In SNMP to informs the manager about rebooting operation the following command can be used
Q: collection address and the delivery address. Quickly design a prototype to present to the board and…
A: Solution: The code with the required functionality is given below. ->It has been executed in…
Q: Under Security Policy there is a single configuration option Security Mode. Note the default…
A: Answer : WPA is Wi-fi protected access . and PSK is Pre shared key.
Q: An employee has lost his company-provided phone during a business trip. What process ensures that he…
A: Please find the answer below :
Q: 131. Once deadlock has been detected, some strategy is needed for a. Control b. Access c. Recovery…
A: Deadlock is a circumstance where a bunch of cycles are impeded on the grounds that each interaction…
Q: an is prevented from accessing esources on a shared folder. Which ne is the best security option…
A: The security options are described below: Read: A user is allowed to view or see the subdirectories…
Q: Does a license only cover one installation?
A: Does a license only cover one installation
Q: Each process utilizes resources in following order: TRue or false release use request
A: Given : Each process utilizes resources in following order: TRue or falsereleaseuserequest
Q: n the event that a script is running an infinite loop, the user can use the command to halt the…
A: kill command
Q: Session data will not be available once the user logged out.
A: Please find the answer below :
Q: Which command can list the files that could be impacted if you terminate the rogue process
A: -> Find the answer in the Step 2.
Q: Why doesn't eigrp have an auto summary command?
A: Introduction: EIGRP (Enhanced Interior Gateway Routing Protocol) is a distance-vector routing…
Q: Your organization has expanded dramatically, and suddenly there's heavy file server use. All the…
A: Since the number of namespace severs are added to existing set of servers, the new servers must be…
Q: Create a program that a user can use to manage the primary email address and phone number for a…
A: In this program using python functions based on the Do while loop and the menu constructed under it.
Q: A. Backup and Restore tool can be used to create a backup on Windows 7 and Windows 10. True False
A: Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: physical access control
A: ANSWER: Physical Access Control:
Q: When system journals are not being manually deleted, where do they reside?
A: What is system. journals? It's a unified area for all messages logged by various parts in a…
Q: ..command is used to display the lineage of a process by tracing its PPIDS until the systemd daemon
A: As the question is related about Linux's command so we will first understand what Linux is. Linux is…
Q: shell command interpretation [ Choose ] Second Third Fork() a child process Fifth First Fourth…
A: Answer:
Q: Create a program that a user can use to manage the primary email address and phone number for a…
A: Since no programming language is mentioned, I am using python. Code: contacts=[[1,"Guido van…
Q: To execute the use case Issue certificate, an actor Professor is required; in addition, an actor…
A: Lets see the solution.
Q: List any five command options available when interacting with a File Manager
A: Five file management commands are given below.
Q: How does UAC determine the types of actions that a user can perform on a system. What is the…
A: Answer of the given question: Each application that requires the chairman access token should…
Q: When a full backup or system state backup is performed on a CA server, the certificate store is…
A: The given statement is true i.e. The certificate store is backed up together with other data when a…
Q: What is the use of Patch Management?
A: SUMMARY: -Hence, We discussed all the points.
Q: eature should be verified to guarantee that users are not unable to access a remote application?
A: Screen sharing is a technique that can be used to see what other person is doing on their screen.
Q: Explain why user access administrator should never be granted the ability to initiate a new user…
A: People having user access administrator rights have a wide range of roles to play. They provide…
Q: To identify attempted computer logins, which log in Event Viewer would you use?
A: Explanation: The event viewer records every detail of system occurrences and keeps a log file for…
Q: After a password change, some users are experiencing trouble logging in. An administrator has…
A: Domain Controller: Domain controllers are computers that run on Microsoft servers and are…
Q: An employee has recently been hired to work in the Finance department. The IT administrator adds the…
A: Ans: An employee has recently been hired to work in the finance department. The IT administrator…
Q: List of commands needed to create connection between the two computers. with references
A: A public/private keypair needs to be created on the machine you want to connect from then the public…
Q: What is the system logs' default location?
A: Introduction: We use cloud technology to the access virtual space and the internet. Some people…
Q: True or False: Automatic updates are essential for system security and reliability.
A: Answer: The answer is True for the above-given statement The explanation is in the Next step.
Q: Each request requires that the system consider the _____________ to decide whether the current…
A: Resource allocation is the process of allocating processes so that they can start task competing.
Q: Planning is the last phase of the SDLC process. True or Fals
A: Software Development Life Cycle(SDLC) is a process used by the software industry to design, develop…
Q: _____________ command shows the backup locations in superblock.
A: This question is related to backup and recovery in linux.
Q: On a Systemd-based system, _______ command you can use to read journald log entries.
A: To be determine: Fill the blank
Q: Set up a new account on an organization's website by writing a standard operating procedure (SOP).
A: Using a hierarchy format: In that it involves publishing the methods of the cycle to be completed,…
Q: What is chmod (change mode) command? Give examples.
A: Linux chmod command: Linux is a clone of UNIX environment. This command is an abbreviation for…
Q: A small insurance company has an online application system that allows its customers to interactwith…
A: Whereas if the file format is too huge, the Libreoffice software may become unresponsive, especially…
Q: State true or false: Every cascadeless schedule is also recoverable
A: this is a true statement that Every cascadeless schedule is also recoverable. correct answer is a.…
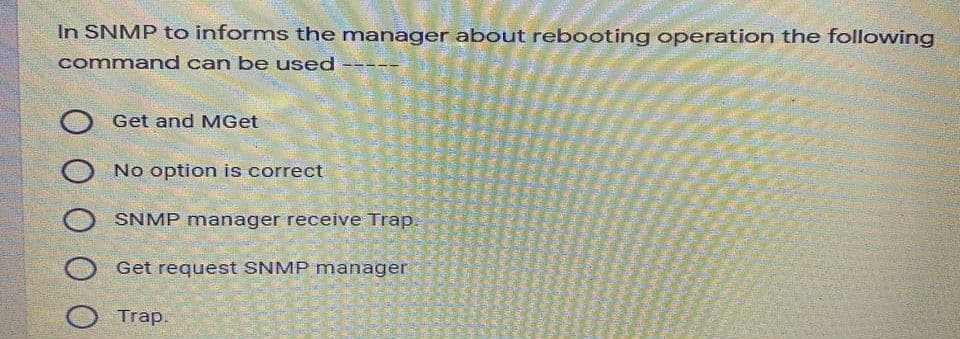
Q: In SNMP to informs the manager about rebooting operation the following command can be used O Get and…
A: Dear learner, hope you are doing well!!, I will try my best to answer this question. According to…
Q: Why isn't there an auto summary command in eigrp?
A: Introduction: EIGRP (Enhanced Interior Gateway Routing Protocol) is a distance-vector routing…
Q: Opsequences alert x1x op5 x2:X op1 op2 x3:X op3 y1:Y op4 op2 op3 Z1:Z new remove ZA
A: Answer: Belwo are the right options. a. The op2 message of x2 invoked by the object x3 is not the…
Step by step
Solved in 2 steps

- Can someone show me a NTFS permission screenshot of what this would be? The “FWC-EMPLOYEES” folder/directory is available to all FWC employees to place additional data (files/folders), but NO OTHER EMPLOYEE (other than sys admins!) should be able to modify, edit, delete, etc. ANY data they did NOT PUT INTO THIS FOLDER.You can use Kusto to query Azure Active Directory (Azure AD) logs stored in Log Analytics to define a rule of an Azure Monitor alert. Select Yes if the statement is true. Otherwise, select No.How to remove the item from the cart if the quantity is 0? I have included my code below that I am confused about how to implement this on. <?php session_start(); $page = 'cart'; //DATABASE CONNECTION INFO include_once ('includes/database.php'); include_once ('includes/header.php'); if(!isset($_COOKIE['loggedIn'])) { header("location: login.php"); } if (isset($_POST['update'])) { for ($x = 0; $x < sizeof($_SESSION['quant']); $x++) { $quant_id = 'quant_'.$x; if($_POST[$quant_id] > 0) { $_SESSION['quant'][$x] = $_POST[$quant_id]; } elseif($_POST[$quant_id] == 0) { //HOW DO I REMOVE THE ITEM FROM THE CART IF QUANTITY IS = 0? } else { echo "Quantity must be greater than 0 to purchase."; } } } if(isset($_POST['remove'])) { //HOW DO I REMOVE THE ITEM FROM THE CART IF THE "REMOVE" BUTTON IS CLICKED? } if(isset($_POST['submit_order'])) {…
- Login.feature file has following scenarios: @negative Scenario: User can't login without entering password Given user is not logged in When user enters email And user clicks Login button Then warning is shown No match for E-Mail Address and/or Password @negative @skip Scenario: User can't login without entering email Given user is not logged in When user enters password And user clicks Login button Then warning is shown No match for E-Mail Address and/or Password Do the following: Combine those 2 Scenarios in 1 Scenario Outline Implement step for a new Scenario OutlineWe can use this parameter from the Start-Job cmdlet to create and start a standard background job that runs a script without opening the script itself. Group of answer choices -Name -Job -FilePath -DefinitionNameIn order to log on to a client of an SAP system, a person needs to have a valid client number. True False An authorization cannot be included in multiple roles. True False Auser can have many roles. True Palse
- if [ $(id -u) -eq 0 ];then read -p "enter username:" username read -s -p "enter password:" password egrep "^$username"/etc/passwd>/dev/null if [ $? -eq 0];then echo "$username exists!" exit 1 else pass=$(perl -e 'print crypt($ARVG[0], "password")' $password) useradd -m -p "$pass" "$username" [ $/ -eq 0 ] && echo "user has been added to system!" || echo "Failed to add a user!" fi else echo "Only root may add to the system" exit 2 fi * recheck the code if this is valid syntax for account management or suggest /do another user account management shell script that runs in unix terminal and please attache the output at the endThe administrator wanted to verify the password expiration of user "Ahmed." Write appropriate commands for the following:● Write a command that is used to expire user Ahmed's password after 45 days.● Write a command that starts sending warnings to user Ahmed 15 days before his password expires.● Write a command that is used to set a minimum of 5 days between password changes for User Ahmed.● Write a command that is used to display user Ahmed's current password policyThe kill all command terminates ___________ .a. all instances of a process with the same PPIDb. all instances of a process with the same PIDc. all instances of a process with the same priorityd. all instances of a process with the same name
- Each process utilizes resources in following order: TRue or falsereleaseuserequestIn MS Access, to ensure that a promised date valued entered must a future point in time, whichvalidation rules can be used?A) > NOW()B) < NOW()C) > sysdateD) < sysdateE) none of the aboveA JMP command can only be used to go to a label included inside the current process.True False.



