In a public key cryptosystem using the RSA algorithm, a user uses two prime numbers 11 and 17. He chooses 7 as the encryption key, e. 18. Find the decryption key. d = Show your work here:
In a public key cryptosystem using the RSA algorithm, a user uses two prime numbers 11 and 17. He chooses 7 as the encryption key, e. 18. Find the decryption key. d = Show your work here:
Elements Of Modern Algebra
8th Edition
ISBN:9781285463230
Author:Gilbert, Linda, Jimmie
Publisher:Gilbert, Linda, Jimmie
Chapter2: The Integers
Section2.8: Introduction To Cryptography (optional)
Problem 19E: Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "algebra" using the -letter...
Related questions
Question
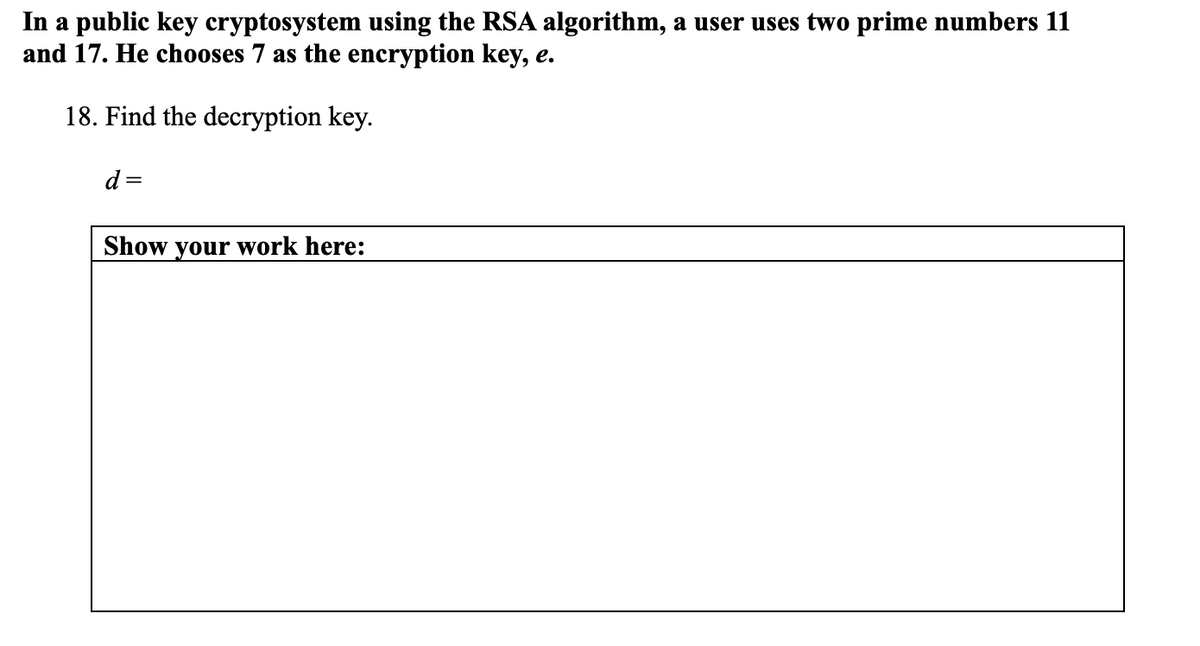
Transcribed Image Text:In a public key cryptosystem using the RSA algorithm, a user uses two prime numbers 11
and 17. He chooses 7 as the encryption key, e.
18. Find the decryption key.
d
Show your work here:
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Recommended textbooks for you

Elements Of Modern Algebra
Algebra
ISBN:
9781285463230
Author:
Gilbert, Linda, Jimmie
Publisher:
Cengage Learning,

Algebra & Trigonometry with Analytic Geometry
Algebra
ISBN:
9781133382119
Author:
Swokowski
Publisher:
Cengage

Elements Of Modern Algebra
Algebra
ISBN:
9781285463230
Author:
Gilbert, Linda, Jimmie
Publisher:
Cengage Learning,

Algebra & Trigonometry with Analytic Geometry
Algebra
ISBN:
9781133382119
Author:
Swokowski
Publisher:
Cengage