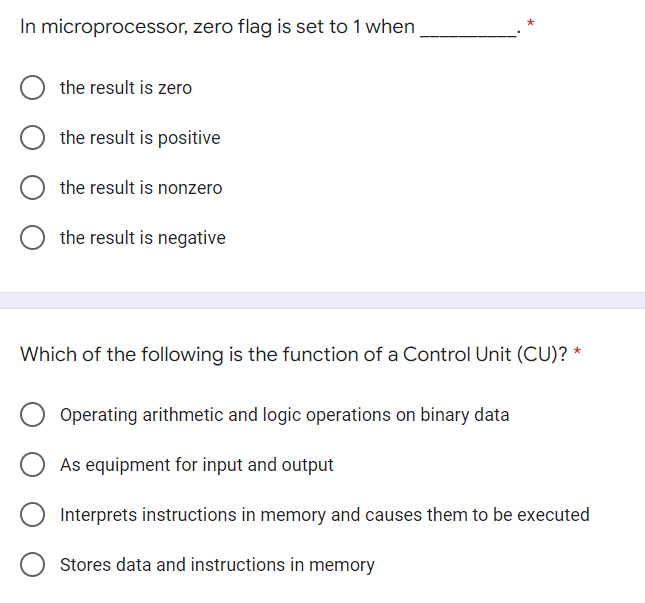
In microprocessor, zero flag is set to 1 when the result is zero the result is positive O the result is nonzero
Q: Could you please clarify what the term "frequent itemset" means? Also, provide an explanation of the…
A: What is a FREQUENT ITEMSET? First, let's try to figure out what data mining is. Data mining is…
Q: Why is magnetic tape such a popular medium for the storing of information?
A: Magnetic: The data may also be stored on magnetic tape, which is a technology that is commonly…
Q: Can you explain how to access databases using Java programs?
A: Answer: We'll talk about database access from a Java application in this issue. JDBC is required in…
Q: Describe the three WORM disk recording methods.
A: The following are three methods for recording WORM CDs. WORM CDs may be recorded in one of three…
Q: The 'MIME' header is added to web pages to differentiate them from email messages when they are…
A: Define: To differentiate web pages from email communications, they are submitted with a MIME header.…
Q: List the business, technology, and organizational concerns addressed throughout the project to…
A: Three-Sphere Model for system management: The Three-sphere model of system management deals with the…
Q: How are RGB color beams formed in CRT displays
A: The Beam-Penetration method has been used with random-scan monitors. In this method, the CRT screen…
Q: When it comes to cloud backup, what's the difference between "cloud storage" and "cloud backup"?
A: Introduction: Cloud backup may be described as software that safeguards your data, files, and system…
Q: Write a python program to create a variable called 'college' and assign it a string "computer…
A: The above question is solved in step 2:-
Q: does the file called Bevco.xls serve?
A: introduction : XLS was developed by Microsoft for use with Microsoft Excel and is also known as…
Q: How many times will the computer display the message box in the code below? intCounter = 0 Do…
A: In this question we have to find out from the looping program that the computer will display the…
Q: How do we set up each router's routing table?
A: Given: What is a routing table? Interfaces on routers allow them to communicate with other network…
Q: hings to keep in mind while upgrading the components in your laptop
A: Upgradation of components in a laptop should be done crucially so as to get the best result.
Q: Malware can alter the way the Operating System and applications behave in an undesirable and…
A: Introduction: Malware, short for malicious software, is a catch-all term for viruses, worms,…
Q: Discuss the significance of cloud computing's new scalability characteristics. In your writing, be…
A: Scalable Cloud Infrastructure: Building a scalable cloud architecture is made possible through…
Q: What does the term "Data Preparation" indicate, and what steps are involved?
A: Data Preparation:- Data preparation is a pre-processing method that comprises cleaning and modifying…
Q: In order to ensure the integrity of your data, what is the procedure?
A: Answer the above question are as follows
Q: WAP to calculate and display square of an integer and float variable using function overloading
A: Algorithm to display square of an integer and float variable Input float and integer variable to…
Q: One of the advantages of blocking a tape is that it allows the same amount of data to be stored on a…
A: Some examples of backing storage devices are Magnetic tape drives, hard disk drives etc.
Q: The following code extracts contains PIC18F2455 program. The readADC() function read: a value from…
A: Let us see the details below.
Q: Examine wireless networks in developing nations. Why are wireless networks established in areas…
A: Wireless network: To connect nodes, a wireless network takes advantage of wireless data…
Q: Discuss the Microkernel System Structure of operating systems briefly and state two advantages of…
A: Monolithic Nucleus: This is a kind of architecture for operating systems in which the whole…
Q: Design a 4-bit 2’s complementer circuit. The unknown will be treated as don’t care. Include the…
A:
Q: What are the responsibilities of those who manage data?
A: The complete solution is given below:-
Q: One of the most serious challenges confronting the organization today is cloud computing security,…
A: Given: What are the security issues a associated with cloud computing? There is little insight into…
Q: What is the distinction between connotative and denotative language?
A: Denotative significance is the significance of a word that is substantially alluded to as the actual…
Q: Explain the influence of "changing time quantum" on process execution in Round-Robin scheduling by…
A: The predetermined period of time allotted for a particular job that has to be processed in a…
Q: Design a program to store this binary tree by bi-linklist, and inorder, preorder,postorder traverse…
A: Here we have given a program for the binary tree for representing inorder, postorder and preorder…
Q: Which characteristic of cryptography ensures that the information can not be accessed by an…
A: Which characteristic of cryptography ensures that the information can not be accessed by an…
Q: 1.When you are in mountain climbing and emergency
A: Bring 3 litres of water and food with high protein Doing some Caruso exercise before started…
Q: Write a program which repeatedly reads numbers until the user enters "done". Once "done" is entered,…
A: As per the question statement, We will run this code and try out different input value and will…
Q: explain what it means to have an instruction set that is orthogonal
A: In Computer engineering, an orthogonal instruction set is a instruction set engineering where…
Q: Supply your answer by drawing the convex hull and then uploading the graphic using the file upload…
A: Answer: For this, we use the Jarvis march algorithm. Jarvis march algorithm: The idea of Jarvis’s…
Q: It is the basic building block in VB. Select one: a. none of the choices b. label c. textbox d.…
A: The Form is the primary building block of a Visual Basic 6 application Label is needed to change the…
Q: A C 1 1 2 3 4 A D 2 3 COUNTA(A1:11) 4 The formula in the cell above would yield the result: DI
A: COUNTA is a function present in excel.
Q: Defining a system model is a complex task. What should be taken into account while developing the…
A: Introduction: System model is used in many disciplines, sectors of application, and methods with…
Q: Internet users may choose between two sorts of services provided by applications. The following are…
A: Describe the distinctions between two kinds of Internet services accessible through the Internet's…
Q: What is the process that is used to route data in a wide area network?
A: Introduction: What is the process that is used to route data in a wide area network?
Q: What use does the file called Bevco.xis serve?
A: In 1987, Microsoft released Excel for Windows. The XLS file extension is used for files stored as…
Q: Why practically every element of our existence that involves technology
A: Answer:
Q: The use of an unintegrated information system may result in a number of issues and difficulties.
A: Introduction: PC misfortunes and disappointments are big PC troubles, necessitating unnecessary…
Q: How do the nodes of the Adhoc Network know when the topology of the network changes?
A: In wireless Ad hoc network topology, wireless capable devices communicate directly each other…
Q: Explain why access control mechanisms are more important in a database approach than in a flat-file…
A: The Answer is in given below steps
Q: Create a Verilog code, Synthesis, and a testbench of 8-bit Accumulator. Show the result using seven…
A:
Q: Explain the differences between interlacing and progressive scan in the context of video signal…
A: Explanation: In the transmission of visual signals, distinguish between interlacing and progressive…
Q: Describe each assessment method in the realm of human-computer interaction in a few words. Testing…
A: Human-Computer Interaction (HCI): Human-computer interaction (HCI) research, a multidisciplinary…
Q: Match each of the following categories of websites or social networking sites with an example of…
A: We must match the locations correctly. The choices are: Social networking site Government portal
Q: Find the correct phrase to describe the output of a computer that is written directly to optical…
A: Given: A microfiche is a sheet of the flat film measuring 105 x 148 mm, which is the same size as…
Q: To begin, what is a model of a system exactly? What are the most important considerations while…
A: System model: A description of each process, as well as how those processes interact with one…
Q: System management is based on the three-sphere model. Avoid copying examples from your textbooks.
A: A three-sphere model of system management: Three realms of system management exist.BUSINESS…
Hi
solve all of them plz
Step by step
Solved in 2 steps

- A(n) __________ is a storage location implemented in the CPU.Convert given code to LEGv8 code:int f, g, y //global 64-bit variablesint sum (int a, int b) { // at memory address X0+1000.return (a +b)} int main (void) // at memory address X0 + 800{f=2;g=3;y= sum (f, g);return y;}Convert this code, making valid assumptions about registers and register use. Notethat brackets and global variable declarations are not affecting the addresses of the instructionsin memory.The control signal Ep or iEnableoutput allows the program counter to decrement its value. True False The control signal Ep or iEnableoutput sends the content of the program counter to the W bus. True False A tri-state buffer is needed for all data going to the W bus. True False In using 'assign' statement in Verilog, the left hand side must always be a register. True False In declaring a register in Verilog, the following format must be followed: reg [LSB:MSB] identifier; True False
- Answer the given question with a proper explanation and step-by-step solution. PLEASE PAY ATTENTION TO THE DATA TYPES AND FOLLOW THE CODE AND DIRECTIONS EXACTLY Convert the following C++ program into an x86 assembly language program.Comment the start of each "code block" that performs one of the listed mathematical calculations.Comments go to the right of the actual code, all starting on the same column.Post ONLY your ASM file here to Blackboard when complete. // Global variableschar a = 5;char b = 6;char c = 7;char d = 8;char e = 2;char f = 3;char g = 1;char h = 4;// Codeint main(){ --h; c = g + h; d = e + 22 - c - b; g = -h; ++b; a = g + d - 15; b = a + 92 - b; h = d + (-f) - d; // Move a into the eax register // Move b into the ebx register // Move c into the ecx register // Move d into the edx register // Call the DumpRegs function // Move e into the eax register // Move f into the ebx register // Move g into the ecx register…Write a program, in assembly language format, to hold a character set at a specific memory location. Each character is entered via the keyboard and ends with the character '!'. Furthermore, the set of characters that have been stored in memory is displayed on the monitor screen. Hint: use the interrupts mentioned in question no 2 above. For example: from the keyboard type 'I', 'L', 'K', 'O', 'M', '!' ; then save it in a certain memory location and the screen display becomes ILKOM. Instructions: create a program in the form of procedures.IN asmly language please Pretty please with successful build screen shot and output 1.Using the AddTwo program from Section 3.2 as a reference, write a program that calculates the following expression, using registers: A = (A + B) − (C + D). Assign integer values to the EAX, EBX, ECX, and EDX registers. Note: you can hard code integer literal onto the registers, e.g. mov eax,55 ; AddTwo.asm - adds two 32-bit integers.; Chapter 3 example .386.model flat,stdcall.stack 4096ExitProcess proto,dwExitCode:dword .codemain proc mov eax,5 add eax,6 invoke ExitProcess,0main endpend main 2. Listing File for AddTwoSum Generate a listing file for AddTwoSum.asm(in 3.4.3 of the text) and write a description of the machine code bytes generated for each instruction. You can write your descriptions directly over the .lst file. You might have to guess at some of the meanings of the byte values. Submit the .lst file with your description over it.…
- What will be the contents of BX after the following instructions execute?mov bx,5stcmov ax,60hadc bx,axHere are some registers and storage locations during the run of a program.For this example, all numbers are hex.eax contains 300ebx contains 3000The doubleword at memory location 300 contains 500The doubleword at memory location 10 contains 70 What is in eax after the command addl $10, %eax executes? a. 310 b. 510 c. 370f R0 = 0x20008000, after executing STMIA r0!, {r3, r9, r7, r1, r2}, register r7 will be stored in memory starting from which bases. Please choose one:A. R0 = 0x2000800CB. R0=0x20008004C. R0= 0x20008014D. R0 = 0x20008010E. R0 = 0x20008008
- Please this question answered by this website but not appropriate answer because in c++ I want to answer in Assemly language to 8086 processor and 16 bit registers only Please solve it and send me please ? This question: Write a program to find the factors of a number and store the result at address 200 in memory.Sample Answer: I wrote a program to store factors of 60 at 200. (you should choose anynumber but greater than 20.WOLcUID wwreyg-100Ax-0060 BX=0030 CX-000 DX-0000 SP-0OFD BP=0900 SI=0000 DI-0209DS-073F ES-073P SS=073PF CS-973F IP-0110 NU UP EI PL ZR NA PE NC073F:011C CCd 2873F:020002 03 04 06 08 OC 10 18-20 00 00 00 00 00 00 00073F:0210 00 00 00 00 00 00 00 00-00 00 00 00 00 00 00 00973F:0220 00 00 00 00 00 00 00 0-00 00 00 00 00 00 00 00073F:0230 00 00 00 00 00 00 00 00-00 00 00 00 00 00 00 0873F :0240 00 00 00 00 00 00 00 0-00 00 00 00 00 00 00 00o73P:250 00 00 00 00 08 00 0 00-00 00 00 00 00 00 00 00073F873F:0270 00 00 00 00 00 00 00 00-00 00 00 00 00 00 00 00f 400 40c…A fragment of code is given to compare text in the field alpha with a text in the field beta: .data alpha db 12 dup(?) beta db ’abrakadabra’, 0 ; ::: .code ; ::: mov esi, 0 mov ecx, 12 ns: mov dl, alpha[esi] cmp dl, beta[esi] jne wrong ;=====MISSING==== loop ns ; ::: wrong: Choose missing instruction to insert in the code line marked by the comment “MISSING”.Write a MIPS program (please show the whole code with comments)Given the following data definition statements, compute the addresses of arr2, arr3, str1, and str2, given that the address of arr1 is 0x10010000. Show your steps for a full mark. Select “Show Labels Window (symbol table)” from the Settings menu in MARS to check the values of your computed addresses. .data arr1: .word 5:20 arr2: .half 7, -2, 8, -6 arr3: .space 100 str1: .asciiz "This is a message" str2: .asciiz "Another important string"



