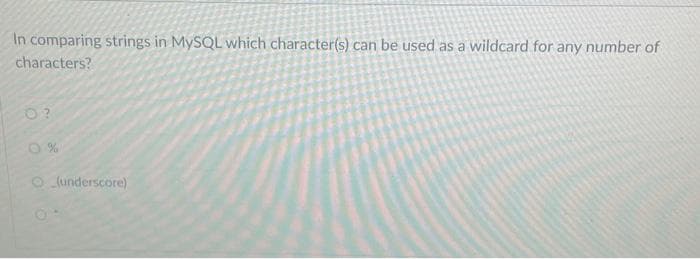
In comparing strings in MySQL which character(s) can be used as a wildcard for any number of characters? O(underscore)
Q: What are the best firewall management methods? Explain?
A: The effectiveness, security, and proper operation of firewalls inside a network are ensured through…
Q: What role does "content library" play in managing VM templates and vApp templates?
A: In the realm of virtualization and cloud computing, the management of virtual machines (VMs) and…
Q: List the various wireless communication standards and their relevance to web technologies.
A: The detailed explanation about wireless communication and their relevance to web technology is given…
Q: Compare the efficiency of RF (Radio Frequency) transmission with infrared in the context of web…
A: When comparing the effectiveness of RF (Radio Frequency) transmission with infrared in the context…
Q: Do you agree that networking plays an important part in the further development of information…
A: The process of joining computers, gadgets, or systems to provide resource access, data exchange, and…
Q: It's possible that infiltrating a network may be accomplished by rerouting malicious traffic from…
A: Preventing network infiltration through the rerouting of malicious traffic from one VLAN (Virtual…
Q: b) Write a query to display the patron ID, last name, number of times that patron has ever checked…
A: Algorithm:Join Tables: Join the PATRON and CHECKOUT tables on the Pat_ID to associate patrons with…
Q: Identify and discuss key components of the Wilson approach.
A: It's crucial to identify the context in which you're using the Wilson approach because it can be…
Q: The following query is given as an expression of relational algebra.…
A: In this analysis, we will identify the best query evaluation strategy to reduce the amount of disk…
Q: Explain arithmetic operators in C with example
A: Arithmetic operators in C are fundamental tools for performing mathematical calculations. They are…
Q: Can the relevance of data quality in relation to data warehousing be investigated from a scholarly…
A: Investigating the significance of data quality within the realm of data warehousing is a valuable…
Q: What is the primary function of a hypervisor in virtualization?
A: When it comes to virtualization a hypervisor plays a role in managing and enabling the creation and…
Q: What are the challenges and benefits of implementing a software-defined WAN (SD-WAN) in a…
A: Software-defined WAN (SD-WAN) is a networking technology that uses software to control and manage a…
Q: What are some of the advantages and disadvantages that come along with the various forms of…
A: Authentication is a critical process that verifies the identity of users, devices, or entities…
Q: Explain the role of a "virtual hardware version" in hypervisors.
A: In the world of hypervisors and virtualization a "virtual hardware version" plays a role.Hypervisors…
Q: Explain different operators in C-Language with examples.
A: Operators in the C programming language are symbols that represent computations and actions to be…
Q: Provide a rundown of the three most significant issues that result from concurrently processing…
A: In this question we need to explain three most significant or important problems which result from…
Q: Write a query to display the patron ID, book number, and days kept for each check-out. "Days Kept"…
A: The below query will display the patron ID, book number, and number of days kept for each check-out…
Q: Consider the following Boolean formula: AB+ !C F= Write out a truth table corresponding to this…
A: We have constructed a truth table for the Boolean formula F = AB + !C, where A, B, and C are binary…
Q: When accessing shared resources like a printer, it is necessary to adopt suitable security measures…
A: The company uses a shared network printer located centrally for all employees to print documents.…
Q: How does the addition of technology to the lesson plan compare positively and adversely to the use…
A: What is technological tools:Technological tools are specific technologies that are designed to serve…
Q: Matching Drag the letter from the list on the right to its matching term in the list on the left.…
A: A database is a structured collection of organized data that is stored and managed electronically.…
Q: nowledgeable about the source or provenance of the material.
A: Reading a news item on a tablet computer is a must.The data suggest a disparity between smartphone…
Q: Explain the concept of "handoff" in wireless communication
A: Wireless communication has become an indispensable part of our daily lives, driving seamless…
Q: How do 5G technologies impact web application design and user experience?
A: The introduction of 5G technology has ushered in a new era of possibilities for web application…
Q: Consider the code C: C = {000000, 001011, 010101, 011110,100110, 101101, 110011, 111000} Explain…
A: In coding theory, a coset is a set formed by adding a fixed vector to all the vectors in another…
Q: Why do we call them a set of principles "inference rules"? Please include examples of both "reverse…
A: In the realm of logic, reasoning, and problem-solving, inference rules play a pivotal role. These…
Q: How do web technologies cater to the power consumption issues in wireless devices?
A: As internet users and devices continue to skyrocket, power efficiency has become a concern. Wireless…
Q: Provide a made-up illustration of the user login management process. Create a list of all of the…
A: Inspection:Scenario management is a very successful strategy for managing several futures and…
Q: What are the security benefits and drawbacks of using different authentication methods?
A: Authentication is the process of verifying the identity of a user or device. It is an essential part…
Q: Explain the implications of cache coherency in virtualized multi-CPU environments
A: Cache coherency refers to the consistency of shared resource data that ends up stored in multiple…
Q: Consider the following truth table, which includes don't cares: ABC 001 0 0 1 00 010 1 1 1 00 0 1 1…
A: We are given a truth table and based on that we are going to find out sum of products. To find the…
Q: Discuss the future trends and developments expected in wireless transmission technology for web…
A: In the realm of wireless transmission technology for web applications, several exciting trends and…
Q: What goes into setting up a design workstation? Give examples to illustrate the concept?
A: Setting up a design workstation can be a complex task, but it is important to get it right in order…
Q: When it comes to virtual machines, the number of possible configurations is almost infinite. How can…
A: Setting up a new network with VMware Fusion to run four distinct operating systems simultaneously…
Q: What exactly does it mean to have autonomous computing, and how does this kind of computing add to…
A: The term "autonomous computing" refers to computer systems that are intended to run and govern…
Q: Since you have all of the required tools at your disposal, are you capable of developing a web…
A: A web application is a software program that operates over the internet, allowing users to access…
Q: Explain the decision making statements in C language
A: In this question we have to understand the decision making statements in C Language.Let's understand…
Q: It is crucial to know why authentication is being done. When weighed against one another, how do the…
A: Authentication:Authentication is the process of ascertaining whether or not someone or something is…
Q: Do you think it would be a good idea to write an essay regarding the part that networking played in…
A: Information Technology (IT) has witnessed a remarkable transformation over the decades, and one of…
Q: How exactly may PHP and MySQL be put to use in order to create a database?
A: PHP and MySQL are a powerful duo when it comes to creating and managing databases for web…
Q: 7) What is the output of C Program with arrays and pointers.? int main() { } int ary[] = {11, 33,…
A: In this algorithm, start by creating an array called 'ary' with three elements, 11, 33 and 55. Then…
Q: Which wireless network standard operates at 5 GHz and has a maximum data rate of 1 Gbps?
A: The 5 gigahertz frequency band is used for wireless communication and is also referred to as the…
Q: 2. Explain different types of inheritances in C++.
A: In this question we need to explain various kinds of inheritance in C++ programming…
Q: What are the advantages of storing data on the cloud, and what are the drawbacks and potential…
A: In this question we need to explain the advantages along with potential problems and drawbacks of…
Q: hoice for the data center infrastructure of big data clusters. A Big Data Cluster could be up and…
A: Cloud computing is a vital technology that allows for the execution of massively parallel and…
Q: In order to secure the privacy of users and the integrity of their networks, one essential step is…
A: Firewalls fulfill a momentous function in fortifying the privacy of users and upholding the…
Q: In what ways is it helpful to verify the legitimacy of something? Take into account the pluses and…
A: Ensuring that users are genuine in the digital space is the essence of authentication. This process…
Q: Describe the CAP theorem in the context of distributed databases.
A: The CAP theorem, also referred to as Brewer's theorem, stands as a cardinal principle in the realm…
Q: Prove that a binary tree with k leaves has height at least log k
A: The binary tree structure represents a branching structure, where each node can have zero, one, or…
Trending now
This is a popular solution!
Step by step
Solved in 4 steps

- Using MySQL, populate the CUST_LNAME, CUST_FNAME, and CUST_BALANCE fields with the following customers: CUST_LNAME CUST_FNAME CUST_BALANCE Smith Jeanne 1050.11 Ortega Juan 840.92I tried using this and it gives me (Error Code: 1052. Column 'AU_ID' in field list is ambiguous) could you provide fix and explain why MySQL does this?How do I load/move URL information from one column into a seperate column on power BI?
- Can a shared key be used to encrypt an AES key? Justify your answerHash function is compared to keyed hash function. View an example of a hash function with a single key.When compared to other families of secure hash functions (such the SHA family of algorithms), what sets a Key Derivation Function apart? If you want your message to have an impact, you need to provide as much specificity as possible.Question 16 kk Draw the process of top-down parsing for id + id * id with E → TE’ E’ → +TE’ / ∈ T → FT’ T’ → xFT’ / ∈ Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
- What is the function of compression in the hash function and how does it work?Can an AES key be encrypted using a shared secret? Defend your response Compare hash function with keyed hash function. View an example of a one-keyed hash function.Name your friends by the values of their ASCII characters and store them in a hash table using the divide technique. Be sure to note the insertion point for each step and whether or not there was a collision. Respond to the following inquiries. Which table size is preferred, and why?How did you handle collisions, and why?What is the significance of the load factor?
- Consider your name, take ASCII value of each character and map all those values in a Hash table using division method. Mention each insertion step wise and if there is collision, mention that as well. Answer the following questions A) What should be the preferable Table size and why? B) What technique did you use to cater collision and why? C) What is the value of load factorLinear Hash Table Question. Insert the values 1nto the hash table in sequence: 00000, 11101, 11001, 10111, and draw all intermediate steps. Please do not forget to denote bit flips, thank you.When compared to other families of secure hash functions (such the SHA family of algorithms), what sets a Key Derivation Function apart? When communicating, it is important to provide as much information as possible to the receiver.

