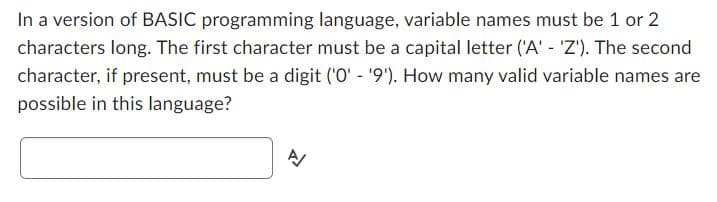
In a version of BASIC programming language, variable names must be 1 or 2 characters long. The first character must be a capital letter ('A' - 'Z'). The second character, if present, must be a digit ('0' - '9'). How many valid variable names are possible in this language? A/
Q: Why does everyone seem to think that the problem of system security is more difficult to solve than…
A: From a cybersecurity viewpoint, reputational damage has typically been the biggest concern.…
Q: If a user states, "my machine won't boot," the help-desk specialist will ask the following…
A: My pc refuses to start: It may be a hardware or software problem if Windows freezes or displays a…
Q: Assume that both lists and strings are indexed starting with index 1. The list wordList has the…
A: We have to find the value of myChar from the given list wordList ["abc", "def", "ghi", "jkl"].
Q: Wireless networks may have vulnerabilities that create trouble. Describe the consequences that three…
A: Wireless networks are computer networks that lack any type of cable connection. The use of a…
Q: When using a computer, what precautions can you take to protect it from sudden voltage fluctuations?…
A: Given: In the context of WiFi, what does the phrase "Access Point" mean? Will you tell me what to do…
Q: During the process of integrating connections, there are potentially four different issues that…
A: Because of the merging of the connections, there are four problems that arise, and their solutions…
Q: When you first turn on your computer, you don't hear the spinning disc or see the indicator lights;…
A: Introduction: The acronym "CPU" stands for "Central Processing Unit," and it is comparable to the…
Q: Memorized information may be retrieved in one of two ways: sequentially or directly. Why do typical…
A: Sequential and direct access are two common methods of accessing information from files. With…
Q: Module 04 Content You are working as a software developer for a large insurance company. Your…
A: Program Approach: Step 1: Import the required packages. Step 2: Create a public class Main. Step 3:…
Q: The two components of a computer's primary memory-ROM and RAM-work together (read-only memory and…
A: There are two components of computer primary memory that is RAM(random access memory) and ROM(read…
Q: Which six paper mill requirements ultimately lead to the design being made?
A: Introduction: Each processor in the chain will have its own implementation for processing a…
Q: Information stored in memory may be retrieved using either the sequential access technique or the…
A: The Response Is: When using direct access, the data may be read immediately, as opposed to needing…
Q: In the following program skeleton, replace the line with the appropriate code. The resulting…
A: Java: On billions of devices, including laptops, smartphones, gaming consoles, medical equipment,…
Q: What changes and improvements has each new generation of networking technology seen, and what are…
A: First-generation is 1G: Mobile phones may utilise it as a carrier. Improve voice readability. The…
Q: Define a function named “getInfoAfterIncrement” that accepts an array of Exam object pointers, its…
A: Answer:
Q: There are two main justifications for using layered protocols, and both are persuasive. To back up…
A: We need to give example for two main justifications for using layered protocols.
Q: mple may help clarify the function of an OS in allocating resources. Please refer to [citati
A: Introduction: Resources, to put it briefly and precisely, are the hardware or software that a…
Q: The data tablet's resolutions are on par with those of a CRT screen, yet it uses far less processing…
A: A light Pen: A light pen is a kind of stylus that uses light sensors to interact with user interface…
Q: Which books aren’t in the Fitness category? List each book title and category.
A: Which books aren’t in the Fitness category? List each book title and category answer in below step.
Q: When a sniffer assault is successful, what steps must the attacker take? To what extent may a…
A: In terms of the network security, sniffer attacks are defined as a stealing data or collecting the…
Q: To what extent can distributed systems help? Please list the top four advantages. List the four…
A: Introduction: A distributed system comprises physically separated PCs (nodes). They're all linked…
Q: mples in which encryption would be insufficient to protect a message. Why is this the case and would…
A: Introduction: Below describe the two examples in which encryption would be insufficient to protect…
Q: Using a while loop. ▪ Make a JavaScript that counts from 0 to 20. ▪ Writing the output as follows:
A: Introduction JavaScript While Loop: You can come across a circumstance where you need to repeat an…
Q: What safeguards can you install to protect your computer from power surges, and what additional…
A: Safe power surges are essential for maintaining the machine's health and providing the operator with…
Q: limitations of the weighted scoring model (weighting scheme), briefly discuss how Coady can use…
A: Solution - According to bartleby policy, I can only answer first question. Please post next…
Q: Assess how well wireless network technologies operate in low-income countries. When compared with…
A: Wireless is an approach to moving transmissions with next to no wires or optic filaments. Signals…
Q: how to use and get access to cloud-hosted applications and services
A: Introduction: This statement explains how cloud-based services and applications are used: Hosting…
Q: How similar are the issues with compilers and two-pass assemblers? The compilers are assumed to…
A: Introduction: Considerations that apply to two-pass assemblers also apply to compilers: a. Assume…
Q: When compared to centralized systems, how do dispersed ones fare? Clearly state the good and the bad…
A: Introduction: Distributed Systems?Distributed computing is distributed system. Distributed systems…
Q: When someone talks about their WiFi having a "Access Point," what exactly do they mean by that? Do…
A: Given: In the context of WiFi, what does the phrase "Access Point" mean? Do you know what has to be…
Q: All entity names, relationship names, and attribute definitions must be correct.
A: The solution to the given question is: RELATIONSHIPS AND ENTITIES An entity relationship models (or…
Q: Even though wired networks are faster than wireless ones, the best performance is gained by using…
A: Wireless networks are often slower than conventional networks: Wired connections transmit more data…
Q: What precisely differentiates symmetric key cryptography from asymmetric key cryptography and vice…
A: Introduction: There are two different kinds of encryption, symmetric and asymmetric key encryption:…
Q: How do you collect data for a comprehensive operations manual? How many items will be examined at…
A: Sequential Search is a technique for searching that involves checking the item being searched for…
Q: The python function first_words takes one parameter, fname, the name of a text file, and returns a…
A: Python : Python is frequently used to create websites and applications, automate tasks, analyse…
Q: The following illustrations show how a suggested scheme may be of aid in the process of designing…
A: Introduction: An organisational setting's rules and procedures for establishing and administering…
Q: What are the needs for information security?
A: System of Information: Information systems are interconnected pieces of software that gather,…
Q: will write a c++ program that prompts the user to input elements for two 2x2 matrices. Your program…
A: A 2D array can be defined as an array of arrays. A 2D array is organized as a matrix and can be…
Q: How different are the approaches to deadlock avoidance and deadlock prevention?
A: Given: When a group of processes are in a deadlock, each process is waiting for a resource that is…
Q: Here is my method (image), what should i change or fix to have 4 different random size squares each…
A: Java: Java is a high level, class based object oriented programming language. It was developed by…
Q: will appreciate a zoomed in screenshot of the code I could not see the figures clearly from my…
A: Lists are used to store multiple items in a single variable. Lists are one of 4 built-in data types…
Q: Why do we need virtual LANs if many subnets can be created on a single switch, and if users on…
A: To route across distinct VLANs, you require a router. Additionally, the same IP subnet cannot be…
Q: When turning on the computer for the first time, if you don't hear the fan spinning or see any…
A: The above question that is When turning on the computer for the first time, if you don't hear the…
Q: The two components of a computer's primary memory—ROM and RAM—work together (read-only memory and…
A: Both read-only memory (ROM) and random-access memory (RAM) make up the main memory of a personal…
Q: Is message authentication the only method available, or are there others?
A: Given: In cryptography, a message authentication code (MAC) is used to verify the sender and…
Q: What does the word "security" mean in the context of information and communication technologies? In…
A: Information technology (IT) security refers to the procedures, devices, and personnel employed to…
Q: Please explain what a cassette drive is and how it varies from a normal tape recorder used to store…
A: Introduction: The term "cassette drive" refers to a typical tape recorder that may be used to store…
Q: After updating the BIOS on my laptop, I discovered that even though everything wa eceiving…
A: To Finding Root of the Issue ,There are several ways to verify that there are no display issues:…
Q: What is a Linux Distribution?
A: A computer operating system made up of components developed by several open source developers and…
Q: Please explain what a cassette drive is and how it varies from a normal tape recorder used to store…
A: cassette drive (plural cassette drive) (computing) A cassette tape interface unit for computers used…
Step by step
Solved in 2 steps

- If the following code segment compiles correctly, what do you know about the variable x? if(x) WriteLine(OK); a. x is an integer variable. b. x is a Boolean variable. c. x is greater than 0. d. none of theseThe programming language is C++, write a program base on the given statement. In 2001, Bureau of Internal Revenue proposed an overhaul of theIncome Tax Law. They proposed the ff. schedule: INCOME TAX RATE0 to 5000 0 5001 to 10000 100 + 3% of income over 5000 10001 to 25000 200 + 6% of income over 10000 25001 to 50000 300 + 9% of income over 25000 Over 50000 500 + 15% of income over 500008- Which of the following primitive types in Python would be most suitable for representing acceleration due to gravity on Earth, 9.81 m/s²? a. float (floating point number) b. str (string) c. bool (boolean) d. int (integer)
- Q1. Write a program in G+ language to obtain the equation below, for values of x from (1~ 20), by using for statement: 2 X o Y=—+cosix— vX+ — 4 Ix|Write a program to check whether the given number is positive or negative (using ? : ternary operator ) (C language)A ) Write down the rules for naming the python variables . 11 Mark ] B ) Write the differences for the following operators given below and explain with an example on your own words • Greater Than and Greater than Equal to operator [ 1 Mark for Difference + 1 Mark Example • Division and Floor Division operator [ 1 Mark for Difference + 1 Mark Example • OR and NOT operator ( 1 Mark for Difference + 1 Mark Example )
- Write a program that prompts the user for a wavelength (W) value or a frequency (F) value and prints a description of the corresponding part of the electromagnetic spectrum, as given in the following table. Using if statements (python)Write a program in C# that will ask the user to enter two double numbers. Use an if() statement to determine which numberis largest, and output a line indicating the larger number.xyz is a telecom company,there are three recharge plans as listed below- 10$ - 50 Gb for 28 days 20$ - 150 Gb for 56 days 40$ - 350 Gb for 84 days write a program in c++ to ask user to which plans does he wants and display the cost of that recharge plan.
- In C programming language, the name of a variable is a string that can contain uppercase letters, lowercase letters, digits, or underscores. Further, the first character in the string must be a letter, either uppercase or lowercase, or an underscore. If the name of a variable is determined by its first eight characters, how many different variables can be named in C? (Note that the name of a variable may contain fewer than eight characters.)WRITE A PROGRAM TO CALCULATE THE SIMPLE INTEREST ON A LOAN AMONUT OF 50000 GHANA CEDIS AT AN INTEREST RATE OF 30% FOR A NUMBER OF YEARS WHICH WILL BE SPECIFIED BY THE USER.In Python: The line endings are missing. Usually a gift line ends with a comma (","), but the last one ends with a period (".") , and the next-to-last ends with "and". Write an if-elifelse to add (+) a comma, a period, or and. code: gifts = ['partridge in a pear tree','turtle doves','french hens','colly birds','gold rings','geese a-laying','swans a-swimming','maids a-milking','ladies dancing','lords a-leaping','pipers piping','drummers drumming'] ordinals = ['first', 'second', 'third', 'fourth','fifth', 'sixth', 'seventh', 'eighth','ninth', 'tenth', 'eleventh', 'twelvth'] numerals = ['a', 'two', 'three', 'four', 'five', 'six', 'seven','eight', 'nine', 'ten', 'eleven', 'twelve']#numerals=numerals[0].title() first_verse = 'On the X day of Christmas my true love sent to me' # Your work begins here.# RULES:# 1. Your program must use the variables declared above# 2. Your program may only use these string literals:# "." "," "and" ""# All other strings must be obtained from the variables…

