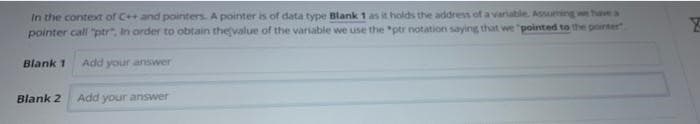
In the context of C++ and pointers. A pointer is of data type Blank 1 as it holds the address of a variable. Assuming we have a pointer call "ptr" In order to obtain the value of the variable we use the "ptr notation saying that we "pointed to the pointer Blank 1 Add your answer Blank 2 Add your answer
Q: What sets Sqoop distinct from its rivals and makes it the clear winner?
A: The data transfer process from relational databases to Hadoop is simplified with the help of the…
Q: Authentication is still a problem in today's information age, can you explain why this is so?
A: The above question is solved in step 2 :-
Q: It is important to investigate in depth the various methods to security management as well as the…
A: Please find the detailed answer in the following steps.
Q: Which kind of video game do you believe has arrived at a "turning point" in its evolution the most…
A: Multiplayer Online Battle Arena: The multiplayer online battle arena (MOBA) genre, in my opinion,…
Q: Write a python3 function sqr( n ) that returns the square of its numeric parameter n.
A: According to the information given. we have to write python3 function sqr( n )that returns the…
Q: Describe the ways in which the dependencies between running instructions on a modern pipelined…
A: In the field of Computer Architecture, PipeliningIt is the means through which an instruction stream…
Q: Why are APC ferrules less reflective of light than UPC ferrules? Computer science
A: APC: APC stands for Angle Polished Connector, which has an angled fibre end face of "8" degrees. APC…
Q: Describe the two competing opinions on operating system kernel design.
A: Introduction: The two competing schools of thought regarding the architecture of the kernel in…
Q: the flow of information
A: It is the bearing where information streams between two communication gadgets that is characterized…
Q: In the context of computer systems, how are architecture and organization differentiated from one…
A: Introduction: The design of computers, data storage devices, and networking components that store…
Q: 3. Convert the following two complement numbers into their signed decimal equivalents. i. 11111011…
A: First lets understand the process to convert two's complement number to signed decimal: if given : n…
Q: Providing a comprehensive breakdown of the evolution of a programming language is requested.
A: The question has been answered in step2
Q: What distinguishes a variable in a structured programming language from an object in an…
A: Introduction of Object-Oriented Language Object-Oriented Programming (OOP) is a programming…
Q: Why is big data both a problem and a possibility?
A: Introduction: Big data is data that contains a large amount of information and whose volume is…
Q: Why is it critical to plan a worksheet's structure before you begin inputting data? By preparing the…
A: Introduction It is necessary to structure the data in the worksheet properly. The formulas used in…
Q: When it comes to the creation of user interfaces, having a solid understanding of what mapping…
A: Mapping Implies: A strategy for bridging the gap between the requirements imposed by users or…
Q: rmation technology's impact on our lives and societies.Justify the benefits and drawba
A: Benefits:
Q: Is setting up and installing a firewall necessary, and if so, how do you go about doing so?
A: Introduction: A firewall, a security device that filters traffic and prevents unauthorised access to…
Q: computer science - Explain the function of any three to four value stream measurement parameters.
A: Introduction: Various Value Stream Measurement parameters are:
Q: security
A: Network security is a broad term that covers a multitude of technologies, devices, and processes. In…
Q: If you absolutely must, demonstrate that people and information systems are the driving drivers…
A: Introduction If you have to, show that people and information: systems are the driving drivers…
Q: It is critical to explain the current convergence of digital gadgets, as well as the interaction…
A: Intro The confluence of digital devices and cellphones is as follows: Device convergence is the…
Q: Following diagram is the confusion matrix for multi classification. Find the precision and recall.…
A: Given that confusion matrix. We need to find the precision and recall. See below steps.
Q: Unlike datagram and virtual-circuit networks, circuit-switched networks do not require a routing or…
A: INtro We said that two kinds of networks, datagram and virtual-circuit, need a routing or switching…
Q: List all known threat types and arrange threats with URL evidence from most commonly encountered to…
A: Introduction: List all known threat types and arrange threats with URL evidence from most commonly…
Q: Describe the ways in which the dependencies between running instructions on a modern pipelined…
A: Answer: Computer Architecture PipeliningIt's a method of collecting instructions from a processor…
Q: 5. How would cache size, block size and associativity change effect miss rate of those miss types?…
A: Below I have provided the answer
Q: What different sorts of data structures are required in order to carry out the instructions that are…
A: Data structures: When a programme is generated, the compiler generates executable files for that…
Q: The term "Network Database System" refers to a kind of database management system that is predicated…
A: Introduction: The network database system is an ownership-based database management system.
Q: Explain the distinctions between block and convolutional codes.
A: Answer in step2
Q: Describe the components of the security spheres paradigm. There must be enough information in the…
A: Introduction: Information security is primarily concerned with preventing unauthorized access to…
Q: When you're surfing the web and come across some strange information on a supposedly safe website,…
A: Introduction: The goal of search engines is to return results that are relevant and come from…
Q: Getting people to visit a website is one of the most crucial issues that emerges during the…
A: Intro Informing others about the newly created website the user and making the website interesting…
Q: What are the key duties that are expected of the Chief Information Security Officer, the Security…
A: Definition: We must fix the problem in accordance with the question. What are the CISO's, security…
Q: Sort DNS records into logical categories and organize them. In a brief paragraph, provide an example…
A: Introduction: Translating IP addresses into human-readable domain names is the goal of the Domain…
Q: Give an explanation of both the benefits and the drawbacks associated with software prototyping.
A: Introduction: PROTOTYPING SOFTWARE: The process of generating prototypes of different sorts of…
Q: How does an E-Book Reader work? What makes this distinct from past types of technology, like…
A: Inspection: A device that reads electronic books, such as the Amazon Kindle, is known as an…
Q: In terms of the functionality that they both provide, could you please give a full description of…
A: Object-Oriented Programming: Object-oriented programming, sometimes known as OOP, is a kind of…
Q: Describe the steps involved in setting up a brand new computer for use. Computer science
A: To start usage of a new computer, there are many things on must know. Because the new computer does…
Q: What precisely is a Trojan horse, and how does it carry out its intended purpose? In this respect,…
A: According to the information given:- We have to define the Trojan horse, it carry out its intended…
Q: In the context of computer systems, what exactly is the difference between architecture and…
A: COMPUTER SYSTEM: A computer system is a collection of elements (hardware, software, and liveware)…
Q: There are two types of database architectures: relational and object-oriented.
A: The main difference between Object Oriented Database and Object Relational Database is that Object…
Q: Fig 1 Change Pictures Select Picture to Display Sunset Display a photo of water lilies. Winter Scene…
A: Code:
Q: Using a certain form of processing, is it feasible to avoid wasting computing cycles while…
A: Introduction This article was written to address the topic of write-blocking, which is a prevalent…
Q: How can leadership be updated on the status of the monitoring of security? How can crucial areas be…
A: Monitoring is the most reliable method for identifying and tracking customers who are accessing…
Q: What are some of the views and opinions that you have towards the use of technology and computers in…
A: Encryption: Computers change our life. Regular internet usage has affected people's behaviour. New…
Q: Describe the function that the Internet Engineering Task Force (IETF) plays in the overall process…
A: Introduction: The IETF improves Internet performance by supplying high-quality, critical specialized…
Q: A time-consuming procedure for selecting the most suited programming language
A: Inspection: A programming language is nothing more than a collection of instructions for writing…
Q: What exactly is meant by the use of a poison package in an assault, and what does the fact that it…
A: Intro Any type of attacks involves the violation of the security by exploiting the vulnerability…
Q: It would be quite helpful if you could elaborate on the logic behind the authentication procedure.…
A: Start: Authentication is the process of making sure a user is who they say they are. With this…
Hand written answer plzz
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Problem 8. What is the correct syntax of declaring array of pointers of integers of size 10 in C++? a) int arr = new int[10]; b) int **arr = new int*[10]; c) int *arr = new int[10]; d) int *arr = new int*[10];What's the distinction between void and NULL pointers? Give appropriate examples to back up your answer. Give the distinctions in TABULAR form.WRITE THE PROGRAM IN C LANGUAGE : Write a program to countNon-Armstrong numbers fromm and n (including m and nalso) using the concept ofpassing pointers to function.Pass addresses of m, n andcount integers from the main ()function to the user definedfunction: calculate () [Functionis not returning any value], anddisplay the count in the main ()function.
- C PROGRAMMING Differentiate the output of the two programs. a. struct node {int x;node *next;};int main(){node *root; // This will be the unchanging first noderoot = new node; // Now root points to a node structroot->next = 0; // The node root points to has its next pointer// set equal to a null pointerroot->x = 5;} // By using the -> operator, you can modify the node// a pointer (root in this case) points to. b.struct node {int x;node *next;};int main(){node *root; // This won't change, or we would lose the list in memorynode *conductor; // This will point to each node as it traverses the listroot = new node; // Sets it to actually point to somethingroot->next = 0; // Otherwise it would not work wellroot->x = 12;conductor = root; // The conductor points to the first nodeif ( conductor != 0 ) {while ( conductor->next != 0)conductor = conductor->next;}conductor->next = new node; // Creates a node at the end of the listconductor = conductor->next; // Points to…Write a program to find the number of times that a given word occurs in a sentence using pointers. Read data from standard input. The first line is a single word, which is followed by general text on the second line. Read both up to a new line character, and insert a terminating null before processing. Typically output should be : The word is “ the ”. The sentence is “ the cat on the mat “ . The word occurs 2 times. IN C LANGUAGEIn C++ Create an array of head pointers, statically allocated of size 101 of that type: Now, create a pointer that can point to the first element: Show how to dynamically allocate an array of 101 elements of head pointers: Write the code to initialize each element to NULL: Rewrite the code to initialize each element to NULL using pointer arithmetic:
- What's the distinction between void and NULL pointers? Give appropriate examples to back up your answer.What is the difference between void and null pointers.Give suitable example in support of your answerA pointer variable is what? Then what? A dynamic array is a What's the deal with dynamic arrays and pointers?
- This lab will exercise your understanding of some of the concepts covered in Chapter 14: pointers and linked lists 1. Declare an integer pointer variable intPointer. Initialize it to point to an int variable named someInt. Assign the value 451 to someInt and output (cout) the variable someInt and output (cout) the value pointed to by intPointer. Write an assignment statement that indirectly stores 900 into the value pointed to by intPointer. Output (cout) the value pointed to by intPointer and output (cout) the variable someInt, 2. Declare a pointer variable charArrPointer and initialize it to point to the first element of a three-element char array named initials. Write assignment statements to store 'A', 'E', and 'W' into the first three elements of the array POINTED to by charArrPointer. Do NOT store any values directly into the array named initials. 3. Output (cout) the data in array charArrPointer and the data in array initials. 4. Copy the following code into your program above…A pointer variable is just what it sounds like. What is its purpose? Exactly what does it mean to have a "dynamic array"? Pointers and dynamic arrays have what relationship?Write a program to find the number of times that a given word occurs in a sentence using pointers. Read data from standard input. The first line is a single word, which is followed by general text on the second line. Read both up to a new line character, and insert a terminating null before processing. Typically output should be : The word is “ the ”. The sentence is “ the cat on the mat “ . The word occurs 2 times.

