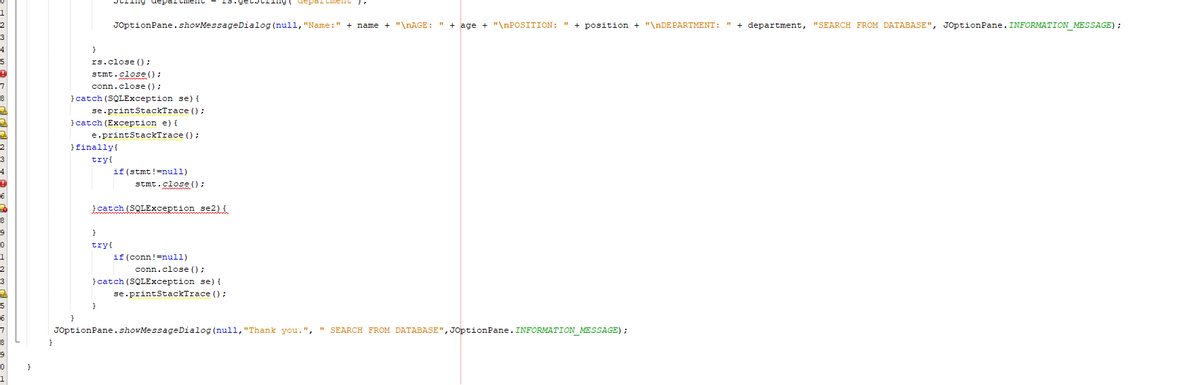
Can someone help what is the reason of ERROR in 39th line and 43rd line?
search from
Transcribed Image Text:1
String department
Cment") 7
JOptionPane.showMessageDialog(null, "Name:" + name + "\nAGE: " + age + "\nPOSITION: " + position + "\nDEPARTMENT: " + department, "SEARCH FROM DATABASE", JOptionPane. INFORMATION_MESSAGE) ;
}
rs.close();
stmt.close();
conn.close();
} catch (SQLException se) {
se.printStackTrace();
} catch (Exception e) {
e.printStackTrace();
} finally{
try{
if (stmt!=null)
stmt.close();
}catch (SQLException se2) {
}
try{
if (conn!=null)
conn.close();
} catch (SQLException se) {
se.printStackTrace();
}
JOptionPane.showMessageDialog(null, "Thank you.", SEARCH FROM DATABASE", JOptionPane. INFORMATION_MESSAGE) ;
}
![4
* and open the template in the editor.
5
package mysqlsearch;
7
8
import java.beans. Statement;
9 import java.sql.Connection;
10
import java.sql.DriverManager;
11
import java.sql.ResultSet;
12
import java.sql.SQLException;
13
import javax.swing.JOptionPane;
14
15
/**
16
*
17
* @author kell_pc
18
*/
19
public class MySqlSearch {
20
21
static final String JDBC_DRIVER = "com.mysql.jdbc.Driver";
22
23
static final String DB_URL = "jdbc:mysql://localhost/sanagustin_database";
24
25
static final String USER = "root";
26
static final String PASS = "";
27
28
public static void main(String[] args) {
29
Connection conn = null;
30
Statement stmt = null;
31
String searchName= JOptionPane.show Input Dialog(null, "Select the name or first letter of the name");
try{
32
33
Class. forName ("com.mysql.jdbc.Driver");
34
35
System.out.println("Connecting to database...");
36
conn = DriverManager.getConnection (DB_URL, USER, PASS);
37
38
System.out.println("Creating statement...");
stmt = conn.createStatement ();
40
String sql;
41
42
;
sql = "SELECT name, age, position, department FROM tblinfol WHERE name LIKE'"+searchName+"""
ResultSet rs = stmt.executeQuery (sql);
44
45
while (rs.next()) {
46
47
String name = rs.getString ("name");
48
int age = rs.getInt ("age");
49
String position = rs.getString("position");
50
String department = rs.getString ("department");
51](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2Fce01bb58-0e02-419d-811c-f275c38fab0f%2Fa3e00ba5-7282-42bf-ab41-5667e8d8c540%2Fp527kwk_processed.png&w=3840&q=75)
Transcribed Image Text:4
* and open the template in the editor.
5
package mysqlsearch;
7
8
import java.beans. Statement;
9 import java.sql.Connection;
10
import java.sql.DriverManager;
11
import java.sql.ResultSet;
12
import java.sql.SQLException;
13
import javax.swing.JOptionPane;
14
15
/**
16
*
17
* @author kell_pc
18
*/
19
public class MySqlSearch {
20
21
static final String JDBC_DRIVER = "com.mysql.jdbc.Driver";
22
23
static final String DB_URL = "jdbc:mysql://localhost/sanagustin_database";
24
25
static final String USER = "root";
26
static final String PASS = "";
27
28
public static void main(String[] args) {
29
Connection conn = null;
30
Statement stmt = null;
31
String searchName= JOptionPane.show Input Dialog(null, "Select the name or first letter of the name");
try{
32
33
Class. forName ("com.mysql.jdbc.Driver");
34
35
System.out.println("Connecting to database...");
36
conn = DriverManager.getConnection (DB_URL, USER, PASS);
37
38
System.out.println("Creating statement...");
stmt = conn.createStatement ();
40
String sql;
41
42
;
sql = "SELECT name, age, position, department FROM tblinfol WHERE name LIKE'"+searchName+"""
ResultSet rs = stmt.executeQuery (sql);
44
45
while (rs.next()) {
46
47
String name = rs.getString ("name");
48
int age = rs.getInt ("age");
49
String position = rs.getString("position");
50
String department = rs.getString ("department");
51
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education